
Technical How-To: Configure Password Policies on Windows, Linux, and macOS to Enforce Complexity and Character Changes for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - IA.L2-3.5.7
Step-by-step guidance to configure password complexity and character-change controls on...
Read more →
How to Validate and Test Clock Synchronization to Satisfy NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AU.L2-3.3.7: Audit-Ready Procedures and Evidence
Step-by-step guidance to validate, test, and collect audit-ready evidence for...
Read more →
How to Use Version Control and Configuration Management to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - CM.L2-3.4.3 Requirements
Practical steps, tools, and small-business examples to track, review, approve,...
Read more →
How to Use Open-Source Tools to Monitor and Control Communications for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SC.L1-B.1.X: Practical Implementation Steps
Practical steps and open-source toolsets to monitor and control communications...
Read more →
How to Use Data Classification and Redaction to Meet FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.IV Requirements
Practical guide to implementing data classification and redaction to satisfy...
Read more →
How to Use Agile Project Management to Implement and Track Your Cybersecurity Roadmap — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-1-2
Learn how to apply Agile project management to implement, evidence...
Read more →
How to Train Your Security Team to Execute NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - CA.L2-3.12.1 Assessments Effectively
Practical, step‑by‑step guidance for training security teams to plan, perform,...
Read more →
How to Train Teams and Define Roles for Effective Penetration Testing Under Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-11-2
Practical guidance for training staff, defining roles, and producing evidence...
Read more →
How to Train IT and Security Teams to Review, Approve, and Log Changes per NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - CM.L2-3.4.3
Practical guidance to train IT and security staff to review,...
Read more →
How to Train Internal Teams to Perform Effective Periodic Assessments for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - CA.L2-3.12.1
Practical step-by-step guidance to train internal teams to perform repeatable,...
Read more →
How to Train Executives and Board Members to Comply with Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-10-2: Practical Tactics
Practical, step-by-step tactics to train executives and board members to...
Read more →
How to Train Admins and Users for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.II: Practical Exercises to Enforce Authorized Functions Only
Practical, exercise-driven guidance for training admins and users to enforce...
Read more →
How to Train Administrators and Users to Enforce Transaction-Level Access Controls for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.II (Code 545)
Practical, step-by-step guidance for training admins and users to implement...
Read more →
How to Test, Validate, and Document Periodic Scans and On-Access File Scanning: Evidence Checklist for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - SI.L2-3.14.5
Step-by-step guidance and an evidence checklist to test, validate, and...
Read more →
How to test and validate periodic and real-time scanning controls for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SI.L1-B.1.XV: Audit-ready procedures
Practical, audit-ready procedures to implement, test, and validate periodic and...
Read more →
How to Secure BYOD and OT Devices with Lightweight Anti-Malware for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SI.L1-B.1.XIII
Practical steps for small businesses to meet FAR 52.204-21 and...
Read more →
How to Monitor, Report, and Escalate Cross-Border Cybersecurity Obligations: Practical Implementation Steps — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-7-2
Practical, step-by-step guidance for small businesses to monitor, report, and...
Read more →
How to Monitor and Alert on Time Drift to Ensure Audit Record Integrity — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AU.L2-3.3.7
Practical guidance to detect, monitor, and alert on system clock...
Read more →
How to Measure Training Effectiveness for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AT.L2-3.2.2: Metrics, Tests, and Continuous Improvement
Practical guidance on measuring and proving training effectiveness to meet...
Read more →
How to Measure, Report, and Improve Physical Facility Security Metrics for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - PE.L2-3.10.2
Practical guidance for measuring, reporting, and improving physical facility security...
Read more →
How to Map Your Cloud Contracts to Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 4-2-3 for Compliance
A practical guide to aligning cloud provider contracts with ECC...
Read more →
How to Map and Classify Data Before Publishing: Actionable Implementation for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.IV
Practical, step‑by‑step guidance to map and classify business data before...
Read more →
How to Integrate Threat Modeling and Penetration Testing to Comply with Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-11-2
Practical, step-by-step guidance for combining threat modeling and penetration testing...
Read more →
How to Integrate Periodic Cybersecurity Requirement Reviews into Agile Project Workflows — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-6-4
Learn how to operationalize periodic cybersecurity requirement reviews within Agile...
Read more →
How to Integrate Maintenance Tasks into Your CMMS to Comply with NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - MA.L2-3.7.1
Step-by-step guidance to configure your CMMS so maintenance on systems...
Read more →
How to Implement MFA for Nonlocal Maintenance: NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - MA.L2-3.7.5 Step-by-Step Guide
Step-by-step guidance to implement multi-factor authentication (MFA) for nonlocal maintenance...
Read more →
How to implement KPIs and reporting for periodic backup reviews to meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-9-4
Learn how to design, implement, and report KPIs for periodic...
Read more →
How to implement data classification and redaction for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.IV on public websites
Practical steps for small businesses to classify, detect, and redact...
Read more →
How to Implement Application Whitelisting for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SI.L1-B.1.XIII to Prevent Malicious Code
Step-by-step guidance to implement application whitelisting (allowlisting) to meet FAR...
Read more →
How to Get Executive Approval for Your Vulnerability Management Plan: Practical Steps and Evidence for Auditors — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-10-1
Step-by-step guidance to secure executive sign-off for your Vulnerability Management...
Read more →
How to Draft Vendor SLAs and Contracts to Ensure Compliant Maintenance to Perform Maintenance on Organizational Systems (NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - MA.L2-3.7.1)
Practical guidance and sample contract/SLA language to ensure vendors perform...
Read more →
How to Deploy Secure Containerization and App Controls to Achieve Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-6-3 Compliance
Step-by-step guidance for implementing secure containerization and application controls to...
Read more →
How to Deploy an Automated Asset Classification and Labeling System for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-1-5
Step-by-step guidance for implementing an automated asset classification and labeling...
Read more →
How to Create an Incident Response Flow for Public Content Exposure under FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.IV
Step-by-step guidance to build an incident response flow that detects,...
Read more →
How to Create a Trigger-Based Policy Review Process for Legal and Regulatory Changes: Implementation Checklist for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-1-3
Step-by-step checklist and practical guidance to build a trigger-based policy...
Read more →
How to Create a Compliant IAM Requirements Template for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-2-1 (Code 472)
Step-by-step guidance to build a Compliance Framework-aligned IAM requirements template...
Read more →
How to Configure Network Access Control (NAC) to Satisfy Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-5-3
Step-by-step guidance to design, configure, and validate Network Access Control...
Read more →
How to Combine Threat Modeling and Vulnerability Scanning into a Compliant RA.L2-3.11.1 Assessment Process — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - RA.L2-3.11.1
[Write a compelling 1-sentence SEO description about this compliance requirement]...
Read more →
How to Build an Audit-Ready Compliance Program for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-7-1: Policies, Evidence, and Checklists
Practical steps to implement ECC-2:2024 Control 1-7-1 with policies, evidence...
Read more →
How to Build a Compliant Physical Asset Inventory and Tagging Program for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-14-3 (Code 542)
Practical step-by-step guidance to design and operate a Compliance Framework-aligned...
Read more →
How to Automate Pre-Implementation Security Impact Analysis in DevOps for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - CM.L2-3.4.4
Practical guide to automating pre-implementation Security Impact Analysis (CM.L2-3.4.4) in...
Read more →
How to Automate Monitoring and Evidence Collection for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-7-3 to Pass NCA Reviews
Step-by-step guidance to automate continuous monitoring and build tamper-evident evidence...
Read more →
How to Automate Asset Classification and Labeling for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-1-5 Compliance Using Tools and Workflows
Practical, step-by-step guidance to automate asset classification and labeling to...
Read more →
Step-by-Step: Migrating Public Services into Isolated Subnetworks Without Downtime to Comply with FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SC.L1-B.1.XI
Practical, step-by-step guidance for small businesses to migrate public-facing services...
Read more →
Step-by-Step Guide to Enforcing Least Privilege During Personnel Transfers to Protect CUI — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - PS.L2-3.9.2
Practical step-by-step guidance to enforce least privilege during personnel transfers...
Read more →
Step-by-Step: Getting Executive Approval for Your Cybersecurity Strategy under Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-1-1
Practical, step-by-step guidance to secure executive approval for your cybersecurity...
Read more →
How to Validate and Audit MFA Enforcement and Session Termination for External Nonlocal Maintenance — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - MA.L2-3.7.5
Step-by-step guidance to validate and audit MFA enforcement and session...
Read more →
How to Use Open-Source Tools to Monitor Organizational Communications for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SC.L1-B.1.X
Practical guide showing how small organizations can use open-source network,...
Read more →
How to Train Your Team to Perform RA.L2-3.11.1 Risk Assessments: NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 Implementation Tips
Practical, step-by-step guidance to train teams to perform RA.L2-3.11.1 risk...
Read more →
How to Train Your Team to Monitor, Control, and Protect Communications under FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SC.L1-B.1.X: Roles, Procedures, and Metrics
Practical guidance to train teams to monitor, control, and protect...
Read more →
How to Train Your IT Team to Execute Risk-Based Vulnerability Remediation for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - RA.L2-3.11.3
[Write a compelling 1-sentence SEO description about this compliance requirement]...
Read more →
How to Train Teams to Approve and Record Policy Updates for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-3-4
Practical, step-by-step guidance to train teams so they consistently approve...
Read more →
How to train teams on cryptography requirements under Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-8-3: Role-based procedures and enforcement best practices
Practical guidance on building role-based cryptography training, procedures, and enforcement...
Read more →
How to Train Staff on Visitor Escorting and Physical Access Device Controls for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - PE.L1-B.1.IX
Practical, step-by-step guidance to train staff on visitor escorting and...
Read more →
How to Train Staff on Escorting Visitors and Recording Access for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - PE.L1-B.1.IX (552): A Practical Training Plan
A practical, step-by-step training plan to ensure staff properly escort...
Read more →
How to Train Staff and Integrate Scan Workflows into Incident Response for Files Downloaded or Executed — Compliance Steps for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SI.L1-B.1.XV
Practical, step-by-step guidance to train staff and embed automated/manual scanning...
Read more →
How to Train Staff and Enforce Processes Acting on Behalf of Users for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - IA.L1-B.1.V
Practical, actionable guidance for training staff and enforcing processes when...
Read more →
How to Train Staff and Contractors on FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.III Requirements to Limit External System Use
Practical guidance for training staff and contractors to meet FAR...
Read more →
How to Train Remote and Hybrid Workforces for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AT.L2-3.2.2: Implementation Best Practices
Practical, role-based training and evidence-focused implementation steps to meet AT.L2-3.2.2...
Read more →
How to Train Operations Teams and Operationalize Monitoring of External/Internal Boundaries — FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SC.L1-B.1.X
Practical guidance for operations teams to define, monitor, and respond...
Read more →
How to Train IT and End Users for Ongoing BYOD Review Requirements under Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-6-4
Step-by-step guidance to train IT staff and end users to...
Read more →
How to Train Contractors and Third Parties to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AT.L2-3.2.2 Requirements
Practical, step-by-step guidance for small businesses to train contractors and...
Read more →
How to Train Authorizing Officials to Assign Roles Securely under Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-4-1
Practical, step-by-step guidance for training Authorizing Officials to assign roles...
Read more →
How to Train and Enforce Least Privilege for Media Access to Keep CUI Restricted to Authorized Users: NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - MP.L2-3.8.2
Practical steps and real-world examples to train personnel and enforce...
Read more →
How to Test and Validate Boundary Controls: Penetration Tests and Validation for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SC.L1-B.1.X
Practical guide to testing and validating boundary controls to meet...
Read more →
How to Test and Validate Access Restrictions for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.II: Audit and Penetration Techniques
Practical, step-by-step guidance on testing and validating access restrictions to...
Read more →
How to Secure Remote Workflows by Encrypting CUI on Mobile Devices and Mobile Computing Platforms with Minimal User Friction — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AC.L2-3.1.19
Practical, step-by-step guidance for implementing AC.L2-3.1.19 to encrypt CUI on...
Read more →
How to Secure Mobile and Shared Equipment in Co-Working Spaces for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - PE.L1-B.1.VIII
Practical, step-by-step guidance for small businesses to secure mobile and...
Read more →
How to Respond to Physical Access Incidents Under FAR 52.204-21 / CMMC 2.0 Level 1 - Control - PE.L1-B.1.IX: Incident Playbooks for Escort Failures, Log Tampering, and Device Compromise
Step-by-step incident playbooks and practical controls to satisfy FAR 52.204-21...
Read more →
How to Monitor Third-Party Software for Flaws under FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SI.L1-B.1.XII: Practical Steps for Compliance
Practical, step-by-step guidance for small businesses to monitor third‑party software...
Read more →
How to Monitor, Detect, and Respond to Mobile Threats: Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-6-3 Playbook
Step-by-step guidance to implement monitoring, detection and incident response controls...
Read more →
How to Migrate Public-Facing Services into Isolated Subnetworks Without Downtime — Compliance Guide for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SC.L1-B.1.XI
Step-by-step guidance to move public-facing services into isolated subnetworks with...
Read more →
How to Migrate Public-Facing Services into Compliant Subnetworks Without Downtime — FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SC.L1-B.1.XI
Step-by-step guidance for migrating internet-facing services into compliant subnetworks to...
Read more →
How to Measure and Report Compliance Metrics from Periodic Reviews for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-8-1
Step-by-step guidance to define, measure, and report actionable compliance metrics...
Read more →
How to Map Threat Modeling into Documented External Web App Requirements for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-15-1
Practical guidance for turning threat-model outputs into auditable external web...
Read more →
How to Map and Harden Critical Assets to Improve Detection of Unauthorized Use of Organizational Systems — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - SI.L2-3.14.7
Practical steps to identify, classify, harden, and monitor your critical...
Read more →
How to Integrate Third-Party Vendors into Your Incident Response Tests for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - IR.L2-3.6.3
Practical, step-by-step guidance to include third-party vendors in incident response...
Read more →
How to Integrate Risk Assessment Tools with Your Procedures to Satisfy Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-5-2
Practical guidance for small businesses to integrate automated risk-assessment tools...
Read more →
How to Integrate HR and IAM for Automated Screening Under NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - PS.L2-3.9.1
Practical guidance to automate personnel screening by integrating HR systems...
Read more →
How to Integrate Business Continuity into Risk Management for ECC 3-1-2 Compliance: Practical Implementation Roadmap (Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 3-1-2)
Practical roadmap to embed business continuity into your risk management...
Read more →
How to Integrate Automated Sanitization Tools into Your Asset Lifecycle to Meet FAR 52.204-21 / CMMC 2.0 Level 1 - Control - MP.L1-B.1.VII
Practical, step-by-step guidance for integrating automated media sanitization into your...
Read more →
How to Implement Zero Trust Access for BYOD to Satisfy Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-6-3: Practical Implementation Steps
Step-by-step guidance for small businesses to implement Zero Trust access...
Read more →
How to Implement Temporary Access Controls and Emergency Procedures for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - PE.L1-B.1.VIII Without Disrupting Operations
Practical, step-by-step guidance for implementing temporary access controls and emergency...
Read more →
How to Implement Role-Based Access Controls for CUI Backup Storage — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - MP.L2-3.8.9
Practical, step-by-step guidance to implement role-based access controls for Controlled...
Read more →
How to Implement Just-in-Time Access and Automated Provisioning to Meet AC.L2-3.1.1 — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AC.L2-3.1.1
Step-by-step guidance to implement Just-in-Time access and automated provisioning to...
Read more →
How to Implement Identity Authentication for IoT and Embedded Devices Under FAR 52.204-21 / CMMC 2.0 Level 1 - Control - IA.L1-B.1.VI
Practical, step-by-step guidance to implement device identity and authentication for...
Read more →
How to Implement Continuous Penetration Testing and Vulnerability Validation under Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-11-3
Practical, step-by-step guidance for implementing continuous penetration testing and vulnerability...
Read more →
How to implement adaptive, risk-based authentication to strengthen compliance with Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-2-3
Practical, step-by-step guidance for implementing adaptive, risk-based authentication (Control 2-2-3)...
Read more →
How to Harden and Secure NTP/Time Services to Prevent Manipulation: Practical Steps for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AU.L2-3.3.7
Practical, actionable steps to harden NTP/time services so organizations can...
Read more →
How to Encrypt and Manage Keys for Backup CUI to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - MP.L2-3.8.9: Practical Key Management Steps
Step-by-step guidance to encrypt Controlled Unclassified Information (CUI) backups and...
Read more →
How to Draft Incident Response Steps for Unauthorized External System Access and Use — FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.III
Step-by-step guidance to create incident response actions for unauthorized external...
Read more →
How to Document Technical Vulnerability Acceptance, Exceptions, and Risk Thresholds for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-10-1
Practical guidance for documenting vulnerability acceptance, exception handling, and risk...
Read more →
How to Develop KPIs and Metrics to Quantitatively Test the Organizational Incident Response Capability — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - IR.L2-3.6.3
Learn how to create measurable KPIs and metrics that demonstrate...
Read more →
How to Develop and Document Cybersecurity Policies for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-3-1: Step-by-Step Guide
Practical, step-by-step guidance to develop, document, and evidence cybersecurity policies...
Read more →
How to Design Incident Response Playbooks Triggered by Event Logs to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-12-3
Practical guidance for designing event-log-triggered incident response playbooks that satisfy...
Read more →
How to Design and Test Disaster Recovery Playbooks to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-9-2
Practical, step-by-step guidance for small businesses on designing, implementing, and...
Read more →
How to Deploy Ongoing Skills Development and Access to Professional Mentors per Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-10-4
Step-by-step guidance for implementing ongoing cybersecurity skills development and mentor...
Read more →
How to Deploy Deny-by-Exception Blacklisting on Linux with AppArmor/SELinux for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - CM.L2-3.4.8
Step‑by‑step guidance to implement deny‑by‑exception (blacklist) controls on Linux using...
Read more →
How to Create Incident Response Steps for Unauthorized Visitor Activity under FAR 52.204-21 / CMMC 2.0 Level 1 - Control - PE.L1-B.1.IX
Practical steps to build an incident response process for unauthorized...
Read more →
How to Create a Malware Incident Response Playbook to Comply with NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - SI.L2-3.14.2
Step-by-step guidance to build a practical malware incident response playbook...
Read more →
How to Create a Documented Vulnerability Risk Acceptance Process That Satisfies Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-10-1
Practical, step-by-step guidance to design and document a vulnerability risk...
Read more →
How to Create a Backup Data Classification and Handling Plan to Protect CUI — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - MP.L2-3.8.9
Step-by-step guidance to build a backup data classification and handling...
Read more →
How to Choose and Manage Third-Party Penetration Testers to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-11-3 Requirements
Practical guidance for selecting, contracting, and managing third-party penetration testers...
Read more →
How to Build an Automated Incident Response Test Plan Aligned to NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - IR.L2-3.6.3
Step-by-step guidance to design and implement an automated incident response...
Read more →
How to Build a Risk-Based Event Log Review Program to Satisfy Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-12-4
Practical step-by-step guidance for building a risk-based event log review...
Read more →
How to Balance Visitor Experience with Security When Implementing NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - PE.L2-3.10.3 Escort Requirements
Practical, small-business focused guidance to implement PE.L2-3.10.3 escort requirements so...
Read more →
How to Automate SSP Maintenance for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - CA.L2-3.12.4: Tools, Workflows, and Best Practices
Practical guidance to automate System Security Plan (SSP) maintenance to...
Read more →
How to Automate Identity Provisioning with SCIM for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-2-3: Tools & Scripts
Automate secure user lifecycle management with SCIM to meet ECC...
Read more →
How to Automate Cloud Configuration and Compliance Checks to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 4-2-4
Practical steps to automate cloud configuration and continuous compliance checks...
Read more →
How to Assess Residual Risk After Remediation to Comply with NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - RA.L2-3.11.3
Practical guidance for small organizations to measure and document residual...
Read more →
Implementing Least-Privilege Access with Identity Verification to Comply with FAR 52.204-21 / CMMC 2.0 Level 1 - Control - IA.L1-B.1.VI
Practical steps and real-world examples for applying least-privilege access and...
Read more →
How to Validate and Test Controls for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - IA.L1-B.1.V: Practical Tests to Verify User, Process and Device Identification
Practical, step-by-step tests and evidence collection methods to demonstrate user,...
Read more →
How to Use Red Team/Blue Team Scenarios to Test the Organizational Incident Response Capability for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - IR.L2-3.6.3
Practical guidance for designing red team/blue team exercises that demonstrate...
Read more →
How to Use Automated Access Controls and ABAC for Compliance with FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.I
Practical guidance on implementing automated access controls and attribute-based access...
Read more →
How to Train Your Team to Identify and Report Information System Flaws for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SI.L1-B.1.XII
Step‑by‑step guidance for small businesses to train personnel to detect,...
Read more →
How to Train Your Team on Secure Media Destruction for Federal Contract Information — FAR 52.204-21 / CMMC 2.0 Level 1 - Control - MP.L1-B.1.VII Best Practices
Practical, step‑by‑step guidance to train small business teams on secure...
Read more →
How to Train Teams to Perform Periodic Hosting and Cloud Security Reviews: Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 4-2-4
Practical guidance to train teams to perform scheduled hosting and...
Read more →
How to Train Teams to Define, Document, and Approve Cloud Security Requirements: A Practical Implementation Guide — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 4-2-1
Practical step-by-step guidance for training teams to define, document, and...
Read more →
How to Train Teams and Assign Roles for Ongoing ECC 2-3-4 Periodic Reviews — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-3-4
Practical, step-by-step guidance for training teams and assigning roles to...
Read more →
How to Train Supervisors to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - MA.L2-3.7.6: Practical Steps for Overseeing Maintenance Without Access Authorization
Practical, step-by-step guidance to train supervisors to oversee maintenance activities...
Read more →
How to Train Staff to Monitor and Control Communications to Meet FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SC.L1-B.1.X: Policies, Playbooks, and Testing Exercises
Practical, step-by-step guidance to train staff to monitor and control...
Read more →
How to Train Staff to Enforce FAR 52.204-21 / CMMC 2.0 Level 1 - Control - PE.L1-B.1.VIII: Policies, Procedures, and Accountability
Practical, step-by-step guidance for training staff to implement and document...
Read more →
How to Train Staff on Secure Media Handling and Disposal under FAR 52.204-21 / CMMC 2.0 Level 1 - Control - MP.L1-B.1.VII: Practical Exercises
Practical, hands-on training exercises and technical steps to help small...
Read more →
How to Train Staff on Media Sanitization and Reuse Controls for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - MP.L1-B.1.VII
Practical, step-by-step guidance to train staff on media sanitization and...
Read more →
How to Train Staff on ECC 3-1-2 Business Continuity Procedures: Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 3-1-2 Training Plan
Step-by-step guidance to build a compliant ECC 3-1-2 training plan...
Read more →
How to Train Staff and Operationalize Controls for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SC.L1-B.1.X: Role-Based Procedures to Monitor, Control, and Protect Organizational Communications
Practical, step-by-step guidance to train staff and operationalize role-based procedures...
Read more →
How to Train Staff and Governance Teams to Enforce Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-7-2 Requirements
Practical, audit-ready guidance to train staff and governance teams to...
Read more →
How to Train Staff and Enforce Procedures for MP.L2-3.8.3 Compliance — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - MP.L2-3.8.3 Implementation Tips
Practical, step-by-step guidance for training staff and enforcing procedures to...
Read more →
How to Train Staff and Enforce Procedures for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.III Compliance: Limiting External System Use
Practical, step-by-step guidance to train staff and enforce policies that...
Read more →
How to Train Staff and Enforce Policies for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - PE.L1-B.1.VIII Compliance
Practical, step-by-step guidance for small businesses to train personnel and...
Read more →
How to Train Staff and Enforce Policies for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.IV on Public-Facing Platforms
Practical guidance to train staff and enforce policies so public-facing...
Read more →
How to Train Managers and IT to Execute Immediate CUI Safeguards During Offboarding — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - PS.L2-3.9.2
Practical guidance for training managers and IT to promptly remove...
Read more →
How to Train IT Teams to Enforce Identification Requirements for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - IA.L1-B.1.V: Practical Exercises
Practical, exercise-based guidance for IT teams to enforce identification and...
Read more →
How to Train IT Teams to Apply Technical Security Standards and Satisfy Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-3-3
Practical, hands-on guidance to train IT teams to implement and...
Read more →
How to Train Employees on Physical Access Procedures to Achieve FAR 52.204-21 / CMMC 2.0 Level 1 - Control - PE.L1-B.1.VIII Compliance
Step-by-step guidance for training employees on physical access procedures to...
Read more →
How to Train Contractors and Temporary Staff for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AT.L2-3.2.2 Compliance
Step-by-step guidance for small businesses to train contractors and temporary...
Read more →
How to Track Progress and Measure Success: KPIs and Reporting for ECC Roadmap Execution — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-1-2
Practical guide to defining KPIs, implementing reporting, and measuring ECC...
Read more →
How to Test and Validate Transaction-Level Access Controls with Practical Use Cases — FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.II
Step-by-step guidance to test and validate transaction-level access controls for...
Read more →
How to Test and Validate Offboarding Controls with Tabletop Exercises — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - PS.L2-3.9.2
Learn how to design and run tabletop exercises to test...
Read more →
How to Test and Monitor Offboarding Controls to Prove CUI Protection: Compliance Checklist for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - PS.L2-3.9.2
Step-by-step checklist to test and monitor offboarding controls required by...
Read more →
How to Select Third-Party Pen Test Providers to Satisfy Requirement 502 - Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-11-3 (Vendor Evaluation Template)
Practical guidance and a vendor-evaluation template to choose third-party penetration...
Read more →
How to Secure APIs and WebSockets to Ensure Communication Authenticity in Production - NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - SC.L2-3.13.15
Practical guide to securing APIs and WebSockets for communication authenticity...
Read more →
How to Remediate Excess Audit Log Privileges Quickly and Compliantly: NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AU.L2-3.3.9 Rapid Remediation Steps
Step-by-step rapid remediation guidance to remove excess audit log privileges...
Read more →
How to Map Technical Controls (SAST, DAST, WAF) to Documented Requirements for External Web Apps - Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-15-1
Practical guidance to map SAST, DAST, and WAF controls to...
Read more →
How to Map Strategy Goals to Regulatory Requirements and ECC Controls: A Hands-On Playbook for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-1-1
A practical playbook to align business strategy with regulatory obligations...
Read more →
How to Map Job Functions to Access Controls: A Practical Implementation Plan — FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.II
Practical, step-by-step guidance for small businesses to map job functions...
Read more →
How to Map, Inventory, and Secure Publicly Accessible Information Systems to Achieve NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AC.L2-3.1.22 Compliance
Practical step-by-step guidance to discover, inventory, and secure all publicly...
Read more →
How to Map Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-2-3 to AWS, Azure, and GCP IAM Controls: Concrete Implementation Examples
Practical guidance to map ECC 2-2-3 identity and access requirements...
Read more →
How to Integrate Threat Intelligence Feeds into Malicious Code Defenses for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SI.L1-B.1.XIII
Practical guide to integrating threat intelligence feeds into malicious code...
Read more →
How to Integrate Real-Time File Scans into Incident Response Workflows to Satisfy FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SI.L1-B.1.XV
Step-by-step guidance for small businesses to implement real-time file scanning...
Read more →
How to Integrate Mobile Endpoint Detection and Response to Fulfill Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-6-3
Step-by-step guidance for integrating Mobile Endpoint Detection and Response (M-EDR)...
Read more →
How to Integrate Media Sanitization into Your Incident Response and Asset Lifecycle: FAR 52.204-21 / CMMC 2.0 Level 1 - Control - MP.L1-B.1.VII
Practical guidance for small businesses to integrate media sanitization into...
Read more →
How to Integrate Incident Response with Business Continuity and Recovery Plans for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - IR.L2-3.6.1
Practical, step-by-step guidance to integrate incident response with business continuity...
Read more →
How to integrate IAM periodic review metrics into your security program for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-2-4
Practical guidance to implement and measure IAM periodic access reviews...
Read more →
How to Implement Zero Trust Controls for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - IA.L2-3.5.1: Identify Users, Processes, and Devices End-to-End
Practical, step-by-step guidance to implement end-to-end identity for users, processes,...
Read more →
How to Implement Microsegmentation and Subnetworks for Public Assets — FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SC.L1-B.1.XI Best Practices
Practical, step-by-step guidance for isolating public-facing assets with subnetworks and...
Read more →
How to Implement Immutable Backups and Air-Gapped Recovery to Satisfy Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-9-2
Step-by-step guidance for implementing immutable backups and air-gapped recovery to...
Read more →
How to Implement Guest Wireless Segmentation and Strong Encryption for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AC.L2-3.1.17
Step-by-step guidance for small organizations to segment guest Wi‑Fi and...
Read more →
How to Implement Business Continuity Cybersecurity Requirements for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 3-1-2: Step-by-Step Guide
Practical, step-by-step guidance to implement Business Continuity cybersecurity requirements under...
Read more →
How to Harden Third-Party Vendor Access with MFA and Session Controls for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - MA.L2-3.7.5
Practical guidance to enforce MFA, session controls, and least-privilege for...
Read more →
How to Harden Cloud Email Platforms (Exchange Online, Gmail) to Comply with Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-4-3
Step-by-step guidance to secure Exchange Online and Gmail to meet...
Read more →
How to Enforce Failed Login Thresholds on Linux and SSH to Meet AC.L2-3.1.8 — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AC.L2-3.1.8
Practical, step-by-step guidance for implementing failed-login thresholds on Linux and...
Read more →
How to Design Role-Specific Cybersecurity Exercises and Simulations for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AT.L2-3.2.2
Practical guidance to design, run, and document role-specific cybersecurity exercises...
Read more →
How to Create Effective Monitoring Metrics and KPIs for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - CA.L2-3.12.3
Practical guidance to design monitoring metrics and KPIs that satisfy...
Read more →
How to Create Audit-Ready Evidence for Periodic Requirement Reviews (Templates & Checklist) — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-3-4
Practical, step-by-step guidance to assemble audit-ready evidence for periodic requirement...
Read more →
How to Create an Exceptions and Approval Workflow for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AC.L2-3.1.21 Compliant Portable Device Use
Step-by-step guidance to build an auditable exceptions and approval workflow...
Read more →
How to Conduct Risk-Based Periodic Reviews of Cybersecurity Requirements: Practical Implementation Guide — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-3-4
Step-by-step guide to implementing risk-based periodic reviews of cybersecurity requirements...
Read more →
How to Conduct Continuous Threat Hunting on Inbound/Outbound Traffic to Satisfy NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - SI.L2-3.14.6
Practical, step-by-step guidance for implementing continuous threat hunting on inbound...
Read more →
How to Build a Repeatable Risk Assessment Process for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-5-3: Templates, Metrics, and Automation
Step-by-step guidance to create repeatable, auditable risk assessments for ECC...
Read more →
How to Build a Practical Data Flow Map to Control CUI Movement: NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AC.L2-3.1.3
Step-by-step guidance for creating and enforcing a data flow map...
Read more →
How to build a GAAS-compliant audit program for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-8-2: 10-step implementation plan
Step-by-step guidance to design a GAAS-aligned audit program for ECC...
Read more →
How to Build a Compliant Cybersecurity Strategy Document (+ Template) for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-1-1
Step-by-step guidance and a ready-to-use template to produce a compliant...
Read more →
How to Build a Certificate-Based Device Identity Strategy for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - IA.L1-B.1.VI
Practical, step-by-step guidance on using PKI and device certificates to...
Read more →
How to Build a BYOD and Third-Party Device Policy Aligned with FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.III
Step-by-step guidance for small businesses to create a BYOD and...
Read more →
How to Automate Policy Enforcement to Implement Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-3-2 with CI/CD and Configuration Management
Practical, step-by-step guidance for automating policy enforcement to meet ECC...
Read more →
How to Automate Evidence Collection for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - MA.L2-3.7.3: Workflow, Logging, and Reporting
Practical, automated approaches to collect, retain, and report evidence for...
Read more →How to Automate Approval and Tracking of Third-Party Cybersecurity Requirements: Tools and Processes for ECC 4-1-1 Compliance — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 4-1-1
Learn practical, step-by-step methods and tool patterns to automate approval...
Read more →
How to Assign Roles, Train Staff, and Run Tabletop Exercises for RA.L2-3.11.1 Compliance: Implementation Playbook for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - RA.L2-3.11.1
Practical playbook for assigning roles, building staff training, and running...
Read more →
Step-by-step: configure backups, RTOs and RPOs to comply with Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 3-1-3
A practical, step-by-step guide to designing and implementing backups, recovery...
Read more →
Step-by-Step Checklist: Implementing Physical Access Device Controls to Achieve FAR 52.204-21 / CMMC 2.0 Level 1 - Control - PE.L1-B.1.IX
Practical, step-by-step guidance to implement and document physical access device...
Read more →
Step-by-Step Checklist for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - MP.L2-3.8.4: Labeling Physical and Electronic Media with CUI
Practical, step-by-step guidance for small businesses to implement MP.L2-3.8.4: properly...
Read more →
Maintenance Evidence Checklist: What Auditors Look For Under NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - MA.L2-3.7.1
Practical checklist and evidence examples to demonstrate compliance with NIST...
Read more →
Implementing Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-8-2: How to Structure an Internal Audit Function for Independence and GAAS Compliance
Step-by-step guidance to design an independent internal audit function that...
Read more →
How to Use Automated Tools and Simulations to Test the Organizational Incident Response Capability — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - IR.L2-3.6.3
Practical guidance on using automated tools and simulation exercises to...
Read more →
How to Train Your Team to Remediate Vulnerabilities per NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - RA.L2-3.11.3: Roles, Runbooks, and Metrics
Practical guidance to train teams to remediate vulnerabilities in accordance...
Read more →
How to Train Your SOC to Monitor Communications and Detect Attacks for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - SI.L2-3.14.6: Playbooks and Measurement Metrics
Practical guidance to build SOC playbooks and measurable detection metrics...
Read more →
How to Train Your IT Team to Enforce FAR 52.204-21 / CMMC 2.0 Level 1 - Control - IA.L1-B.1.V: Roles, Procedures, and Tooling
Practical, step-by-step guidance for IT teams to implement and enforce...
Read more →
How to Train Teams and Enforce Policies for Technical Vulnerabilities Management under Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-10-3
Practical guidance on training teams and enforcing policies to meet...
Read more →
How to train staff to enforce FAR 52.204-21 / CMMC 2.0 Level 1 - Control - PE.L1-B.1.VIII: procedures, incident reporting, and accountability
Practical steps for small businesses to train staff on procedures,...
Read more →
How to Train Staff on FAR 52.204-21 / CMMC 2.0 Level 1 - Control - MP.L1-B.1.VII: Implementing Procedures to Sanitize or Destroy Media Containing FCI
Practical training steps, procedures, and verification techniques to ensure staff...
Read more →
How to Train Staff and Enforce SOPs for File Scanning Compliance with FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SI.L1-B.1.XV
Practical guidance to train personnel and enforce SOPs that ensure...
Read more →
How to Train Managers and HR on Secure Transfer and Termination Procedures for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - PS.L2-3.9.2 Compliance
Learn practical, step-by-step training and operational controls to ensure managers...
Read more →
How to Train Legal and Procurement Teams on Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 4-1-1 Compliance for Contracts
Practical guidance to train legal and procurement teams to enforce...
Read more →
How to Train Front-Desk Staff to Escort Visitors and Capture Audit Logs for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - PE.L1-B.1.IX
Practical, step-by-step guidance for training front-desk staff to escort visitors...
Read more →
How to Test and Audit Authentication Mechanisms to Prove Compliance with FAR 52.204-21 / CMMC 2.0 Level 1 - Control - IA.L1-B.1.VI
Practical steps and tests to validate authentication controls and produce...
Read more →
How to select and deploy Endpoint Detection & Response (EDR) to meet FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SI.L1-B.1.XIII requirements
Practical, step-by-step guidance for selecting and deploying Endpoint Detection &...
Read more →
How to sanitize or destroy storage media to meet FAR 52.204-21 / CMMC 2.0 Level 1 - Control - MP.L1-B.1.VII: NIST 800-88 methods and tool selection
Practical guidance for small businesses to sanitize or destroy storage...
Read more →
How to Sanitize or Destroy Information System Media to Meet FAR 52.204-21 / CMMC 2.0 Level 1 - Control - MP.L1-B.1.VII (Checklist & Tools)
Practical, step-by-step guidance and a checklist for sanitizing or destroying...
Read more →
How to Sanitize and Destroy Hard Drives, SSDs, and Portable Media for CUI: Practical Procedures — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - MP.L2-3.8.3
Step-by-step, auditable procedures for sanitizing or destroying hard drives, SSDs,...
Read more →
How to Run Practical Tabletop Exercises That Teach Security Risks to Managers, Admins, and Users — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AT.L2-3.2.1
Step‑by‑step guidance for designing and running tabletop exercises that teach...
Read more →
How to Replace Password-Only Access with Phishing-Resistant MFA (FIDO2/Smartcard) for Compliance: Implementation Checklist — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - IA.L2-3.5.4
Step-by-step implementation checklist to replace password-only access with phishing‑resistant MFA...
Read more →
How to Prepare Audit Evidence and Maintain Continuous Compliance for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - PE.L1-B.1.VIII
Practical steps, evidence examples, and continuous-monitoring techniques to demonstrate and...
Read more →
How to Perform Onsite vs Offsite Media Destruction: Risk-Based Decision Guide for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - MP.L1-B.1.VII
Practical, risk-based guidance for deciding between onsite and offsite media...
Read more →
How to Measure Training Effectiveness: KPIs and Metrics for Insider Threat Recognition Programs (NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AT.L2-3.2.3)
Practical KPIs, data sources, and implementation steps to measure and...
Read more →
How to Measure KPIs and Reporting to Prove Compliance with Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-9-1 for Personnel Security
Practical guidance on defining KPIs, collecting evidence, and building repeatable...
Read more →
How to Measure and Report Audit Correlation Effectiveness to Prove Compliance — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AU.L2-3.3.5
Practical guidance to measure, validate, and report the effectiveness of...
Read more →
How to limit BYOD and contractor access to external information systems: actionable controls for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.III
Practical, step-by-step controls to restrict BYOD and contractor access to...
Read more →
How to Label Digital and Physical Media for CUI: Practical Implementation for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - MP.L2-3.8.4
Practical guidance for small businesses to label digital and physical...
Read more →
How to Integrate Penetration Testing Review Outcomes into Your Risk Register for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-11-4
Step-by-step guidance to convert penetration testing findings into measurable risk...
Read more →
How to Integrate IAM and Attribute-Based Policies to Control CUI Flow in Real Time — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AC.L2-3.1.3
Practical guide to using IAM + attribute-based access control to...
Read more →
How to Integrate DevOps Change Pipelines with Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-6-2: Practical Implementation Guide
Practical, step-by-step guidance for integrating DevOps change pipelines with ECC...
Read more →
How to Implement Secure Media Sanitization for FCI: FAR 52.204-21 / CMMC 2.0 Level 1 - Control - MP.L1-B.1.VII Step-by-Step Guide
Step-by-step, practical guidance for small businesses to implement media sanitization...
Read more →
How to Implement Risk-Based Controls for Accepting External Media with Diagnostic and Test Programs — Step-by-Step for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - MA.L2-3.7.4
Step-by-step guidance to implement risk-based controls for accepting external diagnostic...
Read more →
How to Implement Rapid Patch Management to Correct Information System Flaws — FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SI.L1-B.1.XII
Practical, step-by-step guidance for small businesses to implement rapid patch...
Read more →
How to Implement NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - MP.L2-3.8.8: Employee Training and Incident Response for Unknown Portable Storage
Practical steps to meet NIST SP 800-171 Rev.2 / CMMC...
Read more →
How to Implement KPIs and Reporting for Incident and Threat Management Under Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-13-2
Practical step-by-step guidance for implementing measurable KPIs and reporting to...
Read more →
How to Implement FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.I: Step-by-Step Guide to Restricting System Access to Authorized Users, Processes, and Devices
Practical, step-by-step guidance for meeting FAR 52.204-21 and CMMC 2.0...
Read more →
How to Implement Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-3-2: A Step-by-Step Plan to Protect Information Systems and Processing Facilities
Step-by-step guidance to implement ECC 2-3-2 to secure information systems...
Read more →
How to Implement ECC – 2 : 2024 Control 1-2-1: Create an Independent Cybersecurity Department That Complies with Royal Decree 37140
Step-by-step guidance to establish an independent cybersecurity department that meets...
Read more →
How to Implement Chain-of-Custody and Reuse Verification for Media Containing FCI: FAR 52.204-21 / CMMC 2.0 Level 1 - Control - MP.L1-B.1.VII How-To Guide
Step-by-step how-to for small businesses to implement chain-of-custody and reuse...
Read more →
How to implement a step-by-step risk assessment checklist and templates for ECC compliance — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-5-3
Step-by-step guidance, checklists, and ready-to-use templates to perform risk assessments...
Read more →
How to Document and Report Information System Flaws to Satisfy FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SI.L1-B.1.XII (555): Template and Examples
Clear, practical guidance and a ready-to-use template for documenting and...
Read more →
How to Deploy MFA and Device Authentication to Meet FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.I: A Practical Implementation Guide
Step-by-step guidance for small businesses to implement multifactor and device-based...
Read more →
How to Create Traffic Baselines and Anomaly Detection Rules for Inbound/Outbound Communications — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - SI.L2-3.14.6
Practical guide to building network traffic baselines and anomaly detection...
Read more →
How to Create Policy Templates and Checklists to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-4-1 for Organizational Structure and Roles
Practical guidance to design policy templates and verification checklists that...
Read more →
How to Create KPIs and Reporting Mechanisms for a Cybersecurity Function Reporting to Leadership — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-2-1 Metrics Guide
Practical guide to designing KPIs and reporting mechanisms to meet...
Read more →
How to Create a Step-by-Step Patch and Update Checklist for Malicious Code Protection (FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SI.L1-B.1.XIV)
Step-by-step guidance to build a patch and update checklist that...
Read more →
How to Create a Practical Compliance Checklist for Periodic Project Cybersecurity Reviews — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-6-4
Step-by-step guidance to build a practical, auditable checklist for periodic...
Read more →
How to Create a Practical Checklist to Satisfy NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - PE.L2-3.10.5: Control and Manage Physical Access Devices
A concise, actionable checklist and implementation guidance to control and...
Read more →
How to Create a Continuous Monitoring Metrics Dashboard for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - CA.L2-3.12.3 (KPI Examples)
Step-by-step guidance and KPI examples to design a continuous monitoring...
Read more →
How to configure WPA3-Enterprise and RADIUS to meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AC.L2-3.1.17 and protect wireless access with strong authentication and encryption
Step-by-step guidance for configuring WPA3-Enterprise with RADIUS (EAP-TLS), certificates, and...
Read more →
How to Configure Windows, Linux, and Cloud Permissions to Limit User Transactions for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.II
Step-by-step guidance to configure Windows, Linux, and cloud permissions to...
Read more →
How to Configure WAF, TLS, and HTTP Headers to Comply with Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-15-2 for External Web Apps
Step-by-step guidance to configure WAF, TLS, and HTTP security headers...
Read more →
How to Configure TLS and HTTPS to Prevent Unauthorized Disclosure of CUI — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - SC.L2-3.13.8
Practical, step-by-step guidance to configure TLS/HTTPS to protect Controlled Unclassified...
Read more →
How to Configure SIEM for Audit Record Reduction and On-Demand Reporting to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AU.L2-3.3.6
Practical guidance to configure your SIEM to reduce audit record...
Read more →
How to Configure MFA to Meet FAR 52.204-21 / CMMC 2.0 Level 1 - Control - IA.L1-B.1.VI: Practical Implementation and Best Practices
Step-by-step guidance for small businesses on implementing multi-factor authentication to...
Read more →
How to Configure Endpoint Security to Meet FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SI.L1-B.1.XV: Real-Time Scans on Download, Open, Execute
Step-by-step guidance to configure endpoint security for real-time scanning on...
Read more →
How to Configure Cloud Platforms (Azure/AWS) for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AU.L2-3.3.9: Restricting Audit Log Management to Privileged Roles
Practical, step-by-step guidance to configure Azure and AWS so that...
Read more →
How to Conduct a Gap Analysis Against International Cybersecurity Agreements to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-7-2
Practical, step-by-step guidance to perform a gap analysis against international...
Read more →
How to Communicate Audit Findings to Non-Technical Leadership: Presentation Templates and Talking Points — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-8-3
Practical templates and ready-to-use talking points to present ECC 2:2024...
Read more →
How to Build an Encryption Policy Template That Meets Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-8-1 Requirements
A practical guide and template for small businesses to implement...
Read more →
How to Build an Automated Log Review Workflow to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AU.L2-3.3.3
Step-by-step guidance to design and operate an automated log review...
Read more →
How to Build an Authorization Workflow that Satisfies FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.I: Policies, Procedures, and Automation
Step-by-step guidance to design an authorization workflow that meets FAR...
Read more →
How to Build an AUP Template with Role-Based Approval Workflows for Fast Compliance — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-1-3
Learn how to create an Acceptable Use Policy (AUP) template...
Read more →
How to Build a Step-by-Step Audit Checklist for Third-Party Agreements to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 4-1-4
Step-by-step guidance to create an audit checklist for third-party agreements...
Read more →
How to Build a Cryptography Review Checklist for Compliance with Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-8-4
A practical, actionable guide to building a cryptography review checklist...
Read more →
How to Build a Compliant Data Handling Policy for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-7-2 with Templates and Implementation Steps
Step-by-step guidance and ready-to-use templates to implement ECC 2-7-2 Data...
Read more →
How to Automate Temporary Password Provisioning and Force First-Login Reset with PowerShell — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - IA.L2-3.5.9
Practical step-by-step guidance to automate temporary password creation and require...
Read more →
How to assign roles, SOPs and KPIs for recurring cybersecurity reviews under Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-3-4
Assign clear roles, documented SOPs and measurable KPIs to run...
Read more →
Checklist: 10 Technical Controls to Enforce Mobile Device Security for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-6-2 Compliance
A practical checklist of 10 technical controls to enforce mobile...
Read more →
Step-by-Step Guide: Implementing Anti-Malware Controls for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SI.L1-B.1.XIII (Code 556)
Practical, step-by-step guidance to implement anti‑malware controls that satisfy FAR...
Read more →
Practical Checklist to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - RA.L2-3.11.1: Periodic Risk Assessment of Operations, Assets and Individuals
A concise, actionable checklist to implement RA.L2-3.11.1—periodic risk assessments of...
Read more →
Practical Checklist: Deploying Physical Access Controls and Audit Logs for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - PE.L1-B.1.IX
Step-by-step checklist to implement physical access controls and tamper-resistant audit...
Read more →
Operational Checklist: Reviewing and Updating Logged Events to Satisfy NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AU.L2-3.3.3
A practical operational checklist for small businesses to review, update,...
Read more →
How to Use SIEM to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AU.L2-3.3.1: Implementation Checklist and Best Practices
Practical guide to configuring SIEM to satisfy NIST SP 800-171...
Read more →
How to Use Policy Templates and Implementation Checklists to Achieve Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-3-1 Compliance
Practical guidance on using policy templates and implementation checklists to...
Read more →
How to Tune Alerts, Reduce Noise, and Prioritize Actions for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - SI.L2-3.14.3
Practical guidance to tune security alerts, reduce noise, and prioritize...
Read more →
How to Select and Manage Penetration Testing Vendors to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-11-3 Requirements
Practical guidance for small businesses on selecting, contracting, executing and...
Read more →
How to Select and Deploy Tools for Real-Time Scanning of External Files and Periodic System Scans — FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SI.L1-B.1.XV
Practical guidance for selecting, configuring, and evidencing real-time external file...
Read more →
How to Select and Configure EDR/AV Solutions to Satisfy FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SI.L1-B.1.XIII
Practical guidance for small businesses to choose, deploy, and configure...
