NIST SP 800-171 and CMMC requirements can be vague, and understanding how to make your systems “compliant” can be difficult. How do you configure a windows laptop, a firewall, a Linux server, or another device to be “compliant” with your security requirements? Do you just need to set a complex password and configure multi-factor authentication? No. There is more to it. Wouldn’t it be great if there was a list that could tell you exactly how to configure your systems to meet your security requirements? Guess what? There are lists. Introducing DISA STIGs.
What are DISA STIGs?
A Defense Information Systems Agency (DISA) Security Technical Implementation Guide (STIG) is a list of configuration settings that should be applied to a system to properly secure or “harden” it. Systems are inherently vulnerable out of the box. By implementing DISA STIGs you are remediating those vulnerabilities, making your systems much more secure.
How DISA STIGs Support Compliance
DISA STIGs settings are linked back to NIST SP 800-53 security controls, so every time you are implementing a setting you are working towards meeting your security control requirements. As you may know, NIST SP 800-171 and CMMC draw most of their controls from NIST SP 800-53. So by implementing DISA STIG settings on your systems you are configuring them to be compliant with NIST SP 800-171 and CMMC requirements. DISA STIG settings cover various NIST SP 800-171 and CMMC domains including access control, identification and authentication, audit and accountability, configuration management, and system and communications protection. By implementing these settings you can be confident that your systems are configured to meet your compliance requirements.