Read more →
How to secure third-party external web applications: defining, documenting and approving requirements to meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-15-1
Step-by-step guidance to define, document, approve and enforce security requirements...
Read more →
How to Secure Cloud and Remote Access Boundaries for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SC.L1-B.1.X: Concrete Steps for Hybrid Environments
Practical, step-by-step guidance to secure cloud and remote access boundaries...
Read more →
How to Revoke Access and Recover Assets After Termination or Transfer — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - PS.L2-3.9.2 Checklist
Step-by-step checklist and practical controls to revoke access and recover...
Read more →
How to Prioritize and Remediate Vulnerabilities Using Risk Assessments — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - RA.L2-3.11.3
Learn practical steps to prioritize and remediate vulnerabilities using risk...
Read more →
How to Prepare for a Compliance Audit: Penetration Testing Processes Checklist for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-11-2
Practical, audit-focused penetration testing process checklist to meet ECC –...
Read more →
How to Prepare Audit-Ready Evidence of Periodic Incident & Threat Reviews for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-13-4
Step-by-step guide to collecting and organizing audit-ready artifacts for periodic...
Read more →
How to Perform a Gap Analysis Against Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-7-1 to Meet National Law Requirements
Step-by-step guidance to perform a gap analysis against ECC–2:2024 Control...
Read more →
How to Pass an Audit of Media Disposal Practices: FAR 52.204-21 / CMMC 2.0 Level 1 - Control - MP.L1-B.1.VII Implementation Guide for Small Contractors
Practical, step-by-step guidance for small contractors to implement, document, and...
Read more →
How to Pass a CMMC 2.0 Assessment for PS.L2-3.9.1: A Practical Implementation Checklist for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - PS.L2-3.9.1 Screening
Step-by-step guidance and an evidence-ready checklist to implement PS.L2-3.9.1 Screening...
Read more →
How to Migrate to a Compliant Cloud: Practical Steps for Meeting Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 4-2-3
Step-by-step guidance for migrating workloads to the cloud while meeting...
Read more →
How to Integrate Vulnerability Scanning with Patch Management and Ticketing Workflows for Faster Remediation — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - RA.L2-3.11.2
Practical guidance to integrate vulnerability scanning, patch management, and ticketing...
Read more →
How to Integrate Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-5-2 Procedures with ISO 27001 and NIST: Implementation Roadmap
Practical roadmap to implement ECC 2:2024 Control 1-5-2 Procedures and...
Read more →
How to Implement Threat Detection and Logging for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-13-3 Using SIEM and EDR
Step-by-step guidance for meeting ECC 2-13-3: implement SIEM and EDR...
Read more →
How to Implement NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AC.L2-3.1.7: Enforce Least Privilege and Block Non-Privileged Execution (Step-by-Step)
Step-by-step guidance to implement AC.L2-3.1.7—enforce least privilege and prevent non-privileged...
Read more →
How to Implement FAR 52.204-21 / CMMC 2.0 Level 1 - Control - IA.L1-B.1.V: Identify Users, Processes, and Devices in 7 Practical Steps
Step-by-step guide to meeting FAR 52.204-21 and CMMC 2.0 Level...
Read more →
How to Implement Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 4-1-3 in Managed Services Agreements: Security Clauses, SLAs, and Templates
Practical guidance and ready-to-use clause/SLA templates to implement ECC –...
Read more →
How to Implement Cloud-Native Alerts for Audit Log Failures (AWS/Azure/GCP): NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AU.L2-3.3.4
Step-by-step guidance to implement cloud-native detection and alerting for audit...
Read more →
How to Implement a Security Awareness Program for Managers, System Administrators, and Users — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AT.L2-3.2.1 (Step-by-Step Plan for Compliance)
Step-by-step guide to implement a NIST SP 800-171 Rev.2 /...
Read more →
How to Implement a Patch-and-Update-Checklist-for-malicious-code-tools-to-satisfy-SI.L1-B.1.XIV (FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SI.L1-B.1.XIV)
[Write a compelling 1-sentence SEO description about this compliance requirement]...
Read more →
How to Implement a Compliant Backup and Recovery Policy (Step-by-Step) — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-9-1
Step-by-step practical guidance to implement a compliant backup and recovery...
Read more →
How to Harden Windows and Linux Systems to Enforce Least Functionality: Implementation Guide for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - CM.L2-3.4.6
Practical, technical guidance to apply the principle of least functionality...
Read more →
How to Enforce Password Reuse Restrictions in Azure AD/Entra for a Specified Number of Generations — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - IA.L2-3.5.8 (Password Protection + Conditional Access)
Step‑by‑step guidance to prevent password reuse for a defined number...
Read more →
How to Deploy Single Sign-On and Conditional Access for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - IA.L1-B.1.VI with Azure AD or Okta
Step-by-step guidance to implement SSO and Conditional Access with Azure...
Read more →
How to Deploy MFA and Secure Process Access for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.I: Practical Steps for Small Contractors
Step-by-step guidance for small contractors to deploy MFA and secure...
Read more →
How to Deploy AWS/GCP/Azure KMS for Controlled Cryptographic Keys to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - SC.L2-3.13.10
Practical, step-by-step guidance to deploy AWS KMS, Google Cloud KMS,...
Read more →
How to Create Policies and Technical Controls to Limit External Connections for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.III
Practical steps to create policies and deploy technical controls that...
Read more →
How to Create Audit-Ready Reports and Track Remediation for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - CA.L2-3.12.1
Practical steps for small businesses to build audit-ready reports and...
Read more →
How to Create and Document Cybersecurity Policies That Comply with Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-3-1: Step-by-Step Implementation Guide
Step-by-step guidance to create, document, and evidence cybersecurity policies that...
Read more →
How to Create an Inventory and Identification Process for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - IA.L1-B.1.V: Checklist and Templates
Step-by-step guidance, checklist items, and reusable templates to build an...
Read more →
How to Create an ECC 1-8-1 Review Checklist and Schedule: Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-8-1 Practical Template
A practical, step‑by‑step template and schedule to implement ECC 1-8-1...
Read more →
How to Create an Audit-Ready Physical Access Log Process: Practical Checklist — FAR 52.204-21 / CMMC 2.0 Level 1 - Control - PE.L1-B.1.IX
Step-by-step guidance to build audit-ready physical access logging that satisfies...
Read more →
How to create an anti‑malware implementation checklist and evidence package for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SI.L1-B.1.XIII
[Write a compelling 1-sentence SEO description about this compliance requirement]...
Read more →
How to Create a Visitor Management Plan for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - PE.L1-B.1.IX: Policies, Workflows, and Audit Trails
Practical step-by-step guidance to build a visitor management plan that...
Read more →
How to Create a Step-by-Step CUI Risk Assessment Checklist for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - RA.L2-3.11.1 Compliance
Step-by-step checklist and practical guidance to perform CUI risk assessments...
Read more →
How to Create a Network Security Management Checklist for Compliance with Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-5-3
Step-by-step guidance and a practical checklist to help small organizations...
Read more →
How to create a compliance-ready workflow for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SI.L1-B.1.XII: templates to identify, report, and remediate flaws
Step-by-step guidance and ready-to-use templates to satisfy FAR 52.204-21 and...
Read more →
How to Configure SIEM and Log Aggregation to Identify Unauthorized Use - NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - SI.L2-3.14.7
Practical, step-by-step guidance for configuring SIEM and log aggregation to...
Read more →
How to Configure Firewalls and Segmentation to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-5-3 Requirements
Practical, step-by-step guidance for small businesses to configure firewalls and...
Read more →
How to Configure Encryption, ACLs, and DLP to Ensure Only Authorized Users Access CUI on Media — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - MP.L2-3.8.2
Practical steps to configure encryption, access controls, and DLP so...
Read more →
How to Configure DMARC, SPF and DKIM for Email Authenticity to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-4-3 (Practical Implementation)
Step-by-step guidance to configure SPF, DKIM, and DMARC for email...
Read more →
How to Configure Cloud Perimeter and Internal Boundary Protections in AWS and Azure for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SC.L1-B.1.X
Step-by-step guidance to configure perimeter and internal boundary protections in...
Read more →
How to Configure CCTV and Visitor Activity Monitoring to Comply with FAR 52.204-21 / CMMC 2.0 Level 1 - Control - PE.L1-B.1.IX
Step-by-step guidance for small businesses to configure CCTV and visitor...
Read more →
How to Configure Automatic Updates for Endpoint Malware Tools to Meet FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SI.L1-B.1.XIV
Step-by-step guidance for small businesses to configure automatic updates for...
Read more →
How to Conduct Post-Incident Reviews and Lessons-Learned Sessions to Satisfy Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-13-4
Step-by-step guidance to run compliant post-incident reviews and lessons-learned sessions...
Read more →
How to Build Network and Endpoint Controls to Block Remote Activation of Collaboration Devices (Zoom Rooms, Teams Rooms) — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - SC.L2-3.13.12
Practical, step-by-step guidance for implementing network and endpoint controls to...
Read more →
How to Build and Document Event Logging Requirements with Ready-to-Use Templates — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-12-1
Step-by-step guidance and ready-to-use templates to define, implement, secure, and...
Read more →
How to Build an Incident Response Program to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-13-3 Requirements
Step-by-step guidance for small businesses to build an incident response...
Read more →
How to Build an Audit-Ready Roles Review Checklist for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-4-2 to Prove Compliance
Practical, step-by-step guidance to create an audit-ready roles review checklist...
Read more →
How to Build an Audit-Ready Risk Management Framework Using Templates for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-5-1
Step-by-step guidance to implement an audit-ready risk management framework for...
Read more →
How to Build an Audit-Ready Mobile Device Security Standard: Template & Approval Workflow — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-6-1
Step-by-step guidance to create an audit-ready mobile device security standard...
Read more →
How to Build a VPN Encryption Strategy (IPsec vs SSL/TLS) for Compliance with NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AC.L2-3.1.13
A practical guide to selecting and configuring IPsec or SSL/TLS...
Read more →
How to Build a Vendor SLA Template with Required Security KPIs and Evidence Collection for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 4-1-2
Step-by-step guidance to build a vendor SLA template aligned to...
Read more →
How to Build a Step-by-Step Maintenance Control Checklist for Tools, Techniques, and Personnel — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - MA.L2-3.7.2
Step-by-step guidance to build a maintenance control checklist that satisfies...
Read more →
How to Build a Small-Business Physical Access Checklist to Satisfy FAR 52.204-21 / CMMC 2.0 Level 1 - Control - PE.L1-B.1.VIII
Step-by-step guidance to build a practical physical access checklist that...
Read more →
How to Build a Screening Policy for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - PS.L2-3.9.1: Templates and Implementation Guide
Step-by-step guidance and reusable policy language to build a compliant...
Read more →
How to Build a Patch-and-Update Workflow to Keep Malicious Code Protection Current — FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SI.L1-B.1.XIV
Step-by-step guidance for building a repeatable patch-and-update workflow that keeps...
Read more →
How to Build a Media Sanitization Policy for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - MP.L1-B.1.VII: Practical Implementation Checklist
A practical, step-by-step checklist to build a media sanitization policy...
Read more →
How to Build a Compliance Checklist for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SI.L1-B.1.XIII: From Risk Assessment to Ongoing Monitoring
A practical, step-by-step guide to building a compliance checklist for...
Read more →
How to Automate Periodic Vulnerability Reviews and Reporting to Meet ECC Requirements — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-10-4
Step-by-step guidance to automate vulnerability scans, remediation tracking, and compliance...
Read more →
How to Automate Audit Record Reduction and On-Demand Reports with Splunk or ELK for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AU.L2-3.3.6
Practical steps to implement automated audit-record reduction and on-demand reporting...
Read more →
Checklist: Configuring Authentication Controls to Satisfy FAR 52.204-21 / CMMC 2.0 Level 1 - Control - IA.L1-B.1.VI
Step-by-step checklist to configure authentication controls that satisfy FAR 52.204-21...
Read more →
Step-by-Step Implementation Guide to Supervise Unauthorized Maintenance Personnel: NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - MA.L2-3.7.6
Practical, step-by-step guidance to supervise and control maintenance personnel to...
Read more →
Step-by-Step Guide: Implementing Periodic Risk Assessments for CUI (NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - RA.L2-3.11.1)
Practical, step-by-step guidance for small businesses to implement periodic risk...
Read more →
Step-by-step guide: building continuous employee security training and awareness to meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-9-4
Practical, step-by-step implementation guidance to build a continuous employee security...
Read more →
Step-by-Step Checklist to Make Business Continuity Reviews Audit-Ready - Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 3-1-4
Practical, audit-focused checklist to make your Business Continuity reviews defensible...
Read more →
Step-by-Step Checklist to Implement FAR 52.204-21 / CMMC 2.0 Level 1 - Control - MP.L1-B.1.VII (Code 550): Sanitizing and Destroying FCI Media
A practical, step-by-step checklist to help small businesses sanitize and...
Read more →
Practical Tools and Methods to Sanitize Hard Drives and Flash Media for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - MP.L1-B.1.VII Compliance
Practical, step-by-step guidance and tool recommendations to sanitize HDDs, SSDs,...
Read more →
Practical Checklist: Identify Information System Users, Processes Acting on Behalf of Users, and Devices for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - IA.L1-B.1.V
A concise, practical checklist to inventory and identify all users,...
Read more →
How to Write Penetration Testing Review Reports That Satisfy Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-11-4: Template & Examples
Practical guidance and a ready-to-use template to produce penetration testing...
Read more →
How to Verify Experience and Certifications to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-2-2 Hiring Requirements
Practical, step-by-step guidance for small businesses to verify candidate experience...
Read more →
How to use Zero Trust principles to meet FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.III: Implementable controls to verify and limit external connections
Practical Zero Trust controls and step-by-step implementation guidance to verify...
Read more →
How to Use IAM and Endpoint Management to Satisfy FAR 52.204-21 / CMMC 2.0 Level 1 - Control - IA.L1-B.1.V: A Practical Guide
Step-by-step, actionable guidance for small businesses to implement IAM and...
Read more →
How to Use Free and Low-Cost Tools to Meet FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SI.L1-B.1.XIII Requirements
Practical, low-cost ways small businesses can meet FAR 52.204-21 /...
Read more →
How to Use Endpoint and Network Tools to Automatically Identify Devices for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - IA.L1-B.1.V
Practical guidance for using endpoint agents, NAC, and network telemetry...
Read more →
How to Use Checklists and Templates to Dispose of Federal Contract Information Media Compliantly: FAR 52.204-21 / CMMC 2.0 Level 1 - Control - MP.L1-B.1.VII
Practical, step-by-step guidance and ready-to-adapt checklist/template fields to dispose of...
Read more →
How to Use Automation and Tools to Satisfy FAR 52.204-21 / CMMC 2.0 Level 1 - Control - IA.L1-B.1.V: Identifying Users, Processes Acting for Users, and Devices Efficiently
Practical automation and tooling approaches to reliably identify users, processes...
Read more →
How to Use Automation and Tooling to Streamline Periodic Requirement Reviews for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-3-4
Practical guidance on using automation, tooling, and lightweight processes to...
Read more →
How to Use a Checklist and Template to Meet ECC Review and Documentation Requirements — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-5-4
Practical step-by-step guidance on using a checklist and template to...
Read more →
How to Secure Cloud Storage and SaaS to Protect CUI at Rest: Implementation Checklist — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - SC.L2-3.13.16
Practical, step-by-step checklist to encrypt and manage Controlled Unclassified Information...
Read more →
How to Screen Individuals Before Granting CUI System Access: Step-by-Step Guide — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - PS.L2-3.9.1
Practical, step-by-step guidance for implementing PS.L2-3.9.1 (Personnel Screening) to screen...
Read more →
How to Run Tabletop Exercises to Test the Organizational Incident Response Capability — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - IR.L2-3.6.3
Practical, step-by-step guidance for designing and running tabletop exercises to...
Read more →
How to Run Background Checks and Vetting for CUI Access: NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - PS.L2-3.9.1 Implementation Checklist
Step-by-step implementation checklist and practical guidance for conducting background checks...
Read more →
How to Run a Technical Email Service Review: Tools, Tests, and Evidence for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-4-4
Step-by-step guidance to perform a technical email service review for...
Read more →
How to Reduce Insider Risk by Implementing Personnel Requirements from Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-9-2
Practical, step-by-step guidance for small businesses to implement personnel requirements...
Read more →
How to Recruit and Retain Experienced Saudi Cybersecurity Professionals to Satisfy Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-2-2: Proven Recruitment Channels and Retention Strategies
Practical guidance on recruiting and retaining experienced Saudi cybersecurity professionals...
Read more →
How to Protect Cloud Workloads from Malicious Code for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SI.L1-B.1.XIII: Configurations, Tools, and Tests
Practical, step-by-step configurations, tools, and tests to protect cloud workloads...
Read more →
How to Prioritize and Patch Vulnerabilities to Comply with NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - SI.L2-3.14.1
Practical, step-by-step guidance for small businesses to identify, prioritize, patch,...
Read more →
How to perform a gap analysis for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-7-1 to meet national regulatory requirements
Step-by-step guide for small organizations to perform a gap analysis...
Read more →
How to Monitor and Verify Implementation for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-3-2: Audit-Ready Techniques to Prove Compliance
Practical, audit-ready monitoring and verification techniques to demonstrate Control 1-3-2...
Read more →
How to Monitor and Alert on Audit Log Tampering: Practical Steps and Tool Configurations — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AU.L2-3.3.8
Learn practical steps, specific tool configurations, and real-world examples to...
Read more →
How to Measure and Report Security Awareness Effectiveness: KPIs and Evidence for Compliance Audits — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AT.L2-3.2.1
Practical guidance on selecting KPIs, collecting auditable evidence, and presenting...
Read more →
How to Maintain Physical Access Audit Logs for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - PE.L1-B.1.IX: Tools, Templates, and Best Practices
Practical guidance for small businesses to implement, store, and audit...
Read more →
How to implement technical controls for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-7-1: Configurations and Monitoring to Satisfy National Laws
Practical steps to implement technical configurations and monitoring required by...
Read more →
How to Implement Security Awareness Training for Insider Threat Indicators: Step-by-Step — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AT.L2-3.2.3
Step-by-step guidance to build security awareness training that detects and...
Read more →
How to Implement Physical Access Controls for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - PE.L2-3.10.1: A Step-by-Step Guide
Step-by-step, practical guidance for implementing PE.L2-3.10.1 physical access controls so...
Read more →
How to Implement Periodic and Real-Time File Scanning to Meet FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SI.L1-B.1.XV: Step-by-Step Deployment Guide
Practical, step-by-step guidance for small businesses to deploy periodic and...
Read more →
How to Implement Patch and Configuration Management to Satisfy FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SI.L1-B.1.XII: A Practical Guide
Practical, step-by-step guidance for small businesses to implement patching and...
Read more →
How to Implement NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - CM.L2-3.4.7: Step-by-Step Guide to Restricting Nonessential Programs and Services
Practical, step-by-step guidance for small businesses to meet NIST SP...
Read more →
How to Implement NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AU.L2-3.3.8: Step-by-Step Guide to Protect Audit Logs and Logging Tools From Unauthorized Access, Modification, and Deletion
Learn practical, step-by-step methods to secure audit logs and logging...
Read more →
How to Implement Malicious Code Protection Across Endpoints and Servers: FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SI.L1-B.1.XIII Step-by-Step Guide
Step-by-step guidance for small businesses to implement malicious code protection...
Read more →
How to Implement Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-2-2: HR Policies and Job Descriptions to Secure Saudi Talent
Practical guidance for implementing ECC‑2:2024 Control 1‑2‑2 by embedding security...
Read more →
How to Encrypt and Manage Keys for CUI at Rest: Step-by-Step Implementation to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - SC.L2-3.13.16
Step-by-step guidance to encrypt Controlled Unclassified Information (CUI) at rest...
Read more →
How to Document and Demonstrate ECC 1-5-3 Risk Assessment Procedures for Audits — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-5-3: Template and Evidence Guide
Step-by-step guide to document and demonstrate ECC 1-5-3 risk assessment...
Read more →
How to deploy MFA for Windows RDP and Linux SSH privileged logins to comply with NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - IA.L2-3.5.3
Step-by-step guidance to implement multifactor authentication for Windows RDP and...
Read more →
How to Define and Document Committee Members, Roles & Responsibilities for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-2-3 (Template + Checklist)
Step-by-step guidance and ready-to-use templates to define, document and operationalize...
Read more →
How to Create Audit-Ready Evidence of Approved Access Changes: Templates and Processes for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - CM.L2-3.4.5
Practical steps, templates, and technical evidence sources to produce audit-ready...
Read more →
How to Create an Authorizing Official‑Approved Cybersecurity Org Chart for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-4-1 (Template + Checklist)
Step-by-step guidance to build an Authorizing Official–approved cybersecurity organizational chart...
Read more →
How to Create an Audit-Ready Security Impact Analysis Template for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - CM.L2-3.4.4
Step-by-step guidance to build an audit-ready Security Impact Analysis (SIA)...
Read more →
How to create an audit-ready event logging program for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-12-1: retention, format, and approval best practices
Practical, step-by-step guidance for implementing an audit-ready event logging program...
Read more →
How to Create a Step-by-Step Network Segmentation Checklist to Implement FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SC.L1-B.1.XI
A practical, step-by-step network segmentation checklist to help small businesses...
Read more →
How to Create a Step-by-Step Compliance Checklist to Periodically Review Business Continuity Cybersecurity Requirements — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 3-1-4
A practical, step-by-step guide to building a repeatable compliance checklist...
Read more →
How to Create a Step-by-Step Checklist for Periodic Review of Data Security Requirements (Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-7-4)
Practical, step-by-step guidance for building a periodic review checklist to...
Read more →
How to Create a Practical Labeling Standard Aligned to Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-1-5: Templates and Examples
A practical guide for small businesses to design and implement...
Read more →
How to Configure Web Servers and CMS to Enforce FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.IV
Practical, step‑by‑step guidance for configuring web servers and CMS platforms...
Read more →
How to Configure SIEM and Alerting Rules to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - SI.L2-3.14.3
Step‑by‑step guidance to configure SIEM ingestion, alerts, and evidence to...
Read more →
How to Configure Firewalls and Traffic Filters to Meet FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SC.L1-B.1.X: Practical Implementation Steps
Step-by-step, practical guidance for small businesses to configure firewalls and...
Read more →
How to Configure AWS VPC Subnets and Security Groups to Meet FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SC.L1-B.1.XI
Step-by-step guidance to configure AWS VPC subnets, route tables, and...
Read more →
How to Configure 802.1X and RADIUS to Enforce Authorized Wireless Access: NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AC.L2-3.1.16 Implementation
Step-by-step guidance to implement 802.1X with RADIUS (WPA2/WPA3-Enterprise) to meet...
Read more →
How to conduct ECC-compliant risk assessments during cloud migrations — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-5-3: Step-by-step migration guide
Practical, step-by-step guidance to conduct ECC 2:2024 Control 1-5-3 compliant...
Read more →
How to Conduct Background Checks to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - PS.L2-3.9.1: Practical Checklist
A practical, step-by-step checklist for conducting personnel background checks to...
Read more →
How to Conduct Background Checks and Identity Verification for CUI Access: NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - PS.L2-3.9.1 Implementation Checklist
Step-by-step implementation checklist and practical guidance to perform background checks...
Read more →
How to Build Physical and Logical Subnetworks on AWS to Meet SC.L1-B.1.XI (FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SC.L1-B.1.XI) — Hands-On Tutorial
A practical, hands-on guide showing how small businesses can design...
Read more →
How to Build Cloud Public Subnets for AWS and Azure to Comply with FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SC.L1-B.1.XI
Practical, step-by-step guidance for designing AWS and Azure public subnets...
Read more →
How to Build an Evidence-Based Compliance Program for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-7-2: Templates and Implementation Checklist
Practical, step-by-step templates and an implementation checklist to satisfy ECC...
Read more →
How to Build an Audit-Ready Program for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-7-2: Evidence, Templates and Checklist
Practical guidance and ready-to-use templates to collect evidence, organize artifacts,...
Read more →
How to Build an Audit-Ready Physical Security Checklist for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - PE.L2-3.10.2
Step-by-step guidance to build an audit-ready physical security checklist and...
Read more →
How to Build a Periodic Vulnerability Scanning Program for All Network-Connected Devices (Servers, Desktops, Laptops, VMs, Containers, Firewalls, Switches, Printers) - NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - RA.L2-3.11.2
Practical step-by-step guidance to design and operate a periodic vulnerability...
Read more →
How to Build a Patch-and-Update Process for Antivirus and EDR to Meet FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SI.L1-B.1.XIV
Step-by-step guidance for small businesses to create an auditable patch-and-update...
Read more →
How to Build a DMZ in AWS or Azure to Separate Public Components from Internal Networks — FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SC.L1-B.1.XI Implementation Checklist
Practical, actionable guidance to design and implement a DMZ in...
Read more →
How to Build a Compliance Checklist for Monitoring, Controlling, and Protecting Communications: FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SC.L1-B.1.X
A practical, step-by-step compliance checklist to monitor, control, and protect...
Read more →
How to Build a BYOD Policy That Satisfies NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AC.L2-3.1.18: Control connection of mobile devices (Template + Implementation)
Step-by-step guidance and a ready-to-adapt BYOD policy template to meet...
Read more →
How to Automate Periodic Malware and Integrity Scans Across Endpoints and Cloud Storage: Practical Steps for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SI.L1-B.1.XV
Practical, step‑by‑step guidance to automate periodic malware and file integrity...
Read more →
Checklist and Templates to Document, Approve, and Support Cybersecurity Roles per Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-4-1
Practical checklist and ready-to-use templates to document, approve, and operationally...
Read more →
Step‑by‑Step Implementation Guide: Removing CUI Before Off‑Site Repairs — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - MA.L2-3.7.3
Practical, step‑by‑step guidance for small organizations to remove Controlled Unclassified...
Read more →
Step-by-Step Guide: Implementing a Repeatable CUI Risk Assessment Process to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - RA.L2-3.11.1
Learn a practical, repeatable process to assess and manage risk...
Read more →
Step-by-Step Guide: Automating Access Revocation for Terminations and Transfers — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - PS.L2-3.9.2
Practical step-by-step guidance to automate deactivation and removal of access...
Read more →
Step-by-Step Checklist to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-15-3 for External Web App Security
A practical, hands-on checklist to help small businesses meet ECC...
Read more →
Implementing FAR 52.204-21 / CMMC 2.0 Level 1 - Control - IA.L1-B.1.V: Practical Checklist for Identifying Users, Processes, and Devices
Step-by-step practical checklist to identify and track users, processes, and...
Read more →
How to Use IAM Tools to Limit System Access for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.I: AWS, Azure, and On-Prem Implementation Steps
Practical, step-by-step guidance to use AWS, Azure, and on-prem IAM...
Read more →
How to Use Automation to Scale Periodic Cybersecurity Reviews: Implement Continuous Monitoring and Reporting for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-8-1
Learn practical automation strategies to implement continuous monitoring and automated...
Read more →
How to Use Automated Tools to Schedule, Track, and Document Asset Reviews for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-1-6
Practical guidance for using automated tools to schedule, track, and...
Read more →
How to Use Automated Scanning to Detect Public Data Leakage for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.IV
Practical guide to using automated scanners, cloud APIs, and CI/CD...
Read more →
How to Use a Practical Template to Run Quarterly Penetration Testing Process Reviews for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-11-4
Step-by-step guidance and a ready-to-use template to run quarterly penetration...
Read more →
How to Use a Compliance Checklist to Conduct Periodic Cybersecurity Strategy Reviews — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-1-3
A practical guide to building and using a compliance checklist...
Read more →
How to Use a 15-Point Testing Checklist to Validate Incident Response for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - IR.L2-3.6.3
[Write a compelling 1-sentence SEO description about this compliance requirement]...
Read more →
How to Turn Vulnerability Scan Results into Actionable Plans of Action (POA&Ms) — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - CA.L2-3.12.2
Step-by-step guidance for converting vulnerability scan output into prioritized, auditable...
Read more →
How to Select and Deploy Scanning Tools That Meet SI.L1-B.1.XV Requirements — FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SI.L1-B.1.XV
Practical guidance for small businesses to select, configure, and operate...
Read more →
How to Sanitize vs Destroy Electronic Media Containing FCI: Practical Methods to Comply with FAR 52.204-21 / CMMC 2.0 Level 1 - Control - MP.L1-B.1.VII
Practical, technical guidance for small businesses to sanitize or destroy...
Read more →
How to Sanitize and Destroy Media Containing Federal Contract Information: Step-by-Step Guide for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - MP.L1-B.1.VII
Practical, step-by-step guidance for small businesses to sanitize and destroy...
Read more →
How to Revoke Access on Employee Termination: Step-by-Step CUI Protection — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - PS.L2-3.9.2
Practical, step-by-step guidance for immediately revoking access on employee termination...
Read more →
How to Prioritize and Remediate Vulnerabilities Using Risk Assessment Results for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - RA.L2-3.11.3
Practical guidance for small businesses to prioritize and remediate vulnerabilities...
Read more →
How to Prepare Your Organization for CMMC Assessments: Testing Incident Response Capability per NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - IR.L2-3.6.3
Practical, step-by-step guidance for preparing and documenting incident response testing...
Read more →
How to Prepare for an Audit: Evidence and Documentation to Demonstrate Compliance with FAR 52.204-21 / CMMC 2.0 Level 1 - Control - PE.L1-B.1.VIII
Practical guidance and an evidence checklist for small businesses to...
Read more →
How to Prepare for an Assessment: Verifying Physical Access Controls for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - PE.L1-B.1.VIII with a Pre-Audit Checklist
Practical, step-by-step guidance and a pre-audit checklist to verify physical...
Read more →
How to Prepare Backup & Recovery Documentation for Audits: Evidence, Approval Records, and Best Practices (Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-9-1)
Practical guidance on preparing backup and recovery documentation, approval records,...
Read more →
How to Perform Secure Media Sanitization and Destruction for FCI: Tools, Techniques, and Checklist — FAR 52.204-21 / CMMC 2.0 Level 1 - Control - MP.L1-B.1.VII
Step‑by‑step guidance to securely sanitize and destroy media holding Federal...
Read more →
How to Map Technology Project Requirements to Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-6-1: A Compliance Checklist
Step-by-step guidance for mapping project requirements to ECC‑2:2024 Control 1-6-1...
Read more →
How to Integrate Identity Proofing, MFA, and Logging to Enforce FAR 52.204-21 / CMMC 2.0 Level 1 - Control - IA.L1-B.1.VI in Cloud and On-Prem Environments
Step-by-step guidance to combine identity proofing, strong MFA, and centralized...
Read more →
How to Integrate HR and IT Processes to Automate Personnel Security Controls (Pre‑Hire to Post‑Separation) — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-9-1
Practical guidance to integrate HR and IT workflows to automate...
Read more →
How to Implement Technical Controls (ACLs, RBAC, MFA) to Restrict Authorized User Functions — FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.II
Practical, step-by-step guidance for small businesses to implement ACLs, RBAC,...
Read more →
How to Implement Secure Cloud Backups and Encryption for ECC Compliance — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-9-2
Practical, step-by-step guidance for implementing secure cloud backups and encryption...
Read more →
How to Implement Password Complexity and Character-Change Policies in Azure AD for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - IA.L2-3.5.7
Step-by-step guidance to implement password complexity and character-change controls in...
Read more →
How to Implement NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - MP.L2-3.8.2: Step-by-Step Guide to Limiting CUI Access on System Media to Authorized Users
Practical, step-by-step guidance for small businesses to meet MP.L2-3.8.2 by...
Read more →
How to Implement MFA for Users, Processes, and Devices to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - IA.L2-3.5.2: A Step‑by‑Step Guide
Step-by-step guidance for implementing multifactor authentication (MFA) across users, processes,...
Read more →
How to Implement Low-Cost Physical Controls for Small Businesses to Meet FAR 52.204-21 / CMMC 2.0 Level 1 - Control - PE.L1-B.1.VIII
Practical, low-cost steps small businesses can implement to meet FAR...
Read more →
How to Implement Low-Cost, High-Impact Controls for FAR 52.204-21 / CMMC 2.0 Level 1 in Small Defense Contractors
Practical, budget-friendly steps small defense contractors can apply right away...
Read more →
How to Implement Least-Privilege Access: A Step-by-Step Guide to FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.II
Practical, step-by-step guidance for small businesses to implement least-privilege access...
Read more →
How to Implement Egress Monitoring and DLP Controls to Identify Data Exfiltration — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - SI.L2-3.14.6
[Write a compelling 1-sentence SEO description about this compliance requirement]...
Read more →
How to Implement DKIM/SPF/DMARC and Document Compliance for ECC 2-4-1 — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-4-1
Step-by-step guidance to deploy DKIM, SPF, and DMARC and produce...
Read more →
How to Implement Continuous Vulnerability Scanning and Reporting to Satisfy Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-10-1
Practical, step-by-step guidance to implement continuous vulnerability scanning and reporting...
Read more →
How to Implement a Risk Management Methodology for Your Cybersecurity Function — Practical Steps (Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-5-2)
Step-by-step guidance for implementing a documented risk management methodology to...
Read more →
How to Implement a Penetration Testing Policy that Meets Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-11-1: Templates and Checklists
Step-by-step guidance and ready-to-use templates to build a penetration testing...
Read more →
How to Draft an ECC-Compliant Acceptable Use Policy — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-1-4 Template and Best Practices
Practical guidance and a ready-to-use template to create an ECC...
Read more →
How to Draft a BYOD Policy and Review Cycle That Satisfies Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-6-4
Step-by-step guidance to create a BYOD policy and review cycle...
Read more →
How to Design Cloud Subnetworks in AWS/Azure/GCP for Public-Facing Components — FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SC.L1-B.1.XI Implementation Playbook
Practical playbook for designing AWS/Azure/GCP subnetworks for public-facing components to...
Read more →
How to Design a DMZ and Segmented Subnets to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - SC.L2-3.13.5 Compliance
Step-by-step guidance to design a DMZ and segmented subnets that...
Read more →
How to Deploy Mobile Device Management (MDM) and Configure Encryption for BYOD: Implementation Checklist for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-6-2
Step‑by‑step guidance to deploy MDM, enforce device encryption and BYOD...
Read more →
How to Deploy Cost-Effective Physical Security Measures to Meet FAR 52.204-21 / CMMC 2.0 Level 1 - Control - PE.L1-B.1.VIII for Small Businesses
Practical, low-cost physical security strategies and step-by-step implementation advice to...
Read more →
How to create and retain system audit logs to meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AU.L2-3.3.1: A practical implementation checklist
A practical, step‑by‑step checklist for small organizations to create, protect,...
Read more →
How to Create a Step-by-Step Checklist to Identify System Users, Processes Acting for Users, and Devices — FAR 52.204-21 / CMMC 2.0 Level 1 - Control - IA.L1-B.1.V
Practical, step-by-step checklist and implementation guidance to identify system users,...
Read more →
How to Create a Practical Risk Assessment Checklist and Template to Meet RA.L2-3.11.1 for CUI — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - RA.L2-3.11.1
Step-by-step guide to build a checklist and template that meets...
Read more →
How to Create a Continuous Monitoring Playbook for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - CA.L2-3.12.3: Tools, Processes, and Checklist
Learn how to build a practical continuous monitoring playbook that...
Read more →
How to Create a Compliance-Ready IR Test Checklist for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - IR.L2-3.6.3
Step-by-step guidance to build a compliance-ready incident response (IR) testing...
Read more →
How to Create a Compliance Checklist to Periodically Review Cybersecurity Requirements in Business Continuity Plans — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 3-1-4
Practical step-by-step guidance to build a Compliance Framework checklist for...
Read more →
How to Configure Windows & macOS to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - MP.L2-3.8.8: Technical Steps to Prevent Use of Unidentified USB Drives
Step‑by‑step, practical guidance to configure Windows and macOS systems so...
Read more →
How to Configure Key Management and Cryptographic Controls to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-8-3 Requirements
Practical, step-by-step guidance for implementing key management and cryptographic controls...
Read more →
How to Conduct a Public-Facing Systems Audit and Fix Gaps for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.IV
Step-by-step guide to auditing and remediating public-facing systems to meet...
Read more →
How to Build an Audit-Ready Visitor Log System for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - PE.L1-B.1.IX
Step-by-step guidance to design and operate an audit-ready visitor log...
Read more →
How to Build an Audit-Ready Inventory for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - IA.L1-B.1.V: Practical Steps to Map Users, Processes Acting for Users, and Devices
Step-by-step guidance to create an audit-ready inventory that maps authorized...
Read more →
How to Build an Audit-Ready Email Security Review Checklist Aligned to Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-4-4
Step-by-step guidance to create an audit-ready email security review checklist...
Read more →
How to Build an Audit-Ready Communications Protection Checklist for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SC.L1-B.1.X
Step-by-step guidance to build an audit-ready communications protection checklist that...
Read more →
How to Build an Audit-Ready Business Continuity Cybersecurity Policy: Step-by-Step for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 3-1-1
Step-by-step guidance for small businesses to create an audit-ready Business...
Read more →
How to Build a Timely Flaw Remediation Workflow for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SI.L1-B.1.XII (Templates & SLAs)
Step-by-step guidance, templates, and recommended SLAs to implement a timely...
Read more →
How to Build a Step-by-step Security Awareness Training Program to Recognize and Report Insider Threats — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AT.L2-3.2.3
Step-by-step guidance for implementing NIST SP 800-171 / CMMC 2.0...
Read more →
How to Build a Patch Management Process That Demonstrates Compliance with NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - RA.L2-3.11.3
A practical, step-by-step guide to building a risk-based patch and...
Read more →
How to Build a Compliance Checklist for Protecting and Handling Data to Satisfy Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-7-1
Step-by-step checklist and practical guidance for small businesses to protect...
Read more →
How to Build a BYOD Policy for Compliance with Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-6-2: Template and Enforcement Checklist
Step-by-step guidance to create and enforce a BYOD policy that...
Read more →
How to Automate Identifier Deactivation in Azure AD and Microsoft 365 for IA.L2-3.5.6 Compliance — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - IA.L2-3.5.6
Step‑by‑step guidance to automate disabling inactive Azure AD and Microsoft...
Read more →
How to Automate Cryptographic Inventory and Periodic Reviews for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-8-4
Practical steps to automate discovery, inventory, and periodic review of...
Read more →
How to automate backup integrity checks and scheduled reviews to meet compliance — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-9-4
Step-by-step guidance to automate backup integrity checks and scheduled review...
Read more →
How to Apply CUI Markings and Limit Distribution: 10 Best Practices for Compliance with NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - MP.L2-3.8.4
Practical, step-by-step best practices for marking Controlled Unclassified Information (CUI)...
Read more →
A Practical Checklist for Establishing Incident Handling (Prep, Contain, Recover) — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - IR.L2-3.6.1
Step-by-step checklist to build an incident handling program (prepare, contain,...
Read more →
10 Practical Steps to Achieve FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.IV Compliance for Publicly Accessible Information Systems
Step-by-step, practical guidance for small businesses to secure publicly accessible...
Read more →
Step-by-Step Implementation Roadmap to Protect and Monitor Facilities for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - PE.L2-3.10.2
Practical, step-by-step guidance to protect and monitor facilities to meet...
Read more →
Step-by-Step Guide: How to Zone Your Facility and Restrict Equipment Access for Compliance — FAR 52.204-21 / CMMC 2.0 Level 1 - Control - PE.L1-B.1.VIII
Practical, step-by-step instructions to zone your facility and restrict equipment...
Read more →
Step-by-Step Guide: Configure SIEM and Alerts for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-12-3 Compliance
Practical step-by-step instructions to configure your SIEM and alerts to...
Read more →
Step-by-Step Checklist to Identify Information System Users, Processes Acting on Behalf of Users, and Devices for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - IA.L1-B.1.V
A practical, step-by-step checklist to identify and document users, processes...
Read more →
Implementation Checklist: Meeting FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SI.L1-B.1.XII for Timely Identification, Reporting, and Correction
Practical, step-by-step implementation checklist to satisfy FAR 52.204-21 and CMMC...
Read more →
Implementation Checklist: FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SC.L1-B.1.X — 10 Actions to Monitor, Control, and Protect Communications at External/Internal Boundaries
Practical 10-step checklist to implement FAR 52.204-21 / CMMC 2.0...
Read more →
How to Write an Email Security Policy That Meets Approval Standards — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-4-1
Practical guidance to draft, implement and get formal approval for...
Read more →
How to Use System Logs and SIEM to Prove Identification for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - IA.L1-B.1.V
Practical steps for small businesses to collect, normalize, and present...
Read more →
How to use project management tools (Jira/MS Project) to automate ECC 1-6-4 periodic reviews and evidence collection — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-6-4
Practical step-by-step guidance to automate ECC 1-6-4 periodic reviews and...
Read more →
How to Use Firewalls, ACLs, and NGFWs to Achieve NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - SC.L2-3.13.6 Compliance
Practical guidance for implementing firewalls, ACLs, and NGFW controls to...
Read more →
How to scan every device (servers, desktops, laptops, VMs, containers, firewalls, switches, printers) for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - RA.L2-3.11.2 compliance
Practical, step-by-step guidance to discover, scan, and remediate vulnerabilities across...
Read more →
How to Sanitize Devices for Off‑Site Maintenance: NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - MA.L2-3.7.3 Implementation Checklist
Step-by-step implementation checklist to sanitize devices prior to off-site maintenance...
Read more →
How to run a risk-based periodic review of BYOD and corporate mobile device controls with a step-by-step checklist — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-6-4
A practical, step-by-step guide to performing a risk-based periodic review...
Read more →
How to Prepare for an Audit: Evidence Collection for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SC.L1-B.1.X Boundary Monitoring
Practical guidance and an evidence checklist to prepare small businesses...
Read more →
How to Prepare for a CMMC Assessment by Implementing Effective Plans of Action — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - CA.L2-3.12.2
Practical guidance for building and managing Plans of Action (POA&Ms)...
Read more →
How to Prepare for a CMMC 2.0 Level 2 Assessment: Passing PS.L2-3.9.1 Screening Requirements with Practical Steps — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - PS.L2-3.9.1
Practical, step-by-step guidance for meeting CMMC 2.0 Level 2 /...
Read more →
How to Prepare Audit-Ready Network Security Management Documentation and Approvals: A Practical Implementation Guide for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-5-1
Concrete steps, templates, and technical examples to build audit-ready network...
Read more →
How to Prepare an Audit-Ready Incident Response Program for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-13-3 in 8 Practical Steps
Practical, audit-focused guidance to build an incident response program that...
Read more →
How to Perform Maintenance on Organizational Systems to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - MA.L2-3.7.1: A Step-by-Step Implementation Guide
Practical, step-by-step guidance for small organizations to implement MA.L2-3.7.1 (Perform...
Read more →
How to Map Your Backup & Recovery Procedures to Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-9-4 with Templates and Evidence
Learn a step-by-step method to align your backup and recovery...
Read more →
How to Implement Visitor Escorting and Monitoring for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - PE.L1-B.1.IX: Step-by-Step Checklist
Practical, step-by-step checklist to implement visitor escorting and monitoring required...
Read more →
How to Implement USB and Removable Media Controls to Comply with NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AC.L2-3.1.21: A Step-by-Step Guide
Practical, step-by-step guidance to implement USB and removable media controls...
Read more →
How to Implement Subnetworks in AWS/GCP/Azure for Publicly Accessible Components — FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SC.L1-B.1.XI Cloud Implementation Steps
Practical, platform-specific steps to place public-facing cloud components in dedicated...
Read more →
How to Implement Session Timeout Rules in Cloud Environments (AWS/Azure) — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - SC.L2-3.13.9
Practical guidance to implement automatic session termination in AWS and...
Read more →
How to Implement Plans of Action to Correct Deficiencies and Reduce Vulnerabilities — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - CA.L2-3.12.2 (Template + Timeline)
Step-by-step guidance, a reusable POA&M template, and pragmatic timelines to...
Read more →
How to Implement File, Web, and Email Scanning to Comply with FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SI.L1-B.1.XIII: Tools, Settings, and Best Practices
Practical guidance for small businesses on implementing file, web, and...
Read more →
How to Implement Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 4-1-1: 7 Practical Steps to Ensure Third-Party Agreements Meet Cybersecurity Requirements
Step-by-step guidance for Control 4-1-1 of the ECC 2:2024 Compliance...
Read more →
How to Implement Encrypted, Immutable Backups to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-9-3
Step-by-step guidance for implementing encrypted, immutable backups to satisfy Compliance...
Read more →
How to Implement Cloud Subnet Segmentation for Public-Facing Services (AWS/Azure/GCP): Hands-On Steps for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SC.L1-B.1.XI
Step-by-step guidance to segment public-facing cloud subnets across AWS, Azure,...
Read more →
How to Implement Background Checks and Screening Policies for CUI Access: NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - PS.L2-3.9.1
Practical, step-by-step guidance for implementing workforce screening and background-check policies...
Read more →
How to Implement Automated Patch and Remediation Workflows Aligned with NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - RA.L2-3.11.3
Practical, step-by-step guidance for building automated patching and remediation workflows...
Read more →
How to Implement Audit Record Reduction and Report Generation for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AU.L2-3.3.6: A Step-by-Step Guide
Practical, step-by-step guidance to implement audit record reduction and automated...
Read more →
How to Implement a Visitor Monitoring Program and Audit Logs for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - PE.L1-B.1.IX: Template & Best Practices
Practical, step-by-step guidance and templates to implement visitor monitoring and...
Read more →
How to Implement a Step-by-Step Network Security Review Checklist for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-5-4
Step-by-step guidance to implement an auditable network security review checklist...
Read more →
How to Implement a Security Impact Analysis Process for Changes: NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - CM.L2-3.4.4 (Step-by-Step Checklist)
Step-by-step guidance for building a repeatable Security Impact Analysis (SIA)...
Read more →
How to Follow a Step-by-Step Implementation Checklist to Identify Users, Processes, and Devices for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - IA.L1-B.1.V
A practical step-by-step checklist to inventory and authorize users, processes,...
Read more →
How to Deploy SIEM for Inbound/Outbound Traffic Monitoring: Step-by-Step for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - SI.L2-3.14.6
Step-by-step practical guide to deploying SIEM monitoring for inbound and...
Read more →
How to Deploy Multi-Factor Authentication for Authorized Users and Systems — FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.I
Practical, step-by-step guidance on deploying multi-factor authentication to meet FAR...
Read more →
How to Deploy MFA and SSO to Meet FAR 52.204-21 / CMMC 2.0 Level 1 - Control - IA.L1-B.1.VI (Small Contractor Guide)
Step-by-step guidance for small contractors to implement MFA and SSO...
Read more →
How to Deploy EDR and Anti-Malware Across Your Network: Practical Implementation for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - SI.L2-3.14.2
Practical, step-by-step guidance for deploying endpoint detection & response (EDR)...
Read more →
How to Create an Authorizing Official Approval Workflow for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-4-1: Templates and Checklist
Step-by-step guidance and ready-to-use templates to implement an Authorizing Official...
Read more →
How to Create a Compliant Maintenance Policy to Perform Maintenance on Organizational Systems — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - MA.L2-3.7.1
Step-by-step guidance to build a NIST SP 800-171/CMMC-compliant maintenance policy...
Read more →
How to Configure Visitor Management and Badging for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - PE.L1-B.1.VIII: Practical Implementation for Small Defense Contractors
Step-by-step, low-cost guidance for small defense contractors to implement visitor...
Read more →
How to Configure Multi-Factor Authentication to Meet FAR 52.204-21 / CMMC 2.0 Level 1 - Control - IA.L1-B.1.VI Compliance
Step-by-step guidance for small businesses to configure and document multi-factor...
Read more →
How to Configure MFA Across On-Prem and Cloud Systems to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - IA.L2-3.5.3: Implementation Plan
Step-by-step plan to deploy multi-factor authentication across on-premises and cloud...
Read more →
How to Configure MDM to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AC.L2-3.1.19 and Encrypt CUI on Mobile Devices and Mobile Computing Platforms
Step-by-step MDM guidance to enforce encryption of CUI on mobile...
Read more →
How to Configure Logging, Monitoring, and Alerting to Satisfy Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-13-3
Step-by-step guidance to implement centralized logging, monitoring, and alerting that...
Read more →
How to Configure Identity and Access Management to Meet FAR 52.204-21 / CMMC 2.0 Level 1 - Control - IA.L1-B.1.V: Practical Implementation Checklist
Step-by-step, actionable guidance for configuring Identity and Access Management to...
Read more →
How to Configure Endpoint Controls to Enforce NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - MP.L2-3.8.7: USB Blocking, Whitelisting, and Encryption
Practical step-by-step guidance to block, whitelist, and require encryption for...
Read more →
How to Configure AWS VPC Subnetworks for Public-Facing Systems to Comply with FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SC.L1-B.1.XI
Practical step-by-step guidance for designing AWS VPC subnetworks so public-facing...
Read more →
How to Conduct Risk Assessments for Cloud Migrations: Implementation Checklist and Common Pitfalls | Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-5-3
Step-by-step guide to performing risk assessments for cloud migrations to...
Read more →
How to Conduct a Gap Analysis for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-7-2: Identify, Prioritize, and Remediate Agreement-Based Requirements
Practical step-by-step guidance to identify, prioritize, and remediate contract- and...
Read more →
How to Complete Compliance in 7 Steps: Identify Users, Processes, and Devices for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - IA.L1-B.1.V
A practical 7-step guide to inventory and map users, processes,...
Read more →
How to Build an SIEM-Based Workflow to Monitor System Security Alerts and Advisories for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - SI.L2-3.14.3
Step-by-step guidance to design an SIEM workflow that ingests alerts...
Read more →
How to Build an Effective POA&M for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - CA.L2-3.12.2: Step-by-Step Implementation Guide
Practical, step-by-step guidance for small businesses to create and maintain...
Read more →
How to build an ECC 2-7-3 compliant data inventory, classification, and handling workflow : Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-7-3
Step-by-step guidance to build a repeatable, auditable data inventory, classification,...
Read more →
How to Build an Automated Vulnerability Review Process to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-10-4 Requirements
Practical guidance to design and operate an automated vulnerability review...
Read more →
How to Build an Audit-Ready Plan to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-3-2: Practical Compliance Checklist
Practical, step-by-step guidance to implement Control 2-3-2 of the ECC...
Read more →
How to Build a Vulnerability Management Program to Satisfy Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-10-2: Asset Inventory, Scanning, and Patching
Step-by-step guidance to implement asset inventory, vulnerability scanning, and patching...
Read more →
How to Build a Timely Flaw Identification and Reporting Process for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SI.L1-B.1.XII (Checklist & Templates)
Practical steps, checklists, and ready-to-use templates for small businesses to...
Read more →
How to Build a Step-by-Step Audit Checklist for Periodic Cybersecurity Requirement Reviews of Business Continuity Management — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 3-1-4
Step-by-step guidance to create an audit checklist that ensures your...
Read more →
How to Build a Practical Access Control Checklist for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.I Compliance
Step-by-step guidance and a practical checklist to implement access control...
Read more →
How to Build a Dedicated Cybersecurity Department Independent from IT: Compliance Checklist for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-2-1
Practical, step-by-step guidance to establish an independent cybersecurity department to...
Read more →
How to Build a CUI Media Access and Transport Policy for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - MP.L2-3.8.5: Templates, Procedures, and Enforcement
Step-by-step guidance, templates, and technical controls to create a CUI...
Read more →
How to Build a Compliance Checklist for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - PE.L1-B.1.IX: Escorting, Monitoring, and Logging Requirements
Practical steps to implement escorting, monitoring, and logging controls required...
Read more →
How to build a compliance checklist for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-3-2 and verify protection of information systems
Step-by-step guidance to create a practical, evidence-based compliance checklist for...
Read more →
How to Build a Compliance Checklist and Implementation Timeline to Limit Physical Access for DoD Contractors — FAR 52.204-21 / CMMC 2.0 Level 1 - Control - PE.L1-B.1.VIII
Step-by-step guidance and a ready-to-use checklist plus timeline to limit...
Read more →
How to Automate User Deprovisioning to Comply with NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - PS.L2-3.9.2: Tools and Best Practices
Practical guide to automating user deprovisioning to satisfy NIST SP...
Read more →
How to Automate Periodic Review of Cybersecurity Requirements in Your Project Management Tools — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-6-4
Practical, step-by-step guidance to automate mandatory periodic reviews of cybersecurity...
Read more →
How to Assess and Authorize Cloud and SaaS Integrations to Meet FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.III
Practical, step-by-step guidance for small businesses to assess and authorize...
Read more →
Step-by-Step Implementation Checklist: Escort Visitors, Monitor Activity, and Manage Access Devices for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - PE.L1-B.1.IX
A practical, step-by-step implementation checklist to help small businesses meet...
Read more →
Step-by-Step: How to Encrypt CUI in Transit Over Networks Using TLS and SFTP for Compliance — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - MP.L2-3.8.6
Practical, audit-ready steps to encrypt Controlled Unclassified Information (CUI) in...
Read more →
Step-by-Step Guide: Implementing Technical and Organizational Measures to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-7-2 Compliance
Practical, step-by-step guidance to implement the technical and organizational measures...
Read more →
Step-by-Step Guide: Implementing Periodic Risk Assessments for Organizational Operations (CUI) — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - RA.L2-3.11.1
Practical, step-by-step guidance to implement periodic risk assessments for organizational...
Read more →
Step-by-Step Guide: Implementing Endpoint Detection and Response for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - SI.L2-3.14.2
Practical, step-by-step guidance to select, deploy, tune, and document Endpoint...
Read more →
Network Segmentation Best Practices: Implementing Subnetworks for Public Systems (FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SC.L1-B.1.XI)
Practical guidance for isolating publicly accessible systems into subnetworks to...
Read more →
How to Use Templates and Checklists to Meet Personnel Review Requirements in Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-9-6
Step-by-step guidance, templates, and checklists to help organizations meet the...
Read more →
How to Use SIEM and Vulnerability Scanning to Satisfy NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - CA.L2-3.12.3
Practical steps to combine SIEM and vulnerability scanning to meet...
Read more →
How to Use PAM and MFA to Enforce NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AC.L2-3.1.15: Practical Implementation Steps
Step-by-step guidance for small organizations to implement Privileged Access Management...
Read more →
How to Use Free and Low-Cost Tools to Satisfy FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SI.L1-B.1.XII: Quick Identification and Timely Correction of System Flaws
Practical, low-cost approaches and tool choices to quickly find and...
Read more →
How to Use Access Control Tools to Meet FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.I: Configuring AD, MFA, and Network Segmentation
Practical, step-by-step guidance for configuring Active Directory, multi-factor authentication, and...
Read more →
How to Train Remote and Hybrid Teams to Recognize and Report Insider Threats: Implementation Checklist — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AT.L2-3.2.3
Step-by-step, audit-ready checklist to train remote and hybrid teams to...
Read more →
How to Track, Document, and Report Incidents Using SIEM and Ticketing Systems for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - IR.L2-3.6.2
Practical guidance for small businesses on using SIEM and ticketing...
Read more →
How to Produce Compliance Evidence: Documentation Templates for Enforcing CUI Safeguards at Alternate Work Sites — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - PE.L2-3.10.6
Practical templates and evidence collection steps to enforce Controlled Unclassified...
Read more →
How to Prepare for an Audit of Your Cybersecurity Function: Evidence and Documentation for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-2-1
Step-by-step guidance and practical evidence templates to prepare your cybersecurity...
Read more →
How to Prepare for an Audit of FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SC.L1-B.1.X: Evidence, Common Findings, and Remediation Steps
Practical, step-by-step guidance for small businesses to prepare audit evidence,...
Read more →
How to Prepare for an Audit: Evidence of Boundary Monitoring for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SC.L1-B.1.X (Templates & Logs)
Practical, step-by-step guidance and evidence templates to demonstrate boundary monitoring...
Read more →
How to Prepare Evidence and Pass an Assessment for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - PE.L2-3.10.1: Implementation Checklist
Concrete, step-by-step guidance on preparing evidence and passing an assessment...
Read more →
How to Meet FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SI.L1-B.1.XII: Step-by-Step Checklist for Identifying, Reporting, and Correcting Flaws
Practical step-by-step checklist to identify, report, and remediate system flaws...
Read more →
How to Maintain Separation of Duties and Avoid Conflicts of Interest in ECC Role Assignments (Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-4-1)
Practical guidance for implementing Separation of Duties and preventing conflicts...
Read more →
How to Implement User, Process, and Device Identification Controls to Achieve FAR 52.204-21 / CMMC 2.0 Level 1 - Control - IA.L1-B.1.V Compliance
Practical, step-by-step guidance for small businesses to implement user, process,...
Read more →
How to Implement Role-Based Access and Least Privilege for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.II: A Step-by-Step Guide
Practical, step-by-step guidance to implement role-based access control and least...
Read more →
How to Implement Patch Management as Part of Performing Maintenance on Organizational Systems — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - MA.L2-3.7.1
Learn a practical, audit-ready approach to implementing patch management as...
Read more →
How to Implement NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - PE.L2-3.10.4: Step-by-Step Guide to Maintaining Audit Logs of Physical Access
A practical, step-by-step guide to implement and maintain tamper-resistant physical...
Read more →
How to Implement MFA to Authenticate Identities for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - IA.L1-B.1.VI: Step-by-Step Deployment for Users, Processes, and Devices
Practical, step-by-step guidance for implementing multifactor authentication (MFA) to meet...
Read more →
How to implement MFA for users, processes, and devices to meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - IA.L2-3.5.2
Practical, step-by-step guidance to deploy multifactor authentication for users, processes,...
Read more →
How to Implement FAR 52.204-21 / CMMC 2.0 Level 1 - Control - PE.L1-B.1.VIII: Step-by-Step Guide to Limiting Physical Access to Information Systems
Practical, step-by-step guidance for small businesses to meet FAR 52.204-21...
Read more →
How to Implement Employee Screening for CUI Access: Step-by-Step Guide to NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - PS.L2-3.9.1
Step-by-step practical guidance to implement personnel screening for Controlled Unclassified...
Read more →
How to Implement AWS Subnetworks for Public-Facing Systems to Satisfy FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SC.L1-B.1.XI: Terraform and Best Practices
Step-by-step guidance to design and deploy AWS public and private...
Read more →
How to Implement Automated Vulnerability Scanning and Reporting for External Web Apps to Satisfy Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-15-4
Practical step-by-step guidance to implement automated external web application vulnerability...
Read more →
How to Implement Automated Scanning and Manual Validation for Periodic External Web App Reviews | Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-15-4
Step-by-step guidance to combine automated external web application scanning with...
Read more →
How to Implement an Auditable Physical Protection Policy for IT Assets: A Step-by-Step Checklist — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-14-1
Practical, auditable steps to implement Control 2-14-1 of the Compliance...
Read more →
How to Implement a Small-Business Friendly Physical Access Control Checklist for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - PE.L1-B.1.VIII
Step-by-step, small-business friendly guidance to meet FAR 52.204-21 and CMMC...
Read more →
How to Implement a Periodic Data Handling Review for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-7-4: A Step-by-Step Compliance Checklist
A practical, step-by-step checklist for meeting ECC 2-7-4 periodic data...
Read more →
How to Enforce Privileged Access Controls for Audit Logging in AWS/Azure with NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AU.L2-3.3.9
Practical guidance to enforce privileged access controls for protecting audit...
Read more →
How to Document Evidence of Malicious Code Protection for Audits: Templates and Examples for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SI.L1-B.1.XIII
Step-by-step guidance and ready-to-use templates for documenting malicious code protection...
Read more →
How to Document and Prove Compliance with Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-2-2 (Code 434): Evidence for Audits Showing Full-Time Saudi Cybersecurity Positions
Practical guidance for collecting, organizing, and presenting audit-ready evidence that...
Read more →
How to Deploy Network and Endpoint Controls for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-3-2: Practical Configuration Checklist
Step-by-step configuration checklist and real-world examples to deploy network and...
Read more →
How to Deploy a Visitor Management System Integrated with Audit Logging for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - PE.L1-B.1.IX
Step-by-step guidance for deploying a visitor management solution that integrates...
Read more →
How to Create Evidence-Based Offboarding Documentation for Assessors: Templates and Examples — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - PS.L2-3.9.2
Practical guidance and ready-to-use templates to produce evidence-based offboarding artifacts...
Read more →
How to Create and Document Cybersecurity Roles and Responsibilities to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-4-1 (Includes Templates)
[Write a compelling 1-sentence SEO description about this compliance requirement]...
Read more →
How to Create an Incident Report Template and Evidence Trail for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - IR.L2-3.6.2
A practical guide for small businesses to build an incident...
Read more →
How to Create an Implementation Checklist for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - IA.L1-B.1.V: Identify Users, Processes, and Devices
Step-by-step checklist and practical guidance for small businesses to identify...
Read more →
How to create an audit-ready VoIP compliance checklist for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - SC.L2-3.13.14
Step-by-step guidance to build an audit-ready VoIP security checklist that...
Read more →
How to Create an Audit-Ready Checklist for Periodic Reviews of Physical Protection — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-14-4
Practical, audit-ready checklist and step-by-step guidance to meet ECC 2-14-4...
Read more →
How to Create an Actionable Inventory to Meet FAR 52.204-21 / CMMC 2.0 Level 1 - Control - IA.L1-B.1.V: Identify Users and Devices for Compliance
Practical step-by-step guidance to build and maintain an auditable, actionable...
Read more →
How to Create a Third-Party Contract Review Checklist to Achieve ECC Compliance: Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 4-1-4
Practical step-by-step guidance and a vendor contract checklist to help...
Read more →
How to Create a Practical Implementation Plan for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.III Including Templates and Timelines
Practical, step-by-step guidance and templates to implement the FAR 52.204-21...
Read more →
How to Create a Practical Audit Checklist for Physical Protection Compliance — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-14-4
Step-by-step guidance to build an audit-ready, pragmatic checklist that verifies...
Read more →
How to Create a Compliant System Security Plan (SSP) for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - CA.L2-3.12.4: Step-by-Step Template and Examples
Practical step-by-step guidance to build an SSP that addresses CMMC...
Read more →
How to Configure Web and Cloud Settings for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.IV Compliance: A Practical Checklist
Practical, step-by-step checklist for configuring web and cloud settings to...
Read more →
How to Configure SIEM Rules and Alerting to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - SI.L2-3.14.3 for Monitoring Alerts and Advisories
Practical, step-by-step guidance to configure SIEM rules, ingest advisories, correlate...
Read more →
How to Choose Between Software Erasure, Degaussing, and Physical Destruction for FCI: Decision Guide for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - MP.L1-B.1.VII
A practical decision guide for small businesses on choosing software...
Read more →
How to Choose Authentication Technologies to Satisfy FAR 52.204-21 / CMMC 2.0 Level 1 - Control - IA.L1-B.1.VI: Comparison and Implementation Tips
Practical guidance for selecting and implementing authentication technologies that meet...
Read more →
How to Build and Approve an ECC Organizational Chart: Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-4-1 Implementation Checklist
Step-by-step guide to build, document, and approve an ECC organizational...
Read more →
How to Build an MFA and SSO Implementation Plan for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - IA.L1-B.1.VI (Checklist & Configs)
Step-by-step plan, checklist, and sample configurations to implement MFA and...
Read more →
How to Build an Incident Response Playbook to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-13-2 Requirements
Step-by-step guidance to build an incident response playbook that satisfies...
Read more →How to Build an Audit-Ready POA&M Template and Tracking Dashboard — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - CA.L2-3.12.2
Step-by-step guidance to create an audit-ready POA&M template and tracking...
Read more →
How to build an audit-ready checklist for periodic reviews of external web applications to satisfy Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-15-4
Step-by-step guidance to create an audit-ready, evidence-driven checklist for periodic...
Read more →
How to Build a Step-by-Step Cloud Hosting Policy Template to Meet ECC 4-2-1 Requirements — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 4-2-1
A practical, step-by-step cloud hosting policy template to help organizations...
Read more →
How to build a step-by-step audit checklist for mobile device and BYOD periodic reviews — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-6-4
Practical, step‑by‑step guidance to build an audit checklist that ensures...
Read more →
How to Build a Periodic Vulnerability Scanning Program to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - RA.L2-3.11.2: Asset Discovery, Scheduling and Remediation Workflows
Step-by-step guidance for small businesses to implement asset discovery, scheduled...
Read more →
How to Build a Penetration Testing Review Checklist to Achieve Compliance with Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-11-4
Step-by-step guidance to create a penetration testing review checklist that...
Read more →
How to Build a Network Security Management Checklist for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-5-1 and Pass Audit Evidence
Step-by-step guidance to build a practical network security management checklist...
Read more →
How to Build a Compliant Onboarding and Offboarding Process for Personnel: Implementation Checklist for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-9-1
Practical, step-by-step checklist and technical controls to build compliant onboarding...
Read more →
How to Build a Compliant Cryptography Policy Template — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-8-1 (Code 492)
Step-by-step guidance to build a cryptography policy that satisfies ECC...
Read more →
How to Build a Compliance-Ready Screening Program for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - PS.L2-3.9.1 (Checklist + Templates)
A practical guide to designing and operationalizing a screening program...
Read more →
How to Build a BYOD Policy Template That Meets ECC 2-6-1 Mobile Device Security Requirements: Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-6-1
Step-by-step guidance to create a BYOD policy template that satisfies...
Read more →
How to Automate Periodic CUI Risk Assessments and Reporting: Tools, Workflows, and Metrics — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - RA.L2-3.11.1
Practical steps to automate periodic risk assessments and reporting for...
Read more →
How to Achieve Compliance with NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - RA.L2-3.11.2 Using Nessus: Implementation Guide and Scan Templates
Practical guidance for meeting RA.L2-3.11.2 (vulnerability scanning) of NIST SP...
Read more →
Compliance Checklist for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.III: Practical Steps to Control Use of External Information Systems
Practical, step-by-step guidance for small businesses to meet FAR 52.204-21...
Read more →
Checklist: Technical Controls and Configurations to Authenticate Identities under FAR 52.204-21 / CMMC 2.0 Level 1 - Control - IA.L1-B.1.VI
Practical checklist of technical controls and configuration examples to authenticate...
Read more →
Step-by-Step Implementation Checklist for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SC.L1-B.1.X to Monitor, Control, and Protect Organizational Communications
Practical, step-by-step guide for small businesses to meet FAR 52.204-21...
Read more →
Step-by-Step Guide to Creating an Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-10-1 Compliant Vulnerability Management Policy
Practical, step-by-step guidance to build a Control 2-10-1 compliant Vulnerability...
Read more →
Step-by-Step Guide: Deploying EDR, AV and Email Filtering to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - SI.L2-3.14.2
Practical step-by-step guidance for small businesses to deploy EDR, antivirus,...
Read more →
Implementation Checklist: Immediate Steps to Secure Systems After Termination or Transfer — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - PS.L2-3.9.2
A practical, step-by-step checklist to immediately secure systems and access...
Read more →
How to Use Phishing Simulations and Microlearning to Strengthen Culture: Practical Steps for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-10-1
Practical, audit-ready steps to implement phishing simulations and microlearning that...
Read more →
How to Test Email Controls (MFA, TLS, DLP, Anti-Phish) During Periodic Reviews for ECC Compliance — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-4-4
Step-by-step guidance to test MFA, TLS, DLP and anti-phishing email...
Read more →
How to Select and Configure Tools for File Scanning to Satisfy FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SI.L1-B.1.XV: Vendor Comparison and Implementation Tips
Practical, vendor-focused guidance to choose and configure file-scanning tools that...
Read more →
How to Select and Configure Endpoint Protection Tools to Satisfy NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - SI.L2-3.14.2: Vendor Evaluation and Tuning Guide
Practical, step-by-step guidance for selecting, evaluating, and tuning endpoint protection/EDR...
Read more →
How to Sanitize or Destroy Media Before Reuse: Practical Implementation Guide for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - MP.L1-B.1.VII
Step-by-step practical guidance for sanitizing or destroying media to meet...
Read more →
How to Prepare for an ECC 2-8-1 Audit: Practical Steps to Define, Document, and Get Cryptography Requirements Approved (Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-8-1)
Practical, step-by-step guidance for small businesses to define, document, and...
Read more →
How to Perform a Boundary Control Assessment Aligned to FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SC.L1-B.1.X: Checklist and Remediation Plan
Step-by-step guide to assess, document, and remediate system boundary controls...
Read more →
How to Pass an ECC Audit by Documenting Hosting and Cloud Requirements: Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 4-2-1 Compliance Roadmap
Learn step-by-step how to document hosting and cloud requirements to...
Read more →
How to Migrate Legacy Wi‑Fi to WPA3 Enterprise Without Disruption — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AC.L2-3.1.17
Step-by-step guidance to upgrade legacy Wi‑Fi to WPA3-Enterprise to meet...
Read more →
How to Measure and Report Security Awareness Effectiveness to Meet CMMC 2.0 Level 2 Requirements - NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AT.L2-3.2.1
Practical steps, metrics, and evidence templates for measuring and reporting...
Read more →
How to Integrate Third-Party MFA (Duo/Okta/Azure AD) for Remote and Local Privileged Users to Comply with NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - IA.L2-3.5.3
Practical steps and technical details to deploy Duo, Okta, or...
Read more →
How to Integrate Temporary Password Policies into SSO and Identity Providers — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - IA.L2-3.5.9: Okta/AzureAD/Google Workspace Implementation Tips
Practical guidance to implement temporary password and activation policies in...
Read more →
How to Implement Whitelisting and Application Control to Manage User-Installed Software (Practical Guide) — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - CM.L2-3.4.9
Step-by-step guide to implement whitelisting and application control to meet...
Read more →
How to Implement User and Device Identification to Meet FAR 52.204-21 / CMMC 2.0 Level 1 - Control - IA.L1-B.1.V
Practical steps for uniquely identifying and authenticating users and devices...
Read more →
How to Implement Physical Protection for Information and Technology Assets: A Step-by-step Guide to Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-14-3
Practical, step-by-step guidance to implement ECC 2-14-3 physical protection controls...
Read more →
How to Implement Periodic and Real-Time File Scanning for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SI.L1-B.1.XV: Step-by-Step Guide
Practical, step-by-step guidance to implement periodic and real-time file scanning...
Read more →
How to implement FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.III: Step-by-step guide to verify and limit connections to external information systems
Practical, step-by-step guidance for small businesses to verify and limit...
Read more →
How to implement Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-2-2: Practical checklist for vetting, credentialing, and onboarding experienced Saudi cybersecurity professionals
Practical, compliance-focused checklist to vet, credential, and securely onboard experienced...
Read more →
How to Implement ECC 1-5-3 Risk Assessment Procedures for Cloud Migrations — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-5-3 Migration Playbook
Step-by-step guidance to implement ECC 1-5-3 risk assessment procedures for...
Read more →
How to Implement Cryptography Requirements to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-8-2: A Step-by-Step Compliance Checklist
A practical, step-by-step checklist to implement cryptography controls required by...
Read more →
How to Implement Cloud-Based Subnetworks (AWS/Azure/GCP) for Publicly Accessible Components to Satisfy FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SC.L1-B.1.XI
[Write a compelling 1-sentence SEO description about this compliance requirement]...
Read more →
How to Implement Centralized Log Management to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AU.L2-3.3.1: Tools, Configurations, and Best Practices
Practical, step-by-step guidance for implementing centralized log management to satisfy...
Read more →
How to Implement Automated Updates for Antivirus to Meet FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SI.L1-B.1.XIV (Step-by-Step Guide)
Practical, step-by-step guidance to configure, verify, and document automated antivirus...
Read more →
How to Implement and Enforce Cybersecurity Policies: A Step-by-Step Guide for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-3-2
Step-by-step actionable guide to implement and enforce cybersecurity policies to...
Read more →
How to Implement a Periodic Vulnerability Review Process to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-10-4: Step-by-Step Guide
Step-by-step guidance to design and operate a periodic vulnerability review...
Read more →
How to Enforce Least Privilege and Role-Based Access for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-9-4
Practical, audit-ready guidance to implement least privilege and role-based access...
Read more →
How to Deploy Technical Controls (WAF, RBAC, Filtering) to Enforce FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.IV
Practical guide to using WAFs, RBAC, and filtering to meet...
Read more →
How to Deploy SIEM for Real-Time Monitoring and Alerting under Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-12-3
Step-by-step guidance to deploy and tune a SIEM for real-time...
Read more →
How to Deploy Phishing Simulations and Remediation Workflows to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-10-2
Learn practical steps to deploy phishing simulations and automated remediation...
Read more →
How to Deploy an Endpoint Protection Platform to Meet FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SI.L1-B.1.XIII (Checklist & Tool Selection)
Step-by-step guidance and a practical checklist to select, deploy, and...
Read more →
How to Demonstrate Compliance with NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - SI.L2-3.14.3: Logging, Reporting, and Evidence Collection
Practical steps, tools, and evidence examples to meet SI.L2-3.14.3 logging,...
Read more →
How to Create Audit-Ready Logging and Monitoring for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - SI.L2-3.14.7: Practical Implementation Checklist
Practical, audit-ready steps to implement logging and monitoring that meet...
Read more →
How to Create an SSP That Meets NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - CA.L2-3.12.4: Define Boundaries, Environments, and System Connections
Learn how to create a System Security Plan (SSP) that...
Read more →
How to Create an Audit-Ready Sanitization Checklist for FCI Under FAR 52.204-21 / CMMC 2.0 Level 1 - Control - MP.L1-B.1.VII
Step-by-step guidance to build an audit-ready media sanitization checklist that...
Read more →
How to Create an Audit-Ready Physical Access Policy Template for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - PE.L1-B.1.VIII
Step-by-step guidance to build an audit-ready physical access policy that...
Read more →
How to Create an Audit-Ready Incident Response Checklist to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - IR.L2-3.6.1
Step-by-step guide to building an audit-ready incident response checklist that...
Read more →
How to Create an Audit-Ready Checklist for Scanning Media Containing Diagnostic and Test Programs for Malicious Code — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - MA.L2-3.7.4
Practical step-by-step guidance to build an audit-ready checklist for scanning...
Read more →
How to Create a Practical SI.L1-B.1.XV Compliance Checklist: Periodic Scans and Real-Time External File Inspection for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SI.L1-B.1.XV
Step‑by‑step guidance and a practical checklist to implement SI.L1-B.1.XV: periodic...
Read more →
How to Configure Web and Cloud Settings to Meet FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.IV: Practical Implementation for SMBs
Practical, step-by-step guidance for small and medium businesses to configure...
Read more →
How to configure SPF, DKIM and DMARC for compliance with Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-4-2
Step-by-step guidance for configuring SPF, DKIM and DMARC to meet...
Read more →
How to Configure SIEM and Schedule Reviews of Event Logs and Monitoring Management for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-12-4
Step-by-step guidance to configure your SIEM, define log collection and...
Read more →
How to Configure NTP and Chrony on Windows and Linux to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AU.L2-3.3.7
Step-by-step guidance to configure reliable, auditable, and secure time synchronization...
Read more →
How to Configure Multi-Factor Authentication to Meet FAR 52.204-21 / CMMC 2.0 Level 1 - Control - IA.L1-B.1.VI Requirements
Step-by-step guidance for small businesses to implement secure, compliant multi-factor...
Read more →
How to Configure Key Management and Lifecycle Controls to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-8-3 Requirements
Learn step-by-step how to implement key management and lifecycle controls...
Read more →
How to Configure Active Directory and SSO to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - IA.L2-3.5.5: Preventing Identifier Reuse
Practical steps to configure Active Directory and cloud SSO so...
Read more →
How to Configure Access Control Systems and Audit Trails for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - PE.L1-B.1.IX: Practical Setup Guide
Step-by-step guide to implementing access controls and tamper-proof audit trails...
Read more →
How to Conduct Effective Quarterly Business Continuity Cybersecurity Reviews to Meet ECC – 2 : 2024 - Control - 3-1-4
Step-by-step guidance for running quarterly business continuity cybersecurity reviews to...
Read more →
How to Choose and Use Media Sanitization Tools to Meet FAR 52.204-21 / CMMC 2.0 Level 1 - Control - MP.L1-B.1.VII Requirements
Practical guidance for selecting and using media sanitization tools —...
Read more →
How to Choose and Use Approved Tools to Sanitize or Destroy Hard Drives, SSDs, and USBs Holding FCI — FAR 52.204-21 / CMMC 2.0 Level 1 - Control - MP.L1-B.1.VII
Step-by-step guidance to select and operate approved sanitization and destruction...
Read more →
How to Choose and Configure AV/EDR Tools for External File Scanning: Practical Steps for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SI.L1-B.1.XV
Practical, step‑by‑step guidance for selecting and configuring AV/EDR file‑scanning controls...
Read more →
How to Build an Audit-Ready Training Program to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AT.L2-3.2.2: Step-by-Step Implementation
A practical, audit-focused guide to designing, deploying, and evidencing a...
Read more →
How to Build an Audit-Ready Asset Inventory and Periodic Review Workflows for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-1-6
Practical, step-by-step guidance to build an audit-ready asset inventory and...
Read more →
How to Build a Visitor & Badge Policy to Meet FAR 52.204-21 / CMMC 2.0 Level 1 - Control - PE.L1-B.1.VIII (Templates & Checklist)
A practical, step-by-step guide to creating a visitor and badge...
Read more →
How to Build a Secure Media Transport Policy for CUI: NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - MP.L2-3.8.5 with Template and Procedures
Step‑by‑step guidance, a ready policy template, and practical procedures to...
Read more →
How to Build a Practical Checklist for Limiting Physical Access to Systems and Environments — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - PE.L2-3.10.1
Step-by-step guide to creating a compliance-ready checklist to limit physical...
Read more →
How to Build a Media Sanitization Policy That Meets FAR 52.204-21 / CMMC 2.0 Level 1 - Control - MP.L1-B.1.VII: Templates and Procedures
Step-by-step guidance and ready-to-use templates to create a media sanitization...
Read more →
How to Build a Compliant BYOD Program Aligned with Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-6-1
Step-by-step guidance for small businesses to implement a compliant BYOD...
Read more →
How to Build a Compliance-Ready Asset Requirements Policy for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-1-1 with Templates and Examples
[Write a compelling 1-sentence SEO description about this compliance requirement]...
Read more →
How to Build a Compliance-Ready Acceptable Use Policy Template (AUP) — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-1-4
Step-by-step guidance to create an Acceptable Use Policy (AUP) that...
Read more →
How to Build a Compliance Checklist for Verifying and Limiting External Information Systems (FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.III)
Step-by-step guidance to build a practical compliance checklist for verifying...
Read more →
How to Automate Periodic Reviews of Physical Protection Controls with Tools and Templates — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-14-4
Practical, tool-driven guidance to automate periodic reviews of physical protection...
Read more →
How to Automate Compliance for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - IA.L2-3.5.6 Using Azure AD and Conditional Access to Disable Inactive Identifiers
Practical guide to automating IA.L2-3.5.6 (disable inactive identifiers) using Azure...
Read more →
How to Automate Account Deprovisioning to Secure CUI and Comply with NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - PS.L2-3.9.2
Automate account deprovisioning to protect CUI and meet NIST SP...
Read more →
How to Audit and Verify Physical Access Records for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - PE.L1-B.1.IX: A Compliance Checklist
A practical, step-by-step checklist for auditing and verifying physical access...
Read more →
How to Apply Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-6-3 to Your DevSecOps Pipeline: Concrete Steps to Compliance
Step-by-step guidance to implement ECC–2:2024 Control 1‑6‑3 in your DevSecOps...
Read more →
From Zero to Compliant: Build an Operational Incident-Handling-Capability Covering Preparation, Detection, Analysis, Containment, Recovery and User Response for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - IR.L2-3.6.1
A practical, step-by-step guide to implement an operational incident-handling capability...
Read more →
Checklist: 10 Actionable Steps to Make Staff Aware of Security Risks and Policies for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AT.L2-3.2.1
Practical 10-step checklist to ensure managers, admins, and users understand...
Read more →Step-by-Step: Implement Automated Security Alerting and Advisory Tracking for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - SI.L2-3.14.3
Practical, step-by-step guidance to design and operate automated security alerting...
Read more →
Step-by-Step: Implement AT.L2-3.2.1 Awareness Training with Templates, Schedules, and Evidence — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AT.L2-3.2.1
Practical, step-by-step guidance for implementing AT.L2-3.2.1 awareness training — templates,...
Read more →
Step-by-Step Guide to Implementing Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-8-3: Creating Audit Reports That Include Scope, Findings, Recommendations and Remediation Plans
Practical guidance for producing Compliance Framework–aligned audit reports that clearly...
Read more →
Implementation Checklist: 10 Practical Controls to Limit Physical Access to Organizational Information Systems and Equipment — FAR 52.204-21 / CMMC 2.0 Level 1 - Control - PE.L1-B.1.VIII
Practical, step-by-step checklist for small businesses to meet FAR 52.204-21...
Read more →
How to write a backup and recovery review policy that meets Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-9-4 requirements
Step-by-step guidance to create a backup and recovery review policy...
Read more →
How to Use Templates and Checklists to Implement Technical Security Standards for ECC Compliance — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-3-3
Practical guidance on creating and using templates and checklists to...
Read more →
How to Use Simple, Low-Cost Physical Controls to Limit Access for Small Contractors — FAR 52.204-21 / CMMC 2.0 Level 1 - Control - PE.L1-B.1.VIII
Practical, low-cost physical controls and implementation guidance to help small...
Read more →
How to use network segmentation and zero-trust principles to verify and restrict external connections for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.III
Practical guide to using network segmentation and zero-trust controls to...
Read more →
How to Use Least Privilege and RBAC to Secure Audit Logging Functions in AWS/Azure/GCP — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AU.L2-3.3.9
Practical guidance to implement least privilege and RBAC to protect...
Read more →
How to Use Configuration Management Tools to Enforce Technical Security Standards for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-3-3
Practical step-by-step guidance for using configuration management tools (Ansible, Puppet,...
Read more →
How to Use Checklists and Templates to Conduct Periodic Reviews of Business Continuity Cybersecurity Requirements: Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 3-1-4
Practical guidance on building and using checklists and templates to...
Read more →
How to Separate Cybersecurity from IT/ICT Without Disrupting Operations: A Practical Roadmap (Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-2-1)
Practical, phased guidance to implement ECC‑2:2024 Control 1‑2‑1—separating cybersecurity from...
Read more →
How to Select and Tune File-Scanning Tools for External Source Protection Under NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - SI.L2-3.14.5
Practical guidance to choose and tune file-scanning tools that detect...
Read more →
How to Select and Deploy AV, EDR, and DLP Tools to Satisfy NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - SI.L2-3.14.5
Practical guidance for selecting, configuring, and evidencing antivirus, endpoint detection...
Read more →
How to Secure Removable Media and Endpoints for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - MP.L2-3.8.2: Tools, Configurations, and Best Practices
Practical, technical guidance for small businesses to meet MP.L2-3.8.2 by...
Read more →
How to Run a Gap Assessment and Remediate for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.I: Actionable Checklist for Limiting System Access
[Write a compelling 1-sentence SEO description about this compliance requirement]...
Read more →
How to Prevent Insider Threats by Implementing Personnel Cybersecurity Controls: Operational Steps for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-9-2
Operational, audit-ready steps to implement ECC–2:2024 Control 1-9-2 personnel cybersecurity...
Read more →
How to Prepare for an Audit: Demonstrating Compliance with FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.III by Verifying and Limiting External Information Systems
Practical steps for small businesses to verify and limit external...
Read more →
How to Migrate Cybersecurity Responsibilities from IT to a Dedicated Team: A 90-Day Implementation Plan — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-2-1
Step-by-step 90-day plan to transition cybersecurity responsibilities from IT to...
Read more →
How to Measure Effectiveness of Customized Cybersecurity Training for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-10-4: Metrics & KPIs
Practical guidance on defining, instrumenting, and reporting Metrics & KPIs...
Read more →
How to Measure and Report Effectiveness of Your Cybersecurity Awareness Program for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-10-1
Practical, audit-ready guidance for measuring and reporting the effectiveness of...
Read more →
How to Integrate Vulnerability Scanning and Pen Testing into Periodic External Web App Reviews to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-15-4
Practical guidance for small teams to combine automated vulnerability scanning...
Read more →
How to Integrate Threat Detection and Event Log Review into Your Compliance Program: Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-12-4
A practical guide to implementing threat detection and event log...
Read more →
How to Integrate CCTV, Badge, and Visitor Logs into a Centralized Audit Trail for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - PE.L2-3.10.4
Practical steps for small businesses to centrally collect, correlate, and...
Read more →
How to Implement Segregation of Duties: Step‑by‑Step Guide for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AC.L2-3.1.4
Step-by-step, practical implementation guidance to meet NIST SP 800-171 Rev.2...
Read more →
How to Implement Secure Remote Maintenance: Tools, Techniques, and Personnel Controls for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - MA.L2-3.7.2
Practical guidance for implementing secure, auditable remote maintenance that protects...
Read more →
How to Implement Periodic and Real-Time File Scanning to Meet FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SI.L1-B.1.XV: A Step-by-Step Guide
Step-by-step, practical guidance for implementing periodic and real-time file scanning...
Read more →
How to Implement Password History and Complexity Settings in Azure AD to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - IA.L2-3.5.8
Step-by-step guidance to configure password history, complexity and compensating controls...
Read more →
How to Implement NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - PE.L2-3.10.3: Step-by-Step Guide to Escort Visitors and Monitor Visitor Activity
Practical, step-by-step guidance for small businesses to meet PE.L2-3.10.3 by...
Read more →
How to Implement NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - MA.L2-3.7.2: Step-by-Step Guide to Controlling Maintenance Tools, Techniques, Mechanisms, and Personnel
Step-by-step guidance to control maintenance tools, techniques, mechanisms, and personnel...
Read more →
How to Implement FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SC.L1-B.1.X: Firewall and Proxy Configuration Checklist to Control Organizational Communications
Step-by-step checklist and real-world examples to configure firewalls and proxies...
Read more →
How to Implement Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-15-3 for External Web Applications: Step-by-Step Compliance Checklist
Step-by-step checklist to implement Control 2-15-3 of the Compliance Framework...
Read more →
How to Implement Employee and Contractor Screening for CUI Access — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - PS.L2-3.9.1 Step-by-Step
Step-by-step guidance for implementing employee and contractor screening to meet...
Read more →
How to Implement Contractual Cybersecurity Requirements and Review Clauses with a Template — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 4-1-4
Step-by-step guidance and an editable contract clause template to implement...
Read more →
How to implement automated notifications and evidence capture for policy reviews to meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-3-4
Step-by-step guidance for automating policy review notifications and tamper-evident evidence...
Read more →
How to Implement a Low-Cost Physical Access Control Solution Aligned with FAR 52.204-21 / CMMC 2.0 Level 1 - Control - PE.L1-B.1.IX
Practical, low-cost steps for small businesses to meet FAR 52.204-21...
Read more →
How to Draft and Document Cybersecurity Policies That Pass Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-3-1: A Practical Implementation Checklist
Step-by-step checklist and practical templates to draft, approve, document, and...
Read more →
How to Draft an ECC-Aligned Acceptable Use Policy (Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-1-4) with Template and Real-World Examples
Practical guidance and a ready-to-use template to create an ECC-aligned...
Read more →
How to Document, Approve, and Enforce BYOD Requirements for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-6-1: Policy Templates Included
Step-by-step guidance and ready policy snippets to document, approve, and...
Read more →
How to Document and Evidence Contract Cybersecurity Compliance: Templates and Checklists for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 4-1-1
Practical guidance and ready-to-use contract clauses, evidence checklists, and implementation...
Read more →
How to Deploy Low-Cost Physical Access Solutions for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - PE.L1-B.1.VIII: Affordable Hardware and Process Changes for Small Contractors
Step-by-step, low-cost options and processes to meet FAR 52.204-21 and...
Read more →How to Deploy Lightweight Identity Tracking for Small Contractors to Satisfy FAR 52.204-21 / CMMC 2.0 Level 1 - Control - IA.L1-B.1.V
Practical, low-cost steps for small contractors to implement identity tracking...
Read more →
How to Create an Access Control Policy and Checklist for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.II Compliance
Practical, step-by-step guidance to build an access control policy and...
Read more →
How to Create an Access Control Checklist for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AC.L2-3.1.1: Audit-Ready Steps and Templates
Step-by-step guide with templates to build an audit-ready access control...
Read more →
How to Create a Compliance Checklist for Updating Malicious Code Protection (FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SI.L1-B.1.XIV)
Step-by-step guidance and a practical checklist to ensure your malicious...
Read more →
How to Create a Compliance Checklist and Schedule for Periodic Reviews of Information Systems - Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-3-4
Step-by-step guidance to build a Compliance Framework checklist and schedule...
Read more →
How to Create a Compliance Checklist and Implementation Plan for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SC.L1-B.1.X
A practical, step-by-step checklist and implementation plan to help small...
Read more →
How to Configure Windows, macOS, and Linux to Enforce Removable Media Restrictions — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - MP.L2-3.8.7
Step-by-step guidance to configure Windows, macOS, and Linux to control...
Read more →
How to Configure Windows Active Directory to Limit Unsuccessful Logon Attempts (NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AC.L2-3.1.8)
Configure Active Directory account lockout policies to meet NIST SP...
Read more →
How to Configure SSH, RDP and Cloud Console Idle Timeouts for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - SC.L2-3.13.9
Step-by-step guidance to enforce idle session timeouts for SSH, RDP...
Read more →
How to Configure Multi-Factor Authentication to Satisfy FAR 52.204-21 / CMMC 2.0 Level 1 - Control - IA.L1-B.1.VI: Practical Setup and Validation Steps
Step-by-step guidance to deploy and validate multi-factor authentication to meet...
Read more →
How to Configure Identity Management for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - IA.L1-B.1.V: Implementing User and Device Identification with Azure AD and AD
Practical step-by-step guidance to implement user and device identification for...
Read more →
How to Configure Azure AD and AWS IAM to Block Non-Privileged Execution and Capture Logs for AC.L2-3.1.7 — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AC.L2-3.1.7
Step-by-step guidance to configure Azure AD and AWS IAM to...
Read more →
How to Configure Active Directory to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - IA.L2-3.5.6: Disable Inactive Identifiers Automatically
Step-by-step guidance to configure Active Directory to automatically disable inactive...
Read more →
How to Choose and Deploy Scanning Tools That Satisfy FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SI.L1-B.1.XV Requirements for External Files
Practical guidance for selecting, deploying, and evidencing file-scanning controls to...
Read more →
How to Build an Onboarding & Offboarding Process to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-9-2
Practical, step-by-step guidance to design automated and auditable onboarding and...
Read more →
How to Build an Identity Proofing and Verification Workflow for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - IA.L2-3.5.2 (Checklist + Recommended Tools)
Practical step-by-step guide to implement identity proofing and verification for...
Read more →
How to Build an Audit-Ready SI.L1-B.1.XII Compliance Checklist to Identify, Report, and Correct Flaws (FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SI.L1-B.1.XII)
Step-by-step guidance to implement SI.L1-B.1.XII to identify, report, and correct...
Read more →
How to Build an Audit-Ready Asset Inventory for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - IA.L1-B.1.V: Tools, Templates, and Implementation Steps
Practical, step-by-step guidance to create and maintain an audit-ready asset...
Read more →
How to Build a Step-by-Step Malicious Code Protection Checklist for Compliance — FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SI.L1-B.1.XIII
Step-by-step, practical guidance to build a malicious code protection checklist...
Read more →
How to Build a POA&M: Step-by-Step Guide to Developing and Implementing Plans of Action to Fix Vulnerabilities — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - CA.L2-3.12.2
Step-by-step guidance for small businesses to create, manage, and implement...
Read more →
How to Build a Patch and Definitions Management Workflow for Malicious Code Protection (NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - SI.L2-3.14.4)
Step-by-step guidance to design a repeatable patch and malware-definition management...
Read more →
How to Build a Compliant Media Disposal Procedure for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - MP.L1-B.1.VII: Tools, Templates, and Checklist
Step-by-step guidance, tools, templates, and a practical checklist to build...
Read more →
How to Build a Compliance Procedure for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - MP.L1-B.1.VII: Practical Steps, Templates, and Verification for Media Sanitization and Destruction
Step-by-step guidance to implement media sanitization and destruction controls to...
Read more →
How to Build a Compliance Checklist for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.IV to Protect Public-Facing Content
Practical, step-by-step guidance to create a Compliance Framework checklist that...
Read more →
How to Build a CIA-Aligned Risk Management Procedure Template for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-5-1: Practical Implementation and Downloadable Template
Step-by-step guide to creating a CIA-aligned risk management procedure for...
Read more →
How to Build a BYOD Policy Compliant with Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-6-2: Templates & Implementation Checklist
Practical guide and ready-to-use checklist to build a BYOD policy...
Read more →
How to Automate Antivirus & EDR Updates for Compliance — FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SI.L1-B.1.XIV
Practical, step-by-step guidance to automate antivirus and EDR signature and...
Read more →
How Small Businesses Can Implement Cost-Effective Secure Storage and Control for CUI Media — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - MP.L2-3.8.1
Practical, cost-conscious steps small businesses can take to protect, store,...
Read more →
FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.I Compliance Checklist: 10 Practical Steps to Limit Access to Authorized Users, Processes, and Systems
A practical 10-step checklist to help small businesses meet FAR...
Read more →
Visitor Management Checklist: Implementing FAR 52.204-21 / CMMC 2.0 Level 1 - Control - PE.L1-B.1.IX in Your Facility
Step-by-step visitor management checklist to meet FAR 52.204-21 and CMMC...
Read more →
Step-by-Step: How to Configure End-to-End Remote Session Encryption for Compliance — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AC.L2-3.1.13
Practical guide to configure end-to-end encrypted remote sessions to meet...
Read more →
Step-by-Step: How to Build an Ongoing CUI Risk Assessment Program for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - RA.L2-3.11.1
A practical, step-by-step guide to building an ongoing CUI risk...
Read more →
Step-by-Step Guide to Configuring Network Segmentation to Monitor and Protect Communications for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SC.L1-B.1.X
Practical, step‑by‑step guidance for small contractors to implement network segmentation,...
Read more →
Step-by-Step Guide: Automated Access Revocation for CUI After Terminations and Transfers — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - PS.L2-3.9.2
A practical, step-by-step guide to automating revocation of Controlled Unclassified...
Read more →
Practical Steps to Align Cloud Encryption with National Cryptographic Standards | Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-8-3
Clear, practical steps for small businesses to align cloud encryption...
Read more →
Implementing FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.IV in WordPress and Other CMS: A Practical Checklist
Practical, step-by-step checklist for meeting the FAR 52.204-21 / CMMC...
Read more →
Implementation checklist: Identify, report, and correct flaws for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SI.L1-B.1.XII
Clear, actionable checklist to identify, report, and remediate system flaws...
Read more →
Implementation Checklist: Harden Publicly Accessible Information Systems to Satisfy FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.IV
Step-by-step technical checklist to harden publicly accessible systems and meet...
Read more →
How to Use VPNs, Zero Trust, and Conditional Access to Control External Connections (NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AC.L2-3.1.20)
Practical guidance for using VPNs, Zero Trust principles, and Conditional...
Read more →
How to Use Nessus to Satisfy NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - RA.L2-3.11.2: Scan Policies, Credentials, and Remediation Workflows
Step-by-step guide to using Nessus for RA.L2-3.11.2 compliance: scan policies,...
Read more →
How to Use AWS/Azure/GCP IAM Policies to Enforce FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.II
A practical, cloud-specific guide to using AWS, Azure, and GCP...