NIST SP 800-171 3.4.2 & CMMC CM.2.065 Requirements
To meet requirements 3.4.2 and CM.2.065, you need to “establish and enforce security configuration settings for information technology products employed in organizational systems.” This refers to using guidance such as DISA STIGs or CIS Benchmarks. So by implementing DISA STIGs you will be directly meeting this requirement.
Where to Apply DISA STIGs?
You should deploy DISA STIGs to all information technology products that are within the scope of your compliance requirements. According to the NIST glossary, an information technology product is a “discrete, identifiable information technology asset (e.g., hardware, software, firmware) that represents a building block of an information system.” This includes laptops, desktops, smartphones, printers, servers, switches, firewalls, software like Microsoft Office, and google chrome.
How to Apply DISA STIGs
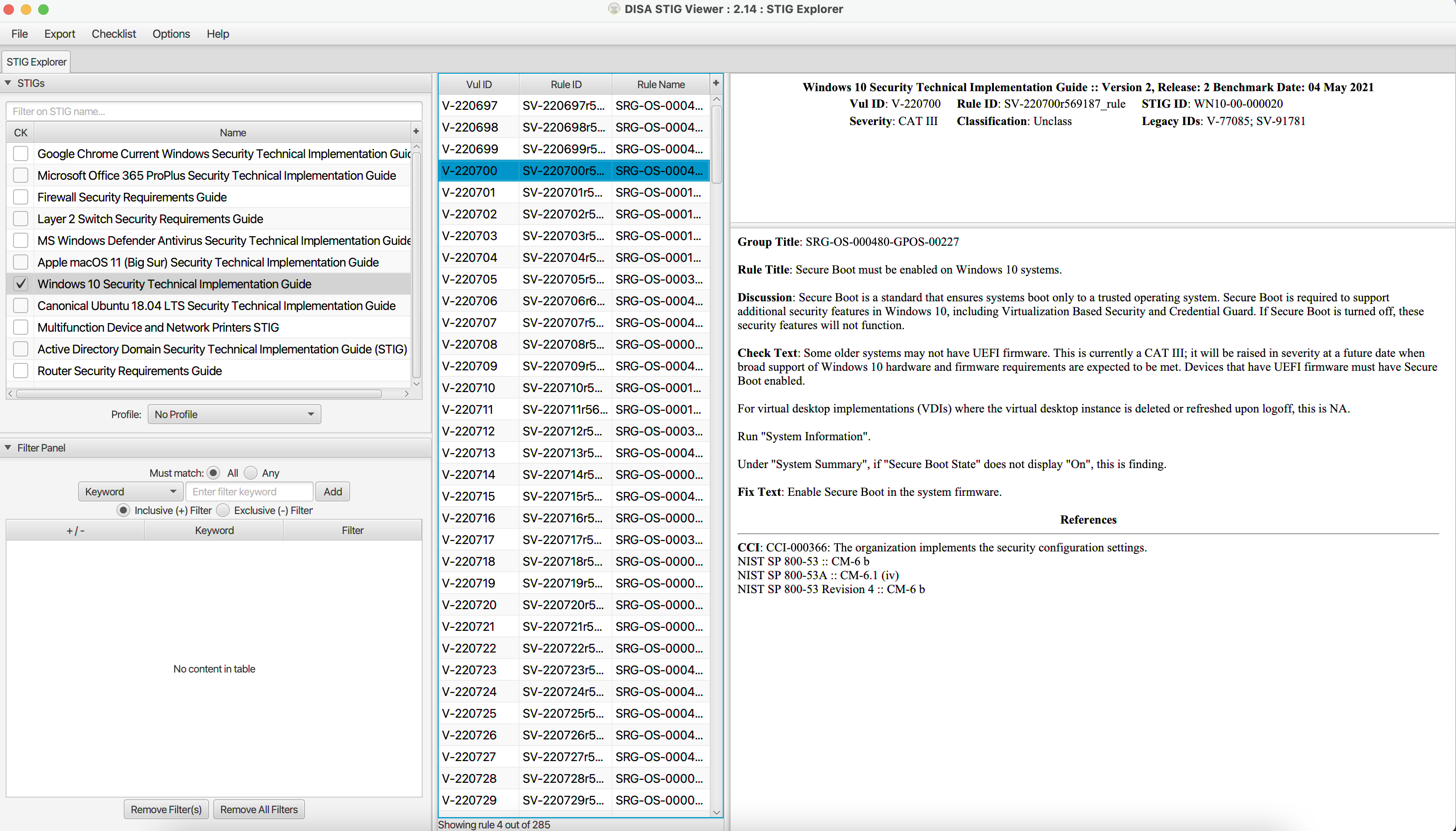
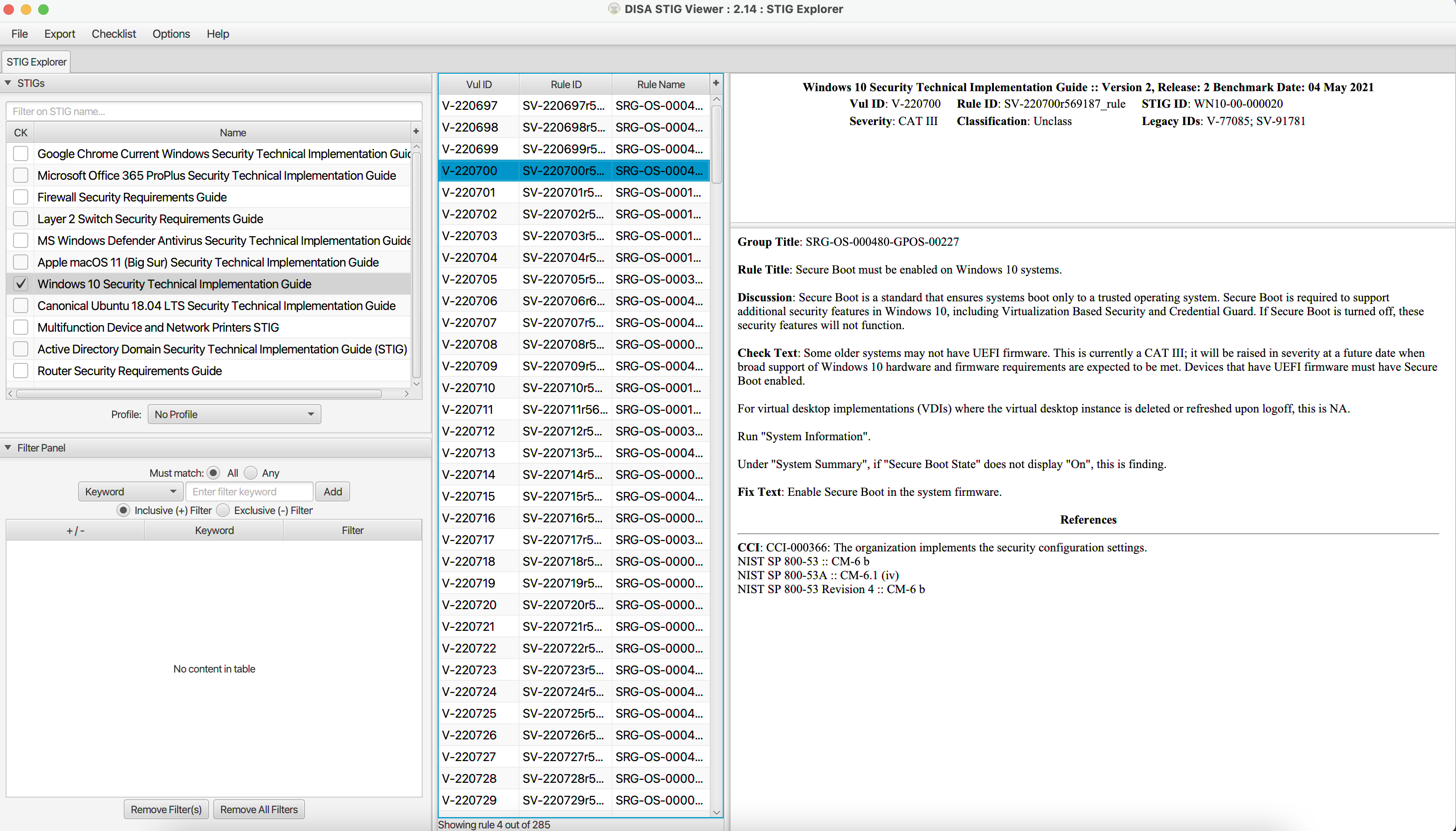
Using STIG Viewer, and the STIG files downloaded from the DoD Cyber Exchange website, you can see which settings need to be configured on your systems. DISA STIGS can be deployed to Microsoft computers and servers using group policy or endpoint manager. They can also be configured individually on each computer or server however this would be inefficient for most organizations. In most cases, STIG settings are individually configured on each network device unless the organization is large in which case standard configuration files can be shared on the same devices.