Read more →
How to Use Automation to Track and Report Periodic Physical Asset Reviews for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-14-4 Compliance
Practical steps and automation patterns for tracking, evidencing, and reporting...
Read more →
How to Separate Cybersecurity from IT/ICT: Practical Steps to Achieve ECC – 2 : 2024 - Control - 1-2-1 Compliance
Practical, step-by-step guidance for small organizations to separate cybersecurity from...
Read more →
How to Select and Implement Commercial Tools to Enforce NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - MP.L2-3.8.7: USB Whitelisting, DLP, and MDM
Practical guidance for small businesses on choosing and deploying commercial...
Read more →
How to Select and Deploy Tools (MDM, EDR, SIEM) for Controlling and Monitoring User-Installed Software — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - CM.L2-3.4.9
Practical guidance for selecting and deploying MDM, EDR, and SIEM...
Read more →
How to Secure Server Rooms and Data Centers: Practical Implementation for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-14-3
Practical, compliance-focused guidance to implement ECC – 2 : 2024...
Read more →
How to Sanitize or Destroy Media Containing FCI: Step-by-Step Guide to Meeting FAR 52.204-21 / CMMC 2.0 Level 1 - Control - MP.L1-B.1.VII
Practical, step-by-step guidance to sanitize or destroy media containing Federal...
Read more →
How to Run Tabletop Exercises That Satisfy NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - IR.L2-3.6.3: Test the organizational incident response capability
Practical, step-by-step guidance for designing and running tabletop exercises that...
Read more →
How to prioritize vulnerability scan findings and integrate patch management to achieve NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - RA.L2-3.11.2
Practical, risk-based steps to prioritize vulnerability scan results and tie...
Read more →
How to Prioritize and Triage Security Advisories to Satisfy NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - SI.L2-3.14.3
Practical guide to building a repeatable advisory intake, triage, and...
Read more →
How to Prioritize and Remediate Findings from Full-Network Scans for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - RA.L2-3.11.2
Step-by-step guidance to prioritize and remediate vulnerabilities discovered by full-network...
Read more →
How to Prepare for a CMMC Assessment: Demonstrating FAR 52.204-21 / CMMC 2.0 Level 1 - Control - MP.L1-B.1.VII Compliance for Media Sanitization and Destruction
Practical, step-by-step guidance to meet FAR 52.204-21 and CMMC 2.0...
Read more →
How to Implement User, Process and Device Identification to Meet FAR 52.204-21 / CMMC 2.0 Level 1 - Control - IA.L1-B.1.V: A Step-by-Step Implementation Guide
Step-by-step guidance to identify and track users, processes, and devices...
Read more →
How to Implement Technical and Administrative Safeguards for CUI Media Access: A Compliance Checklist — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - MP.L2-3.8.2
Step-by-step checklist to implement technical and administrative safeguards that control...
Read more →
How to Implement Physical Access Controls for Small Contractors: FAR 52.204-21 / CMMC 2.0 Level 1 - Control - PE.L1-B.1.VIII Step-by-Step Checklist
Step-by-step checklist to implement cost-effective physical access controls for small...
Read more →
How to Implement Personnel Cybersecurity Requirements: Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-9-2 Compliance Checklist
Step-by-step checklist and practical guidance to implement personnel cybersecurity requirements...
Read more →
How to Implement MFA and Lightweight IAM for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - IA.L1-B.1.VI
Practical guidance for small businesses to implement multifactor authentication and...
Read more →
How to Implement Low-Cost Identity Verification and Authentication Controls for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - IA.L1-B.1.VI for Small Contractors
Practical, low-cost steps for small contractors to meet FAR 52.204-21...
Read more →
How to Implement FAR 52.204-21 / CMMC 2.0 Level 1 - Control - PE.L1-B.1.VIII: Conduct a Physical Access Gap Assessment in 7 Steps
Step-by-step guidance for small businesses to perform a physical access...
Read more →
How to Implement Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-5-2: A Practical 7-Step Procedure and Implementation Checklist
Step-by-step guidance and a practical checklist for implementing ECC‑2:2024 Control...
Read more →
How to Implement a Technical Controls Checklist for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-7-1: 10 Practical Steps to Comply with National Cybersecurity Regulations
A concise, practical guide with 10 actionable steps to implement...
Read more →
How to Document Network Security Requirements to Achieve Compliance with Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-5-1 — Templates & Checklists
Step-by-step guidance, templates, and checklists to document network security requirements...
Read more →
How to Document and Evidence Access Controls for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.II: What Auditors Look For and How to Prepare
Practical guidance for small businesses to document, evidence, and audit-proof...
Read more →
How to Deploy Multi-Factor Authentication to Meet FAR 52.204-21 / CMMC 2.0 Level 1 - Control - IA.L1-B.1.VI Compliance
Step-by-step guidance for small businesses to deploy multi-factor authentication (MFA)...
Read more →
How to Deploy Multi-Factor Authentication to Comply with Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-2-3 in 8 Practical Steps
Step-by-step practical guide to implement multi-factor authentication (MFA) that meets...
Read more →
How to Deploy MFA, RBAC and Least Privilege for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-2-2 Compliance
Practical, step-by-step guidance to implement MFA, RBAC and least-privilege controls...
Read more →
How to Create Role-Based Security Awareness for Managers, Admins, and Users That Meets NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AT.L2-3.2.1
A practical guide to designing, implementing, and evidencing role-based security...
Read more →
How to Create Compliant Incident Notification Templates and Playbooks for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - IR.L2-3.6.2
Practical guide to building incident notification templates and playbooks that...
Read more →
How to create auditor-ready vulnerability scan reports and evidence for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - RA.L2-3.11.2
Step-by-step guidance to produce auditor-ready vulnerability scan reports and evidence...
Read more →
How to Create an Evidence Collection Playbook for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-8-2 Audits: Templates, Logs, and Workpapers
Step-by-step guide to building an evidence collection playbook to meet...
Read more →
How to Create an Audit-Ready System Security Plan (SSP) for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - CA.L2-3.12.4: Step-by-Step Template for Boundaries, Environments, and Connections
Step-by-step guidance and a practical template to document system boundaries,...
Read more →
How to Create an Actionable Risk Assessment Checklist and Playbook for CUI Environments — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - RA.L2-3.11.1
Practical step-by-step guidance to build a repeatable, auditable risk assessment...
Read more →
How to create a step‑by‑step maintenance control checklist to satisfy NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - MA.L2-3.7.2
A practical, step‑by‑step guide to building a maintenance control checklist...
Read more →
How to Create a Step-by-Step Compliance Checklist for External Web Applications Meeting Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-15-1
Step-by-step guidance and a practical checklist to help small businesses...
Read more →
How to Create a Scheduled Review Process for Cybersecurity Roles and Responsibilities — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-4-2 Checklist and Templates
Step-by-step guide to implementing scheduled role-and-responsibility reviews to meet ECC‑2:2024...
Read more →
How to Create a Practical Checklist to Secure Physical Information and Tech Assets under Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-14-2
Step-by-step guidance to build a compliance-ready, actionable checklist for securing...
Read more →
How to Create a Penetration Testing Requirements Template for Compliance (Step-by-Step) — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-11-1
Step-by-step guidance to create a penetration testing requirements template that...
Read more →
How to Create a Compliance Checklist for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SC.L1-B.1.X: Tools, Tests, and Evidence to Pass an Audit
Step-by-step guidance to build a practical compliance checklist for FAR...
Read more →
How to create a checklist for protecting and monitoring power, HVAC, and cabling to satisfy NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - PE.L2-3.10.2
Step-by-step checklist and implementation guidance to protect and monitor power,...
Read more →
How to Configure SIEM and Log Management to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AU.L2-3.3.6 for Audit Record Reduction and Instant Reporting
Practical, step-by-step guidance to configure SIEM and log management so...
Read more →
How to Configure Publicly Accessible Information Systems for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.IV: Practical Settings, Tools, and Checklists
Step-by-step practical guidance to configure publicly accessible information systems to...
Read more →
How to Configure Multi-Factor Authentication for CMMC 2.0 Level 1 Compliance: FAR 52.204-21 / CMMC 2.0 Level 1 - Control - IA.L1-B.1.VI Step-by-Step
Step-by-step guidance to implement multi-factor authentication (MFA) to meet FAR...
Read more →
How to Configure Identity and Device Controls for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.I: Practical Implementation for Small Defense Contractors
Practical, step-by-step guidance for small defense contractors to configure identity...
Read more →
How to Configure Badge Readers, Smart Locks, and Audit Logging for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - PE.L1-B.1.IX Compliance
Step-by-step guidance to configure badge readers, smart locks, and audit...
Read more →
How to Configure Active Directory and Azure AD to Identify Users and Service Accounts for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - IA.L2-3.5.1
Practical, step-by-step guidance to configure Active Directory and Azure AD...
Read more →
How to Conduct a Risk-Based Review of Business Continuity Plans: Practical Steps — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 3-1-4
Step-by-step guidance to perform a risk-based review of Business Continuity...
Read more →
How to Choose and Use Sanitization Tools for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - MP.L1-B.1.VII: Practical Guidance on Degaussing, Overwriting, and Physical Destruction
Practical guidance for small businesses on selecting and using degaussing,...
Read more →
How to Build Physically or Logically Separated Subnetworks in AWS/Azure to Meet FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SC.L1-B.1.XI
Practical step-by-step guidance to create physically or logically separated subnetworks...
Read more →
How to Build an Approved Incident & Threat Management Policy for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-13-1 (Template + Approval Workflow)
Step-by-step guidance and a ready-to-adapt template with an approval workflow...
Read more →
How to Build a Risk-Based Vulnerability Remediation Plan to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - RA.L2-3.11.3
Step-by-step guidance for small businesses to create a risk-based vulnerability...
Read more →
How to Build a Practical Compliance Checklist to Limit Physical Access to Authorized Individuals — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - PE.L2-3.10.1
Step-by-step guidance and an actionable checklist to limit physical access...
Read more →
How to Build a Compliant Media Sanitization Procedure for FCI: FAR 52.204-21 / CMMC 2.0 Level 1 - Control - MP.L1-B.1.VII (Checklist & Templates)
Step-by-step guidance to develop a FAR 52.204-21 and CMMC 2.0...
Read more →
How to Build a Compliant IT & Information Asset Inventory for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-1-1
Practical step-by-step guidance for building and maintaining an auditable IT...
Read more →
How to Build a Compliance Checklist for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-7-1 to Meet National Cybersecurity Laws
Step-by-step, audit-ready guidance to build a practical compliance checklist for...
Read more →
How to Build a Backup and Recovery Policy for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-9-2: Templates and Implementation Checklist
A practical, step‑by‑step guide to creating a compliant backup and...
Read more →
How to Automate Policy Review Reminders and Evidence Collection for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-3-4
Automate reminders and evidence collection for ECC‑2:2024 Control 1-3-4 to...
Read more →
How to Automate Periodic Security Control Assessments to Demonstrate Effectiveness — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - CA.L2-3.12.1
Automate periodic security control assessments to meet NIST SP 800-171...
Read more →
How to automate periodic reviews of IT assets using discovery tools to satisfy Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-1-6
Practical steps to automate recurring IT asset discovery and inventory...
Read more →
How to Automate Periodic Reviews of Data Protection Policies and Controls — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-7-4
Practical, step-by-step guidance on automating periodic reviews of data protection...
Read more →
How to Assign, Support, and Track Cybersecurity Responsibilities Under Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-4-1: Templates and Workflows
A practical guide to assigning, supporting, and tracking cybersecurity duties...
Read more →
Step-by-Step: Implementing Data Loss Prevention on Shared Resources to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - SC.L2-3.13.4
Step-by-step guidance for implementing Data Loss Prevention on shared resources...
Read more →
Practical Implementation Checklist for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - IR.L2-3.6.2: Track, Document, and Report Incidents for SMBs
A practical, step-by-step checklist to help small and medium-sized businesses...
Read more →
How to Write a Media Sanitization Policy to Meet FAR 52.204-21 / CMMC 2.0 Level 1 - Control - MP.L1-B.1.VII: Template and Implementation Steps
Step-by-step guidance and a ready-to-use policy template to implement media...
Read more →
How to Use SIEM and Log Retention to Demonstrate User Action Traceability — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AU.L2-3.3.2
Practical steps to configure SIEM, log retention, and forensic-ready logging...
Read more →
How to Use Free and Low-Cost Tools to Identify, Report, and Correct Flaws for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SI.L1-B.1.XII
Practical guide to using free and low-cost tools and workflows...
Read more →
How to use cloud identity providers (Azure AD / Okta / Duo) to meet IA.L2-3.5.3 requirements: configuration and validation for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - IA.L2-3.5.3
Step-by-step guidance to configure Azure AD, Okta, and Duo to...
Read more →
How to Select and Configure Cost-Effective Anti-Malware Solutions for Small Contractors to Satisfy FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SI.L1-B.1.XIII
Practical guidance for small contractors to select, configure, document, and...
Read more →
How to Run Tabletop and Live Exercises to Validate IR Capability for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - IR.L2-3.6.3
Step‑by‑step guidance on designing and running tabletop and live incident...
Read more →
How to run a training needs analysis and create tailored learning paths for cybersecurity roles under Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-10-4
Step-by-step guidance to perform a training needs analysis and build...
Read more →
How to Prepare a Compliance Checklist for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.IV (Control 547): Step-by-Step Implementation for Publicly Accessible Information Systems
Practical, step-by-step checklist and technical guidance to help small businesses...
Read more →
How to Monitor System Security Alerts and Advisories to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - SI.L2-3.14.3
Learn a practical, step-by-step approach to monitor system security alerts...
Read more →
How to Monitor, Log, and Audit Access Changes to Remain Compliant: Tools, Metrics, and Evidence — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - CM.L2-3.4.5
Practical, step-by-step guidance for logging, monitoring, and auditing access changes...
Read more →
How to Measure Effectiveness of Your Cybersecurity Awareness Program for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-10-2: Surveys, Phish Rates, and Continuous Improvement
Practical, auditable methods to measure and improve your cybersecurity awareness...
Read more →
How to Map and Implement Risk Methodology to Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-5-2 Using Templates and Checklists
Step-by-step guidance for mapping a risk methodology to ECC‑2:2024 Control...
Read more →
How to integrate vulnerability scanning into daily ops to meet FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SI.L1-B.1.XII (step-by-step)
Step-by-step guidance to operationalize daily vulnerability scanning to satisfy FAR...
Read more →
How to Integrate IAM and MDM for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.I Compliance: End-to-End Implementation Guide
Practical, step-by-step guidance to integrate Identity and Access Management (IAM)...
Read more →
How to Implement Technical Controls (AD, Azure AD, IAM) for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.II: Real-World Configurations
Step-by-step AD, Azure AD and IAM configurations to satisfy FAR...
Read more →
How to Implement Segregation of Duties to Prevent Conflicts of Interest and Comply with Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-4-1
Practical, step-by-step guidance for small businesses to implement Segregation of...
Read more →
How to Implement Secure Boundary Controls and Logging for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SC.L1-B.1.X in 7 Actionable Steps
Practical 7-step guide to implement secure network boundary controls and...
Read more →
How to Implement Pre-Access Screening of Individuals for CUI: Step-by-Step NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - PS.L2-3.9.1
Practical, step-by-step guidance to implement pre-access screening for Controlled Unclassified...
Read more →How to Implement NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - IR.L2-3.6.2: Step-by-Step Guide to Tracking, Documenting, and Reporting Incidents
Practical, step-by-step guidance for small and mid-sized organizations to meet...
Read more →
How to Implement FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SC.L1-B.1.X: 30-Day Implementation Checklist for Monitoring, Controlling, and Protecting Communications
A practical 30-day checklist to implement monitoring, control, and protection...
Read more →
How to Implement FAR 52.204-21 / CMMC 2.0 Level 1 - Control - PE.L1-B.1.VIII: Step-by-Step Plan to Limit Physical Access to Information Systems
Practical, step-by-step guidance for small businesses to meet FAR 52.204-21...
Read more →
How to Implement FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.IV: Step-by-Step Checklist to Control Information on Publicly Accessible Systems
Practical, step-by-step guidance to ensure information posted on public-facing systems...
Read more →
How to Implement FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.IV: A 7-Step Checklist to Control Information on Publicly Accessible Systems
Practical 7-step checklist and technical guidance for small businesses to...
Read more →
How to Implement Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-3-3: Step-by-Step Guide to Protecting Information Systems and Processing Facilities
Practical, step-by-step guidance for implementing ECC 2-3-3 to protect information...
Read more →
How to Implement Change Management for Projects and IT Assets to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-6-2: A Step-by-Step Guide
Step-by-step guidance to implement change management for projects and IT...
Read more →
How to Implement Application Whitelisting to Restrict Nonessential Programs for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - CM.L2-3.4.7
Step-by-step, practical guidance to design, deploy, and maintain application whitelisting...
Read more →
How to Implement an Audit-Ready Acceptable Use Policy Template for Info & Tech Assets — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-1-3 (Checklist & Sample)
Step-by-step guide to create an audit-ready Acceptable Use Policy (AUP)...
Read more →
How to Implement a Visitor Management System that Meets FAR 52.204-21 / CMMC 2.0 Level 1 - Control - PE.L1-B.1.IX: Implementation Roadmap and Key Metrics
A practical roadmap and measurable metrics for implementing a visitor...
Read more →
How to Implement a Technical Stack Roadmap (IAM, EDR, MFA) to Meet Your Cybersecurity Strategy — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-1-2
Step-by-step guidance to design and deploy an IAM, EDR and...
Read more →
How to Implement a Continuous Monitoring Program for Periodic Security Control Reviews (NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - CA.L2-3.12.1)
Step‑by‑step guidance for building a continuous monitoring program to satisfy...
Read more →
How to Implement a 7-Step Checklist for Destroying or Sanitizing Media with FCI to Meet FAR 52.204-21 / CMMC 2.0 Level 1 - Control - MP.L1-B.1.VII
A practical 7-step checklist for securely destroying or sanitizing media...
Read more →
How to Harden Cloud Workloads for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - CM.L2-3.4.6: Removing Unnecessary Services in AWS, Azure, and GCP
Practical, step-by-step guidance to remove unnecessary services from cloud workloads...
Read more →
How to Enforce Password Reuse Restrictions in Azure AD to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - IA.L2-3.5.8 (Set Generations & Policies)
Step-by-step guidance to configure Azure AD and on‑prem Active Directory...
Read more →
How to Draft Security and SLA Contract Clauses for Hosting Providers to Satisfy Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 4-2-1
Practical guidance and ready-to-use clause language to ensure hosting contracts...
Read more →
How to Document and Approve Cybersecurity Roles for ECC Compliance: Practical Templates for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-4-1
Practical guidance and ready-to-use templates to document, approve, and evidence...
Read more →
How to Deploy Endpoint DLP and USB Control Rules to Block Unowned Portable Storage (NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - MP.L2-3.8.8)
Step-by-step guidance to implement Endpoint DLP and USB control rules...
Read more →
How to Create and Approve Backup and Recovery Policies: A Step-by-step Implementation Plan for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-9-1
Step-by-step guidance for small businesses to create, implement, test, and...
Read more →
How to Create a Quick Implementation Checklist for Identifying Users, Agents, and Devices under FAR 52.204-21 / CMMC 2.0 Level 1 - Control - IA.L1-B.1.V
A concise, actionable guide to building a fast implementation checklist...
Read more →
How to Create a Practical Compliance Checklist and Step-by-Step Implementation Plan for External Web Applications — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-15-3
Step-by-step guidance and a practical checklist to secure external web...
Read more →
How to Create a Practical Classification Taxonomy and Labeling Scheme for IT Assets (Template Included) — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-1-5
Step-by-step guidance to design and operationalize an IT asset classification...
Read more →
How to Create a Practical Checklist for Periodic Reviews of Cybersecurity Requirements — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-3-4
Step-by-step guidance to build a practical, auditable checklist for periodic...
Read more →
How to Create a Compliance Implementation Checklist for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SC.L1-B.1.X: From Risk Assessment to Validation
Step-by-step guidance and a practical checklist to implement and validate...
Read more →
How to Configure Your SIEM for Continuous Review and Update of Logged Events — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AU.L2-3.3.3
Practical guidance to configure and tune your SIEM for continuous...
Read more →
How to Configure Web Servers, CMS, and S3 to Comply with NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AC.L2-3.1.22
Practical, step-by-step guidance to configure web servers, CMS platforms, and...
Read more →
How to Configure SIEM for AU.L2-3.3.5 Log Correlation and Automated Alerts: NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AU.L2-3.3.5
[Write a compelling 1-sentence SEO description about this compliance requirement]...
Read more →
How to Configure SIEM and Reporting Pipelines to Correlate Audit Records for CMMC 2.0 Compliance — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AU.L2-3.3.5
Practical, step-by-step guidance to configure SIEM and reporting pipelines that...
Read more →
How to Configure Network Segmentation and Boundary Controls for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SC.L1-B.1.X: A Small Business Implementation Guide
Practical, step-by-step guidance for small businesses to implement network segmentation...
Read more →
How to Configure Firewalls, VPNs, and Policies to Control External Connections — FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.III
Practical step-by-step guidance for small businesses to configure firewalls, VPNs,...
Read more →
How to Configure Endpoint and Removable Media Scanning to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - MA.L2-3.7.4: Automating Malicious Code Checks
Step-by-step guidance for configuring automated endpoint and removable-media malware scanning...
Read more →
How to Configure Cloud VPC Subnets and Security Groups to Implement FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SC.L1-B.1.XI
Step-by-step guidance for designing VPC subnets and security groups to...
Read more →
How to Configure Cloud Storage to Protect CUI at Rest: Terraform and Policy Examples for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - SC.L2-3.13.16
Practical, step-by-step Terraform and policy examples to enforce cryptographic protection...
Read more →
How to Configure Cloud IAM (AWS/Azure/GCP) for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.II: Practical Implementation Steps
Step-by-step guidance to configure AWS, Azure, and GCP IAM controls...
Read more →
How to Configure AWS VPC Subnets to Separate Publicly Accessible Components from Internal Networks — FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SC.L1-B.1.XI
Practical, step-by-step guidance for designing AWS VPC subnet architecture that...
Read more →
How to Conduct Security Due Diligence for IT Outsourcing Vendors: Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 4-1-3 Risk Assessment Framework
Practical step-by-step guidance to implement Control 4-1-3 Risk Assessment Framework...
Read more →
How to Build Error Messages That Avoid Revealing Authentication Details — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - IA.L2-3.5.11: Developer Best Practices
Practical developer guidance for implementing NIST SP 800-171 / CMMC...
Read more →
How to Build and Document a Compliant BCP: Implementing Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 3-1-2 in 8 Actionable Steps
A practical, step-by-step guide to build and document a compliant...
Read more →
How to Build an Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 3-1-3 Compliant Business Continuity Plan with Ready-to-Use Templates
Step-by-step guidance and ready-to-use templates to build a Control 3-1-3...
Read more →
How to Build an Audit Results Template Meeting Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-8-3 Requirements for Scope, Findings, and Remediation
Step-by-step guide to designing an audit results template that satisfies...
Read more →
How to Build an Audit-Ready Network Security Management Policy for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-5-1 with Templates and Examples
Practical, audit-focused guidance and ready-to-use templates to build a network...
Read more →
How to Build a Step-by-Step Visitor Management Process to Meet FAR 52.204-21 / CMMC 2.0 Level 1 - Control - PE.L1-B.1.VIII
Practical, step-by-step guidance for small businesses to implement a visitor...
Read more →
How to Build a Patch Management Playbook for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - SI.L2-3.14.1: Prioritization, SLAs, and Verification
Step-by-step guidance to build a patch management playbook that meets...
Read more →
How to Build a Hosting & Cloud Compliance Checklist: Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 4-2-3 Implementation Steps
Step-by-step implementation guidance for ECC‑2:2024 Control 4-2-3 to harden cloud/hosting...
Read more →
How to Build a BYOD Security Policy to Comply with Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-6-1: Templates and Step-by-Step Instructions
Practical, step-by-step guidance and a ready-to-use template to build a...
Read more →
How to Build a BYOD Security Checklist and Review Workflow Aligned to Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-6-4
Practical, step-by-step guidance to build a BYOD security checklist and...
Read more →
How to Automate Periodic Data Protection Reviews for Compliance with Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-7-4
Practical guide to automating periodic data protection reviews to meet...
Read more →
How to Automate Logged Event Reviews with SIEM for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AU.L2-3.3.3
Step-by-step guidance to automate audit log review with a SIEM...
Read more →
Actionable Steps to Harden Physical Access Logging and Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - PE.L2-3.10.4 (Audit Log Examples & Templates)
Practical, step-by-step guidance and ready-to-use log templates to harden physical...
Read more →
7-Step Checklist to Identify Information System Users, Processes Acting for Users, and Devices — FAR 52.204-21 / CMMC 2.0 Level 1 - Control - IA.L1-B.1.V
Practical 7-step checklist to identify and track users, processes acting...
Read more →
Template and Timeline: Performing Periodic Risk Assessments for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - RA.L2-3.11.1 Compliance
Practical template and timeline for performing periodic risk assessments to...
Read more →
Step-by-Step Process to Analyze Security Impact of Changes for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - CM.L2-3.4.4
A practical, step-by-step guide to analyze the security impact of...
Read more →
Step-by-Step Network Segmentation and Monitoring to Meet FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SC.L1-B.1.X
Practical, step-by-step guidance for small businesses to implement network segmentation...
Read more →
SSP Template and Example: Implementing NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - CA.L2-3.12.4 for Small Businesses
Step-by-step SSP template and practical example to implement NIST SP...
Read more →
Practical Steps to Encrypt CUI on iOS and Android Devices for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AC.L2-3.1.19
Step-by-step guidance for encrypting CUI on iOS and Android to...
Read more →
Practical Checklist: Implementing Least Functionality on Windows and Linux to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - CM.L2-3.4.6
A one-page, practical checklist for applying least functionality on Windows...
Read more →
Practical Checklist: Creating Physically or Logically Separated Subnetworks for Public-Facing Components — FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SC.L1-B.1.XI
Step-by-step checklist and pragmatic implementation guidance for separating public-facing components...
Read more →
Implementation Checklist: Logging, Retention, and User ID Mapping for AU.L2-3.3.2 Compliance: NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AU.L2-3.3.2
Practical checklist for implementing logging, retention, and user ID mapping...
Read more →
Implementation Checklist: Identifying Users, Processes Acting on Behalf of Users, and Devices for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - IA.L1-B.1.V
Step-by-step checklist to inventory and identify users, agent/service processes acting...
Read more →
How to Validate and Maintain Continuous Compliance for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - PE.L2-3.10.1: Audit Checklist and Implementation Roadmap
Practical audit checklist and step-by-step roadmap to validate and maintain...
Read more →
How to use MFA, SSO, and device certificates to satisfy FAR 52.204-21 / CMMC 2.0 Level 1 - Control - IA.L1-B.1.V requirements
Step-by-step guidance for small businesses to implement MFA, SSO, and...
Read more →
How to Use Identity and Endpoint Tools to Achieve FAR 52.204-21 / CMMC 2.0 Level 1 - Control - IA.L1-B.1.V Compliance: Tool Selection & Deployment
Practical guidance on selecting and deploying identity and endpoint tools...
Read more →
How to Update Antivirus and EDR Tools and Record Compliance Evidence — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - SI.L2-3.14.4
Step-by-step guidance for keeping antivirus and EDR tools updated and...
Read more →
How to Train Staff on Secure Data Handling Practices to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-7-2: Checklist and Templates
Practical, step-by-step guidance, checklists, and ready-to-use templates to train staff...
Read more →
How to Track KPIs and Report Effectiveness of Periodic Multi-Channel Awareness Programs for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-10-1
Learn how to define KPIs, collect measurable evidence, and report...
Read more →
How to Secure Backup Data in Transit and at Rest (MFT, TLS, AES) to Protect CUI — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - MP.L2-3.8.9
Practical guidance for encrypting and managing backup data in transit...
Read more →
How to Prepare for CMMC 2.0 Level 2 Certification by Periodically Assessing Security Controls (NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - CA.L2-3.12.1)
Learn practical, small-business focused steps to meet CMMC 2.0 Level...
Read more →
How to Map Job Functions to Competency Requirements for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-10-4: Practical Implementation Guide
Step-by-step guidance to map job functions to competency requirements so...
Read more →How to Integrate SIEM and Ticketing Systems for Real-Time Incident Tracking Under NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - IR.L2-3.6.2
Practical, step-by-step guidance to integrate your SIEM and ticketing system...
Read more →
How to Implement Secure Remote Access for CUI: Practical Steps for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - PE.L2-3.10.6 Compliance
Step-by-step guidance for small businesses to implement secure remote access...
Read more →
How to Implement Physical Access Controls to Meet FAR 52.204-21 / CMMC 2.0 Level 1 - Control - PE.L1-B.1.VIII: Step-by-Step Checklist
Practical, step-by-step guidance for small businesses to implement physical access...
Read more →
How to Implement Physical Access Controls to Limit Physical Access to Systems for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - PE.L1-B.1.VIII (Step-by-Step Checklist)
Step-by-step, practical checklist to implement physical access controls that satisfy...
Read more →
How to Implement Physical Access Controls to Limit Access — FAR 52.204-21 / CMMC 2.0 Level 1 - Control - PE.L1-B.1.VIII: Step-by-Step Guide for Small Contractors
Practical, step-by-step guidance for small government contractors to implement physical...
Read more →
How to Implement Phishing Simulations and Reinforcement Tactics to Build a Positive Security Culture: Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-10-1
Step-by-step guidance to implement phishing simulations and reinforcement tactics that...
Read more →
How to Implement Multi-Factor Authentication and Process-Based Access Controls for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AC.L2-3.1.1
Practical, step-by-step guidance to implement multi-factor authentication and process-based access...
Read more →
How to Implement FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.IV: Step-by-Step Guide to Controlling Information on Publicly Accessible Information Systems
Step-by-step, practical guidance for small businesses to prevent exposure of...
Read more →
How to Implement Cloud IAM Controls for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - IA.L2-3.5.5 (AWS, Azure, GCP) to Block Identifier Reuse
Practical guidance to implement NIST SP 800-171 / CMMC 2.0...
Read more →
How to Implement Automated Vulnerability Scanning and Reporting for Periodic External Web App Reviews (Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-15-4)
Step-by-step guidance to implement automated external web application vulnerability scanning...
Read more →
How to Implement Automated Malware Scans for Diagnostic and Test Programs on Removable Media: Tools, Scripts, and Best Practices — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - MA.L2-3.7.4
Practical guide to implementing automated malware scans for diagnostic/test programs...
Read more →
How to Implement an Escort and Visitor Monitoring Program for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - PE.L1-B.1.IX: Step-by-Step Guide
Practical step-by-step guidance for small businesses to implement an escort...
Read more →
How to Implement a Step-by-Step ECC 3-1-1 Compliance Process — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 3-1-1 Checklist for Business Continuity
Step-by-step guidance to meet ECC 3-1-1 business continuity requirements with...
Read more →
How to Harden CMS and Web Portals to Prevent Sensitive Data Exposure — FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.IV
Practical steps to secure CMS and web portals to protect...
Read more →
How to Document Penetration Test Requirements and Evidence for Audits: Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-11-1 Checklist
Step-by-step guidance to document penetration test requirements and evidence so...
Read more →
How to Develop a Contract Checklist and Template for ECC-Compliant Third-Party Agreements: Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 4-1-3
Step-by-step guidance and ready-to-use clause templates to build a contract...
Read more →
How to Deploy Technical Controls (Firewalls, DLP, Segmentation) to Enforce AC.L2-3.1.3 and Control CUI Flow: NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AC.L2-3.1.3
Step-by-step technical guidance for small businesses to use firewalls, segmentation,...
Read more →
How to Deploy Low-Cost Physical Access Controls for Small Businesses to Meet PE.L1-B.1.VIII — FAR 52.204-21 / CMMC 2.0 Level 1 - Control - PE.L1-B.1.VIII
Practical, low-cost physical access control strategies for small businesses to...
Read more →
How to Define Metrics and KPIs to Drive Periodic Reviews of Your Cybersecurity Awareness Program — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-10-5
Learn exactly which metrics and KPIs to define, measure, and...
Read more →
How to Create Approved Security Requirement Documents for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-3-1: Templates and Implementation Workflow
Step-by-step guidance and ready-to-use templates for producing approved Security Requirement...
Read more →
How to Create an IAM Review Checklist That Satisfies Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-2-4
Step-by-step guidance to build an IAM review checklist that meets...
Read more →
How to Create an Audit-Ready Patch Management Plan to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - SI.L2-3.14.1
Step-by-step guidance to build an audit-ready, risk-based patch management plan...
Read more →
How to Create a Step-by-Step Role Review Checklist to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-4-2
A practical, step-by-step guide to building a role review checklist...
Read more →
How to Create a Repeatable CUI Risk Assessment Process with Templates and Timelines — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - RA.L2-3.11.1
Step-by-step guidance for building a repeatable, auditable CUI risk assessment...
Read more →
How to Create a Practical Compliance Checklist and Implementation Roadmap for External Web Applications under Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-15-2
Step‑by‑step checklist and roadmap to secure and demonstrate compliance for...
Read more →
How to Create a Media Sanitization SOP for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - MP.L1-B.1.VII: Templates, Checklist, and Implementation Steps
Step-by-step guidance and ready-to-use templates to build a media sanitization...
Read more →
How to Create a Cryptography Review Checklist and Policy for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-8-4
Step-by-step guidance to build a practical cryptography review checklist and...
Read more →
How to Create a Compliance Checklist for Periodic Network Security Reviews under Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-5-4
Step-by-step guidance to build a practical, auditable compliance checklist for...
Read more →
How to Create a Change Management Access Control Checklist for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - CM.L2-3.4.5
Practical, step-by-step checklist and implementation guidance to control and restrict...
Read more →
How to Configure Windows and Linux Systems for On-Access Scanning of Downloads and Executables: Implementation Steps for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SI.L1-B.1.XV
Step-by-step guidance to configure Windows and Linux endpoints for on‑access...
Read more →
How to configure role-based access for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.II: Practical implementation checklist for contractors
Step-by-step guidance for contractors to implement role-based access (AC.L1-B.1.II) that...
Read more →
How to Configure MFA and Device Verification to Meet FAR 52.204-21 / CMMC 2.0 Level 1 - Control - IA.L1-B.1.VI
Step-by-step guidance to implement multifactor authentication and device verification to...
Read more →
How to Configure MDM, Encryption, and Remote Wipe to Satisfy Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-6-2 (Practical Checklist)
[Write a compelling 1-sentence SEO description about this compliance requirement]...
Read more →
How to Configure Centralized Logging and SIEM Integration to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-12-3
Step-by-step guidance for small businesses to implement centralized logging and...
Read more →
How to Configure AWS and Azure Subnets for Public-Facing Systems: Practical Implementation for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SC.L1-B.1.XI
Practical, audit-ready steps to design and configure AWS and Azure...
Read more →
How to Configure Active Directory to Disable Dormant Accounts Automatically — Practical Implementation for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - IA.L2-3.5.6
Step-by-step guidance to automatically detect and disable dormant Active Directory...
Read more →
How to Configure a SIEM for ECC Compliance: Event Logs, Alerting, and Tuning — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-12-2
Practical step-by-step guidance to configure a SIEM to meet ECC...
Read more →
How to Choose and Configure AV/EDR Tools to Satisfy FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SI.L1-B.1.XIV
Practical guidance for small businesses on selecting and configuring AV/EDR...
Read more →
How to Build an Audit-Ready Cryptography Review Checklist for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-8-4
Practical, audit-ready checklist and implementation guidance to meet ECC 2:2024...
Read more →
How to Build an Asset Change Management Procedure That Satisfies Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-6-1: Templates & Checklists
Step-by-step guidance and ready-to-use template fields to build an asset...
Read more →
How to Build an AC.L1-B.1.IV Implementation Checklist for FAR 52.204-21 / CMMC 2.0 Level 1: Control Information Posted or Processed on Public Systems
Step-by-step guidance and a practical checklist to ensure information posted...
Read more →
How to Build a Visitor Escort and Monitoring Program to Meet FAR 52.204-21 / CMMC 2.0 Level 1 - Control - PE.L1-B.1.IX (Checklist & Templates)
Step-by-step guidance, checklist items, and ready-to-use templates to implement a...
Read more →
How to Build a Step-by-Step Implementation Checklist for Malicious Code Controls (FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SI.L1-B.1.XIII)
Step-by-step practical checklist to implement malicious code controls required by...
Read more →
How to Build a Practical Employee Cybersecurity Training Program That Satisfies Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-9-4
Step-by-step guidance for small businesses to design, implement, and evidence...
Read more →
How to Build a Practical Compliance Checklist for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.IV to Secure Publicly Accessible Information Systems
A practical, step-by-step checklist to help small businesses secure publicly...
Read more →
How to Build a POA&M: Step-by-Step Implementation for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - CA.L2-3.12.2
Practical, step-by-step guidance for creating and maintaining a Plan of...
Read more →
How to Build a Compliance SOP to Review and Update Logged Events (Templates Included) — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AU.L2-3.3.3
Step-by-step SOP guidance to establish, review, and update logged events...
Read more →
How to Build a Compliance-Ready Logging Architecture to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AU.L2-3.3.2
Step-by-step guidance to design and implement a secure, auditable logging...
Read more →
How to Automate Periodic Role and Responsibility Reviews with Workflows and Alerts — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-4-2
Practical, step-by-step guidance for automating periodic role and responsibility reviews...
Read more →
How to Automate Incident Review Workflows to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-13-4 Requirements
Practical guidance to design, implement, and validate automated incident review...
Read more →
How to Automate Identifier Disablement in Cloud IAM (Azure/AWS/GCP) for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - IA.L2-3.5.6
Practical, step‑by‑step guidance to automate disabling user and service identifiers...
Read more →
How small businesses can cost-effectively implement FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SI.L1-B.1.XIII malicious code protections: tools, timelines, and templates
Practical, low-cost steps and templates for small businesses to meet...
Read more →
Checklist: Practical Steps to Protect Transmitted Data at System Boundaries for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SC.L1-B.1.X
A practical, step-by-step checklist for protecting data in transit at...
Read more →
Checklist and Templates to Implement and Approve BYOD Controls under Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-6-1
Step-by-step checklist, templates, and technical guidance to implement and approve...
Read more →
Step-by-Step: Implementing Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-10-3 to Train Staff on Phishing and Ransomware
Practical, audit-ready guidance to implement ECC–2:2024 Control 1-10-3—training staff to...
Read more →
Step-by-Step: Implementing CUI-Focused Risk Assessments with Templates and Tools — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - RA.L2-3.11.1
Practical, step-by-step guidance with templates and low-cost tools to implement...
Read more →
Step-by-Step Guide to Deploying SIEM and IDS for Inbound/Outbound Traffic Monitoring — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - SI.L2-3.14.6
[Write a compelling 1-sentence SEO description about this compliance requirement]...
Read more →
Step-by-Step: Configure Idle Session Timeouts on Windows and Linux for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AC.L2-3.1.11
How to implement and document idle session timeout controls on...
Read more →
Step-by-Step Checklist to Securely Transport and Track CUI Media: NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - MP.L2-3.8.5
Practical, step-by-step checklist for securely transporting, tracking, and maintaining accountability...
Read more →
Step-by-Step Checklist for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - IA.L1-B.1.V: Identify Information System Users, Processes Acting for Users, and Devices
Practical, step-by-step guidance to identify and document users, user-acting processes,...
Read more →
Practical Checklist for Reviewing Cybersecurity Strategy at Planned Intervals: Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-1-3
A concise, actionable checklist to run recurring reviews of your...
Read more →
Implementing Visitor Escort Policies and Monitoring Procedures for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - PE.L1-B.1.IX (Template & Examples)
Practical guidance, templates, and small-business examples to implement visitor escort...
Read more →
How to Use VPNs, Firewalls, and MFA to Limit Connections to External Information Systems — FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.III Implementation Guide
Practical steps for small businesses to implement VPNs, firewalls, and...
Read more →
How to Use Cloud Provider Tools to Monitor Communications for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SC.L1-B.1.X: AWS & Azure Implementation Guide
Practical, step-by-step guidance for using AWS and Azure native tools...
Read more →
How to Scale a Compliant Cybersecurity Organizational Structure for Small and Medium Businesses — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-4-1: Practical Implementation Checklist
Step-by-step checklist to scale a compliant cybersecurity organizational structure for...
Read more →
How to Remediate Common Gaps for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.II (Code 545): Actionable Fixes for Small Contractors
Practical, step-by-step remediation guidance for small contractors to meet FAR...
Read more →
How to Protect Cloud and Remote Connections: Implementing Boundary Controls for Hybrid Environments — FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SC.L1-B.1.X
Step-by-step guidance to implement boundary controls for cloud and remote...
Read more →
How to Prepare for Compliance Audits by Documenting Network Security Management per Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-5-1
Practical, step-by-step guidance to document network security management so small...
Read more →
How to Prepare for CMMC 2.0 Level 2 Assessments: SSP Best Practices for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - CA.L2-3.12.4
Practical SSP guidance to implement and demonstrate CA.L2-3.12.4 audit and...
Read more →
How to Prepare for Audits: Evidence and Documentation Best Practices for Cryptography Requirements under Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-8-1
Practical evidence and documentation best practices to demonstrate compliance with...
Read more →
How to Prepare for a CMMC 2.0 Level 2 Assessment: Control Connection of Mobile Devices Implementation Guide (NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AC.L2-3.1.18)
Step-by-step guidance to control mobile device connections for CMMC 2.0...
Read more →
How to Prepare Backup and Recovery Evidence for Audits: A Practical Checklist for ECC Compliance — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-9-1
Detailed, practical guidance for producing backup and recovery evidence that...
Read more →
How to Map Roles to Required Cybersecurity Competencies and Tools for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-10-4 (Template + Implementation Guide)
Practical step‑by‑step guidance to map job roles to required cybersecurity...
Read more →
How to Label and Handle Sensitive Data in Cloud and Hybrid Environments: Implementation Best Practices — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-1-5
Practical step-by-step guidance for labeling and handling sensitive data in...
Read more →
How to Implement Role-Based Access Control in Active Directory to Limit Information System Access — FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.II
Practical, step-by-step guidance for implementing Role-Based Access Control (RBAC) in...
Read more →
How to Implement Physical Access Controls for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - PE.L1-B.1.VIII: Step-by-Step Guide for Contractors
Practical, step-by-step guidance for small contractors to implement physical access...
Read more →
How to Implement Periodic Security Control Assessments for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - CA.L2-3.12.1: A Step-by-Step Guide
Step-by-step guidance to implement CA.L2-3.12.1 periodic security control assessments to...
Read more →
How to Implement Periodic Cybersecurity Reviews: A Practical Checklist for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-8-1 Compliance
A concise, actionable guide to implementing periodic cybersecurity reviews to...
Read more →
How to Implement Media Sanitization for Federal Contract Information: FAR 52.204-21 / CMMC 2.0 Level 1 - Control - MP.L1-B.1.VII (Step-by-Step Guide)
Step-by-step guidance for small businesses to implement media sanitization that...
Read more →
How to implement cloud-native monitoring to satisfy NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - SI.L2-3.14.7 and identify unauthorized use across Azure, AWS, and GCP
Learn step-by-step cloud-native monitoring patterns and platform-specific configurations for Azure,...
Read more →
How to Implement Cloud-Native Audit Log Failure Alerts in AWS/Azure/GCP — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AU.L2-3.3.4
Step-by-step guidance to implement cloud-native audit log failure detection and...
Read more →
How to Implement Budget-Friendly Steps for Small Businesses to Meet FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SC.L1-B.1.X for Monitoring and Protecting Communications
Practical, low-cost steps small businesses can use to monitor and...
Read more →
How to Implement Automated Malware Scanning for Diagnostic/Test Media to Satisfy NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - MA.L2-3.7.4
Practical guidance for small businesses to implement automated malware scanning...
Read more →
How to Implement Acceptable Use Policies for BYOD and Remote Work under Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-1-4
Practical, step‑by‑step guidance for small businesses to implement Acceptable Use...
Read more →
How to Harden Linux and Windows Servers for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - CM.L2-3.4.7: Disable Unnecessary Daemons, Services, and Listening Ports
Step-by-step guidance for identifying and disabling unnecessary daemons, services, and...
Read more →
How to Harden Cloud Audit Logging Controls to Comply with NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AU.L2-3.3.9
Practical, step-by-step guidance for hardening cloud audit logging so small...
Read more →
How to Get Authorizing Official Approval for Cybersecurity Roles: Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-4-1 Template and Process
Step-by-step guidance, a ready-to-use approval template, and practical controls to...
Read more →
How to Document and Approve Third-Party Cloud Services Under Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 4-2-1: A Practical Template
Practical, step-by-step template to document, risk-assess, and approve third-party cloud...
Read more →
How to Deploy MFA and SSO to Meet FAR 52.204-21 / CMMC 2.0 Level 1 - Control - IA.L1-B.1.VI: Implementation Checklist
Step-by-step guidance for small businesses to implement MFA and SSO...
Read more →
How to Deploy Low-Cost MFA for Small Contractors to Comply with FAR 52.204-21 / CMMC 2.0 Level 1 - Control - IA.L1-B.1.VI
Step-by-step, low-cost guidance for small contractors to implement multi-factor authentication...
Read more →
How to Deploy Endpoint Detection and Response (EDR) to Meet FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SI.L1-B.1.XIII
Step-by-step guidance to deploy and configure EDR to satisfy FAR...
Read more →
How to Deploy Cloud Provider MFA and Automated Session Timeouts for Nonlocal Maintenance (AWS/Azure/GCP) — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - MA.L2-3.7.5
Practical, step-by-step guidance to enforce multi-factor authentication and automated session...
Read more →
How to Deploy CCTV, Alarms and Sensors to Satisfy NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - PE.L2-3.10.2: An Implementation Checklist
Step-by-step, practical checklist to design, deploy, and document CCTV, alarms...
Read more →
How to Create Contract Clauses and Templates that Satisfy Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 4-1-1
Step-by-step guidance and ready-to-use contract clause templates to help organizations...
Read more →
How to Create an Audit-Ready Cybersecurity Risk Management Program under Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-5-2: Templates & Checklists
Step-by-step guidance, templates and checklists to build an audit-ready cybersecurity...
Read more →
How to Create an Audit-Ready Cybersecurity Requirements Document for Information Systems: Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-3-1 Checklist and Template
Step-by-step guidance to build an audit-ready cybersecurity requirements document for...
Read more →
How to create an audit-ready cloud hosting policy template for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 4-2-1 compliance
Step-by-step guidance and a practical template to create an audit-ready...
Read more →
How to Create an Access Control Checklist to Verify and Control External System Use — FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.III
Step-by-step guidance to build an access-control checklist that verifies and...
Read more →
How to Create a System Boundary Diagram and Connectivity Inventory for Compliance — Practical Steps for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - CA.L2-3.12.4
Step-by-step guidance to produce a clear system boundary diagram and...
Read more →
How to Create a Step-by-Step Audit Checklist for Mobile Device Security and BYOD Reviews (Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-6-4)
Step-by-step guidance to build an audit checklist that ensures mobile...
Read more →
How to Create a Media Sanitization Policy for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - MP.L1-B.1.VII and Ensure Secure Disposal
Step-by-step guidance to build a media sanitization policy that satisfies...
Read more →
How to Create a CUI Protection Checklist for Terminations and Role Changes (Templates & Scripts) — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - PS.L2-3.9.2
Step-by-step guidance to build a CUI protection checklist for employee...
Read more →
How to Create a BYOD Review Checklist and Policy Template to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-6-4
Practical step-by-step guidance and a ready-to-adopt BYOD review checklist and...
Read more →
How to Configure Secure Remote Access and VPNs to Comply with FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.III
Practical, step-by-step guidance for configuring secure remote access and VPNs...
Read more →
How to Configure Role-Based Access Controls for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.II: Practical RBAC Implementation Checklist
Step-by-step RBAC implementation guidance to meet FAR 52.204-21 and CMMC...
Read more →
How to Configure Multi‑Factor Authentication to Meet FAR 52.204-21 / CMMC 2.0 Level 1 - Control - IA.L1-B.1.VI: Practical Steps and Tool Choices
Step-by-step guidance and tool recommendations to implement MFA that satisfies...
Read more →
How to Configure Logging, Monitoring, and Approval Workflows to Supervise Maintenance by Non-Authorized Staff — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - MA.L2-3.7.6
Step-by-step guide to implement logging, monitoring, and approval workflows to...
Read more →
How to Configure Identity and Access Tools to Enforce NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - CM.L2-3.4.5 During System Changes: Technical Implementation Guide
[Write a compelling 1-sentence SEO description about this compliance requirement]...
Read more →
How to Configure Automated Scanning Tools to Satisfy NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - MA.L2-3.7.4 for Diagnostic/Test Program Media
Step-by-step guidance on configuring automated discovery, classification, sanitization workflows, and...
Read more →
How to Configure and Integrate Door Access Systems with SIEM to Maintain Audit Logs for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - PE.L2-3.10.4
Step-by-step guide to configure door access systems and integrate them...
Read more →
How to Conduct Security Due Diligence and Negotiate Contracts to Achieve Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 4-1-3 Compliance
Practical step-by-step guidance for conducting security due diligence and negotiating...
Read more →
How to Conduct Background Checks to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - PS.L2-3.9.1: Practical Steps and Compliance Tips
Step-by-step guide to performing background checks to satisfy NIST SP...
Read more →
How to Choose and Use Media Sanitization Tools to Meet FAR 52.204-21 / CMMC 2.0 Level 1 - Control - MP.L1-B.1.VII Requirements
Practical guidance for small businesses on selecting, running, and documenting...
Read more →
How to Choose and Configure Scanning Tools for Cloud Storage and External File Sources to Meet FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SI.L1-B.1.XV
Practical guidance to select and configure cloud and external-file scanning...
Read more →
How to Choose and Configure Anti-Malware Tools to Scan Test Media for Compliance — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - MA.L2-3.7.4
Practical guidance to select and configure anti‑malware tools for scanning...
Read more →
How to Build an Implementation Plan with Templates and Timelines for Physical Access Control Compliance — FAR 52.204-21 / CMMC 2.0 Level 1 - Control - PE.L1-B.1.VII
Step-by-step implementation plan, templates, and realistic timelines to meet physical...
Read more →
How to Build an Audit-Ready BYOD Program for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-6-1: Step-by-Step Mobile Device Security Implementation
Practical, step-by-step guidance to implement BYOD mobile device security for...
Read more →
How to Build an Approved Vulnerability Management Process with Roles, SLAs, and Metrics — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-10-1
Step-by-step guidance to design and operationalize an approved vulnerability management...
Read more →
How to build a step-by-step physical access checklist for compliance with FAR 52.204-21 / CMMC 2.0 Level 1 - Control - PE.L1-B.1.VIII
Step-by-step guide to building a practical physical access checklist to...
Read more →
How to Build a Practical MFA and SSO Setup to Meet FAR 52.204-21 / CMMC 2.0 Level 1 - Control - IA.L1-B.1.VI Compliance
Step-by-step guidance for small businesses to implement MFA and SSO...
Read more →
How to Build a Maintenance Access and Audit Policy (with Templates) — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - MA.L2-3.7.2
Step-by-step guidance and ready-to-use templates to create a maintenance access...
Read more →
How to Build a DevSecOps Pipeline That Meets Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-6-3 Requirements
Practical, step-by-step guidance to implement and evidence automated security enforcement...
Read more →
How to Build a Compliant Cloud Hosting Requirements Policy Using Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 4-2-1 Templates and Examples
Practical, copyable cloud hosting policy templates and step-by-step implementation guidance...
Read more →
How to Build a Compliance Checklist for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.IV to Prevent Unauthorized Public Data Exposure
Practical step-by-step checklist to meet FAR 52.204-21 / CMMC 2.0...
Read more →
How to automate compliance for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-4-2: workflows for periodic role reviews and regulatory changes
Practical guide to automating role review and regulatory-change workflows to...
Read more →
Comparing Replay-Resistant Authentication Methods (MFA, PKI, SRP) and How to Implement Them — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - IA.L2-3.5.4
Practical guidance to meet NIST SP 800-171 Rev.2 / CMMC...
Read more →
Step-by-Step Guide to Configuring Malware Protection for Cloud and On-Prem Systems — FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SI.L1-B.1.XIII
Practical, step-by-step guidance to deploy and evidence malware protection across...
Read more →
Step-by-Step Guide to Automating Access Revocation for CUI When Employees Leave — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - PS.L2-3.9.2
Practical step-by-step instructions to automate revocation of access to Controlled...
Read more →
Step-by-Step Checklist to Periodically Assess Risk to Operations and CUI: NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - RA.L2-3.11.1
A practical, step-by-step checklist to periodically assess risks to operations...
Read more →
Network Segmentation Best Practices: Implement Subnetworks for Publicly Accessible Components under FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SC.L1-B.1.XI
Practical steps and examples to implement subnetworks (DMZ/public subnets) that...
Read more →
Implementing Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-2-2: Step-by-Step Checklist to Verify Experience and Saudi Nationality Requirements
A practical, step-by-step checklist to verify candidate experience and Saudi...
Read more →
How to Write, Document, and Get Approval for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-9-1 Personnel Policies: Templates and Examples
Step-by-step guidance, templates, and small-business examples to write, document, and...
Read more →
How to Use SIEM and Threat Intelligence to Support Periodic Incident Reviews — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-13-4
Practical guidance on integrating SIEM and threat intelligence to meet...
Read more →
How to Use SIEM and EDR for Rapid Flaw Identification and Correction: NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - SI.L2-3.14.1 Implementation Guide
[Write a compelling 1-sentence SEO description about this compliance requirement]...
Read more →
How to Use MFA and Role-Based Access Control to Satisfy FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.I Requirements
Practical guidance on implementing multi-factor authentication (MFA) and role-based access...
Read more →
How to Secure Server Rooms and Equipment: Practical Implementation Guide for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - PE.L1-B.1.VIII
Step-by-step, practical guidance to secure server rooms and equipment to...
Read more →
How to Secure Remote and Cloud Connections: Practical Steps and Tools to Limit External System Use — FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.III
Practical, step‑by‑step guidance for small businesses to limit use of...
Read more →
How to Secure Cloud and Offsite Storage for Backup CUI: Step-by-Step Implementation Guide — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - MP.L2-3.8.9
Step-by-step guidance to securely store backup Controlled Unclassified Information (CUI)...
Read more →
How to Revoke Access and Secure Devices Immediately After Termination: Practical Steps for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - PS.L2-3.9.2
Step-by-step guidance for immediately revoking access and securing devices after...
Read more →
How to Report Cybersecurity Incidents to Authorities Without Breaking Privacy Rules — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - IR.L2-3.6.2
Practical, step-by-step guidance for reporting cybersecurity incidents to authorities in...
Read more →
How to Prioritize and Remediate Technical Vulnerabilities by Risk to Satisfy Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-10-2
Practical, step-by-step guidance to identify, risk-rank, and remediate technical vulnerabilities...
Read more →
How to Prioritize and Remediate Critical Vulnerabilities with Risk Assessment Metrics — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - RA.L2-3.11.3
Learn a practical, metrics-driven approach to prioritize and remediate critical...
Read more →
How to Prioritize and Patch Vulnerabilities to Comply with FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SI.L1-B.1.XII: A Risk-Based Approach
Practical, step-by-step guidance for small businesses to prioritize and remediate...
Read more →
How to Prepare Your Organization for an Independent Audit under Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-8-2: Pre-Audit Remediation and Documentation Guide
Practical, step-by-step guidance to remediate, document and package evidence for...
Read more →
How to Prepare for CMMC 2.0 Level 2 Assessments: Practical Steps to Demonstrate Compliance with NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - MP.L2-3.8.5 for CUI Media Handling and Transport
Practical, step-by-step guidance for small businesses to meet CMMC 2.0...
Read more →
How to Prepare for a Regulatory Audit: Documentation and Controls Checklist for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-7-1
A practical, step-by-step checklist of documentation and technical controls to...
Read more →
How to Perform a Gap Assessment for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-3-3 and Prioritize Remediation Actions
Step-by-step guidance to map, assess, and prioritize remediation for ECC...
Read more →
How to Measure and Improve Time-to-Remediate: KPIs and Implementation Steps for SI.L1-B.1.XII — FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SI.L1-B.1.XII
Practical guidance to measure, report, and reduce Time-to-Remediate (TTR) to...
Read more →
How to implement subnetworks in AWS/Azure for publicly accessible system components for compliance — FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SC.L1-B.1.XI
Practical, step-by-step guidance for segregating publicly accessible components into subnetworks...
Read more →
How to Implement Secure Remote Access and Zero Trust Network Principles for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-5-3
Practical, step-by-step guidance for meeting ECC – 2 : 2024...
Read more →
How to implement NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - PS.L2-3.9.1: Background check checklist and templates for contractors and staff
Practical checklist and ready-to-use templates to implement PS.L2-3.9.1 background checks...
Read more →
How to Implement NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - CM.L2-3.4.9: Step-by-Step Plan to Control and Monitor User-Installed Software
Step-by-step, practical guidance to meet CM.L2-3.4.9 by preventing, controlling, and...
Read more →
How to Implement FAR 52.204-21 / CMMC 2.0 Level 1 - Control - IA.L1-B.1.V: Step-by-Step Guide to Identifying System Users, User-Acting Processes, and Devices
Practical, step-by-step guidance to help small businesses meet FAR 52.204-21...
Read more →
How to Implement FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.I: Step-by-Step Guide to Limiting System Access to Authorized Users, Processes, and Devices
Step-by-step, practical guidance for meeting FAR 52.204-21 and CMMC 2.0...
Read more →
How to implement Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-15-3 for external web applications: a step-by-step compliance checklist
A practical, step-by-step checklist to implement ECC 2-15-3 for external...
Read more →
How to Implement Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-7-1: Step-by-Step Guide to Comply with National Cybersecurity Laws and Regulations
Practical, step-by-step guidance to meet Control 1-7-1 of ECC–2:2024 and...
Read more →
How to Implement Continuous Network Monitoring to Satisfy Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-5-2: SIEM, IDS/IPS and Alerting Playbook
Practical, step-by-step guidance to deploy SIEM, IDS/IPS and an actionable...
Read more →
How to Implement Cloud and Email Attachment Scanning for Downloads and Execution: FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SI.L1-B.1.XV
Practical, step-by-step guidance for implementing cloud and email attachment scanning...
Read more →
How to Implement Centralized Event Log Collection with SIEM to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-12-2
Step-by-step guidance for implementing centralized event log collection with a...
Read more →How to Implement Automated Visitor Tracking and Physical Access Device Controls to Satisfy FAR 52.204-21 / CMMC 2.0 Level 1 - Control - PE.L1-B.1.IX
Practical, step-by-step guidance for small businesses to implement automated visitor...
Read more →
How to Implement a Security Awareness Program for Managers, System Administrators, and Users to Achieve NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AT.L2-3.2.1
Step-by-step, role-based guidance to build and document a security awareness...
Read more →
How to Encrypt, Label, and Track CUI Media in Transit: Practical Implementation Steps — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - MP.L2-3.8.5
Practical, step-by-step guidance for small businesses to encrypt, label, and...
Read more →
How to Draft a Compliant Cybersecurity Strategy Document: Templates and Examples for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-1-1
Step-by-step guidance and a ready-to-use template for drafting a cybersecurity...
Read more →
How to Design Phishing Simulations and Training for the Latest Threats: Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-10-3
Practical guidance for designing, running, and documenting phishing simulations and...
Read more →
How to Deploy Practical Tools (NAC, IAM, MDM) to Meet FAR 52.204-21 / CMMC 2.0 Level 1 - Control - IA.L1-B.1.V
Practical guidance to deploy NAC, IAM, and MDM solutions that...
Read more →
How to Deploy MFA and Strong Authentication to Satisfy Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-2-2
Practical, step-by-step guidance to deploy multi-factor and phishing‑resistant authentication that...
Read more →
How to Deliver Effective Insider Threat Awareness Training: Templates and Scripts for Compliance - NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AT.L2-3.2.3
Step-by-step guidance and ready-to-use templates to implement insider threat awareness...
Read more →
How to Create Procedures That Meet ECC Control 1-5-1 for Small and Medium Businesses — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-5-1 (Low-Cost Implementation Guide)
Practical, low-cost step-by-step guidance for small and medium businesses to...
Read more →
How to Create Policies, Procedures, and a Compliance Checklist to Verify External Information System Connections for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.III
Step-by-step guidance to build policies, procedures, and a practical checklist...
Read more →
How to Create Background Check Policies and Procedures to Comply with NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - PS.L2-3.9.1
Step-by-step guidance for small businesses to design background check policies...
Read more →
How to Create an Event Log Review Policy and Checklist for ECC Compliance: Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-12-4
Step-by-step guide to build an event log review policy and...
Read more →
How to Create an Audit-Ready Cybersecurity Strategy Review Checklist — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-1-3
Step-by-step guidance to build an audit-ready review checklist for ECC...
Read more →
How to Create a Step-by-Step Checklist for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - IA.L1-B.1.V Compliance: User, Process, and Device Identification
Practical step-by-step checklist and implementation guidance to meet FAR 52.204-21...
Read more →
How to Create a Compliance Checklist for Hosting & Cloud Providers to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 4-2-1
Practical step-by-step checklist and implementation guidance to validate hosting and...
Read more →
How to Create a Committee Charter and Governance Framework: Template and Approval Process — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-2-3
Step-by-step guidance and a ready-to-use template to build a committee...
Read more →
How to Configure MFA and Unique Accounts to Comply with FAR 52.204-21 / CMMC 2.0 Level 1 - Control - IA.L1-B.1.VI
Step-by-step guidance to configure multi-factor authentication and unique user accounts...
Read more →
How to Configure MFA and Device Identity Controls to Satisfy FAR 52.204-21 / CMMC 2.0 Level 1 - Control - IA.L1-B.1.VI (Implementation Best Practices)
Practical, step-by-step guidance for implementing MFA and device identity controls...
Read more →
How to Configure Logs and SIEM for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - SI.L2-3.14.7 to Detect Unauthorized System Use
Step-by-step guide to configuring logs and SIEM to meet NIST...
Read more →
How to Configure Identity Inventories to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - IA.L2-3.5.1 Compliance (Templates & Examples)
Step-by-step guidance and ready-to-use templates for building and maintaining identity...
Read more →
How to Configure Cloud VPCs and Subnets to Meet FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SC.L1-B.1.XI: A Practical How-To
Step-by-step guidance for configuring cloud VPCs and subnets to satisfy...
Read more →
How to Configure Cloud Storage Encryption (AWS/Azure/GCP) to Protect CUI at Rest: NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - SC.L2-3.13.16
Step-by-step guidance to configure AWS, Azure, and GCP storage encryption...
Read more →
How to Configure Azure AD and Intune to Disable Identifiers After Defined Inactivity Periods — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - IA.L2-3.5.6
Step-by-step guidance to implement NIST SP 800-171 / CMMC IA.L2-3.5.6...
Read more →
How to Configure Active Directory and Azure AD to Disable Identifiers After Inactivity — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - IA.L2-3.5.6
Step-by-step guidance to automatically detect and disable inactive user identifiers...
Read more →
How to Configure Access Controls for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.I Using Least Privilege and MFA
Practical step-by-step guidance to configure least-privilege access and enforce multi-factor...
Read more →
How to Choose Tools and Techniques to Properly Sanitize Hard Drives and Removable Media — FAR 52.204-21 / CMMC 2.0 Level 1 - Control - MP.L1-B.1.VII
Practical guidance for selecting tools and processes to sanitize hard...
Read more →
How to Build Incident Response Playbooks for Each Phase (Prep → Detect → Analyze → Contain → Recover → Notify) — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - IR.L2-3.6.1
[Write a compelling 1-sentence SEO description about this compliance requirement]...
Read more →
How to Build an SI.L2-3.14.2 Compliance Checklist: Implementing NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - SI.L2-3.14.2 Across Endpoints, Email, and Cloud
Step-by-step checklist to implement NIST SP 800-171 Rev.2 / CMMC...
Read more →
How to Build an Audit-Ready Inventory for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - IA.L1-B.1.V: Practical Steps to Identify Information System Users, Processes, and Devices
Step-by-step guidance for small businesses to create an audit-ready inventory...
Read more →
How to Build a Visitor Escort and Monitoring Program to Comply with FAR 52.204-21 / CMMC 2.0 Level 1 - Control - PE.L1-B.1.IX (Includes Log Templates)
Step-by-step guidance for small businesses on building a visitor escort...
Read more →
How to Build a Step-by-Step Audit Checklist for Network Security Reviews (Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-5-4)
[Write a compelling 1-sentence SEO description about this compliance requirement]...
Read more →
How to Build a Practical Acceptable Use Policy Template for IT Assets to Achieve Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-1-4 Compliance
Learn how to draft, implement, and enforce an Acceptable Use...
Read more →
How to Build a Compliance-Ready Cybersecurity Requirements Policy (Template + Example) — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-3-1
Step-by-step guidance and a ready-to-use template to create a Compliance...
Read more →
How to Automate Policy Review Workflows to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-3-4
Learn how to automate policy review workflows to satisfy ECC...
Read more →
How to Automate Immediate Access Revocation for Departing Employees (AD, MFA, Cloud) — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - PS.L2-3.9.2
Step-by-step guide to automating immediate revocation of access for departing...
Read more →
How to Audit and Verify External Information System Connections for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AC.L2-3.1.20 (Checklist Included)
Step-by-step guidance for auditing, authorizing, and continuously verifying external connections...
Read more →
How to Apply NIST-Based Media Sanitization Methods to Meet FAR 52.204-21 / CMMC 2.0 Level 1 - Control - MP.L1-B.1.VII: Practical Implementation and Examples
Practical, step-by-step guidance on applying NIST SP 800-88 sanitization methods...
Read more →
How Small Businesses Can Implement Periodic and Real-Time File Scans to Meet FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SI.L1-B.1.XV: Practical Steps and Low-Cost Tools
Step-by-step, low-cost strategies for small businesses to implement periodic and...
Read more →
Step-by-Step Patch Management: Identify, Report, and Correct System Flaws for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - SI.L2-3.14.1
Practical, step-by-step guidance to meet SI.L2-3.14.1 by identifying, reporting, and...
Read more →
Step-by-Step Implementation Checklist for Monitoring External and Internal Boundaries to Achieve FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SC.L1-B.1.X
Practical, step-by-step checklist to monitor external and internal network boundaries...
Read more →
Step-by-Step: How to Configure SIEM for Event Logs and Monitoring Management under Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-12-2
Practical, step-by-step guidance for configuring a SIEM to meet ECC...
Read more →
Step-by-Step Guide to Maintaining Physical Access Audit Logs for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - PE.L1-B.1.IX
A practical, step-by-step guide for small businesses to implement, maintain,...
Read more →
Step-by-Step Guide: Implementing VLAN and Subnetwork Segmentation for Public Systems — FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SC.L1-B.1.XI
Practical, step-by-step guidance for small businesses to implement VLAN and...
Read more →
Practical Checklist for Ensuring CUI Is Erased Before Off‑Site Maintenance — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - MA.L2-3.7.3
A concise, actionable checklist for small organizations to ensure Controlled...
Read more →
Implementing Subnetworks for Public Components: 7 Practical Steps and Network Diagram Examples — FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SC.L1-B.1.XI
Practical, step-by-step guidance for creating isolated subnetworks (DMZ/public subnets) to...
Read more →
How to Use SCCM and Intune to Deploy and Enforce Security Configurations for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - CM.L2-3.4.2
Practical guidance for using Microsoft SCCM (ConfigMgr) and Intune to...
Read more →
How to Use Nessus to Scan All Networked Devices and Satisfy NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - RA.L2-3.11.2 (Configuration & Reporting)
Practical guidance to configure Nessus for complete asset discovery, credentialed...
Read more →
How to Use MFA, Rate Limiting, and Adaptive Authentication to Reduce Unsuccessful Logon Attempts — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AC.L2-3.1.8
Practical guidance for small businesses on implementing MFA, rate limiting,...
Read more →
How to use IAM tools and configurations to meet FAR 52.204-21 / CMMC 2.0 Level 1 - Control - IA.L1-B.1.VI from setup to audit
Step-by-step guide to using identity and access management tools and...
Read more →
How to use endpoint detection and response (EDR) to spot unauthorized use in your environment — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - SI.L2-3.14.7
Practical guidance to deploy, tune, and document EDR so you...
Read more →
How to Use Endpoint Detection and Response (EDR) to Identify Unauthorized Use of Organizational Systems with Example Queries — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - SI.L2-3.14.7
Learn how to configure and use Endpoint Detection and Response...
Read more →
How to Use CI/CD and DevSecOps Practices to Achieve NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - SC.L2-3.13.2
Practical CI/CD and DevSecOps steps to meet NIST SP 800-171...
Read more →
How to Use 7 Practical Methods to Sanitize or Destroy Media Containing Federal Contract Information — Comply with FAR 52.204-21 / CMMC 2.0 Level 1 - Control - MP.L1-B.1.VII
Practical, actionable guidance on 7 proven methods to sanitize or...
Read more →
How to Select and Deploy Monitoring Tools (Network Sensors, Proxies, and Loggers) to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - SI.L2-3.14.6
[Write a compelling 1-sentence SEO description about this compliance requirement]...
Read more →
How to Schedule, Track, and Automate Periodic Risk Management Reviews with Templates: Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-5-4
Step-by-step guidance to schedule, track, and automate periodic risk management...
Read more →
How to Run a Gap Analysis for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-7-2 and Close Deficiencies Related to Nationally-Approved International Commitments
Step-by-step guidance to run a gap analysis against ECC–2:2024 Control...
Read more →
How to prioritize vulnerabilities using CVSS and asset criticality for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-10-2
Learn a practical, auditable method to combine CVSS scores with...
Read more →
How to Prepare for an Audit: Evidence and Documentation Your Cybersecurity Steering Committee Needs for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-2-3
Practical guidance and a checklist of evidence your cybersecurity steering...
Read more →
How to Prepare for an Audit: Demonstrating Maintenance Compliance for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - MA.L2-3.7.1
Step-by-step guidance for demonstrating compliance with MA.L2-3.7.1 (maintenance) under NIST...
Read more →
How to Map Data Handling Rules to GDPR, HIPAA, and PCI for ECC Compliance: Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-7-1
Practical, step-by-step guidance to map your data handling policies and...
Read more →
How to Integrate SSO, MFA, and Device Registration to Satisfy FAR 52.204-21 / CMMC 2.0 Level 1 - Control - IA.L1-B.1.V: Implementation Playbook
Step-by-step playbook to integrate Single Sign-On, Multi-Factor Authentication, and device...
Read more →
How to Implement Visitor Escorting, Monitoring, and Audit Logs for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - PE.L1-B.1.IX: A Step-by-step Checklist
Step-by-step guidance for small businesses to implement visitor escorting, monitoring,...
Read more →
How to Implement User and Device Identification for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - IA.L1-B.1.V: Step-by-Step Guide
Step-by-step guidance for small businesses to implement user and device...
Read more →
How to implement the Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-15-2: Step-by-step checklist to secure external web applications and prove compliance
Practical, step-by-step guidance to secure external web applications under ECC...
Read more →
How to Implement Periodic and Real-Time File Scanning to Meet FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SI.L1-B.1.XV: Step-by-Step Deployment Guide
Step-by-step implementation guidance for periodic and real-time file scanning to...
Read more →
How to Implement NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - CM.L2-3.4.9: A Step-by-Step Guide to Controlling and Monitoring User-Installed Software
Practical step-by-step guidance for small businesses to meet NIST SP...
Read more →
How to Implement Network Segmentation and Key Internal Boundary Controls for CMMC Compliance — FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SC.L1-B.1.X
Practical, step-by-step guidance for small businesses to design and operate...
Read more →
How to Implement Multi-Factor Authentication to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - IA.L2-3.5.2: Step-by-Step Guide for Authenticating Users, Processes, and Devices
Step‑by‑step, vendor-neutral guidance to implement phishing‑resistant multi‑factor authentication and device/process...
Read more →
How to Implement Media Sanitization for Common Devices (HDDs, SSDs, USBs, Mobile) Containing Federal Contract Information Before Reuse or Disposal — Device-Specific Steps for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - MP.L1-B.1.VII
Step-by-step, device-specific media sanitization guidance to meet FAR 52.204-21 and...
Read more →
How to Implement Low-Cost Physical Access Controls and Visitor Logging to Achieve FAR 52.204-21 / CMMC 2.0 Level 1 - Control - PE.L1-B.1.IX Compliance
Practical, low-cost steps small businesses can implement today to meet...
Read more →
How to Implement Layered Malware Defenses (Email, Web, Endpoint, Network) to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - SI.L2-3.14.2
Step-by-step guidance for small organizations to implement layered email, web,...
Read more →
How to Implement Idle Session Timeouts for VPNs and Web Apps to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - SC.L2-3.13.9
Step-by-step guidance to configure idle session timeouts for VPNs and...
Read more →
How to Implement Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-10-4: Step-by-Step Role-Based Training Plan for Cyber Staff
Practical, step-by-step guidance to design, deliver, and document a role-based...
Read more →
How to Implement Backup, Restore, and Data Integrity Controls for ECC Compliance: Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 3-1-3 Practical Steps
[Write a compelling 1-sentence SEO description about this compliance requirement]...
Read more →
How to Implement and Enforce Security Configuration Settings for IT Products to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - CM.L2-3.4.2 (Step-by-Step Guide)
Step-by-step guidance for small and mid-size organizations to implement and...
Read more →
How to Implement a Cybersecurity Awareness Program to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-10-2: A Step-by-Step Guide
Step-by-step guidance to design, run, measure, and document a cybersecurity...
Read more →
How to Draft a Cybersecurity Roles and Responsibilities Policy That Passes ECC Review — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-4-1: Sample Policy, Approval Steps, and Evidence Collection
Step-by-step guidance and evidence templates to create a Roles and...
Read more →
How to Define and Document Email Service Protection for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-4-1: A Practical Implementation Checklist
Concrete, step-by-step guidance to design, implement, and document Email Service...
Read more →
How to Create Incident Response Workflows That Satisfy NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - SI.L2-3.14.3 (With Templates)
[Write a compelling 1-sentence SEO description about this compliance requirement]...
Read more →
How to Create an Evidence-Ready Checklist for Malicious Code Protections — FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SI.L1-B.1.XIII
Step-by-step guidance to build an evidence-focused checklist that demonstrates compliance...
Read more →
How to Create a Step-by-Step External Web App Audit Checklist for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-15-4
Practical step-by-step guidance to build an external web application audit...
Read more →
How to Create a Step-by-Step Audit Checklist to Verify Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-3-2 Implementation
Practical step-by-step guidance and an audit checklist to verify Compliance...
Read more →
How to Create a Risk Management Review Checklist and Approval Log (Template Included) — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-5-4
Step‑by‑step guidance and ready-to-use templates to implement Control 1-5-4 of...
Read more →
How to Create a Practical PE.L1-B.1.VIII Implementation Checklist and Timeline for Small Businesses — FAR 52.204-21 / CMMC 2.0 Level 1 - Control - PE.L1-B.1.VIII
Practical step-by-step checklist and 6–8 week timeline to implement PE.L1-B.1.VIII...
Read more →
How to Create a Practical Key Management Procedure to Satisfy Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-8-1
Step-by-step guidance to build a compliant, auditable key management procedure...
Read more →
How to Create a Hardened Configuration Checklist for IT Products Under NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - CM.L2-3.4.2
Step-by-step guidance to build a hardened configuration checklist that meets...
Read more →
How to Create a Contract Review Checklist to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 4-1-4
Create a contract review checklist aligned to ECC 2:2024 Control...
Read more →
How to Create a Compliance Roadmap for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-7-2: From Assessment to Certification
Step-by-step guidance to assess, remediate, and achieve certification for ECC‑2:2024...
Read more →
How to Configure Windows and Linux Systems for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - CM.L2-3.4.7 to Disable Nonessential Functions
Step-by-step guidance to identify, disable, and manage nonessential services and...
Read more →
How to Configure Multi-Factor Authentication to Enforce FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.I for Authorized Users and Processes
Practical, step-by-step guidance for small businesses to deploy multi-factor authentication...
Read more →
How to Configure Login Flows to Obscure Feedback of Authentication Information: Practical Steps and Code Examples for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - IA.L2-3.5.11
Practical guidance, code examples, and compliance evidence to implement NIST...
Read more →
How to Configure Firewalls, TLS, and DLP to Protect Organizational Communications — FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SC.L1-B.1.X Implementation Checklist
Step-by-step checklist to configure firewalls, TLS, and DLP to meet...
Read more →
How to Comply with FAR 52.204-21 / CMMC 2.0 Level 1 - Control - MP.L1-B.1.VII: Step-by-Step Guide to Sanitizing or Destroying Media Containing Federal Contract Information
Practical, step-by-step guidance for small businesses to sanitize or destroy...
Read more →
How to Choose and Tune Anti-Malware and EDR Tools for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SI.L1-B.1.XV Compliance
Practical guidance for small businesses on selecting, configuring, and documenting...
Read more →
How to Build an Onboarding and Offboarding Checklist That Meets Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-9-4 Compliance
Step-by-step guidance to design onboarding and offboarding checklists that satisfy...
Read more →
How to Build an Inventory and Whitelist Strategy to Control User-Installed Software (NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - CM.L2-3.4.9)
Practical guide to creating an inventory and application allowlist to...
Read more →
How to Build an Automated Vulnerability Review Pipeline for External Web Apps to Comply with Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-15-4
Step-by-step guidance to implement an automated vulnerability review pipeline for...
Read more →
How to Build an Audit-Ready Checklist for Reviewing Physical Protection of Information and Technology Assets — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-14-4
Practical, audit-focused guidance to build a checklist that proves compliance...
Read more →
How to Build an Approved Backup & Recovery Policy Template with Implementation Steps — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-9-1
Step-by-step guidance and a ready-to-adapt policy template to meet ECC...
Read more →
How to Build a Practical Offboarding Checklist to Protect CUI During Transfers and Terminations — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - PS.L2-3.9.2
Practical step-by-step guidance to build an offboarding checklist that ensures...
Read more →
How to Build a Least-Functionality Configuration Checklist for Windows and Linux to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - CM.L2-3.4.6
Step-by-step guidance to create and implement a least-functionality configuration checklist...
Read more →
How to Build a Dedicated Cybersecurity Function Independent from IT: A 7-Step Implementation Plan (Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-2-1)
Practical 7-step plan to establish an independent cybersecurity function that...
Read more →
How to Build a Compliance-Ready Support Infrastructure for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - PE.L2-3.10.2: Practical Implementation Checklist
Step-by-step, practical guidance to design and document a support infrastructure...
Read more →
How to Build a Compliance-Focused Physical Access Program Aligned to FAR 52.204-21 / CMMC 2.0 Level 1 - Control - PE.L1-B.1.IX: Policies, Controls, and Continuous Monitoring
Step-by-step guidance for small businesses to design policies, technical controls,...
Read more →
How to Build a BYOD Policy That Meets NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AC.L2-3.1.18 for Mobile Device Connections
Practical guidance to design and enforce a BYOD policy that...
Read more →
How to Automate Periodic Security Reviews of External Web Applications with Tools and Scripts — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-15-4
Practical guidance to automate scheduled security reviews of external web...
Read more →
How to Apply Low-Cost Physical Security Measures for Small Businesses to Meet FAR 52.204-21 / CMMC 2.0 Level 1 - Control - PE.L1-B.1.VIII
Practical, low-cost physical security steps small businesses can implement today...
Read more →
How Small Contractors Can Implement Cost-Effective Anti-Malware Controls to Comply with FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SI.L1-B.1.XIII
Practical, low-cost anti-malware strategies and step-by-step controls small contractors can...
Read more →
How Small Businesses Can Implement Cost-Effective Physical Access Controls for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - PE.L1-B.1.VIII
Practical, budget-friendly strategies for small businesses to meet FAR 52.204-21...
Read more →
Step-by-Step Implementation Guide: Controlling Information on Publicly Accessible Systems — FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.IV
Practical step-by-step guidance to prevent public exposure of covered contractor...
Read more →
Step-by-Step Guide to Configuring Endpoint Real-Time Scans for External Files: NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - SI.L2-3.14.5
Practical, step-by-step guidance to configure endpoint real-time scanning of external...
Read more →
Step-by-Step Guide: Configure VLANs and DMZs to Implement Subnetworks for Public Systems — FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SC.L1-B.1.XI
Practical, step-by-step instructions for using VLANs and DMZs to isolate...
Read more →
Step-by-Step Guide: Configure Access Restrictions by Transaction and Function — FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.II (Code 545)
Practical, step-by-step guidance to implement transaction- and function-level access controls...
Read more →
Step-by-Step Checklist for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - IA.L2-3.5.1: From Policy to Evidence for Identifying System Actors and Devices
A practical, step-by-step checklist to implement IA.L2-3.5.1 — identify users,...
Read more →
Practical Implementation: Automating Backup Verification and Periodic Reviews to Satisfy Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-9-4
Step-by-step guidance for automating backup verification and running periodic reviews...
Read more →
Implementation Checklist: Periodic Information System Scans and Real-Time File Scanning for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SI.L1-B.1.XV
Step-by-step checklist to implement periodic system scans and real-time file...
Read more →
How to Verify and Document Media Sanitization for Federal Contract Information Before Reuse or Disposal: Compliance Steps for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - MP.L1-B.1.VII
Step-by-step guidance to verify and document media sanitization of Federal...
Read more →
How to Verify and Document Media Destruction for CUI Compliance (NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - MP.L2-3.8.3)
Practical guidance to verify and document secure media destruction for...
Read more →
How to Use Identity and Access Management (IAM) to Meet FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.II: Implementation Checklist
Practical, step-by-step Identity and Access Management (IAM) guidance to help...
Read more →
How to Test Your Incident Response Capability: A Step-by-Step Guide to NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - IR.L2-3.6.3
A practical, step-by-step guide to testing your incident response capability...
Read more →
How to Test and Validate Malicious Code Protections (FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SI.L1-B.1.XIII) Before Assessment
Step-by-step guidance for small businesses to test and validate malicious...
Read more →
How to Select and Deploy Endpoint Scanning Tools to Satisfy FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SI.L1-B.1.XV
Practical guidance on choosing and deploying endpoint scanning tools to...
Read more →
How to Securely Transport Electronic and Physical CUI Media: Compliance Steps for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - MP.L2-3.8.5
Practical, actionable steps for small businesses to securely transport electronic...
Read more →
How to Secure Server Rooms and Network Racks: Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-14-3 Implementation Checklist
Practical, step-by-step guidance to secure server rooms and network racks...
Read more →
How to Secure Server Rooms and Equipment: Practical Steps for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - PE.L1-B.1.VIII Compliance
Practical, low-cost steps and technical controls to physically secure server...
Read more →
How to Prioritize Technical Vulnerabilities Using CVSS, Business Context, and Threat Intelligence — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-10-3
Learn a practical, auditable approach to prioritize technical vulnerabilities for...
Read more →
How to Integrate Patch Management with NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - MA.L2-3.7.1: Practical Steps to Perform Maintenance on Organizational Systems
Step-by-step guidance to integrate automated and documented patch management processes...
Read more →
How to Integrate Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-6-3 into CI/CD Pipelines for Automated Compliance
Learn step-by-step how to implement ECC 2:2024 Control 1-6-3 in...
Read more →
How to Integrate Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-3-2 with ISO 27001 and CMMC: Implementing Consistent Policies and Procedures
Practical guidance for small organizations to implement ECC 1-3-2 consistent...
Read more →
How to Implement User, Process, and Device Identity Verification for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - IA.L1-B.1.VI: Practical Checklist
Practical, step-by-step checklist to verify user, process, and device identities...
Read more →
How to Implement User, Process, and Device Identification Step-by-Step — FAR 52.204-21 / CMMC 2.0 Level 1 - Control - IA.L1-B.1.V
Step-by-step guide to identifying users, processes, and devices to meet...
Read more →
How to Implement the Principle of Least Privilege for Privileged Accounts: Step‑by‑Step Implementation — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AC.L2-3.1.5
Practical, step‑by‑step guidance for implementing least privilege for privileged accounts...
Read more →
How to Implement Phishing and Ransomware Training Modules for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-10-3
Step-by-step guidance to design, deploy, and evidence phishing and ransomware...
Read more →
How to Implement Periodic and Triggered Vulnerability Scans to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - RA.L2-3.11.2 (Step-by-Step Nessus Guide for Servers, Desktops, Laptops, VMs, Containers, Firewalls, Switches, Printers)
A practical step-by-step Nessus guide to implement periodic and triggered...
Read more →
How to Implement Multi-Factor Authentication to Authenticate Users, Processes, and Devices for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - IA.L1-B.1.VI: A Step-by-Step Guide
Step-by-step, practical guidance for implementing multi-factor authentication for users, processes,...
Read more →
How to Implement Malware Scanning for Diagnostic and Test Media Before Use to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - MA.L2-3.7.4 (Step-by-Step)
Step-by-step guidance for small organizations to implement malware scanning of...
Read more →
How to implement low-cost visitor management systems that comply with FAR 52.204-21 / CMMC 2.0 Level 1 - Control - PE.L1-B.1.IX for small businesses
Practical, low-cost visitor management approaches for small businesses to meet...
Read more →
How to implement firewall, segmentation, and access controls for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-5-3 compliance
Step-by-step guidance to meet ECC – 2 : 2024 Control...
Read more →
How to Implement FAR 52.204-21 / CMMC 2.0 Level 1 - Control - MP.L1-B.1.VII: Step-by-Step Media Sanitization and Destruction for Federal Contract Information
Step-by-step guidance for small businesses to meet FAR 52.204-21 and...
Read more →
How to Implement FAR 52.204-21 / CMMC 2.0 Level 1 - Control - IA.L1-B.1.V: Step-by-Step Guide to Identifying Information System Users, Processes, and Devices
Practical, step-by-step guidance for small businesses to meet FAR 52.204-21...
Read more →
How to Implement Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-8-1: A Practical Checklist to Define, Document and Approve Cryptography Requirements
A practical, compliance-focused checklist to define, document, and approve cryptography...
Read more →
How to Implement Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-3-3: Step-by-Step Plan to Protect Information Systems
Practical, step-by-step guidance to implement ECC Control 2-3-3 under the...
Read more →
How to Implement Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-7-1 to Meet National Cybersecurity Laws: A Step-by-Step Guide
Practical, step-by-step guidance to implement ECC – 2 : 2024...
Read more →
How to Implement Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-2-2: Step-by-Step Hiring Plan to Fill All Cybersecurity Positions with Full-Time Experienced Saudi Professionals
Step-by-step hiring plan that helps organizations meet ECC–2:2024 Control 1-2-2...
Read more →
How to Implement Content Controls for Public Websites: FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.IV Step-by-Step Checklist
Step-by-step implementation guidance to prevent public websites from exposing covered...
Read more →
How to Implement Cloud Identity Lockout Controls in Azure and AWS to Satisfy NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AC.L2-3.1.8
Practical step-by-step guidance to implement identity account lockout controls in...
Read more →
How to Implement a Technical Vulnerability Management Program: Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-10-2
Practical guide to implementing a Technical Vulnerability Management Program to...
Read more →
How to Implement a Step-by-Step SIEM and Log Strategy to Identify Unauthorized Use of Organizational Systems — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - SI.L2-3.14.7
Practical, step-by-step guidance to build a SIEM and logging strategy...
Read more →
How to Harden SSH and RDP with Replay-Resistant Authentication for Network Access to Privileged and Non-Privileged Accounts — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - IA.L2-3.5.4
Practical, step-by-step guidance to implement replay-resistant authentication (FIDO2/smartcard/SSH certs and...
Read more →
How to Establish an Approved, Periodic Cybersecurity Awareness Program: Template and Checklist for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-10-1
Step-by-step guide and ready-to-use template to implement an approved, periodic...
Read more →
How to Encrypt CUI on USBs and Laptops: Step-by-Step Implementation for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - MP.L2-3.8.6
Step-by-step guidance for small businesses to encrypt CUI on USB...
Read more →
How to Draft Vendor Agreements That Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 4-1-1: Templates, Clauses and Examples
Practical guidance and ready-to-use clause examples to ensure vendor contracts...
Read more →
How to Document and Evidence Personnel Screening to Pass a CMMC 2.0 Level 2 Audit — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - PS.L2-3.9.1
Practical, audit-ready guidance for documenting and evidencing personnel screening to...
Read more →
How to Deploy Multi-Factor Authentication for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-2-3 Compliance
Step-by-step guidance to implement multi-factor authentication to satisfy ECC 2-2-3,...
Read more →
How to Create and Approve Documented Data Handling Standards Per Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-7-1 for HIPAA, GDPR and CCPA Compliance
Step-by-step guide to creating and approving documented data handling standards...
Read more →
How to Create a Step-by-Step Offboarding Checklist to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - PS.L2-3.9.2
A practical, actionable guide for building an auditable offboarding checklist...
Read more →
How to Create a Measurable Security Risk Awareness Plan for Managers, Sysadmins, and Users (Checklist & Templates) — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AT.L2-3.2.1
Step-by-step guide to build a measurable security risk awareness plan...
Read more →
How to Create a Compliance Checklist for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.IV: 10 Actionable Tasks to Control Publicly Posted Data
Practical, step-by-step checklist for small businesses to meet FAR 52.204-21...
Read more →
How to Configure SIEM and Alerting for Event Logs and Monitoring Management — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-12-2 Implementation Guide
Practical, step-by-step guidance for configuring SIEM and alerting to meet...
Read more →
How to Configure Server Room Security: Locks, Cameras, and Monitoring to Meet FAR 52.204-21 / CMMC 2.0 Level 1 - Control - PE.L1-B.1.VIII
Practical, step-by-step guidance for small businesses to secure server rooms...
Read more →
How to configure secure remote access and VPNs to comply with Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-5-3
Practical, step-by-step guidance for configuring secure remote access and VPNs...
Read more →
How to Configure IAM and Automated Deprovisioning for Terminations/Transfers to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - PS.L2-3.9.2
Step-by-step guidance to implement identity lifecycle, automated deprovisioning, and evidence...
Read more →
How to Configure Endpoint Detection and Response (EDR) to Identify Unauthorized Use of Organizational Systems: Step-by-Step Implementation — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - SI.L2-3.14.7
Step-by-step guidance to configure EDR to detect, alert, and document...
Read more →
How to Configure CI/CD Pipelines to Enforce Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-6-3 Requirements
Practical guide to configuring CI/CD pipelines so they automatically enforce...
Read more →
How to Configure AWS VPC Subnets and Security Groups to Separate Public and Internal Networks for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SC.L1-B.1.XI
Step-by-step guidance to design AWS VPC subnets and security groups...
Read more →
How to Conduct Background Checks and Vetting for CUI Access: Compliance Steps for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - PS.L2-3.9.1
Step-by-step guidance for implementing background checks and personnel vetting to...
Read more →
How to Build an Ongoing Security Controls Monitoring Program for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - CA.L2-3.12.3
[Write a compelling 1-sentence SEO description about this compliance requirement]...
Read more →
How to Build an Incident Response Playbook Covering Detection, Analysis, Containment, and Recovery for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - IR.L2-3.6.1
Step-by-step guidance to build a NIST SP 800-171 / CMMC...
Read more →
How to Build an Audit-Ready Periodic Assessment Schedule with Checklists and Templates — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - CA.L2-3.12.1
Practical steps to design and run audit-ready periodic security assessments...
Read more →
How to build an audit-ready Cybersecurity Awareness Program: Practical checklist for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-10-2
Step-by-step, audit-focused guidance to design, implement, and evidence a Cybersecurity...
Read more →
How to Build a Practical Checklist to Protect Against Malicious Code: FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SI.L1-B.1.XIII
Step‑by‑step guidance and a pragmatic checklist to meet FAR 52.204‑21...
Read more →
How to Build a Compliance-Ready IT Asset Security Policy: Templates and Workflow for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-1-1
Step-by-step guidance, templates, and an operational workflow to build a...
Read more →
How to build a compliance checklist for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-7-1 to meet national cybersecurity requirements
Step-by-step guide to creating a compliance checklist for ECC –...
Read more →
How to Build a Change Management Policy Aligned with Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-6-1: Templates, Roles, and Approval Workflows
Practical guidance to design change management templates, assign roles, and...
Read more →
How to Automate Evidence Collection and Reporting for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 4-2-4 Periodic Reviews of Hosting and Cloud Computing Services
Practical steps to automate collection, verification, and reporting of evidence...
Read more →
How to Audit and Document Physical Access Controls for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - PE.L1-B.1.VIII: A Compliance Checklist
Step-by-step guidance and a practical evidence checklist to audit and...
Read more →
How to Architect a Secure DMZ and Network Segmentation for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - SC.L2-3.13.5
Practical guidance for designing a DMZ and network segmentation that...
Read more →
How to Apply NIST 800-88 Methods to Sanitize Media for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - MP.L1-B.1.VII
Practical, step-by-step guidance for small businesses to apply NIST SP...
Read more →
How Small Businesses Can Meet SI.L1-B.1.XIV: Practical Steps to Update Malicious Code Protection — FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SI.L1-B.1.XIV
Practical, step-by-step guidance for small businesses to implement and document...
Read more →
Configuration Checklist: Network and Application Cryptography to Comply with NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - SC.L2-3.13.8
A practical, actionable configuration checklist for securing network and application...
Read more →
30-Day Roadmap to Apply Malware Protections at Appropriate Locations — FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SI.L1-B.1.XIII
A practical 30-day roadmap to implement malware protections at appropriate...
Read more →
Step-by-Step Template: Implement Procedures for Cybersecurity Risk Management (Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-5-2)
A practical, step-by-step template to implement and document cybersecurity risk...
Read more →
Step-by-Step Guide to Meeting NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AT.L2-3.2.3: Practical Training Modules to Spot and Report Insider Threat Indicators
Practical, role-based training module design and implementation steps to satisfy...
Read more →
Step-by-Step Guide to Deploying Anti‑Malware at Appropriate Locations to Meet FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SI.L1-B.1.XIII
Practical, step-by-step guidance for small businesses to deploy anti‑malware in...
Read more →
Step-by-Step Guide to Configuring SIEM Audit Reduction and On-Demand Reports for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AU.L2-3.3.6
A practical, step-by-step guide to configuring SIEM audit reduction and...
Read more →
Step-by-Step AWS VPC Architecture to Meet FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SC.L1-B.1.XI: Isolate Public Subnetworks with Sample CloudFormation
Practical, step-by-step AWS VPC design and a reusable CloudFormation template...
Read more →
Implementing Automated Change Controls to Satisfy Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-6-1: Tools, Templates, and Tests
Practical steps, tools, and templates to implement automated change controls...
Read more →
How to Use Vulnerability Scanning Data to Drive Risk-Based Remediation Decisions: NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - RA.L2-3.11.3
Practical guidance for using vulnerability scanning outputs to prioritize remediation...
Read more →
How to Use SIEM and Detection Rules to Identify Indicators of Attack under NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - SI.L2-3.14.6
Practical guidance for using SIEM, detection rules and log engineering...
Read more →
How to Use Azure AD and Conditional Access to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - IA.L2-3.5.6: Disable Identifiers After Inactivity
Step-by-step guidance to disable inactive Azure AD accounts using automation,...
Read more →
How to Train Employees to Detect and Report Insider Threat Indicators: Practical Implementation Guide — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AT.L2-3.2.3
Step-by-step guidance for small businesses to implement AT.L2-3.2.3: train personnel...
Read more →
How to Test Your Incident Response Capability: Step-by-Step Guide to NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - IR.L2-3.6.3 Compliance
Practical, step-by-step guidance to plan, execute, and document tests of...
Read more →
How to Securely Dispose and Sanitize Digital and Paper Media Containing CUI: Practical Checklist — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - MP.L2-3.8.1
Step-by-step guidance and a practical checklist to sanitize and dispose...
Read more →
How to Secure Data Centers and Server Rooms to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-14-2 Requirements
Practical, step-by-step guidance for small businesses to secure data centers...
Read more →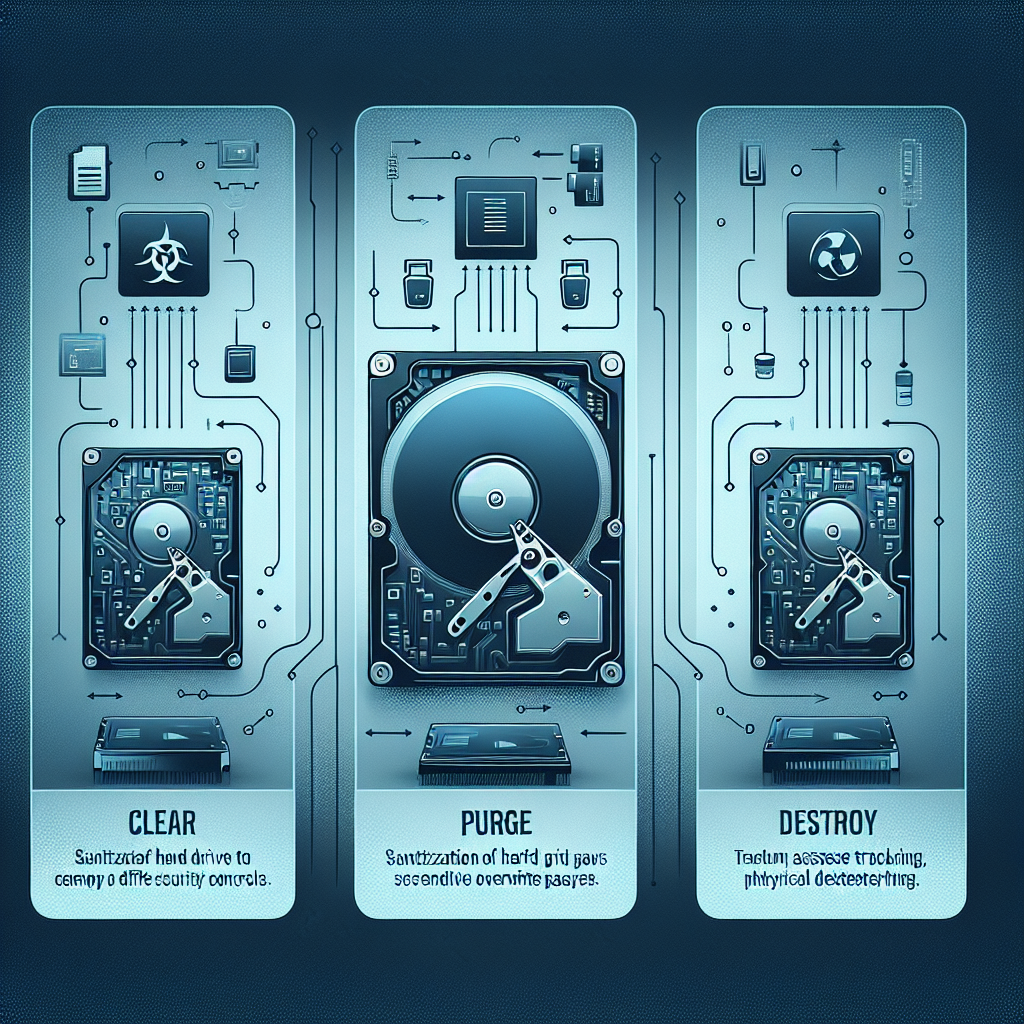
How to Sanitize Hard Drives and SSDs to Comply with FAR 52.204-21 / CMMC 2.0 Level 1 - Control - MP.L1-B.1.VII: NIST SP 800-88 Implementation Steps
Step-by-step guidance to sanitize HDDs and SSDs in line with...
Read more →
How to Sanitize Hard Drives and SSDs Containing Federal Contract Information to Comply with FAR 52.204-21 / CMMC 2.0 Level 1 - Control - MP.L1-B.1.VII
Practical, step-by-step guidance for sanitizing HDDs and SSDs that contain...
Read more →
How to Run Effective Phishing Simulations and Awareness Campaigns for ECC Compliance — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-10-1
Step-by-step guide to run phishing simulations and awareness campaigns to...
Read more →
How to Prioritize and Remediate CVEs Using CVSS for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-10-2
Practical guidance to use CVSS and business context to prioritize,...
Read more →
How to Monitor Visitor Activity and Retain Audit Logs for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - PE.L1-B.1.IX: Tools, Logging Settings, and Retention Policies
[Write a compelling 1-sentence SEO description about this compliance requirement]...
Read more →
How to Map SPF, DKIM, DMARC and Encryption into Your Periodic Email Review under Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-4-4
Practical guidance to map SPF, DKIM, DMARC and email encryption...
Read more →
How to Integrate Security Requirements into DevOps Pipelines to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-6-2
Practical, step-by-step guidance to embed security requirements into DevOps pipelines...
Read more →
How to Implement Visitor Escort Policies to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - PE.L2-3.10.3: A Step-by-Step Guide
Practical step-by-step guidance for small businesses to implement visitor escort...
Read more →
How to Implement Role-Based Access and MFA for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.I: A Step-by-step Guide
Step-by-step guidance to implement role-based access control and multi-factor authentication...
Read more →
How to Implement Physical Protection for Information and Technology Assets: Step-by-Step Guide — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-14-3
Practical, step-by-step guidance to meet Compliance Framework ECC – 2...
Read more →
How to Implement Maintain Audit Logs of Physical Access: Step-by-Step Guide for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - PE.L2-3.10.4
Step-by-step guidance to implement and maintain immutable, auditable physical access...
Read more →
How to Implement FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.I: Step-by-Step Guide to Limiting System Access to Authorized Users and Devices
A practical, step-by-step implementation guide for meeting FAR 52.204-21 /...
Read more →
How to Implement Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-1-1: Step-by-Step Guide to Defining and Documenting Your Cybersecurity Strategy
Step-by-step practical guidance for small businesses to define, document, and...
Read more →
How to Implement DLP and Encryption for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SC.L1-B.1.X Compliance: Practical Steps
Practical step-by-step guidance to implement data loss prevention and encryption...
Read more →
How to Implement Continuous Monitoring and Metrics to Demonstrate Compliance with FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SI.L1-B.1.XII
Step-by-step, practical guidance for small contractors to implement continuous monitoring...
Read more →
How to Implement Cloud Subnets for Public-Facing Systems (AWS/Azure/GCP): FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SC.L1-B.1.XI
Step-by-step guidance to place public-facing systems in segregated cloud subnets...
Read more →
How to Implement Cloud IAM Policies to Meet FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.II with Practical Examples
Step-by-step guidance on designing cloud IAM policies that satisfy FAR...
Read more →
How to Implement Centralized Physical Access Audit Logs to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - PE.L2-3.10.4: Step-by-Step Guide
Step-by-step guidance for small businesses to centralize, protect, and review...
Read more →
How to Implement a Role-Based Security Training Program to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AT.L2-3.2.2 (Step-by-Step Guide)
Step-by-step guidance to design, deploy, and document a role-based security...
Read more →
How to Encrypt, Transport, and Securely Store Digital Media: Practical Steps for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - MP.L2-3.8.1
Step-by-step guidance for small businesses to encrypt, transport, and securely...
Read more →
How to Create an Audit-Ready Risk Assessment Checklist for CUI to Satisfy NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - RA.L2-3.11.1
A practical, step-by-step checklist and evidence guide to perform audit-ready...
Read more →
How to Create an Audit-Ready Checklist for Supervising Unauthorized Maintenance Personnel — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - MA.L2-3.7.6
Step-by-step guidance to build an audit-ready checklist and operational controls...
Read more →
How to create an audit-ready checklist for periodic control assessments (NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - CA.L2-3.12.1)
Practical, step-by-step guidance to build an audit-ready checklist for CA.L2-3.12.1...
Read more →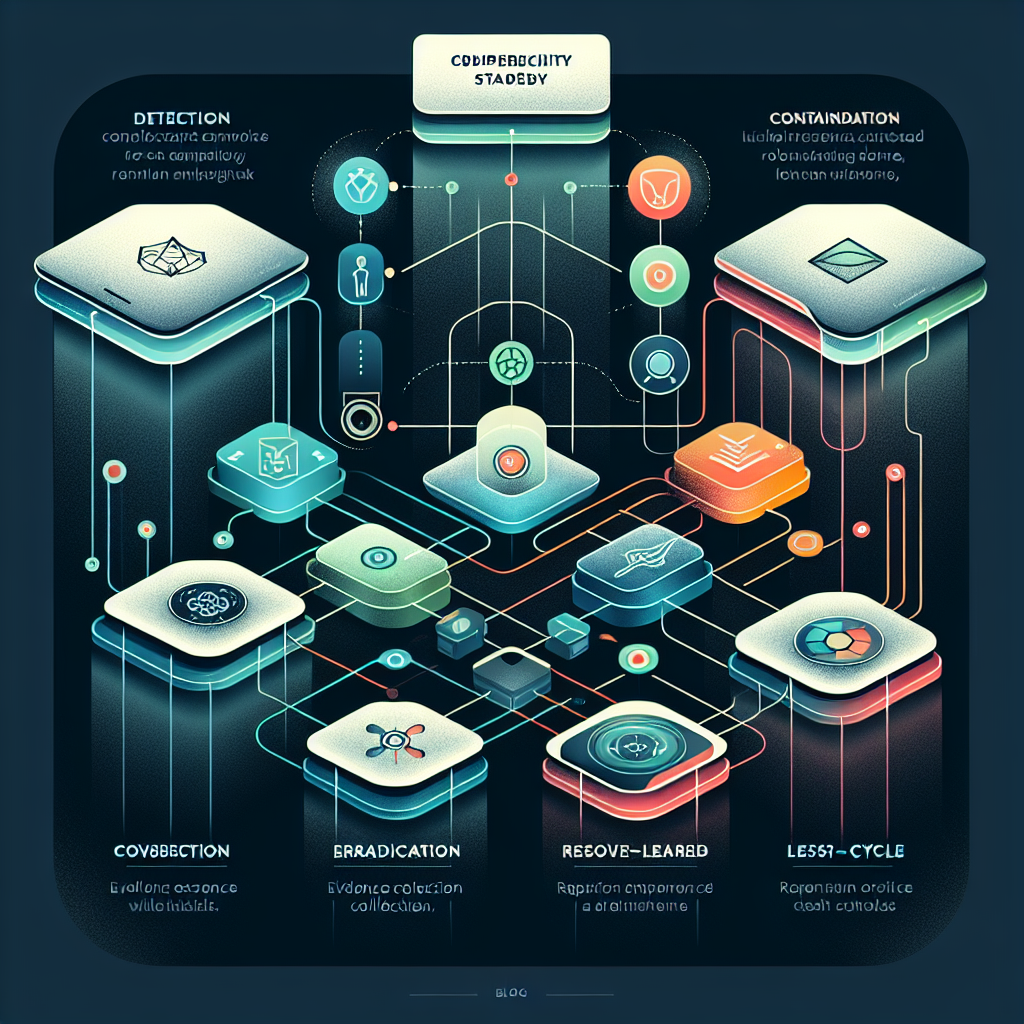
How to Create a Threat Management Playbook to Satisfy Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-13-1 (With Downloadable Template)
Step-by-step guidance and a ready-to-use template to build a threat...
Read more →
How to Create a Step-by-Step Checklist for Periodic Asset Reviews to Achieve Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-1-6 Compliance
Practical, step-by-step checklist and implementation guidance to perform periodic asset...
Read more →
How to Create a SI.L1-B.1.XIII Compliance Checklist: Implementing FAR 52.204-21 / CMMC 2.0 Level 1 Malicious Code Protections
Step-by-step guidance to implement SI.L1-B.1.XIII malicious code protections that satisfy...
Read more →
How to Create a Practical Implementation Checklist for Subnetwork Segmentation — FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SC.L1-B.1.XI
Practical, step-by-step checklist and examples to implement subnetwork segmentation that...
Read more →
How to Create a Penetration Test Requirements Checklist for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-11-3 Compliance
Practical step‑by‑step guidance to build a penetration test requirements checklist...
Read more →
How to Create a Compliant System Security Plan for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - CA.L2-3.12.4: Step-by-Step Template
Step-by-step template and practical guidance to build a compliant System...
Read more →
How to Create a Compliance Checklist to Limit Physical Access under NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - PE.L2-3.10.1
Step‑by‑step guide and practical checklist to limit physical access per...
Read more →
How to Create a Compliance Checklist for Periodic Cloud Service Reviews — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 4-2-4
Step-by-step guidance for building a practical, evidence-based checklist to perform...
Read more →
How to Configure SIEM and Audit Tools to Enforce Privileged-Only Management of Logs (AWS/Azure/On‑Prem) — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AU.L2-3.3.9
Practical steps to configure SIEM and logging systems so only...
Read more →
How to Configure Secure RDP and SSH Session Controls to Satisfy NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AC.L2-3.1.12
Practical, step-by-step guidance to configure RDP and SSH session controls...
Read more →
How to Configure Error Responses to Avoid Revealing Authentication Details: Practical Steps — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - IA.L2-3.5.11
Practical steps to configure consistent, non-revealing authentication error responses to...
Read more →
How to configure endpoint protection and EDR for automatic release updates to meet compliance - FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SI.L1-B.1.XIV
Practical, step-by-step guidance for configuring endpoint protection and EDR automatic...
Read more →
How to Configure Automatic Signature and Engine Updates for AV/EDR to Ensure Malicious Code Protection — FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SI.L1-B.1.XIV
Step-by-step guidance to configure automatic signature and engine updates for...
Read more →
How to Configure Access Control Systems and Audit Trails for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - PE.L1-B.1.IX: Practical Steps
Practical guide to implementing access control systems and tamper-resistant audit...
Read more →
How to Choose and Use Media Destruction Tools (Physical & Logical) to Comply with FAR 52.204-21 / CMMC 2.0 Level 1 - Control - MP.L1-B.1.VII
Practical guidance for selecting and operating physical and logical media...
Read more →
How to Choose and Configure Anti-Malware Tools for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SI.L1-B.1.XIII: Vendor Selection and Deployment
Practical guidance for choosing, configuring, and documenting anti‑malware tools to...
Read more →
How to Build an Organizational Communications Monitoring Plan (Checklist & Tools) — FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SC.L1-B.1.X
Practical checklist and tool recommendations to design an organizational communications...
Read more →
How to Build an IR.L2-3.6.3 Test Plan: Templates and Checklists for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - IR.L2-3.6.3
Practical step-by-step guidance, templates, and checklists to build a test...
Read more →
How to Build an Internal Boundary Monitoring Plan for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SC.L1-B.1.X (Checklist & Tools)
Practical step-by-step guidance and a checklist for building an internal...
Read more →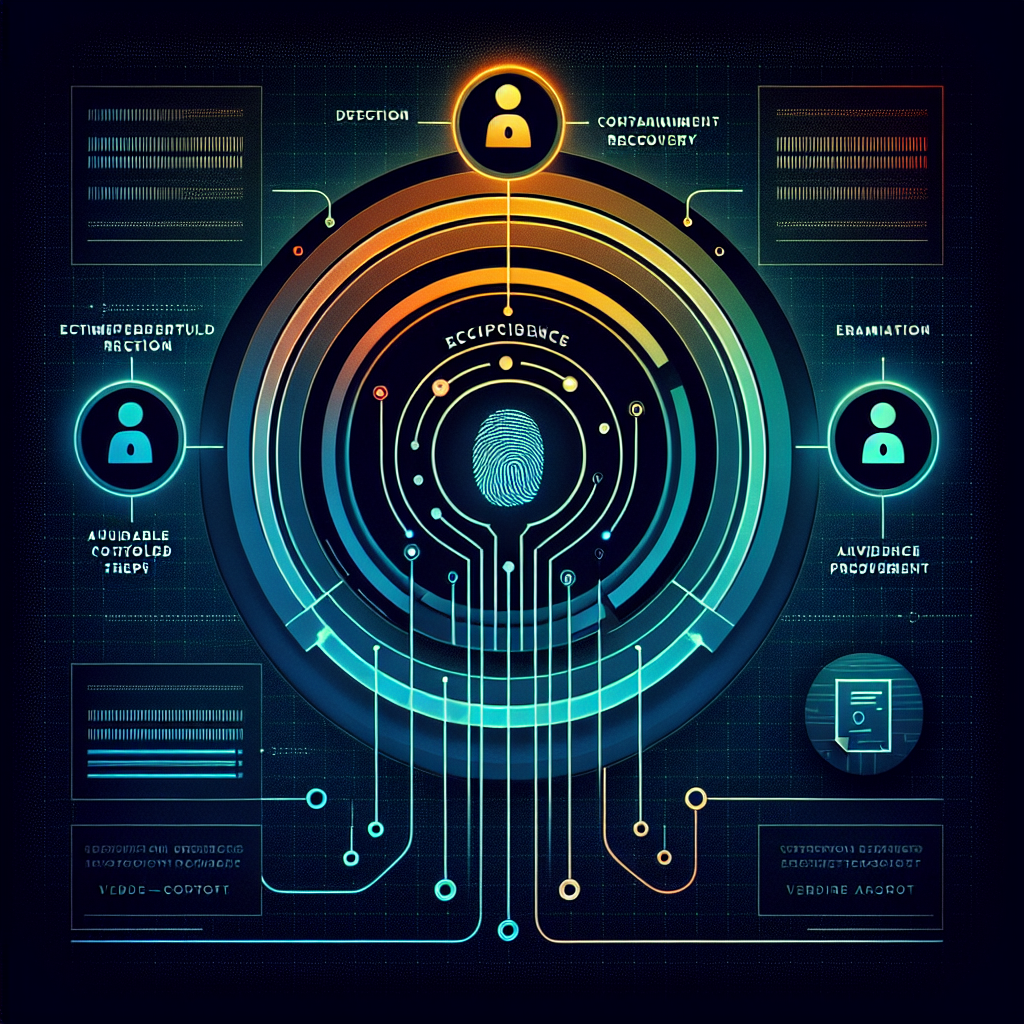
How to Build an Incident Response Plan Aligned with Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-13-3: Templates, Roles, and Runbooks
Practical guidance for implementing Control 2-13-3 of ECC 2:2024 —...
Read more →
How to Build an Automated Monitoring Pipeline for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - CA.L2-3.12.3 Using SIEM and EDR
Step-by-step guidance to build an automated SIEM+EDR monitoring pipeline that...
Read more →
How to Build an Audit-Ready Network Security Requirements Template (Define, Document, Approve) — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-5-1
Step-by-step guidance to define, document, and approve an audit-ready network...
Read more →
How to Build an Audit-Ready Access-Control Policy for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.I: Templates, Controls, and Deployment Checklist
Concrete steps, templates, and a deployment checklist to build an...
Read more →
How to Build a Third-Party Contract Review Checklist for Compliance with Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 4-1-4
Step-by-step guidance to build a third-party contract review checklist that...
Read more →
How to Build a Step-by-Step Visitor Management Process to Meet FAR 52.204-21 / CMMC 2.0 Level 1 - Control - PE.L1-B.1.VIII
Practical, step-by-step guidance for small businesses to implement a visitor...
Read more →
How to build a step-by-step checklist to sanitize equipment before off-site maintenance for CUI compliance — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - MA.L2-3.7.3
Step-by-step guidance to create a practical, auditable sanitization checklist for...
Read more →
How to Build a Step-by-Step Backup and Recovery Policy to Achieve Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-9-1 Compliance
Step-by-step guidance to create a backup and recovery policy that...
Read more →
How to Build a Simple Boundary Monitoring Architecture for Small Businesses to Meet FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SC.L1-B.1.X
Practical step-by-step guidance for small businesses to implement a lightweight...
Read more →
How to Build a Cryptographic Key Management Program That Satisfies Compliance Requirements — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-8-3
Practical, step-by-step guidance to implement a compliant cryptographic key management...
Read more →
How to Build a Compliance-Ready Cloud Security Policy and Template for Hosting Services: Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 4-2-1
Practical, step-by-step guidance and a ready-to-use policy template to make...
Read more →
How to Build a Compliance Checklist for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.IV to Protect Publicly Posted Data
Practical checklist and technical steps to ensure compliance with FAR...
Read more →
How to Build a Cloud Hosting Security Checklist to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 4-2-2
Step-by-step guidance to build a cloud hosting security checklist that...
Read more →
How to Automate Role and Responsibility Reviews with Workflows and Alerts — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-4-2
Step-by-step guidance to automate role and responsibility reviews with workflows...
Read more →
How to Automate Required Risk Assessment Workflows for Ongoing Compliance — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-5-3: Tools, Scripts, and Implementation Steps
Step-by-step guide to automate required risk-assessment workflows for ongoing Compliance...
Read more →
How to Automate Periodic Email Service Compliance Checks for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-4-4
Learn step-by-step how to automate periodic compliance checks for email...
Read more →
Step-by-Step Implementation Plan for an Acceptable Use Policy — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-1-4 Compliance Checklist
A practical, step-by-step plan to design, deploy, and enforce an...
Read more →
Step-by-Step Implementation: Limit Management of Audit Logging Functionality to a Subset of Privileged Users for AU.L2-3.3.9 — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AU.L2-3.3.9
Practical, step-by-step guidance to restrict audit logging management to a...
Read more →
Step-by-Step Guide to Sanitize or Destroy IT Media Before Reuse to Meet FAR 52.204-21 / CMMC 2.0 Level 1 - Control - MP.L1-B.1.VII
Practical, step-by-step instructions to sanitize or destroy IT media to...
Read more →
Step-by-Step Guide: Meeting FAR 52.204-21 / CMMC 2.0 Level 1 - Control - IA.L1-B.1.V to Identify Users, Service Accounts, and Devices
Practical, step-by-step guidance for small businesses to meet FAR 52.204-21...
Read more →
Step-by-Step Checklist to Meet FAR 52.204-21 / CMMC 2.0 Level 1 - Control - MP.L1-B.1.VII: Tools, Verification, and Records
A practical, step-by-step checklist for small businesses to implement tools,...
Read more →
Practical Implementation Checklist: Protecting Systems from Malicious Code to Meet FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SI.L1-B.1.XIII
Step-by-step checklist and technical controls to protect contractor systems from...
Read more →
How to use MDM and policy automation to run periodic mobile device compliance reviews for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-6-4
Practical guide to using MDM and policy automation to run...
Read more →
How to Use Identity Management and MFA to Limit Information System Access to Authorized Entities — FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.I
Practical guide to implementing identity management and multi-factor authentication (MFA)...
Read more →
How to Use AWS/Azure/GCP to Store Cryptographically Protected Passwords in Compliance with NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - IA.L2-3.5.10
Practical guidance for using AWS, Azure, and GCP services and...
Read more →
How to Use an LMS and Automation to Deliver Compliant Security Training for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AT.L2-3.2.2
Practical guide to using an LMS plus automation to meet...
Read more →
How to Run a Compliance‑Ready Insider Threat Awareness Campaign in 90 Days (NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AT.L2-3.2.3)
Step-by-step 90-day plan to design, run, and document an insider...
Read more →
How to recover critical systems after ransomware: step-by-step procedures aligned to Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-9-3
Step-by-step, auditable procedures to recover critical systems after a ransomware...
Read more →
How to Prioritize Vulnerabilities Using Risk Scores to Comply with NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - RA.L2-3.11.3
Learn how to use risk-based vulnerability scoring to meet NIST...
Read more →
How to Prioritize Technical Vulnerabilities Using CVSS and Business Risk for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-10-3 Compliance
Practical guidance for combining CVSS scores with business-impact factors to...
Read more →
How to Prepare for an External Cybersecurity Audit under Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-8-2: Checklist and Timeline
Step-by-step checklist and a practical timeline to prepare a small...
Read more →
How to Pass a Compliance Assessment for SC.L1-B.1.X (Code 553): Quick Implementation Roadmap for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SC.L1-B.1.X
Step-by-step, practical roadmap to implement SC.L1-B.1.X (Code 553) for FAR...
Read more →
How to Label Digital and Physical Media for CUI: Practical Templates and Examples — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - MP.L2-3.8.4
Practical guidance, ready-to-use templates, and small-business examples for labeling digital...
Read more →
How to Integrate Vulnerability Scanning with Patch Management to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - RA.L2-3.11.2
Practical, step-by-step guidance for integrating vulnerability scanning with patch management...
Read more →
How to Integrate Vulnerability Scanning and Patch Management to Satisfy NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - RA.L2-3.11.3
Step-by-step guidance for small businesses to combine vulnerability scanning and...
Read more →
How to Integrate Security Impact Analysis into DevOps Pipelines for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - CM.L2-3.4.4
Practical guide to embedding Security Impact Analysis checks into DevOps...
Read more →
How to Implement Secure Password Storage and Transmission Using PBKDF2, bcrypt, or Argon2 for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - IA.L2-3.5.10
Practical, actionable guidance for small businesses to store and transmit...
Read more →
How to Implement Network Segmentation to Comply with Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-5-3: Diagram, Policies, and Controls
Practical guidance for small and medium organizations to design network...
Read more →
How to Implement Email Authentication (SPF, DKIM, DMARC) for Compliance with Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-4-3
Step-by-step guidance to implement SPF, DKIM, and DMARC for ECC...
Read more →
How to Implement Cloud Subnet Segmentation for Public-Facing Services (AWS/Azure/GCP): FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SC.L1-B.1.XI
[Write a compelling 1-sentence SEO description about this compliance requirement]...
Read more →
How to Implement Cloud and On-Prem Subnetworks for Public-Facing Services: Compliance Checklist for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SC.L1-B.1.XI
Step-by-step checklist to isolate public-facing services into cloud and on-prem...
Read more →
How to Implement an Audit-Ready Risk Assessment Program for CUI: Practical Checklist for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - RA.L2-3.11.1
Step-by-step, audit-focused guidance to implement the RA.L2-3.11.1 risk assessment requirement...
Read more →
How to Implement an Audit-Ready Change Management Process to Track, Review, Approve, Disapprove, and Log Changes — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - CM.L2-3.4.3
Step-by-step guidance to build an audit-ready change management process that...
Read more →
How to Implement a Compliance-Friendly Network Security Management Schedule (Step-by-Step) — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-5-4
Practical, step-by-step guidance to build and maintain a compliance-aligned network...
Read more →
How to Enforce Device and User Authentication for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.I: 8 Technical Controls You Can Deploy Today
Practical, step‑by‑step controls to enforce device and user authentication for...
Read more →
How to Deploy Endpoint DLP and USB Whitelisting to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - MP.L2-3.8.7
Step-by-step guidance to deploy endpoint DLP and USB whitelisting to...
Read more →
How to Create an Evidence-Ready Checklist for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - IA.L1-B.1.V: Users, Processes, and Devices
Practical, evidence-focused guidance for meeting FAR 52.204-21 / CMMC 2.0...
Read more →
How to Create an Audit-Ready Penetration Testing Review Checklist for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-11-4
Step-by-step guide to build an audit-ready penetration testing review checklist...
Read more →
How to Create an Audit-Ready Media Sanitization Checklist for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - MP.L1-B.1.VII
Practical step-by-step guidance to build an audit-ready media sanitization checklist...
Read more →
How to Create an Audit-Ready Compliance Checklist for Information Processing Facilities Under Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-3-2
Practical step-by-step guidance to build an audit-ready checklist for securing...
Read more →
How to Create an Audit-Ready Calendar and Evidence Trail for Role Reviews (step-by-step template) — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-4-2
Create an audit-ready role-review calendar and immutable evidence trail to...
Read more →
How to Create an Approved Hosting & Cloud Security Policy: Step-by-Step Template and Evidence for Auditors — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 4-2-1
Step-by-step guidance, template text, and auditor-ready evidence to create an...
Read more →
How to Create a Practical Compliance Checklist for Personnel Cybersecurity Requirements under Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-9-4
A concise, actionable guide to build a practical compliance checklist...
Read more →
How to Create a Physical Access Policy for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - PE.L1-B.1.VIII, with Templates and Implementation Plan
Step-by-step guidance, templates, and a practical implementation plan to meet...
Read more →
How to Create a Media Sanitization Policy to Comply with FAR 52.204-21 / CMMC 2.0 Level 1 - Control - MP.L1-B.1.VII: Checklist and Templates
Step‑by‑step guide, checklist, and starter policy template to implement media...
Read more →
How to Create a Compliance Checklist for Monitoring External/Internal Boundaries — FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SC.L1-B.1.X
Practical, step-by-step guidance to build a Compliance Framework checklist for...
Read more →
How to Create a Compliance Checklist for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SI.L1-B.1.XIV: Ensuring Malicious Code Protection Is Updated
Step-by-step guidance and a practical checklist to ensure malicious code...
Read more →
How to Configure Your SIEM for Audit Record Reduction and On‑Demand Reporting — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AU.L2-3.3.6
Practical steps to tune your SIEM for audit record reduction...
Read more →
How to Configure Windows and Active Directory to Limit Unsuccessful Logon Attempts — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AC.L2-3.1.8
Step-by-step guidance to configure Windows and Active Directory account lockout...
Read more →
How to Configure VPN and MDM Policies to Enforce NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - SC.L2-3.13.7 (No Split Tunneling)
Step-by-step guidance for configuring VPN servers and MDM policies to...
Read more →
How to Configure Visitor Management Software for Compliance with NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - PE.L2-3.10.3
Step-by-step guide to configuring visitor management software to meet NIST...
Read more →
How to Configure SPF, DKIM and DMARC to Secure Your Email Service — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-4-3
Step-by-step guidance to implement SPF, DKIM and DMARC for Compliance...
Read more →
How to Configure MDM and DLP to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - MP.L2-3.8.8 and Prevent Unowned USB Use
Step-by-step guidance to use MDM and Endpoint DLP to enforce...
Read more →
How to Configure Logging, Monitoring, and Alerts to Satisfy Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-13-3 Compliance
Step-by-step guidance for small businesses to implement centralized logging, effective...
Read more →
How to Configure Endpoint Controls for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AC.L2-3.1.21: Blocking and Managing Portable Storage Devices
Step‑by‑step guidance for blocking and managing portable storage devices to...
Read more →
How to Configure "Deny All, Permit by Exception" in AWS for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - SC.L2-3.13.6: Practical VPC and Security Group Rules
Step-by-step guidance for implementing a 'deny all, permit by exception'...
Read more →
How to Configure Cloud Remote Access Encryption (VPN, TLS, and SASE) for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AC.L2-3.1.13 Compliance
Step-by-step guidance to encrypt cloud remote access sessions (VPN, TLS,...
Read more →
How to Configure AWS VPC Subnetworks for Public-Facing Assets (FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SC.L1-B.1.XI) — Practical Guide
Step-by-step guidance to isolate and secure public-facing AWS resources in...
Read more →
How to Conduct a Gap Analysis for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-7-2: Meet International Agreement Requirements Step-by-Step
Practical step-by-step guidance to perform a gap analysis for ECC‑2:2024...
Read more →
How to Comply with FAR 52.204-21 / CMMC 2.0 Level 1 - Control - IA.L1-B.1.V (Code 548): Practical Mapping of System Users and Agents
Step-by-step guidance to inventory, classify, and document system users and...
Read more →
How to Build an Ongoing Security Controls Monitoring Program for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - CA.L2-3.12.3 (Checklist & Tools)
Practical, step-by-step guidance and tool recommendations to implement an ongoing...
Read more →
How to Build a Visitor Monitoring and Escort Program: Implementation Checklist for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - PE.L1-B.1.IX
Step-by-step implementation checklist to create a visitor monitoring and escort...
Read more →
How to Build a Step-by-Step Test Plan to Validate NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - IR.L2-3.6.3 — Test the Organizational Incident Response Capability
A practical, step-by-step guide to designing and executing test plans...
Read more →
How to Build a Step-by-Step Security Awareness Program for Managers, System Administrators, and Users — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AT.L2-3.2.1
Step-by-step guidance to build a role-based security awareness program that...
Read more →
How to Build a Step-by-Step Cryptography Review Checklist for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-8-4
A practical, step-by-step guide to building a cryptography review checklist...
Read more →
How to Build a Practical Media Sanitization SOP for Federal Contract Information (FCI) Disposal or Reuse: Checklist + Templates — FAR 52.204-21 / CMMC 2.0 Level 1 - Control - MP.L1-B.1.VII
Step-by-step guidance, checklists, and templates to build a media sanitization...
Read more →
How to Build a Penetration Testing Requirements Template and Approval Workflow for Compliance — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-11-1
Learn how to create a penetration testing requirements template and...
Read more →
How to Build a Compliant DMZ on AWS to Segregate Public Components from Internal Networks — FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SC.L1-B.1.XI
Step-by-step guidance to design and operate a FAR 52.204-21 /...
Read more →
How to Build a Communications Monitoring Program to Meet FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SC.L1-B.1.X (Checklist + Configuration Examples)
Practical guide to design and implement a communications monitoring program...
Read more →
How to build a centralized logging architecture (SIEM) for event monitoring and compliance with Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-12-3
Practical steps for designing and operating a centralized SIEM logging...
Read more →
How to Automate Periodic Policy Reviews with Tools and Templates — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-3-4
Automate and evidence periodic policy reviews for Compliance Framework Control...
Read more →
How to Automate Periodic Penetration Testing Requirement Reviews to Maintain Compliance with Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-11-4
Learn a practical, step-by-step approach to automating periodic penetration-testing requirement...
Read more →
How to Automate Periodic Identity and Access Management Reviews for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-2-4: Tools and Playbook
Practical guide to automating periodic Identity and Access Management reviews...
Read more →
How to Automate Classification and Labeling Across Cloud and On-Prem Systems: Implementation Tips for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-1-5
Practical guidance to automate data classification and labeling across cloud...
Read more →
How to Audit and Remediate Publicly Posted Data for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.IV
Practical steps to discover, remediate, and monitor publicly posted data...
Read more →
How to Audit and Remediate Public Content for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.IV: Checklist, Tools, and Compliance Steps
Step-by-step guide to discovering, auditing, and remediating public-facing content to...
Read more →
How to Align NIST and ISO Practices with Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-5-2 for Practical Implementation
Practical step-by-step guidance to align NIST and ISO access and...
Read more →
20 Actionable Steps to Meet FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.III: Verify, Restrict, and Monitor External Information System Use
Practical, step-by-step guidance to verify, restrict, and monitor use of...
Read more →
Step-by-Step Guide to Mapping Users, Service Accounts, and Devices for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - IA.L2-3.5.1
Practical, step‑by‑step instructions to discover, inventory, and map users, service...
Read more →
Step-by-Step Guide: How to Conduct an Audit-Ready Periodic Email Service Review for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-4-4
Practical, audit-focused steps for small businesses to review and document...
Read more →
Step-by-Step Guide: Establishing Update Policies for Antivirus/EDR to Comply with FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SI.L1-B.1.XIV
Practical, step-by-step guidance to create and evidence antivirus/EDR update policies...
Read more →
Step-by-Step Checklist: Verifying and Controlling Remote and Third-Party Connections for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.III
Practical, step-by-step checklist to verify and control remote and third‑party...
Read more →
Step-by-step checklist for limiting system access to authorized users, processes, and devices — FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.I
A practical, step-by-step checklist to implement FAR 52.204-21 / CMMC...
Read more →
Practical Checklist: Identify, Report, and Correct Flaws Quickly for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - SI.L2-3.14.1 Compliance
Straightforward, actionable checklist to help small businesses identify, report, and...
Read more →
How to use IAM tools (Azure AD, Okta, AWS IAM) to enforce FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.II: step-by-step setups
Practical, step-by-step guidance to use Azure AD, Okta, and AWS...
Read more →
How to Use DLP and MDM to Prohibit Unowned External Storage: Implementation Checklist for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - MP.L2-3.8.8
[Write a compelling 1-sentence SEO description about this compliance requirement]...
Read more →
How to Use Cloud Security Posture Management (CSPM) Tools to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 4-2-4 Periodic Review Requirements
Practical guidance on using CSPM tools to implement and evidence...
Read more →
How to Use an Acceptable Use Policy Template to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-1-4 Requirements — Template + Customization Tips
Learn how to adapt an acceptable use policy template to...
Read more →
How to Select and Verify Sanitization Methods (Overwrite, Degauss, Physical Destroy) for Federal Contract Information: FAR 52.204-21 / CMMC 2.0 Level 1 - Control - MP.L1-B.1.VII (Code 550)
Practical, step-by-step guidance for small businesses to select and verify...
Read more →
How to Sanitize SSDs and Mobile Devices Containing Federal Contract Information: FAR 52.204-21 / CMMC 2.0 Level 1 - Control - MP.L1-B.1.VII Technical Methods Explained
Step-by-step guidance to securely sanitize SSDs and mobile devices to...
Read more →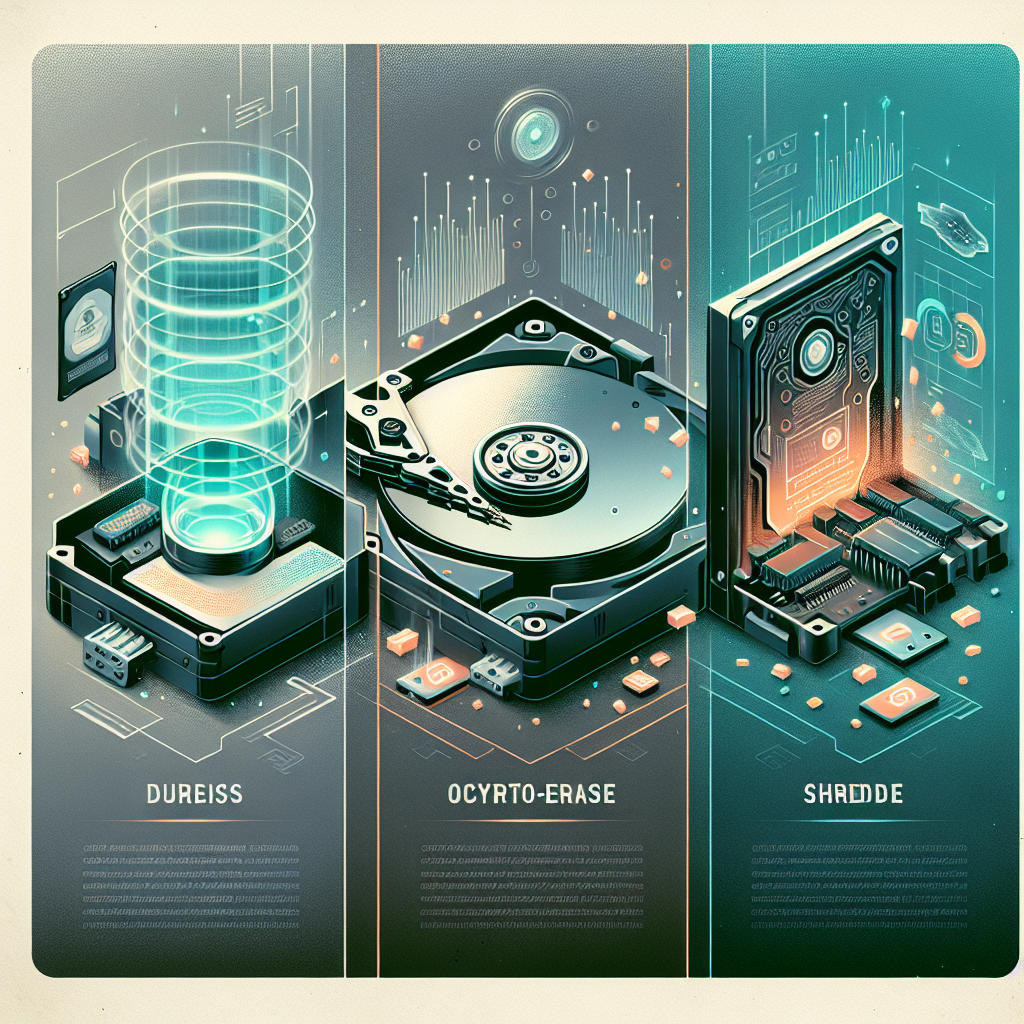
How to Sanitize or Destroy Hard Drives and SSDs to Meet FAR 52.204-21 / CMMC 2.0 Level 1 - Control - MP.L1-B.1.VII: Practical Methods (Degauss, Overwrite, Crypto-Erase, Shredding)
Practical, step-by-step methods for sanitizing and destroying HDDs and SSDs...
Read more →
How to Run a Gap Assessment and Remediation Roadmap for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - SC.L2-3.13.1
Step-by-step guide to assess gaps and build a prioritized remediation...
Read more →
How to Recruit and Verify Experienced Saudi Cybersecurity Professionals to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-2-2 Compliance
Practical steps for recruiting, vetting, and verifying experienced Saudi cybersecurity...
Read more →
How to Recruit and Staff a Dedicated Cybersecurity Team: Job Descriptions, Skills, and Budgeting for Compliance — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-2-1
Practical guidance to recruit, staff, and budget a dedicated cybersecurity...
Read more →
How to Prioritize CVEs and Mitigate High-Risk Vulnerabilities for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-10-2
A practical guide to triaging CVEs, assigning remediation SLAs, and...
Read more →
How to Prepare for an External Audit of Periodic Personnel Cybersecurity Reviews: Checklist for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-9-6
Step‑by‑step checklist and practical guidance to prepare for an external...
Read more →
How to Prepare for a CMMC Assessment: Demonstrating Visitor Escort, Audit Logs, and Access Device Control for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - PE.L1-B.1.IX
[Write a compelling 1-sentence SEO description about this compliance requirement]...
Read more →
How to Prepare Audit-Ready Training Records for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AT.L2-3.2.2: A Practical Checklist
Step-by-step guidance for small businesses to prepare tamper-evident, auditable training...
Read more →
How to perform a step-by-step gap analysis for national cybersecurity laws to achieve Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-7-1 compliance
A practical step-by-step guide to performing a gap analysis against...
Read more →
How to Implement Zero Trust Network Principles to Achieve Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-5-3 Compliance
Practical, step-by-step guidance for small organizations to implement Zero Trust...
Read more →
How to Implement User, Process, and Device Identification for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - IA.L1-B.1.V: A Step-by-Step Checklist
A practical, step-by-step checklist for small businesses to identify and...
Read more →
How to Implement Removable Media Controls on Endpoints: Step-by-Step Guide for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - MP.L2-3.8.7
Learn step-by-step how to design, enforce, and audit removable media...
Read more →
How to Implement Physical Access Controls for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - PE.L1-B.1.VIII: Step-by-Step Checklist for Small Contractors
Practical, step-by-step guidance for small contractors to implement the physical...
Read more →
How to Implement Multi-Factor Authentication for Email Services per Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-4-3
Step-by-step guidance to enforce Multi-Factor Authentication (MFA) for email services...
Read more →
How to Implement FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SI.L1-B.1.XIV: Step-by-Step Guide to Updating Malicious Code Protection Mechanisms
Practical step-by-step guidance for small businesses to meet FAR 52.204-21...
Read more →
How to implement Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-6-1 in the project lifecycle: templates and practical workflows
Practical, actionable guidance to implement ECC‑2:2024 Control 1‑6‑1 across your...
Read more →
How to Implement Cloud IAM Policies (AWS/Azure) to Limit User Functions for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.II
Practical, step-by-step guidance to implement AWS and Azure IAM policies...
Read more →
How to Implement Background Screening for CUI: Step-by-Step Guide to NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - PS.L2-3.9.1
A practical, step-by-step guide to designing and operating a compliant...
Read more →
How to Implement Background Screening for CUI Access: NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - PS.L2-3.9.1 Step-by-Step
Practical, step-by-step guidance for small businesses to implement background screening...
Read more →
How to Harden Endpoints: Practical Steps to Restrict Programs, Functions, Ports and Protocols for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - CM.L2-3.4.7
Practical, step-by-step guidance to restrict programs, functions, ports and protocols...
Read more →
How to Gather and Present Audit-Ready Evidence from IR Tests to Satisfy NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - IR.L2-3.6.3
Practical guidance for collecting, organizing, and presenting incident response (IR)...
Read more →
How to Document and Prove Boundary Controls for Audits and Assessments — FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SC.L1-B.1.X
Practical guidance on documenting and providing evidence of network and...
Read more →
How to Develop a Plan of Action (POA&M) for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - CA.L2-3.12.2: Step-by-Step Template to Correct Deficiencies
Step-by-step POA&M template to help organizations document, prioritize, and remediate...
Read more →
How to Deploy TLS 1.2/1.3 for Secure CUI Transfers and Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - SC.L2-3.13.8
Step-by-step guidance for implementing and validating TLS 1.2/1.3 deployments so...
Read more →
How to Create and Periodically Update an SSP Template with Evidence — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - CA.L2-3.12.4
Step-by-step guidance for building and maintaining a System Security Plan...
Read more →
How to Create an Implementation Checklist and Evidence Package for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - IA.L1-B.1.V
Step-by-step guidance to build an implementation checklist and evidence package...
Read more →
How to Create an Audit-Ready Incident Review Process to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-13-4
Learn a practical, step-by-step approach to build an audit-ready incident...
Read more →
How to Create an Audit-Ready Data Protection Review Checklist for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-7-4
Step-by-step guidance to build an audit-ready data protection review checklist...
Read more →
How to Create an Audit-Ready Checklist for Updating Malicious Code Protection (FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SI.L1-B.1.XIV)
Step-by-step guidance to build an audit-ready checklist ensuring your malicious...
Read more →
How to Create a Weekly Audit Checklist to Review and Update Logged Events (NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AU.L2-3.3.3)
Learn how to build a practical weekly audit checklist to...
Read more →
How to create a third-party contract review checklist aligned with Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 4-1-4
Step-by-step guidance to build a practical third‑party contract review checklist...
Read more →
How to Create a Step-by-Step Patch and Signature Update Checklist for Malicious Code Protection — FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SI.L1-B.1.XIV
Step-by-step guidance to build a practical patch and malware-signature update...
Read more →
How to Create a Compliance Checklist and Evidence Template for ECC 2-10-4 Periodic Vulnerability Reviews — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-10-4
Step-by-step guidance to build a practical compliance checklist and evidence...
Read more →
How to Configure SIEM to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - SI.L2-3.14.3: Monitor System Security Alerts and Automate Response Workflows
Practical, step-by-step guidance to configure your SIEM and SOAR to...
Read more →
How to Configure Nessus to Fulfill NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - RA.L2-3.11.2: Credentialed Scans, Plugins, and Scan Templates
Step-by-step guidance to configure Nessus credentialed scans, select plugins, and...
Read more →
How to Configure IAM and MFA to Meet FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.I: Enforce Authorized User and Device Access
Practical guidance to configure identity and multifactor authentication (MFA) controls...
Read more →
How to Configure Firewalls, VPNs, and TLS to Comply with FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SC.L1-B.1.X
Practical, small-business focused steps to configure firewalls, VPNs, and TLS...
Read more →
How to Configure Endpoint Protection to Auto-Apply New Releases and Stay Compliant — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - SI.L2-3.14.4
Practical guidance to configure endpoint protection to automatically apply vendor...
Read more →
How to Choose Tools and Methods to Sanitize Hard Drives and Mobile Devices Containing CUI — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - MA.L2-3.7.3
Practical guidance to select tools and techniques to sanitize hard...
Read more →
How to Choose the Right Sanitization Methods (Overwrite, Degauss, Physical Destruction) for FCI: FAR 52.204-21 / CMMC 2.0 Level 1 - Control - MP.L1-B.1.VII Guide
Practical guidance to choose and implement overwrite, degauss, and physical...
Read more →
How to Build Audit-Ready Configuration Baselines to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - CM.L2-3.4.2 (Templates & Checklist)
Step-by-step guide to build audit-ready configuration baselines to satisfy NIST...
Read more →
How to Build an Internal Audit Program to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-8-2 Requirements: Practical Checklist
A practical, step-by-step guide to designing an internal audit program...
Read more →
How to Build an External System Access Policy for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.III: Practical Templates and Checklists
Step-by-step guidance to create an External System Access Policy that...
Read more →
How to Build an Audit-Ready Scanning Program (Periodic + Real-Time) for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SI.L1-B.1.XV
Practical steps to design and operate an audit-ready periodic and...
Read more →
How to Build an Audit-Ready Log Management System for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-12-2 Compliance
Step-by-step guidance to implement an audit-ready, centralized log management system...
Read more →
How to Build a Technical Vulnerability Management Program to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-10-3
Step-by-step guidance to design and operate a technical vulnerability management...
Read more →
How to Build a Step-by-Step System Maintenance Control Program to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - MA.L2-3.7.2
Step-by-step guide to creating a system maintenance control program that...
Read more →
How to build a step-by-step checklist to meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-9-6 for personnel cybersecurity reviews
Practical step-by-step checklist and implementation guidance to meet ECC–2:2024 Control...
Read more →
How to Build a Risk-Based POA&M Template for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - CA.L2-3.12.2 to Reduce and Eliminate Vulnerabilities
Step-by-step guidance and a practical POA&M template to meet NIST...
Read more →
How to Build a Repeatable Third-Party Contract Review Program (Implementation Guide) - Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 4-1-4
Step-by-step implementation guidance to build a repeatable third-party contract review...
Read more →
How to Build a Practical Physical Access Checklist to Meet FAR 52.204-21 / CMMC 2.0 Level 1 - Control - PE.L1-B.1.VIII Requirements
Practical guidance and a ready-to-use checklist to implement physical access...
Read more →
How to Build a Deny-All, Permit-by-Exception Whitelisting Policy for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - CM.L2-3.4.8 (Checklist + Templates)
Step-by-step guidance to implement a deny-all, permit-by-exception application whitelisting policy...
Read more →
How to Build a Compliance Checklist for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - PE.L2-3.10.6 to Protect CUI in Home Offices and Remote Locations
[Write a compelling 1-sentence SEO description about this compliance requirement]...
Read more →
How to Build a Compliance Checklist for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.IV to Prevent Unintended Data Exposure
Practical, step-by-step guidance for small businesses to implement AC.L1-B.1.IV under...
Read more →
How to Build a Compliance Checklist for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-7-1 to Meet National Cybersecurity Regulations
Step-by-step guide to creating a practical compliance checklist for ECC...
Read more →
How to Avoid Conflicts of Interest in Cybersecurity Audits: Compliance Steps for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-8-2
Practical, step-by-step guidance for small businesses to prevent and manage...
Read more →
How to Automate Periodic Vulnerability Assessments and Reporting for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-10-4
Step-by-step guidance to automate recurring vulnerability assessments and generate audit-ready...
Read more →
How to Automate Periodic Reviews of Cybersecurity Roles with Workflows and RBAC — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-4-2
Practical, step-by-step guidance for automating periodic reviews of cybersecurity roles...
Read more →
How to Automate Continuous Monitoring and Periodic Assessments of CUI — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - RA.L2-3.11.1
Practical steps and automation recipes to meet RA.L2-3.11.1 for continuous...
Read more →
How Small Contractors Can Meet FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SI.L1-B.1.XII: Fast Vulnerability Reporting & Patching Workflows
Practical steps, tools, and SLAs small contractors can use to...
Read more →
Step-by-Step Terraform Templates to Create Compliant Subnetworks for Public Services: FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SC.L1-B.1.XI
[Write a compelling 1-sentence SEO description about this compliance requirement]...
Read more →
Step-by-Step Guide to Meeting FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SI.L1-B.1.XV: Configure Periodic System Scans and Real-Time External File Scanning
Practical, step-by-step guidance to implement periodic system scans and real-time...
Read more →
Step-by-Step Guide: Deploying Hardware-Encrypted USBs to Protect CUI in Transit — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - MP.L2-3.8.6
Learn practical, step-by-step procedures to deploy hardware-encrypted USBs to protect...
Read more →
Practical SSP Template and Checklist to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - CA.L2-3.12.4 (Fillable Examples Inside)
Step-by-step SSP template, POA&M example, and checklist to implement CA.L2-3.12.4...
Read more →
Implementing Visitor Escort, Monitor Visitor Activity, and Maintain Audit Logs to Meet FAR 52.204-21 / CMMC 2.0 Level 1 - Control - PE.L1-B.1.IX: A Practical Guide
Practical, step-by-step guidance for small businesses to implement visitor escort,...
Read more →
Implementing Technical and Operational Safeguards for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-3-2: A 10-Point Checklist
Practical, actionable 10-point checklist to implement Control 2-3-2 of the...
Read more →
Implementing FAR 52.204-21 / CMMC 2.0 Level 1 - Control - IA.L1-B.1.V: Practical Checklist to Identify Users, Processes Acting on Behalf of Users, and Devices
A practical, step-by-step checklist to identify and inventory users, processes...
Read more →
How to Use Templates and Policies to Stand Up a Compliant Cybersecurity Function: Ready-to-Use Tools for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-2-1
Practical, ready-to-use policy and template guidance to help small organizations...
Read more →
How to Use KPIs and Metrics to Review Cybersecurity Awareness Effectiveness Quarterly — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-10-5
Practical guidance on defining, collecting, and reporting quarterly KPIs to...
Read more →
How to Use Free and Commercial Tools to Build an Inventory & Baseline Program — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - CM.L2-3.4.1 (Tool Comparison + Implementation Tips)
Practical guidance and tool comparisons (free and commercial) to build...
Read more →
How to Turn Audit Findings Into Actionable Recommendations: Practical Report Templates and Evidence for Compliance Reviews — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-8-3
Practical guidance to convert audit findings into clear, testable remediation...
Read more →
How to Track, Measure, and Produce Evidence of Training Compliance for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AT.L2-3.2.2
Practical step-by-step guidance for tracking, measuring, and producing auditable evidence...
Read more →
How to Select and Deploy Scanning Tools (AV, EDR, CASB) for Compliance with FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SI.L1-B.1.XV
Practical guidance for selecting and deploying antivirus (AV), endpoint detection...
Read more →
How to Sanitize Equipment Before Off-Site Maintenance: A Step-by-Step Guide for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - MA.L2-3.7.3
Step-by-step guidance to sanitize devices before off-site maintenance to meet...
Read more →
How to Run Tabletop Exercises and Technical Simulations to Test Incident Response for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - IR.L2-3.6.3
Step-by-step guidance on running tabletop exercises and technical simulations to...
Read more →
How to Run Simulated Phishing and Ransomware Drills to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-10-3 Requirements
Step-by-step guidance for running phishing and ransomware simulation drills to...
Read more →
How to Recruit and Assess Experienced Saudi Cybersecurity Talent for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-2-2: Interview Guides, Skill Tests, and Scoring Rubrics
Practical, step-by-step guidance for hiring and evaluating experienced Saudi cybersecurity...
Read more →
How to Prepare for a CMMC Assessment: Demonstrating Compliance with FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.IV (Control 547) — Evidence, Artifacts, and Best Practices
Practical guidance for small businesses to collect the evidence, implement...
Read more →
How to Perform Secure Data Destruction for USBs, Hard Drives, and Mobile Devices Under FAR 52.204-21 / CMMC 2.0 Level 1 - Control - MP.L1-B.1.VII
Practical, step-by-step guidance for securely sanitizing and destroying USBs, HDDs,...
Read more →
How to Pass a Compliance Audit: Documenting and Approving Physical Protection Requirements for Information and Technology Assets — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-14-1
Practical, step-by-step guidance for documenting and approving physical protection requirements...
Read more →
How to Monitor Cloud Inbound/Outbound Communications and Prove Compliance — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - SI.L2-3.14.6
Practical, step-by-step guidance for monitoring cloud inbound/outbound communications and collecting...
Read more →
How to Integrate SAST and DAST into CI/CD Pipelines for Compliance — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-6-3
Practical guidance to integrate SAST and DAST into CI/CD pipelines...
Read more →
How to Implement SPF, DKIM, and DMARC for Email Service Security under Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-4-2
Step-by-step guidance for small businesses to implement SPF, DKIM, and...
Read more →
How to Implement Periodic and Real-Time File Scanning for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SI.L1-B.1.XV: A Step-by-Step Guide
Practical, step-by-step guidance to implement periodic and real-time file scanning...
Read more →
How to Implement Non-Privileged IAM Roles in AWS, Azure, and GCP for Nonsecurity Functions — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AC.L2-3.1.6
Step-by-step guidance to define, deploy, and audit non-privileged IAM roles...
Read more →
How to implement low-cost secure media destruction for small contractors — FAR 52.204-21 / CMMC 2.0 Level 1 - Control - MP.L1-B.1.VII
Practical, low-cost methods and step-by-step controls for small contractors to...
Read more →
How to Implement Low-Cost Physical Access Controls to Comply with FAR 52.204-21 / CMMC 2.0 Level 1 - Control - PE.L1-B.1.IX
Practical, low-cost physical access control strategies and step-by-step actions small...
Read more →
How to Implement FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.III: Step-by-Step Guide to Verifying and Limiting External Information System Connections
Practical step-by-step guidance for small businesses to verify and limit...
Read more →
How to Implement Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-6-4: A Step-by-Step Guide to Periodically Reviewing Project Management Cybersecurity Requirements
Step-by-step guidance for Compliance Framework Control 1-6-4: how to set...
Read more →
How to Implement Endpoint Detection and Response to Identify Unauthorized Use of Organizational Systems — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - SI.L2-3.14.7
[Write a compelling 1-sentence SEO description about this compliance requirement]...
Read more →
How to Implement Contractual Cybersecurity Requirements for Vendors: A Step-by-Step Guide — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 4-1-2
Practical, step-by-step guidance for drafting, negotiating, and enforcing contractual cybersecurity...
Read more →
How to Implement Continuous Monitoring for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - CA.L2-3.12.3: Step-by-Step Plan for Ongoing Control Effectiveness
Practical, step-by-step guidance to implement continuous monitoring for CA.L2-3.12.3 so...
Read more →
How to Implement an Automated Vulnerability Scanning and Reporting Pipeline for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - SI.L2-3.14.1
Step-by-step guidance to design, implement, and document an automated vulnerability...
Read more →
How to Implement a Step-by-Step Media Sanitization Process for FCI Disposal and Reuse — FAR 52.204-21 / CMMC 2.0 Level 1 - Control - MP.L1-B.1.VII
Practical, step-by-step guidance for small businesses to sanitize media containing...
Read more →
How to Implement a Step-by-Step Media Protection Plan to Protect System Media Containing CUI (Paper & Digital) — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - MP.L2-3.8.1
Step-by-step guidance to create a media protection plan that secures...
Read more →
How to Document System Boundaries and Environments of Operation for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - CA.L2-3.12.4 (Template + Example SSP Sections)
Step-by-step guidance and ready-to-use SSP templates to document system boundaries...
Read more →
How to document data classification and handling procedures to satisfy Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-7-1: examples & templates
Step-by-step guidance, templates, and examples to document data classification and...
Read more →
How to Deploy Encryption and Secure Signaling for VoIP to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - SC.L2-3.13.14
Step-by-step guidance to implement SRTP/DTLS and SIP-TLS for VoIP to...
Read more →
How to Deploy Automated Discovery and Continuous Monitoring for Asset Management — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-1-2
Step-by-step guidance to implement automated discovery and continuous monitoring to...
Read more →
How to Deploy Application Whitelisting at Scale Using Intune, SCCM, and EDR to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - CM.L2-3.4.8
Practical guidance for implementing application whitelisting at scale with Intune,...
Read more →
How to Demonstrate Compliance With SI.L1-B.1.XII: Evidence, Timelines, and Best Practices for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SI.L1-B.1.XII
Practical guidance for small businesses to collect evidence, set timelines,...
Read more →
How to Create an Evidence-Ready Training Plan for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AT.L2-3.2.2 (Templates & Checklist)
Step-by-step guidance and ready-to-use templates to build an evidence-ready, role-based...
Read more →
How to Create an Audit-Ready Penetration Testing Review Process Aligned to ECC 2-11-4 (Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-11-4)
Practical, step-by-step guidance to build an audit-ready penetration testing review...
Read more →
How to Create an Audit-Ready Evidence Pack for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-7-1: Templates and Checklists
Practical guide to building an audit-ready evidence pack for ECC...
Read more →
How to Create a Step-by-Step Audit Checklist for Periodic Reviews of External Web Applications — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-15-4
Practical, step-by-step guidance to build an auditable checklist for periodic...
Read more →
How to create a reusable checklist and evidence templates for reviewing external web applications under Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-15-4
A practical guide to building a reusable checklist and evidence...
Read more →
How to Create a Compliance Checklist for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - MA.L2-3.7.4: Validating Removable Test Media for Malicious Code
A practical guide to build a NIST SP 800-171 Rev.2...
Read more →
How to Configure Windows AppLocker and Group Policy for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - CM.L2-3.4.8: Practical Implementation Steps
Step-by-step guidance to implement AppLocker via Group Policy to meet...
Read more →
How to Configure Web Servers and Cloud Storage for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.IV Compliance: Practical Implementation Steps
Practical, step-by-step guidance to configure web servers and cloud storage...
Read more →
How to Configure TLS and Encryption Settings to Satisfy Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-8-2 for Web and API Traffic
Practical, step-by-step guidance to configure TLS and encryption for web...
Read more →
How to Configure SPF, DKIM, and DMARC for Compliance with Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-4-3
Step‑by‑step guidance for small businesses to implement SPF, DKIM, and...
Read more →
How to Configure SIEM Alerts and Review Workflows for Ongoing Monitoring Management — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-12-4
Practical, step-by-step guidance for configuring SIEM alerts and review workflows...
Read more →
How to Configure Network Segmentation and Boundary Controls for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SC.L1-B.1.X
Practical, step-by-step guidance for implementing network segmentation and boundary controls...
Read more →
How to Configure Multi-Factor Authentication to Comply with FAR 52.204-21 / CMMC 2.0 Level 1 - Control - IA.L1-B.1.VI for Users, Processes, and Devices
Practical, step-by-step guidance to implement MFA for users, processes, and...
Read more →
How to Configure Endpoints for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - SC.L2-3.13.12: Technical Implementation Checklist to Block Remote Webcam/Mic Activation and Show Device Status
Practical, platform-specific steps and checks to meet NIST SP 800-171...
Read more →
How to Conduct and Document Penetration Tests to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-11-2 Requirements
Practical, step-by-step guidance for small businesses to plan, execute, and...
Read more →
How to Build Practical Checklists and Templates for Periodic Reviews of Business Continuity Cybersecurity Requirements — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 3-1-4
Step-by-step guidance and ready-to-use checklist templates to meet ECC 2:2024...
Read more →
How to Build an Independent Cybersecurity Function for SMEs: Practical Roadmap for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-2-1
Step-by-step guidance for SMEs to establish an independent cybersecurity function...
Read more →
How to Build an Audit-Ready Inventory for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - IA.L1-B.1.V: Practical Steps to Identify Users, Processes Acting for Users, and Devices
Step-by-step guidance for small businesses to create an audit-ready inventory...
Read more →
How to Build an Asset Inventory for Hardware, Software & Firmware to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - CM.L2-3.4.1
Step-by-step guidance for creating and maintaining a hardware, software, and...
Read more →
How to Build an Asset & Identity Inventory for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - IA.L2-3.5.1: Practical Implementation Checklist
Step-by-step practical guidance to build and maintain a combined asset...
Read more →
How to Build an AC.L1-B.1.I Compliance Checklist for FAR 52.204-21 / CMMC 2.0 Level 1: Policies, Technical Controls, and Audit Evidence
Step-by-step guide to build an AC.L1-B.1.I compliance checklist aligned to...
Read more →
How to Build a Penetration Testing Review Checklist and Evidence Package for Compliance — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-11-4
Step-by-step guidance to build a penetration testing review checklist and...
Read more →
How to Build a Compliance Checklist for Updating Malicious Code Protection Mechanisms — FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SI.L1-B.1.XIV
Step-by-step checklist to keep malicious code protection mechanisms updated to...
Read more →
How to Build a Complete Hardware, Software, and Firmware Inventory to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - CM.L2-3.4.1 Compliance
Practical, step-by-step guidance for small businesses to create and maintain...
Read more →
How to Build a Cloud VPC Subnetwork for Public Services to Satisfy FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SC.L1-B.1.XI (AWS & Azure Examples)
Step-by-step guidance for designing a segregated public subnetwork (VPC/subnet) with...
Read more →
How to Build a BYOD Policy That Satisfies NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AC.L2-3.1.18 to Control Connection of Mobile Devices
Step-by-step guidance for small businesses to build a BYOD policy...
Read more →
How to Automate Compliant Subnetwork Deployment with Terraform for Public-Facing Components (FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SC.L1-B.1.XI) — Code Examples & Best Practices
[Write a compelling 1-sentence SEO description about this compliance requirement]...
Read more →
How to Automate Account Deprovisioning for Immediate CUI Protection — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - PS.L2-3.9.2
Step-by-step guidance to automate user deprovisioning so Controlled Unclassified Information...
Read more →
How to Audit Your Physical Security: Checklist to Verify Compliance with FAR 52.204-21 / CMMC 2.0 Level 1 - Control - PE.L1-B.1.IX
Step-by-step physical security audit checklist to verify compliance with FAR...
Read more →
Compliant Media Disposal: A Practical Implementation Guide for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - MP.L1-B.1.VII Including Templates and SOPs
Step-by-step guidance for small businesses to implement compliant media disposal...
Read more →
Checklist: Configure Perimeter Devices, VPNs, and Monitoring to Satisfy FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SC.L1-B.1.X
Step-by-step checklist and practical guidance to configure firewalls, VPNs, and...
Read more →
Step-by-Step: Implementing Visitor Activity Monitoring and Escort Procedures for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - PE.L1-B.1.IX
Practical step-by-step guidance for small businesses to implement visitor monitoring...
Read more →
Step-by-Step Guide: Track, Document, and Report Incidents to Internal and External Authorities for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - IR.L2-3.6.2
Practical, step-by-step guidance for small businesses to track, document, and...
Read more →
Step-by-Step Guide to Configure NTP and Chrony on Windows and Linux for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AU.L2-3.3.7
Practical step-by-step instructions to configure reliable time synchronization (Windows NTP...
Read more →
Step-by-Step Checklist to Secure Systems Containing CUI on Employee Exit and Transfer — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - PS.L2-3.9.2
Practical, step-by-step checklist and technical playbook to secure systems that...
Read more →
Practical Implementation Checklist for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - IA.L1-B.1.V: Identify and Track System Users, Agent Processes, and Devices
Step-by-step checklist and practical guidance to identify and track users,...
Read more →
Implementing Multi-Factor Authentication for BYOD: A Compliance Playbook for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-6-3
A practical, step-by-step compliance playbook to implement phishing-resistant multi-factor authentication...
Read more →
How to Validate Third-Party Security Controls During Procurement and Contract Renewal: Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 4-1-3 Audit Checklist
Step-by-step guidance and an evidence-based audit checklist to validate third-party...
Read more →
How to Use Templates and Checklists to Execute the ECC Cybersecurity Strategy Roadmap — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-1-2
Practical guidance on using repeatable templates and checklists to implement...
Read more →
How to Use Cloud Identity Providers to Achieve FAR 52.204-21 / CMMC 2.0 Level 1 - Control - IA.L1-B.1.VI Compliance: Azure AD & Google Workspace Examples
Practical, step-by-step guidance for using Azure AD and Google Workspace...
Read more →
How to Use a Penetration Testing Checklist to Satisfy Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-11-1 Compliance
Practical guidance for building and using a penetration testing checklist...
Read more →
How to Select and Deploy Scanning Tools to Meet FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SI.L1-B.1.XV: Vendor Checklist
Practical guidance and a vendor checklist for selecting and deploying...
Read more →
How to Sanitize Hard Drives and Removable Media to Meet FAR 52.204-21 / CMMC 2.0 Level 1 - Control - MP.L1-B.1.VII: Tools, Verification, and Recordkeeping
Step‑by‑step guidance to sanitize hard drives and removable media to...
Read more →
How to Reduce Audit Records Without Losing Forensic Value — Practical Steps for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AU.L2-3.3.6
Practical, actionable steps to limit audit log volume while preserving...
Read more →
How to Recover from Ransomware Using Backup Strategies That Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-9-2: Tactical Recovery Steps
Practical tactical recovery steps and backup strategies to recover from...
Read more →
How to Prepare for an ECC 2-11-4 Audit: Evidence, Timing, and Best Practices for Penetration Testing Reviews (Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-11-4)
Learn exactly what evidence, timing, and processes auditors expect for...
Read more →
How to Prepare for an Audit: Demonstrating Compliance with FAR 52.204-21 / CMMC 2.0 Level 1 - Control - PE.L1-B.1.VIII
Practical, step-by-step guidance for small businesses to demonstrate compliance with...
Read more →
How to Mitigate OWASP Top 10 Risks in External Web Applications to Comply with ECC 2-15-2 — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-15-2
Practical, actionable guidance to mitigate the OWASP Top 10 in...
Read more →
How to Measure Effectiveness of Security Awareness for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AT.L2-3.2.1: KPIs, Tests, and Improvement Plan
Practical guidance to measure, test, and improve security awareness to...
Read more →
How to Label Electronic Files, USBs, and Printed Materials with CUI Markings per NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - MP.L2-3.8.4
Practical, step-by-step guidance for small businesses to label electronic files,...
Read more →
How to Integrate MFA into Active Directory, Azure AD, and VPNs to Comply with NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - IA.L2-3.5.3
Step-by-step guide to deploying multi-factor authentication across on‑prem Active Directory,...
Read more →
How to Implement NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - RA.L2-3.11.3: Step-by-Step Vulnerability Remediation Aligned to Risk Assessments
Practical, step-by-step guidance for small organizations to implement RA.L2-3.11.3: remediating...
Read more →
How to Implement NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - PS.L2-3.9.2: Step-by-Step Offboarding Checklist to Protect CUI During Terminations and Transfers
Practical, step-by-step offboarding checklist to help organizations meet NIST SP...
Read more →
How to Implement FAR 52.204-21 / CMMC 2.0 Level 1 - Control - IA.L1-B.1.V: Step-by-Step User and Device Identification Guide
Practical, step-by-step guidance to meet FAR 52.204-21 and CMMC 2.0...
Read more →
How to Implement FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.III: Step-by-Step Guide to Verify and Limit External Information System Connections
Step-by-step, practical guidance for small businesses to verify and limit...
Read more →
How to Implement Device and Network Controls to Meet FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.III: Step-by-Step Guide
Practical, step-by-step guidance for small businesses to implement device and...
Read more →
How to Implement Boundary Monitoring for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SC.L1-B.1.X: Step-by-Step Network & Internal Boundary Guide
Practical, step-by-step guidance for small businesses to implement boundary monitoring...
Read more →
How to Implement AWS VPC Subnets and Security Groups to Separate Public and Internal Networks — FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SC.L1-B.1.XI
Step-by-step guidance to configure AWS VPC subnets, route tables, NAT/IGW,...
Read more →How to Implement an Incident Tracking System to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - IR.L2-3.6.2
Practical, step-by-step guidance for designing and operating an incident tracking...
Read more →
How to Implement a Quarterly Audit Checklist for Physical Protection of IT Assets to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-14-4
Step-by-step guidance to build and run a quarterly physical protection...
Read more →
How to Implement a Learning Management System (LMS) to Demonstrate Compliance with NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AT.L2-3.2.2
Practical guide to implementing an LMS that meets NIST SP...
Read more →
How to Harden SSH and RDP to Satisfy NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AC.L2-3.1.15: Practical Configuration Steps
Step-by-step, practical guidance to harden SSH and RDP to meet...
Read more →
How to document compliant event log policies with templates for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-12-1 and accelerate approval
Step-by-step guidance and ready-to-use templates to document event log policies...
Read more →
How to Destroy SSDs and HDDs: Step-by-Step Methods to Satisfy FAR 52.204-21 / CMMC 2.0 Level 1 - Control - MP.L1-B.1.VII
Step‑by‑step, practical guidance to sanitize and destroy SSDs and HDDs...
Read more →
How to Create POA&M Templates and Documentation That Satisfy NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - CA.L2-3.12.2
Step-by-step guidance and ready-to-use POA&M template elements to help small...
Read more →
How to Create Audit-Ready Incident Review Reports to Satisfy Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-13-4
Step-by-step guidance to produce audit-ready incident review reports that meet...
Read more →
How to Create an Audit-Ready Policy Review Schedule for ECC – 2 : 2024 (Essential Cybersecurity Controls - Control - 1-3-4) with Templates and Evidence Trails
Step-by-step guidance to build an audit-ready policy review schedule for...
Read more →
How to Create a Step-by-Step Checklist to Implement Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-2-4 Identity and Access Reviews
Practical, step-by-step guidance for small businesses to implement ECC 2-2-4...
Read more →
How to Create a Maintenance Schedule and Checklist for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - MA.L2-3.7.1
Step-by-step guidance for building a repeatable maintenance schedule and checklist...
Read more →
How to Create a Contract Checklist and Template to Ensure IT Outsourcing Meets Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 4-1-3
Step-by-step guidance and a practical contract checklist/template to ensure IT...
Read more →
How to Create a Compliance Checklist for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SI.L1-B.1.XIV: Evidence, Policies, and Logs to Prove You Update Malware Protections
Step-by-step guidance for building an auditable checklist that proves you...
Read more →
How to Create a Checklist and Schedule for Periodic Cybersecurity Reviews under Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-8-1
Step-by-step guidance to build a practical checklist and schedule to...
Read more →
How to Configure VLANs and Firewalls to Separate Public and Internal Networks — FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SC.L1-B.1.XI: Practical Deployment Steps
Step-by-step guidance to configure VLANs and firewalls to isolate public/DMZ...
Read more →
How to Configure SIEM and Alerting for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-13-3 to Meet Incident and Threat Management Requirements
Step-by-step guidance for configuring SIEM ingestion, detection rules, and alerting...
Read more →
How to Configure Secure VoIP Encryption (SRTP/TLS) and Logging for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - SC.L2-3.13.14
Practical step‑by‑step guidance to secure VoIP (SIP/RTP) with SRTP and...
Read more →
How to Configure Least-Privilege Permissions in Windows and Linux for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.II
Practical, hands‑on guidance to implement least‑privilege access controls in Windows...
Read more →
How to Configure Bastion Hosts and Jump Servers to Route Remote Access for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AC.L2-3.1.14
Practical step-by-step guidance to implement bastion hosts and jump servers...
Read more →
How to Configure AWS VPC Subnets and Security Groups to Meet FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SC.L1-B.1.XI
Step-by-step guidance to design AWS VPC subnets and security groups...
Read more →
How to Configure AWS IAM and Groups to Limit Information System Access to Allowed Transactions and Functions (Practical Guide) — FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.II
Practical, step-by-step guidance to implement FAR 52.204-21 / CMMC 2.0...
Read more →
How to Configure Active Directory Password Policies to Comply with NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - IA.L2-3.5.7
Step-by-step guidance to configure Active Directory password and account policies...
Read more →
How to Conduct Physical Security Risk Assessments and Remediation Plans for Information and Technology Assets — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-14-3
Step-by-step guidance to assess physical security risks to information and...
Read more →
How to Conduct a Gap Assessment for Independent Cybersecurity Audits under Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-8-2: 10 Actionable Steps
Step-by-step guidance to perform a gap assessment for independent cybersecurity...
Read more →
How to Choose and Configure Antivirus, EDR, and Sandboxing Tools for Diagnostic Media Scanning — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - MA.L2-3.7.4
Practical guidance for selecting and configuring antivirus, EDR, and sandbox...
Read more →
How to Build an MFA and User Verification Plan to Meet FAR 52.204-21 / CMMC 2.0 Level 1 - Control - IA.L1-B.1.VI
Step-by-step guidance for small businesses to design and implement MFA...
Read more →
How to Build an Audit-Ready Program for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-7-1: 10 Practical Steps to Prove Compliance with National Regulations
Practical, step-by-step guidance for small businesses to build an audit-ready...
Read more →
How to Build an Audit-Ready Business Continuity Cybersecurity Requirements Document: Implementation Checklist — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 3-1-1
Step-by-step guidance to create an audit-ready Business Continuity Cybersecurity Requirements...
Read more →
How to Build an Access Control Policy for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.II: Practical Template and Implementation Steps
Step-by-step guide to build an access control policy that satisfies...
Read more →
How to Build a Vulnerability Scanning Schedule to Comply with NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - RA.L2-3.11.2: Frequency, Scope and Reporting
Step-by-step guidance to create a vulnerability scanning schedule that meets...
Read more →
How to Build a Step-by-Step Application Allowlist (Whitelisting) Strategy to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - CM.L2-3.4.8
Step-by-step guidance to design, deploy, and operate an application allowlist...
Read more →
How to Build a Practical Checklist for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.IV to Secure Public-Facing Websites and Portals
Step-by-step checklist and technical guidance to meet FAR 52.204-21 /...
Read more →
How to Build a NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AT.L2-3.2.1 Compliant Security Awareness Program for Managers, SysAdmins, and Users
Step-by-step guidance to design and operate a role-based security awareness...
Read more →
How to Build a Media Sanitization Policy that Meets FAR 52.204-21 / CMMC 2.0 Level 1 - Control - MP.L1-B.1.VII: Templates and Implementation Steps
Practical guide with templates, technical steps, and real-world examples to...
Read more →
How to Build a Contract Review Checklist for Vendor Agreements Aligned with Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 4-1-4
Step-by-step guide to creating a vendor contract review checklist that...
Read more →
How to Build a Compliance-Ready POA&M Template for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - CA.L2-3.12.2 (Includes Sample Entries)
Build a practical POA&M template to satisfy NIST SP 800-171...
Read more →
How to Build a Compliance-First Vulnerability Scanning Program for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - RA.L2-3.11.2: Scheduling, Scope, and Evidence Collection
Practical guide to designing, scheduling, scoping, and evidencing vulnerability scans...
Read more →
How to Build a Checklist to Test Incident Response and Pass Audits for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - IR.L2-3.6.3
Step-by-step guidance and a practical checklist template to test your...
Read more →
How to Automate Periodic Vulnerability Scanning and Reviews for Compliance with Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-10-4
Step-by-step practical guidance to automate periodic vulnerability scanning and review...
Read more →
How to Automate Periodic Reviews of Information & Technology Assets Using CMDB and Tooling — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-1-6
Step-by-step guidance to automate periodic reviews of IT and information...
Read more →
How to Automate Detection and Reporting for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SI.L1-B.1.XII: Tools, Scripts, and Configuration Examples
Practical, step-by-step guidance to automate detection and reporting to meet...
Read more →
How to Automate Asset Discovery and Monitoring to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-1-2
Practical, step-by-step guidance to automate asset discovery and continuous monitoring...
Read more →
FAR 52.204-21 / CMMC 2.0 Level 1 - Control - MP.L1-B.1.VII: Practical Checklist to Sanitize or Destroy FCI Before Disposal or Reuse
Practical, step-by-step checklist and technical guidance to securely sanitize or...
Read more →
Checklist: Monitoring, Controlling, and Protecting Organizational Communications to Satisfy FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SC.L1-B.1.X
Practical checklist and step-by-step guidance for monitoring, controlling, and protecting...
Read more →
Step-by-Step Checklist to Perform Maintenance on Organizational Systems — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - MA.L2-3.7.1
Practical, step-by-step checklist to meet NIST SP 800-171 Rev.2 /...
Read more →
Step-by-Step Checklist to Encrypt CUI on BYOD and Corporate Mobile Platforms for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AC.L2-3.1.19
Practical, step-by-step checklist to encrypt CUI on BYOD and corporate...
Read more →
Small Business Implementation Guide: Achieve FAR 52.204-21 / CMMC 2.0 Level 1 - Control - PE.L1-B.1.IX by Deploying Visitor Escort Programs and Access Device Controls
A practical small-business guide to meeting FAR 52.204-21 and CMMC...
Read more →
Quick Compliance Checklist: Verifying and Controlling External Connections for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.III
Practical one-page checklist and implementation guidance to verify and control...
Read more →
Implementation Checklist: Real-Time File Scanning on Windows, macOS, and Linux for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SI.L1-B.1.XV
Practical, platform-specific checklist to implement and validate real-time file scanning...
Read more →
Implementation Checklist: Policies, Technology, and Audits to Limit Physical Access — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - PE.L2-3.10.1
Practical one-page implementation checklist and actionable controls to limit physical...
Read more →
How to Verify and Document Media Destruction to Meet FAR 52.204-21 / CMMC 2.0 Level 1 - Control - MP.L1-B.1.VII Compliance: Templates & Evidence for Auditors
Practical, auditor-ready guidance and templates for verifying and documenting media...
Read more →
How to Use Templates and Checklists to Conduct Periodic CUI Risk Assessments — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - RA.L2-3.11.1
Practical guidance on building templates and checklists to meet NIST...
Read more →
How to Use Patch Management Tools to Ensure Timely Malicious Code Protection Updates for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - SI.L2-3.14.4
Step-by-step guidance for configuring patch management and anti-malware update processes...
Read more →
How to Use a Quick Compliance Checklist to Deploy Real-Time File Scans on Downloads and Executions for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SI.L1-B.1.XV
Step-by-step checklist to deploy real-time file scans on downloads and...
Read more →
How to select SIEM and monitoring tools to satisfy NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - CA.L2-3.12.3: vendor checklist
A practical vendor checklist to help small businesses select SIEM...
Read more →
How to Select and Deploy Endpoint Protection Tools to Satisfy FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SI.L1-B.1.XIII
Practical guidance to choose and deploy endpoint protection (AV/EDR) to...
Read more →
How to Sanitize or Destroy Media Containing Federal Contract Information: FAR 52.204-21 / CMMC 2.0 Level 1 - Control - MP.L1-B.1.VII — Practical Guide for Small Contractors
Practical, low-cost steps for small contractors to sanitize or destroy...
Read more →
How to Sanitize and Destroy Hard Drives to Meet FAR 52.204-21 / CMMC 2.0 Level 1 - Control - MP.L1-B.1.VII: Tools, Methods, and Verification Checklist
Practical guidance for small businesses to sanitize and destroy hard...
Read more →
How to Prioritize and Remediate Findings from Periodic Vulnerability Reviews — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-10-4
Practical guidance for small businesses to prioritize, track, and remediate...
Read more →
How to Prioritize and Patch Vulnerabilities Using Risk Assessments — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - RA.L2-3.11.3
Practical, step-by-step guidance to prioritize and remediate vulnerabilities using risk...
Read more →
How to Prepare for Compliance Audits: Step-by-Step Periodic Review Procedures for Incident & Threat Management for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-13-4
Practical, step-by-step periodic review procedures to meet ECC–2:2024 Control 2-13-4...
Read more →
How to Prepare for an Audit: Demonstrating Compliance with FAR 52.204-21 / CMMC 2.0 Level 1 - Control - MP.L1-B.1.VII (MP.L1-B.1.VII, Code 550)
Practical, small‑business focused guidance to demonstrate compliance with FAR 52.204-21...
Read more →
How to Migrate from Password-Only to Replay-Resistant Authentication Across Your Network — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - IA.L2-3.5.4 Migration Plan
Step-by-step migration plan to replace password-only access with replay-resistant authentication...
Read more →
How to Measure Effectiveness of Insider Threat Awareness Training with Metrics and Reporting — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AT.L2-3.2.3
Practical guidance for measuring and reporting insider-threat awareness training effectiveness...
Read more →
How to Integrate SSO, MFA, and Device Trust to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - IA.L2-3.5.1 Requirements
Step-by-step guidance for combining SSO, MFA, and device trust to...
Read more →
How to integrate automated security testing (SAST/DAST) into CI/CD for external web apps to satisfy Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-15-2
Practical, step-by-step guidance for integrating SAST and DAST into CI/CD...
Read more →
How to Implement Periodic and Real-Time File Scanning to Meet FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SI.L1-B.1.XV: A Step-by-Step Guide
Step-by-step guidance to deploy periodic and real-time file scanning to...
Read more →
How to Implement NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - SC.L2-3.13.3: Step-by-Step Guide to Separate User Functionality from System Management Functionality
Step-by-step practical guidance to separate user functionality from system management...
Read more →
How to Implement NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - PE.L2-3.10.4: Step-by-Step Guide to Maintain Audit Logs of Physical Access
Step-by-step guidance for small businesses to implement and maintain physical...
Read more →How to Implement NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - MP.L2-3.8.5: Step-by-Step Guide to Controlling and Tracking CUI Media in Transit
Step-by-step, practical guidance for small businesses to control and track...
Read more →
How to Implement Least-Privilege Role-Based Access for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.II: A Step-by-Step Guide
Step-by-step guidance for implementing least-privilege, role-based access controls to meet...
Read more →
How to Implement Identity Authentication for Users, Processes, and Devices — FAR 52.204-21 / CMMC 2.0 Level 1 - Control - IA.L1-B.1.VI (Step-by-Step Checklist)
Step-by-step practical guide to implement identity authentication for users, processes,...
Read more →
How to Implement Cost-Effective Audit Record Reduction and On-Demand Reporting in Cloud Environments for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AU.L2-3.3.6
Practical, cost-aware steps for reducing audit-record volume and enabling on-demand...
Read more →
How to Implement a Quarterly Security Control Assessment Process for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - CA.L2-3.12.1: Step-by-Step Checklist and Templates
A practical, step-by-step guide to implementing a repeatable quarterly security...
Read more →
How to Implement a Cybersecurity Awareness Program That Meets Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-10-3: Step-by-Step Threat Coverage Plan
Step-by-step guidance to design, document, and operate a threat-coverage-focused cybersecurity...
Read more →
How to Document Vulnerability Remediation Evidence for Audits: NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - RA.L2-3.11.3 Compliance Checklist
Practical, audit-ready guidance on collecting and organizing vulnerability remediation evidence...
Read more →
How to Deploy Multi-Factor Authentication to Meet FAR 52.204-21 / CMMC 2.0 Level 1 - Control - IA.L1-B.1.VI
Practical, step-by-step guidance for small businesses to deploy multi-factor authentication...
Read more →
How to Deploy FIDO2/WebAuthn for Replay-Resistant Authentication on Corporate Networks — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - IA.L2-3.5.4
Practical guidance for implementing FIDO2/WebAuthn to satisfy NIST SP 800-171...
Read more →
How to Deploy Data Loss Prevention (DLP) Solutions to Comply with Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-7-2: Deployment Guide and Policy Integration
Practical, step-by-step guidance to deploy and integrate DLP solutions that...
Read more →
How to Create and Execute a BYOD Review Checklist Aligned to Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-6-4
A step-by-step guide to building and executing a BYOD review...
Read more →
How to Create and Apply CUI Labels to Electronic and Physical Media: Implementation Guide for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - MP.L2-3.8.4
Practical step‑by‑step guidance for small businesses to create, apply, and...
Read more →
How to Create an Audit-Ready Third-Party Agreement Review Checklist for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 4-1-4
A step-by-step guide to building an audit-ready third-party agreement review...
Read more →
How to Create a Step-by-Step Penetration Testing Process Checklist for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-11-3
Practical, step-by-step guidance for building a penetration testing checklist to...
Read more →
How to Create a Practical Template and Checklist to Define Cybersecurity Business Continuity Requirements — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 3-1-1
Learn how to create a concise, testable template and checklist...
Read more →
How to create a practical checklist for periodic penetration testing process reviews (Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-11-4)
Step-by-step guidance to build a practical, auditable checklist for periodic...
Read more →
How to configure Windows AppLocker for deny-all, permit-by-exception whitelisting to satisfy NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - CM.L2-3.4.8
Step-by-step guidance to implement a deny-all, permit-by-exception AppLocker whitelist on...
Read more →
How to Configure Nessus for Continuous and On-Demand Scans to Satisfy NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - RA.L2-3.11.2
Step-by-step guidance to configure Nessus (and Tenable agents) for continuous...
Read more →
How to configure IAM policies to satisfy FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.II: Practical AWS and Azure examples
Step-by-step guidance and ready-to-use IAM policy patterns in AWS and...
Read more →
How to Configure Firewalls and ACLs to Deny Network Communications by Default — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - SC.L2-3.13.6 Practical Walkthrough
Step-by-step guidance for implementing deny-by-default firewall and ACL rules to...
Read more →
How to Configure Firewall Rules and Subnetworks to Isolate Public Services — FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SC.L1-B.1.XI Checklist for Compliance
Practical steps and examples to configure firewall rules and subnetworks...
Read more →
How to Configure Centralized Logging and SIEM for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-12-2 Compliance
Practical, step-by-step guidance to implement centralized logging and SIEM that...
Read more →
How to Conduct a Business Impact Analysis (BIA) for ECC 3-1-3 Compliance: Templates and Execution Steps — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 3-1-3
Step-by-step guidance, templates, and real-world examples to perform a Business...
Read more →
How to Build Audit Logs for Physical Access: Step-by-Step Implementation for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - PE.L1-B.1.IX
Practical, step-by-step guidance to design, collect, secure, and review physical...
Read more →
How to Build an ECC-Compliant Acceptable Use Policy Template and Approval Workflow — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-1-3
Step-by-step guidance to design an ECC-compliant Acceptable Use Policy template...
Read more →
How to Build an Automated Offboarding Workflow to Protect CUI — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - PS.L2-3.9.2
Step‑by‑step guidance to build an automated offboarding workflow that promptly...
Read more →
How to Build an Auditable Monitoring Management Program (Templates & Checklist) for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-12-1
Practical, step-by-step guidance and ready-to-use evidence checklist to build an...
Read more →
How to Build a Visitor Escort Program and Monitor Visitor Activity to Meet FAR 52.204-21 / CMMC 2.0 Level 1 - Control - PE.L1-B.1.IX
Step-by-step guidance for small businesses to design and operate a...
Read more →
How to build a step-by-step update process for antivirus and EDR to satisfy FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SI.L1-B.1.XIV
Practical, step-by-step guidance to design and operate an antivirus and...
Read more →
How to build a step-by-step external web application requirements template for compliance — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-15-1
A practical, step-by-step template and implementation guide to ensure externally...
Read more →
How to Build a Secure DMZ in AWS and Azure to Isolate Public Components for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SC.L1-B.1.XI Compliance
Practical, step-by-step guidance to design and implement a secure DMZ...
Read more →
How to Build a Repeatable IAM Policy and Controls Framework for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-2-3: Templates and Checklist
A practical, step-by-step guide to creating repeatable IAM policy templates...
Read more →
How to Build a Practical Inventory to Satisfy FAR 52.204-21 / CMMC 2.0 Level 1 - Control - IA.L1-B.1.V: Users, Agent Processes, and Devices Checklist
Practical, step-by-step guidance for small businesses to build and maintain...
Read more →
How to Build a Patch and Vulnerability Management Program to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-10-2
Step-by-step guidance for small businesses to design, operate, and evidence...
Read more →
How to Build a Media Sanitization Workflow for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - MP.L1-B.1.VII (Checklist & Tools)
Step-by-step guide to build a media sanitization workflow that meets...
Read more →
How to Build a High-Impact Cybersecurity Steering Committee: Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-2-3 Member Selection, Meeting Cadence & KPIs
Practical guidance to form a cybersecurity steering committee that meets...
Read more →
How to Build a Compliant Business Continuity Cybersecurity Policy: Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 3-1-1 Template and Implementation Plan
Step-by-step guide to creating and implementing a compliant Business Continuity...
Read more →
How to Build a Compliance-Ready Logging Architecture for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AU.L2-3.3.2: Tools, Configs, and Best Practices
Step-by-step guidance for designing and implementing a logging architecture that...
Read more →
How to Build a Compliance-Ready Business Continuity Plan That Meets Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 3-1-2
Step-by-step guidance to create a business continuity plan that satisfies...
Read more →
How to Build a Compliance Checklist for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.IV to Control Information Posted on Public Websites
Step-by-step guidance and a practical checklist to ensure your public...
Read more →
How to Build a Compliance Checklist for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-3-2: Policies, Technical Controls, and Physical Protections
Step-by-step guidance to build a practical compliance checklist for ECC...
Read more →
How to Automate Vulnerability Prioritization Using CVSS and Threat Intelligence for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-10-3
Practical step-by-step guidance to automate vulnerability prioritization by combining CVSS,...
Read more →
How to Automate Offboarding with SIEM and EDR Integration to Protect CUI — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - PS.L2-3.9.2
Practical guide to automating user offboarding by integrating HR systems,...
Read more →
How to Apply Authentication, Authorization, and Session Security to External Web Apps for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-15-2
Practical, step-by-step guidance to secure authentication, authorization, and session handling...
Read more →
A Practical Checklist to Meet FAR 52.204-21 / CMMC 2.0 Level 1 - Control - PE.L1-B.1.IX: Escort Visitors, Monitor Activity, and Log Access
Concrete, low-cost steps and technical controls small businesses can implement...
Read more →
10-Step Implementation Checklist for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SI.L1-B.1.XII to Identify and Fix Information System Flaws Quickly
Practical 10-step checklist to help small businesses meet FAR 52.204-21...
Read more →
Step-by-Step Template: Performing a Periodic Review of Access Controls, CCTV, and Environmental Protections — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-14-4
Practical, step-by-step guidance to perform compliant periodic reviews of access...
Read more →
Step-by-Step Guide to Monitor Security Controls Ongoing: NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - CA.L2-3.12.3
Practical, step‑by‑step guidance for implementing continuous monitoring to satisfy NIST...
Read more →
Step-by-step guide to creating a compliant asset classification scheme for information and technology assets — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-1-5
Practical, step-by-step guidance to design and implement an ECC 2-1-5...
Read more →
Step-by-Step: Deploying a Trusted Time Source in AWS and Azure for Audit Records — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AU.L2-3.3.7
How to deploy and enforce a trusted, auditable time source...
Read more →
Practical Checklist: Configure and Protect IT Assets for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-1-2
Step-by-step, practical checklist to configure and protect IT assets to...
Read more →
How to Use MFA, Least Privilege, and RBAC to Limit System Access: FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.I Implementation Guide
Step-by-step guide to enforce MFA, least privilege, and RBAC to...
Read more →
How to Use Free and Low-Cost Tools to Identify, Report, and Correct System Flaws for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SI.L1-B.1.XII
Practical, low-cost techniques and toolchain recommendations to help small contractors...
Read more →
How to Use Automated Scanning and Ticketing to Meet FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SI.L1-B.1.XII Requirements
Learn step-by-step how to combine automated vulnerability scanning with ticketing...
Read more →
How to Secure Remote Maintenance Access to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - MA.L2-3.7.2
Practical, step-by-step guidance to secure, monitor, and document remote maintenance...
Read more →
How to Secure Cloud and Hybrid Networks with Practical Controls to Comply with Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-5-2
Concrete, step-by-step controls and examples to secure cloud and hybrid...
Read more →
How to Sanitize Laptops and Mobile Devices for Off‑Site Repair: Practical Procedures — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - MA.L2-3.7.3
Practical, step‑by‑step procedures for sanitizing laptops and mobile devices before...
Read more →
How to Prioritize and Remediate Vulnerabilities According to Risk Assessments — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - RA.L2-3.11.3
Practical guidance for small businesses to prioritize and remediate vulnerabilities...
Read more →
How to Prioritize and Implement Cost-Effective Malware Protections for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SI.L1-B.1.XIII: A Practical Checklist
Practical, cost-conscious checklist and implementation guidance to meet the malware-protection...
Read more →
How to Prepare for a CMMC 2.0 Audit: Remediating Vulnerabilities Based on Risk Assessments — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - RA.L2-3.11.3
Practical guidance for small businesses on remediating vulnerabilities based on...
Read more →
How to Prepare Evidence and Audit Trails to Prove Periodic CUI Risk Assessments for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - RA.L2-3.11.1
Practical guidance on collecting, organizing, and preserving evidence and audit...
Read more →
How to Prepare a Compliance-Friendly Periodic Review Template and Timeline for ISO/HIPAA/CMMC Alignment — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-3-4
Build a practical periodic review template and timeline that maps...
Read more →
How to Map Technical IAM Controls to Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-2-1 with Practical Examples
Practical guidance for mapping technical IAM controls to ECC 2-2-1...
Read more →
How to Integrate Automated Security Testing in CI/CD for External Web Applications for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-15-3
Practical, step-by-step guidance to embed automated SAST/DAST/SCA into CI/CD pipelines...
Read more →
How to Integrate Antivirus and EDR Updates into Patch Management for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SI.L1-B.1.XIV
Step-by-step guidance for integrating antivirus and EDR signature/engine updates into...
Read more →
How to Implement User, Process, and Device Identification: Step-by-Step for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - IA.L1-B.1.V
Practical, step-by-step guidance for small businesses to implement and evidence...
Read more →
How to Implement Periodic Risk Assessments for CUI: NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - RA.L2-3.11.1 Step-by-Step Guide
Step-by-step, practical guidance to implement RA.L2-3.11.1 periodic risk assessments for...
Read more →
How to Implement Obscure Feedback of Authentication Information in Azure and AWS: NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - IA.L2-3.5.11 Cloud Configuration Guide
Practical, step-by-step guidance for implementing obscure feedback of authentication information...
Read more →
How to Implement NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - PS.L2-3.9.1: Step-by-Step Screening Process for CUI Access
Practical, step-by-step guidance for building a defensible personnel screening process...
Read more →
How to Implement NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - IR.L2-3.6.1: Step-by-Step Guide to Building an Operational Incident-Handling Capability
Practical, step-by-step guidance to build an operational incident-handling capability that...
Read more →
How to Implement Network Segmentation and Boundary Controls for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SC.L1-B.1.X in Small Organizations
Practical, step-by-step guidance for small organizations to implement network segmentation...
Read more →
How to implement media sanitization and destruction for Federal Contract Information — FAR 52.204-21 / CMMC 2.0 Level 1 - Control - MP.L1-B.1.VII (Step-by-Step Guide)
Step-by-step guide to meet FAR 52.204-21 and CMMC 2.0 Level...
Read more →
How to Implement Low-Cost Physical Security Measures for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - PE.L1-B.1.VIII: A Small Business Guide
Practical, low-cost physical security strategies for small businesses to meet...
Read more →
How to Implement Lightweight Identity Controls for Small Contractors to Comply with FAR 52.204-21 / CMMC 2.0 Level 1 - Control - IA.L1-B.1.V
Practical, low-cost steps for small contractors to implement lightweight identity...
Read more →
How to Implement Least Privilege to Limit Access: FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.II Step-by-Step
A practical, step-by-step guide for small businesses to implement least-privilege...
Read more →
How to Implement Least Privilege Policies for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.II: A Clear Implementation Checklist
Practical checklist to implement least privilege for FAR 52.204-21 /...
Read more →
How to Implement FAR 52.204-21 / CMMC 2.0 Level 1 - Control - MP.L1-B.1.VII: A Practical Checklist to Sanitize or Destroy Media Before Reuse or Disposal
Step-by-step guidance and a practical checklist to sanitize or destroy...
Read more →
How to Implement Cryptography Requirements under Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-8-3: A Step-by-Step NCA-Aligned Guide
A practical, NCA-aligned step-by-step guide to implement Control 2-8-3 of...
Read more →
How to Implement Approved Network Security Requirements: A Practical Checklist for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-5-1
Step-by-step guidance and an actionable checklist to implement Approved Network...
Read more →
How to Implement an AT.L2-3.2.1 Compliance Plan: Practical Steps to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 Awareness Requirements
Step-by-step guidance to build and document an AT.L2-3.2.1 security awareness...
Read more →
How to Implement a Technical Vulnerabilities Management Program: Step-by-Step to Comply with Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-10-2
Practical, step-by-step guidance to build a Technical Vulnerability Management program...
Read more →
How to Implement a Step-by-Step Screening Process for CUI Access: NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - PS.L2-3.9.1
Practical, step-by-step guidance for implementing personnel screening to control access...
Read more →
How to Harden Windows, Linux, and Database Servers with Technical Standards That Meet Policy Requirements — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-3-3
Practical, audit-ready steps to create and apply technical hardening standards...
Read more →
How to Deploy a Cost-Effective Training Program Aligned to NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AT.L2-3.2.2, Including Templates and Timelines
Step-by-step guidance for small businesses to build a cost-effective, auditable...
Read more →
How to Create Audit Logs for Physical Access to Satisfy FAR 52.204-21 / CMMC 2.0 Level 1 - Control - PE.L1-B.1.IX: Templates and Examples
Step-by-step guidance, practical templates, and low-cost examples for capturing and...
Read more →
How to Create an Employee Onboarding Checklist That Meets Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-9-4
A practical guide to building an employee onboarding checklist that...
Read more →
How to Create an Audit-Ready Physical Access Log and Reporting Process for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - PE.L1-B.1.IX (Checklist + Template)
Step-by-step guidance to build an audit-ready physical access logging and...
Read more →
How to Create an Audit-Ready Data Handling Framework for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-7-1 with Templates and Checklists
Practical step-by-step guidance to build an audit-ready data handling framework...
Read more →
How to Create an Audit-Ready Checklist for Reviewing Data and Information Requirements (Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-7-4)
Step-by-step guidance to build an audit-ready checklist for ECC 2-7-4...
Read more →
How to Create an Actionable BYOD Review Checklist and Remediation Plan — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-6-4
Step-by-step guide to build a practical BYOD review checklist and...
Read more →
How to create a step-by-step network access checklist to verify and control/limit external system use — FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.III (Code 546)
A practical, step-by-step guide to building a network access checklist...
Read more →
How to Create a Penetration Testing Requirements Checklist Aligned to Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-11-1
Step-by-step guidance to build a penetration testing requirements checklist that...
Read more →
How to Create a Compliance Checklist and Timeline to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-2-2: Steps to Recruit, Document, and Retain Saudi Cybersecurity Experts
A practical one-stop guide to recruiting, documenting, and retaining Saudi...
Read more →
How to Configure Windows, Linux and Cloud Audit Logging Controls to Satisfy NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AU.L2-3.3.9
Practical step-by-step guidance for configuring Windows, Linux, and cloud audit...
Read more →
How to Configure TLS, SPF, DKIM and DMARC for Email Compliance Under Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-4-2
Practical step-by-step guidance for configuring TLS, SPF, DKIM and DMARC...
Read more →
How to Configure TLS, Encryption-at-Rest, and Algorithms for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-8-2 Compliance
Practical step-by-step guidance for configuring TLS, encryption-at-rest, and approved cryptographic...
Read more →
How to Configure Firewalls, IDS/IPS and DLP for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - SC.L2-3.13.1 Compliance
Step-by-step guidance to configure perimeter and internal firewalls, IDS/IPS sensors,...
Read more →
How to Configure Encryption in Transit and at Rest for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-8-2 Compliance
Practical, step-by-step guidance to implement encryption in transit and at...
Read more →
How to Configure Cloud VPC Subnetworks for Public-Facing Services to Satisfy FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SC.L1-B.1.XI (AWS/Azure/GCP)
Step-by-step guidance to architect and configure public-facing cloud subnetworks so...
Read more →
How to Configure Cloud IAM Policies for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.II: AWS, Azure, and GCP Implementation Guide
Step-by-step guidance to configure cloud IAM controls that meet FAR...
Read more →
How to Configure a SIEM for Event Logging and Monitoring Management under Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-12-2
Practical, step-by-step guidance to configure a SIEM to meet ECC...
Read more →
How to Collect, Protect, and Retain System Audit Records for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AU.L2-3.3.1
Practical, step-by-step guidance for small businesses to collect, protect, and...
Read more →
How to Choose and Deploy Scanning Tools for Periodic and On-Access Scans: FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SI.L1-B.1.XV Tool Selection Guide
Practical guidance for selecting and implementing on-access and periodic scanning...
Read more →
How to Build an Ongoing Security Control Monitoring Program for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - CA.L2-3.12.3 (Tools, Frequency, KPIs)
Step-by-step guidance for small businesses to implement a continuous security...
Read more →
How to Build an Automated Access Revocation Workflow for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - PS.L2-3.9.2 to Secure Systems Containing CUI
Practical, step-by-step guidance to design and implement an automated access...
Read more →
How to Build an Audit-Ready Plan to Satisfy FAR 52.204-21 / CMMC 2.0 Level 1 - Control - PE.L1-B.1.VIII: Physical Access Implementation Checklist
Step-by-step, audit-ready plan to meet FAR 52.204-21 and CMMC 2.0...
Read more →
How to Build an Audit-Ready Checklist to Verify and Control/Limit Connections to and Use of External Information Systems — FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.III
Step-by-step guidance for small businesses to create an audit-ready checklist...
Read more →
How to Build an Audit-Ready Backup Policy for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-9-1: Practical Templates and Approval Workflows
Step-by-step guidance and ready-to-adopt templates to build an audit-ready backup...
Read more →
How to Build a Visitor Management and Badge System for Compliance — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - PE.L2-3.10.1
Practical guidance for designing and operating a visitor management and...
Read more →
How to Build a Media Disposal Procedure that Meets FAR 52.204-21 / CMMC 2.0 Level 1 - Control - MP.L1-B.1.VII: Checklist and Templates
Step-by-step guidance, checklist, and templates to build a media disposal...
Read more →
How to Build a Continuous Monitoring Program for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - CA.L2-3.12.3: Step-by-Step Implementation
Step-by-step guide to design and run a continuous monitoring program...
Read more →
How to Build a Compliance-Ready Badge, Visitor & Contractor Access System for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - PE.L2-3.10.1
Step-by-step guidance to implement badge, visitor, and contractor access controls...
Read more →
How to Build a Compliance Checklist for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - PE.L2-3.10.5 to Control and Manage Physical Access Devices
Step-by-step guidance and a practical checklist to implement NIST SP...
Read more →
How to Build a Checklist to Secure Controlled Unclassified Information at Home Offices and Satellite Locations — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - PE.L2-3.10.6
Step-by-step checklist and practical guidance to secure Controlled Unclassified Information...
Read more →
How to Build a BYOD Policy That Meets Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-6-2 Requirements: Templates and Implementation Steps
[Write a compelling 1-sentence SEO description about this compliance requirement]...
Read more →
Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-3-3 Compliance Checklist: 10 Practical Implementation Tasks for Immediate Risk Reduction
Practical, prioritized tasks to implement ECC Control 2-3-3 in 2024...
Read more →
7-Step Checklist to Meet FAR 52.204-21 / CMMC 2.0 Level 1 - Control - PE.L1-B.1.IX: Audit Logs and Physical Access Device Management
Practical 7-step checklist to configure, collect, protect, review, and retain...
Read more →
10 Practical Steps to Comply with FAR 52.204-21 / CMMC 2.0 Level 1 - Control - IA.L1-B.1.V: Identify Information System Users, Processes Acting for Users, and Devices
Practical, actionable steps for small businesses to identify and track...
Read more →
Step-by-Step Implementation Checklist to Enforce CUI Safeguards for Employees at Alternate Work Sites — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - PE.L2-3.10.6
Practical, step-by-step checklist to implement PE.L2-3.10.6 safeguards so small businesses...
Read more →
Step-by-Step Guide to Configure Firewalls, Proxies, and Filters for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SC.L1-B.1.X
Practical, step-by-step guidance to configure firewalls, proxies, and content filters...
Read more →
Step-by-Step Checklist to Protect Organizational Communications at External and Internal Boundaries — FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SC.L1-B.1.X
Practical, step-by-step checklist to secure communications at internal and external...
Read more →
Implementing Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-15-3: 10 Actionable Steps to Secure External Web Applications
Practical, actionable guidance to meet Compliance Framework Control 2-15-3 by...
Read more →
Implement a Risk-Based Vulnerability Management Process to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-10-1: Practical Roadmap
A step-by-step, risk-based vulnerability management roadmap to help organizations meet...
Read more →
How to Validate and Test Backup/Recovery Requirements Under ECC – 2 : 2024 Control - 2-9-1: Practical Checklist
Step-by-step, technical and audit-ready guidance to validate and test backup...
Read more →
How to Use Automation and DevOps Controls to Enforce ECC Change Management: Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-6-1 Implementation Strategy
Practical, step-by-step guidance to implement ECC Change Management Control 1-6-1...
Read more →
How to Select and Deploy File-Scanning Tools to Satisfy FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SI.L1-B.1.XV: Vendor Checklist
Practical vendor checklist and deployment guidance to select and configure...
Read more →
How to Secure Executive Buy-In and Budget for a Standalone Cybersecurity Division (Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-2-1): Persuasive Business Case Template
Step-by-step business case template and practical guidance to secure executive...
Read more →
How to Sanitize Hard Drives and SSDs According to FAR 52.204-21 / CMMC 2.0 Level 1 - Control - MP.L1-B.1.VII: Tools and Techniques
Step-by-step guidance for small businesses to sanitize HDDs and SSDs...
Read more →
How to Sanitize and Destroy Media to Meet FAR 52.204-21 / CMMC 2.0 Level 1 - Control - MP.L1-B.1.VII: Overwrite, Degauss, and Physical Destruction Explained
Practical guidance for small businesses to sanitize and destroy electronic...
Read more →
How to Sanitize and Destroy Media Containing Federal Contract Information Before Disposal — FAR 52.204-21 / CMMC 2.0 Level 1 - Control - MP.L1-B.1.VII (Step-by-Step Implementation)
Practical, step-by-step guidance to sanitize and destroy media containing Federal...
Read more →
How to Run Realistic Tabletop Exercises to Test the Organizational Incident Response Capability — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - IR.L2-3.6.3
Step-by-step guidance for planning and running realistic tabletop exercises to...
Read more →How to Prepare for a CMMC Assessment by Implementing Change Tracking, Review, Approval, and Logging Controls: NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - CM.L2-3.4.3
[Write a compelling 1-sentence SEO description about this compliance requirement]...
Read more →
How to prepare a compliance evidence package for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.I: Templates, Samples, and Implementation Proofs
Step‑by‑step guidance and ready‑to‑use templates for assembling an evidence package...
Read more →
How to Pass Regulatory Audits by Implementing Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-1-5 for Classification, Labeling and Handling (Compliance Checklist)
A practical, step-by-step checklist to implement ECC–2:2024 Control 2-1-5 for...
Read more →
How to Measure Effectiveness of Awareness Programs: KPIs, Metrics and Reporting for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-10-1
Practical guidance for measuring and reporting the effectiveness of security...
Read more →
How to Map, Verify, and Restrict Third-Party Connections to Your Environment: Tool Recommendations and Steps — FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.III
Practical steps and tool recommendations for mapping, verifying, and restricting...
Read more →
How to Implement Real-Time Endpoint Detection and Response (EDR) for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SI.L1-B.1.XIII
Practical, step-by-step guidance for small businesses to deploy real-time EDR...
Read more →
How to Implement Periodic and Real-Time File Scanning to Meet FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SI.L1-B.1.XV: Step-by-Step Deployment Guide
Step-by-step, practical guidance for deploying periodic and real-time file scanning...
Read more →
How to Implement NIST SP 800-88 Media Sanitization for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - MP.L1-B.1.VII Compliance
Practical, step-by-step guidance for small businesses to meet FAR 52.204-21...
Read more →
How to implement NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - RA.L2-3.11.2: Step-by-step vulnerability scanning with Nessus across servers, desktops, laptops, VMs, containers, firewalls, switches, and printers
Step-by-step guidance to meet RA.L2-3.11.2 by running repeatable, credentialed and...
Read more →
How to Implement Media Sanitization Procedures for CUI: Step-by-Step Guide to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - MP.L2-3.8.3
Step-by-step, practical guidance for small businesses to sanitize or destroy...
Read more →
How to Implement Lightweight, Cost-Effective Periodic Scans for Small Contractors to Comply with FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SI.L1-B.1.XV
Practical, low-cost steps for small contractors to run periodic vulnerability...
Read more →
How to Implement Cloud-Native Alerting (AWS/Azure/GCP) for Audit Log Failures — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AU.L2-3.3.4
Practical, cloud-native steps to detect and alert on audit log...
Read more →
How to Implement CCTV, Monitoring, and Evidence Retention to Comply with Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-14-3
Practical, step-by-step guidance for small businesses to deploy CCTV, continuous...
Read more →
How to Implement Automated Offsite and Cloud Backups for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-9-2: Practical Steps
Step-by-step guidance for implementing automated offsite and cloud backups to...
Read more →
How to Implement an Employee Screening Program for CUI: Step-by-Step Guide to NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - PS.L2-3.9.1
Step-by-step guidance for small businesses to implement an employee screening...
Read more →
How to Implement a Cryptography Policy Template to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-8-1 Compliance
A practical guide and ready-to-adopt cryptography policy template to meet...
Read more →
How to Implement a Compliant Media Disposal Procedure for FCI: Checklist and Tools — FAR 52.204-21 / CMMC 2.0 Level 1 - Control - MP.L1-B.1.VII
Practical, step‑by‑step guidance and a ready checklist for implementing a...
Read more →
How to implement a complete IT and information asset inventory to meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-1-2 (Step-by-step)
Step-by-step guidance to build a comprehensive IT and information asset...
Read more →
How to Harden Windows and Linux Servers by Removing Unnecessary Features — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - CM.L2-3.4.6 Implementation Guide
Step‑by‑step guidance for meeting CM.L2-3.4.6 by removing unnecessary services, ports,...
Read more →
How to Harden iOS and Android Devices with OS Settings, App Controls, and MDM to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-6-3
Step-by-step guidance for hardening iOS and Android devices with OS...
Read more →
How to Document Evidence and Demonstrate Compliance with FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.IV: Templates and Implementation Tips
Practical guidance and ready-to-use templates to document evidence and prove...
Read more →
How to Deploy SIEM and Log Management to Identify Unauthorized Use of Organizational Systems — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - SI.L2-3.14.7
Practical, step-by-step guidance for small businesses to deploy SIEM and...
Read more →
How to Deploy Data Loss Prevention (DLP) for Shared Drives to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - SC.L2-3.13.4
Step-by-step guide to deploying DLP on shared drives to satisfy...
Read more →
How to Define Committee Members, Roles and Responsibilities for Compliance with Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-2-3 — Template & Examples
Practical guidance and ready-to-use templates to define committee members, roles...
Read more →
How to Create OS, Database, and Firewall Technical Standards Templates for Compliance with Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-3-3
Step-by-step guidance to build OS, database, and firewall technical standards...
Read more →
How to create an audit-ready risk management playbook for the cybersecurity function — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-5-2 (Templates & Checklist)
Step-by-step guidance to build an audit-ready cybersecurity risk management playbook...
Read more →
How to Create an Audit-Ready Network Security Review Checklist for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-5-4
Step-by-step guidance to build an audit-ready network security review checklist...
Read more →
How to Create an Audit-Ready Cybersecurity Awareness Program: Step-by-Step for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-10-3
Step-by-step guidance to build an audit-ready cybersecurity awareness program that...
Read more →
How to Create an Audit-Ready Access-Control Policy for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AC.L2-3.1.1 (Template & Checklist)
Create an audit-ready access control policy that satisfies NIST SP...
Read more →
How to create a practical risk management playbook and templates for the cybersecurity function — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-5-2
Step‑by‑step guidance and ready‑to‑use templates to build a practical cybersecurity...
Read more →
How to Create a Practical Assessment Schedule and Checklist for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - CA.L2-3.12.1
Step-by-step guidance to build a practical assessment schedule and checklist...
Read more →
How to create a compliant requirements template for external web apps (with examples) — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-15-1
Step-by-step guidance and templates to produce compliant, auditable requirements for...
Read more →
How to Configure Endpoint AV/EDR for Real-Time Scans on Downloaded, Opened, or Executed Files: Practical Steps for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SI.L1-B.1.XV
Step-by-step guidance to configure endpoint AV/EDR to perform real-time scans...
Read more →
How to Configure Cloud Storage and File Transfer Scans to Comply with FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SI.L1-B.1.XV
Practical step-by-step guidance for scanning cloud storage and file transfers...
Read more →
How to Configure Azure AD and Okta to Enforce Replay-Resistant Network Authentication — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - IA.L2-3.5.4 Implementation Tips
Step-by-step guidance to configure Azure AD and Okta for replay-resistant...
Read more →
How to Configure AWS IAM Least-Privilege Policies to Satisfy NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AC.L2-3.1.5
Step-by-step guidance and practical AWS IAM policy examples to implement...
Read more →
How to Configure Antivirus, Web Filtering, and EDR to Satisfy FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SI.L1-B.1.XIII (Code 556)
Step-by-step guidance to configure antivirus, EDR, and web filtering to...
Read more →
How to Configure Active Directory GPOs to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - IA.L2-3.5.7: Enforce Password Complexity and Mandatory Character Changes
Step-by-step guidance for configuring Active Directory Group Policy and Fine-Grained...
Read more →
How to Choose Tools and Vendors for Secure Media Sanitization (HDD, SSD, Mobile) — FAR 52.204-21 / CMMC 2.0 Level 1 - Control - MP.L1-B.1.VII Buyer’s Guide
A practical buyer’s guide for selecting tools and vendors to...
Read more →
How to Build Secure Login Flows That Obscure Authentication Feedback: Practical Implementation Checklist for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - IA.L2-3.5.11
Practical checklist to implement NIST SP 800-171 Rev.2 / CMMC...
Read more →
How to Build Role-Based Access Controls (RBAC) to Restrict Functions and Transactions — FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.II
Practical guide to building role-based access control (RBAC) to meet...
Read more →
How to Build DevSecOps Pipelines that Satisfy NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - SC.L2-3.13.2 Requirements
Practical step-by-step guidance for building DevSecOps pipelines that protect CUI...
Read more →
How to build checklists, templates, and playbooks to streamline recurring cybersecurity strategy reviews - Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-1-3
Practical guidance for building checklists, templates, and playbooks to meet...
Read more →
How to Build an MP.L2-3.8.1 Compliant Media Protection Program for CUI — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - MP.L2-3.8.1 Implementation Checklist
Step-by-step guidance to implement MP.L2-3.8.1 — limiting access to Controlled...
Read more →
How to Build an Incident Response Playbook That Meets Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-13-2: A Practical Implementation Checklist
Step-by-step guidance and a practical checklist to build an incident...
Read more →
How to Build an Egress and Ingress Traffic Monitoring Plan for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - SI.L2-3.14.6: An 8-Step Implementation Guide
A practical 8-step guide to designing and implementing egress and...
Read more →
How to Build an Automated Update Pipeline for Antivirus and EDR to Meet FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SI.L1-B.1.XIV
Step-by-step guidance to design and operate an automated update pipeline...
Read more →
How to Build an Automated Deprovisioning Workflow for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-9-5 to Remove Access on Termination
Step-by-step guidance to design and implement an automated deprovisioning workflow...
Read more →
How to Build an Audit-Ready Business Continuity Program Aligned to Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 3-1-2: Templates and Checklist
Practical, audit-focused templates and checklists to build a Business Continuity...
Read more →
How to Build an Actionable Network Traffic Monitoring Plan to Satisfy NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - SI.L2-3.14.6
Step-by-step guide to design and implement a network traffic monitoring...
Read more →
How to Build a Step-by-Step Policy Template to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-3-1
A practical, step-by-step policy template and implementation guide to help...
Read more →
How to Build a Practical MFA and Identity Verification Plan to Meet FAR 52.204-21 / CMMC 2.0 Level 1 - Control - IA.L1-B.1.VI
Step-by-step guidance for small businesses to implement MFA and identity...
Read more →
How to Build a Low-Cost Malicious Code Protection Strategy for Small Contractors (FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SI.L1-B.1.XIII)
Practical, low-cost steps small government contractors can take to satisfy...
Read more →
How to build a compliance checklist for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SC.L1-B.1.X to monitor, control, and protect boundary communications
Practical step-by-step checklist to help small businesses monitor, control, and...
Read more →
How to Build a 10-Step Implementation Checklist for Updating Malicious Code Protection (FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SI.L1-B.1.XIV)
[A concise, actionable 10-step checklist to ensure malicious code protection...
Read more →
How to Automate Periodic Control Testing and Evidence Collection for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - CA.L2-3.12.1
Step-by-step guidance to automate periodic security control testing and secure...
Read more →
How to Automate Audit Logging Failure Alerts with AWS CloudWatch and CloudTrail: NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AU.L2-3.3.4
Automate detection and alerting for audit-logging failures in AWS using...
Read more →
A Practical Checklist to Establish an Operational Incident-Handling Capability for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - IR.L2-3.6.1
Step-by-step checklist and real-world guidance to build an operational incident-handling...
Read more →
Step-by-Step Implementation Guide to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - IR.L2-3.6.1: Preparation, Detection, Analysis, Containment, Recovery, User Response
[Write a compelling 1-sentence SEO description about this compliance requirement]...
Read more →
Step-by-Step Guide to Segmenting Public-Facing Systems from Internal Networks for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SC.L1-B.1.XI
Practical, step-by-step instructions for segregating public-facing systems from internal networks...
Read more →
Step-by-Step Guide to Meeting FAR 52.204-21 / CMMC 2.0 Level 1 - Control - PE.L1-B.1.IX: Control and Manage Physical Access Devices
Practical, step-by-step guidance for small contractors to control and manage...
Read more →
Step-by-Step: Configure Endpoint and Server Scans (Periodic + Real-Time Downloads) for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SI.L1-B.1.XV
Practical step-by-step guidance to configure periodic scans and real-time signature/definition...
Read more →
Practical Implementation Checklist for IR.L2-3.6.1: Preparation, Detection, Analysis, Containment, Recovery, and User Response — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - IR.L2-3.6.1
A practical, step-by-step checklist to implement IR.L2-3.6.1 (incident handling) under...
Read more →
How to Use SIEM and Alerts to Meet AU.L2-3.3.3: NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AU.L2-3.3.3
Practical guidance on using SIEM, log collection, and alerting to...
Read more →
How to Use IAM Tools to Satisfy FAR 52.204-21 / CMMC 2.0 Level 1 - Control - IA.L1-B.1.V: Practical Implementation for Small Defense Contractors
Practical, low-cost identity and access management steps small defense contractors...
Read more →
How to Use IAM Tools (Azure AD, Okta, Google) to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AC.L2-3.1.6: Implementation Best Practices
Practical guidance for using Azure AD, Okta, and Google IAM...
Read more →
How to Use CCTV, Alarms, and Monitoring to Satisfy Physical Protection Requirements: Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-14-3 Practical Steps
Practical guide to implementing CCTV, alarms, and monitoring controls to...
Read more →
How to Scope, Plan, and Execute Penetration Tests to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-11-2
Practical guidance for scoping, planning, executing, reporting, and validating penetration...
Read more →
How to Sanitize Hard Drives and Removable Media Before Reuse: Tools, Methods, and Records — FAR 52.204-21 / CMMC 2.0 Level 1 - Control - MP.L1-B.1.VII
Practical, step-by-step guidance for small businesses to sanitize hard drives...
Read more →
How to Run Effective Tabletop Exercises to Satisfy NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - IR.L2-3.6.3
Step-by-step guidance to design, run, and document tabletop exercises that...
Read more →
How to Prepare Evidence and Audit Trails for a Successful NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - PE.L2-3.10.2 Assessment: Templates and Best Practices
Practical, step-by-step guidance and ready-to-use templates to collect, protect, and...
Read more →
How to Perform a Physical Security Risk Assessment and Remediation Plan for ECC Compliance: Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-14-2
Step-by-step guidance to perform a physical security risk assessment and...
Read more →
How to Pass a CMMC 2.0 Level 2 Assessment: Evidence Requirements for Pre-Authorization Screening of CUI Users — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - PS.L2-3.9.1
Practical guidance and exact evidence examples to demonstrate compliance with...
Read more →
How to Integrate Vulnerability Management into DevSecOps Pipelines for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-10-3
Practical guide to integrating automated vulnerability management into DevSecOps pipelines...
Read more →
How to Integrate Visitor Management Systems to Meet FAR 52.204-21 / CMMC 2.0 Level 1 - Control - PE.L1-B.1.IX: Configuration, Logging, and Device Controls
A practical, step-by-step guide to integrating visitor management systems with...
Read more →
How to Integrate Visitor Management, Badging, and Audit Logging for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - PE.L1-B.1.IX (Code 552)
Practical steps for small businesses to integrate visitor management, physical...
Read more →
How to Implement User, Process, and Device Identification for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - IA.L1-B.1.V: Step-by-Step Deployment for Small Contractors
Practical, step-by-step guidance for small contractors to meet FAR 52.204-21...
Read more →
How to implement step-by-step identification of information system users, agents, and devices for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - IA.L1-B.1.V
Step-by-step guidance to identify and track users, agents, and devices...
Read more →
How to Implement Periodic Risk Assessments for CUI: A Step-by-Step Guide to NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - RA.L2-3.11.1
Step-by-step guidance to implement periodic risk assessments for Controlled Unclassified...
Read more →
How to Implement NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - PE.L2-3.10.4: Maintain Audit Logs of Physical Access (Step-by-Step Implementation)
Step-by-step guidance to implement PE.L2-3.10.4 for maintaining secure, auditable physical...
Read more →
How to Implement NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - PE.L2-3.10.1: A Step-by-Step Plan to Limit Physical Access to Authorized Individuals
Step-by-step, practical guidance for small businesses to meet NIST SP...
Read more →
How to Implement MFA Step-by-Step to Authenticate Users, Processes, and Devices — FAR 52.204-21 / CMMC 2.0 Level 1 - Control - IA.L1-B.1.VI
[Write a compelling 1-sentence SEO description about this compliance requirement]...
Read more →
How to Implement Logical Subnet Separation in AWS to Satisfy FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SC.L1-B.1.XI
Step-by-step guidance to design and operate logical subnet separation in...
Read more →
How to Implement Lightweight, Cost-Effective Scanning for Small Contractors to Comply with FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SI.L1-B.1.XV: Quick Start Guide
A practical, low-cost quick-start guide for small contractors to set...
Read more →
How to Implement Continuous Monitoring Requirements in Vendor SLAs: Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 4-1-2 Step-by-Step
Practical step-by-step guidance to embed continuous monitoring obligations in vendor...
Read more →
How to Implement Boundary Monitoring: Step-by-Step Guide to Monitor, Control, and Protect Organizational Communications — FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SC.L1-B.1.X
Step-by-step practical guidance for implementing boundary monitoring to meet FAR...
Read more →
How to Implement Asset Classification, Labeling and Handling per Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-1-5: Step-by-Step Implementation
Step-by-step guidance to implement ECC 2-1-5 asset classification, labeling and...
Read more →
How to Implement a Quarterly Business Continuity Cybersecurity Review — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 3-1-4: Step-by-Step Process
Step-by-step guidance to implement ECC 2:2024 Control 3-1-4 — a...
Read more →
How to Deploy MFA for External Network Nonlocal Maintenance: Azure AD & Okta Implementation Checklist — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - MA.L2-3.7.5
Step-by-step checklist to implement phishing-resistant MFA for external nonlocal maintenance...
Read more →
How to Deploy Low-Cost Physical Controls for Small Contractors to Comply with FAR 52.204-21 / CMMC 2.0 Level 1 - Control - PE.L1-B.1.VIII
Practical, low-cost physical security controls and deployment steps small contractors...
Read more →
How to Deploy Free and Low-Cost Tools to Identify, Report, and Correct Flaws Rapidly — FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SI.L1-B.1.XII
Practical, low-cost steps and tool recommendations to rapidly identify, report,...
Read more →
How to Create CUI Privacy and Security Notice Templates to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AC.L2-3.1.9 Compliance
Step-by-step guidance and ready-to-deploy templates to create CUI privacy and...
Read more →
How to Create an Implementation Checklist for Protecting Against Malicious Code — FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SI.L1-B.1.XIII
Practical, step-by-step checklist guidance to implement protections against malicious code...
Read more →
How to Create an Audit-Ready Physical Security Requirements Checklist for ECC — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-14-1
Step-by-step guidance and an audit-ready checklist to implement ECC Control...
Read more →
How to Create an Asset Change Checklist Aligned with Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-6-1
Practical step-by-step guidance to build an ECC 2:2024 Control 1-6-1...
Read more →
How to Create a Step-by-Step Test Plan to Validate Incident Response for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - IR.L2-3.6.3
A practical, step-by-step test-plan guide to validate incident response capabilities...
Read more →
How to create a prioritized implementation checklist for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-7-1 to quickly meet national cybersecurity regulations
Step-by-step guidance to build a prioritized, auditable implementation checklist for...
Read more →
How to Create a Practical Risk Management Procedure Template for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-5-2
Learn a step-by-step, ready-to-use procedure template to meet ECC –...
Read more →
How to Create a Compliance Checklist for Periodic Hosting and Cloud Reviews — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 4-2-4
Step-by-step guidance and an actionable checklist to run periodic hosting...
Read more →
How to Create a Compliance Checklist for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - MP.L1-B.1.VII: Sanitize or Destroy Media Before Disposal or Reuse
Step-by-step guidance to build a practical, auditable checklist for sanitizing...
Read more →
How to Create a Checklist and Review Timeline for Periodic Contract Assessments Under Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 4-1-4
Step-by-step guidance to build a practical checklist and timeline for...
Read more →
How to Configure Web and Cloud Settings to Prevent Unauthorized Data Exposure: FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.IV Implementation Guide
[Write a compelling 1-sentence SEO description about this compliance requirement]...
Read more →
How to Configure VPN and TLS for Compliance with NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AC.L2-3.1.13 (Implementation Best Practices)
Practical, step-by-step guidance for configuring VPN and TLS to meet...
Read more →
How to Configure SIEM and Alerting to Fulfill Event Log Requirements Under Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-12-1
Step-by-step guidance to configure SIEM collection, normalization, retention, and alerting...
Read more →
How to Configure Endpoint Security to Enforce NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AC.L2-3.1.21 and Block Portable Storage on External Systems
[Write a compelling 1-sentence SEO description about this compliance requirement]...
Read more →
How to Configure Endpoint Detection and Response (EDR) Updates and Verification to Comply with NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - SI.L2-3.14.4
Practical, technical guidance for configuring automatic EDR updates, validating integrity,...
Read more →
How to Configure Encryption and Key Management to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-8-3: Technical Implementation and Best Practices for Compliance
Practical, step-by-step guidance to implement encryption and key management that...
Read more →
How to Configure AWS VPC Subnets and Security Groups to Satisfy FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SC.L1-B.1.XI
Practical, step-by-step guidance for configuring AWS VPC subnets, route tables,...
Read more →
How to Configure a Secure Server Room: Access Controls, Logging, and Enforcement — FAR 52.204-21 / CMMC 2.0 Level 1 - Control - PE.L1-B.1.VIII
Practical, step-by-step guidance for small businesses to secure server rooms...
Read more →
How to conduct a gap analysis for national cybersecurity law compliance under Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-7-1
Practical step-by-step guidance to perform a gap analysis against ECC...
Read more →
How to Choose Tools and Techniques to Sanitize or Destroy Hard Drives and Removable Media Containing FCI — Practical Implementation for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - MP.L1-B.1.VII
Practical guidance for small businesses on selecting tools, methods, and...
Read more →
How to Choose and Configure Anti-Malware Tools to Demonstrate Compliance with NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - SI.L2-3.14.2: Vendor Selection Checklist
[Write a compelling 1-sentence SEO description about this compliance requirement]...
Read more →
How to Build and Document Cybersecurity Policies for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-3-1: A Step‑by‑Step Implementation Guide
Step‑by‑step guidance to design, approve, implement, and evidence cybersecurity policies...
Read more →
How to Build an Automated Deprovisioning Workflow with IAM Tools to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-9-5
Practical guide to building automated deprovisioning workflows with IAM tools...
Read more →
How to Build an Audit-Ready Physical Access Devices Program: Implementation Checklist for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - PE.L2-3.10.5
Step-by-step implementation checklist and audit evidence guidance to make your...
Read more →
How to Build an Audit-Ready Business Continuity Plan to Comply with Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 3-1-2
Practical, step-by-step guidance to create an audit-ready business continuity plan...
Read more →
How to Build an Asset and Identity Inventory to Identify Users, Processes, and Devices for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - IA.L1-B.1.V
Step-by-step, practical guide for building an asset, identity, and process...
Read more →
How to Build an Annual Risk Assessment Process for CUI Compliance: Checklist and Templates for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - RA.L2-3.11.1
Step-by-step guidance, checklist and ready-to-use templates to implement an annual...
Read more →
How to Build an Access-Control Checklist for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - PE.L1-B.1.VIII to Restrict Equipment and Operating Environments
Practical, step-by-step checklist and real-world guidance to implement access controls...
Read more →
How to Build a Sanitization Checklist for Off‑Site Maintenance Under NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - MA.L2-3.7.3: Practical Templates and Examples
Step-by-step guidance and ready-to-use templates to build an off-site maintenance...
Read more →
How to build a roles & responsibilities review checklist and timeline for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-4-2 compliance
Step-by-step guidance to create a roles and responsibilities review checklist...
Read more →
How to build a logging and SIEM pipeline for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - SI.L2-3.14.7 to identify unauthorized use of organizational systems
Step-by-step guidance to design a practical logging and SIEM pipeline...
Read more →
How to Build a Compliance-Ready Physical Security Program: Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-14-2 Implementation Checklist
Practical, step-by-step guidance to implement Control 2-14-2 of the Compliance...
Read more →
How to Build a Compliance Checklist for Hosting & Cloud Providers Aligned to Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 4-2-2
Step-by-step guide to creating a hosting and cloud provider compliance...
Read more →
How to Budget and Staff a Dedicated Cybersecurity Function Aligned with ECC Requirements: Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-2-1 Hiring Playbook
Practical guide to budget, staff, and operationalize a dedicated cybersecurity...
Read more →
How to Automate Periodic Reviews and Approvals for Risk Management Methodology — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-5-4
Step-by-step guidance to automate periodic reviews and approval workflows for...
Read more →How to Automate Incident Tracking, Documentation, and External Notifications for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - IR.L2-3.6.2 Compliance
Practical, step-by-step guidance to automate incident tracking, documentation, and external...
Read more →
Compliance Checklist: Steps to Sanitize or Destroy Information System Media Containing FCI Before Disposal — FAR 52.204-21 / CMMC 2.0 Level 1 - Control - MP.L1-B.1.VII
Practical, step-by-step guidance for small businesses to sanitize or destroy...
Read more →
Checklist: How to Achieve Continuous Compliance for Malicious Code Protection Updates — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - SI.L2-3.14.4
Practical, step-by-step checklist to maintain continuous compliance with NIST SP...
Read more →
10 Actionable Controls to Limit Physical Access and Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - PE.L2-3.10.1 Today
Practical, step-by-step physical access controls to help organizations implement PE.L2-3.10.1...
Read more →
Step-by-Step: Implementing Session Expiration in Cloud Environments for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AC.L2-3.1.11
Practical, step-by-step guidance to implement automatic session expiration in cloud...
Read more →
Step-by-Step Implementation Plan: From Hiring to Termination — Meeting Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-9-1 Requirements
A practical, step-by-step plan for small businesses to implement ECC-2:2024...
Read more →
Step-by-Step Implementation Checklist for Cryptography under Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-8-2
Practical, step-by-step checklist to implement cryptographic controls for ECC 2-8-2...
Read more →
Practical Checklist: Conducting Effective Periodic Reviews of Backup and Recovery (Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-9-4)
A practical, step-by-step checklist for conducting periodic reviews of backup...
Read more →
How to write an auditable removable media policy aligned to NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - MP.L2-3.8.8 (templates and checklist)
Step-by-step guidance, templates, and a checklist for writing an auditable...
Read more →
How to Use Metrics and KPIs to Drive Periodic Reviews of Your Cybersecurity Awareness Program — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-10-5
Practical guidance on defining, collecting, and using metrics and KPIs...
Read more →
How to Use IAM Tools (Azure AD, AWS IAM, GCP) to Enforce Identifier Reuse Prevention — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - IA.L2-3.5.5
Step-by-step guidance for using Azure AD, AWS IAM, and GCP...
Read more →
How to Test Your Incident Response Capability: Step-by-Step Implementation for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - IR.L2-3.6.3
Step-by-step guidance to plan, run, measure, and document incident response...
Read more →
How to Secure Cloud Workloads for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - CM.L2-3.4.7: Practical Steps for AWS, Azure, and GCP
Practical, platform-specific steps to meet NIST SP 800-171 Rev.2 /...
Read more →
How to Sanitize and Reuse IT Media Safely to Meet FAR 52.204-21 / CMMC 2.0 Level 1 - Control - MP.L1-B.1.VII Requirements
Step-by-step guidance for securely sanitizing and reusing IT media to...
Read more →
How to Run Effective Security Awareness Training and Track Metrics for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-9-2
Practical guidance for implementing Control 1-9-2 of ECC–2:2024: design security...
Read more →
How to Produce an ECC‑Compliant Penetration Test Checklist and Evidence Log for Auditors (Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-11-1)
Step-by-step guidance to create an ECC‑compliant penetration testing checklist and...
Read more →
How to Prepare for a Compliance Audit: Evidence Checklist for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - PE.L1-B.1.VIII
Practical evidence checklist and implementation steps to meet the physical...
Read more →
How to Prepare for a CMMC Assessment by Documenting Periodic Control Effectiveness for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - CA.L2-3.12.1
Practical, step-by-step guidance for documenting periodic control effectiveness to meet...
Read more →
How to Prepare for a CMMC 2.0 Level 2 Assessment: Demonstrating AC.L2-3.1.12 Compliance for Monitoring and Controlling Remote Access Sessions (NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AC.L2-3.1.12)
Step-by-step guidance and practical evidence you can produce to demonstrate...
Read more →
How to Prepare a PE.L1-B.1.IX Compliance Checklist for Assessments (FAR 52.204-21 / CMMC 2.0 Level 1 - Control - PE.L1-B.1.IX)
Practical step-by-step guidance to build a PE.L1-B.1.IX compliance checklist for...
Read more →
How to Perform Secure Media Sanitization Before Reuse: Practical Methods and Tools for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - MP.L1-B.1.VII
Practical, step-by-step guidance on sanitizing storage media before reuse to...
Read more →
How to Move from Policy to Production: Deploy Deny-by-Default Network Controls for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - SC.L2-3.13.6 in 8 Practical Steps
Step-by-step guide to implement deny-by-default network controls required by NIST...
Read more →
How to Monitor Security Alerts and Advisories to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - SI.L2-3.14.3: A Step-by-Step Implementation Guide
Step-by-step guidance to build an operational program that monitors security...
Read more →
How to Migrate Backups Securely to Cloud Storage While Protecting CUI — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - MP.L2-3.8.9
Step-by-step guidance for small businesses to migrate backups to cloud...
Read more →
How to Meet FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SI.L1-B.1.XII (Code 555): Practical Steps to Detect, Report, and Correct Vulnerabilities Quickly
Step-by-step guidance for small businesses to implement rapid vulnerability detection,...
Read more →
How to Map Your Policies to Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-7-1 and National Cybersecurity Regulations: Practical Template & Checklist
Step-by-step guidance and a ready-to-use template for mapping organizational policies...
Read more →
How to Integrate Vulnerability Management Tools with Your Compliance Program for SI.L1-B.1.XII — FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SI.L1-B.1.XII
Practical steps to integrate vulnerability scanning and remediation tools into...
Read more →
How to Integrate SIEM, SOAR, and Automation for Faster Incident Response and Threat Management — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-13-2
Practical guidance to integrate SIEM, SOAR, and automation to meet...
Read more →
How to Integrate ECC 1-1-2 Roadmap Execution with ISO 27001 and HIPAA Compliance — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-1-2
Practical guide to executing ECC 1-1-2 roadmaps and mapping evidence...
Read more →
How to Implement Physical Access Controls: Step-by-Step Guide for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - PE.L2-3.10.1
A practical, step-by-step implementation guide to meet NIST SP 800-171...
Read more →
How to Implement Patch Management and Remediation Workflows Aligned to Risk Assessments — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - RA.L2-3.11.3
Practical step‑by‑step guidance to build patch management and remediation workflows...
Read more →
How to Implement OS Hardening, Database Security and Firewall Rules for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-3-3 Compliance
Step-by-step guidance to implement OS hardening, database security and firewall...
Read more →
How to Implement Onboarding, Credential Verification, and Background Checks for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-2-2 Compliance
Step-by-step guidance for small businesses to implement compliant onboarding, identity...
Read more →
How to Implement NIST SP 800-88 Media Sanitization Techniques to Comply with FAR 52.204-21 / CMMC 2.0 Level 1 - Control - MP.L1-B.1.VII
Step-by-step guidance for small businesses to apply NIST SP 800-88...
Read more →
How to Implement Least Privilege to Comply with FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.II: Practical Controls and Validation
Step-by-step guidance to implement least privilege for FAR 52.204-21 and...
Read more →
How to Implement Least Privilege Across Windows, Linux, and Cloud to Satisfy NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AC.L2-3.1.6
Step-by-step, practical guidance to apply least-privilege on Windows, Linux, and...
Read more →
How to Implement Key Management and Algorithm Controls to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-8-3
Practical, step-by-step guidance for small businesses to implement cryptographic key...
Read more →
How to Implement FAR 52.204-21 / CMMC 2.0 Level 1 - Control - PE.L1-B.1.VIII: Step-by-Step Guide to Limiting Physical Access to Authorized Individuals
Practical, step-by-step guidance for small businesses to meet FAR 52.204-21...
Read more →
How to Implement Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-6-3 in Your Software Development Lifecycle: A Practical 8-Step Plan
A practical, step-by-step guide to integrating ECC 2:2024 Control 1-6-3...
Read more →
How to Implement Encryption, Safes, and Physical Locks for Digital and Paper Media: NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - MP.L2-3.8.1 Compliance Checklist
Practical, step-by-step guidance for meeting MP.L2-3.8.1 (restricting physical access to...
Read more →
How to Implement an Operational Incident-Handling Capability: Step-by-Step for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - IR.L2-3.6.1
Step-by-step guidance to build an operational incident-handling capability that meets...
Read more →
How to Implement an End-to-End SI.L2-3.14.1 Compliance Checklist: From Detection to Correction for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - SI.L2-3.14.1
A practical, step-by-step checklist to meet SI.L2-3.14.1 (detect, report, and...
Read more →
How to Implement a Security Awareness Program for Managers, System Administrators, and Users — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AT.L2-3.2.1 (Step-by-Step Guide)
Step-by-step practical guidance to design, deploy, measure, and document a...
Read more →
How to implement a lightweight verification and control workflow for small businesses to comply with FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.III
A practical, step-by-step guide for small businesses to implement a...
Read more →
How to Harden Cloud IAM (AWS/Azure/GCP) to Limit Access to Authorized Transactions and Functions — FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.II
Practical guidance for small businesses to harden AWS, Azure, and...
Read more →
How to Deploy Multi-Factor Authentication to Satisfy Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-2-2: Implementation Best Practices
Step-by-step guidance to implement Multi-Factor Authentication (MFA) that meets ECC‑2:2024...
Read more →
How to Deploy Cloud-Based Subnetworks to Isolate Public Services (AWS/Azure) - FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SC.L1-B.1.XI
Practical step-by-step guidance to design and deploy isolated cloud subnets...
Read more →
How to Create Ready-to-Use Third-Party Security Clause Templates for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 4-1-3
Practical guidance and ready-to-use clause language to help organizations meet...
Read more →
How to create an ECC-compliant data handling policy: Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-7-1 template and approval workflow
Practical, step-by-step template and approval workflow to implement ECC Control...
Read more →
How to Create an Audit-Ready Vulnerability Reporting Workflow for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SI.L1-B.1.XII
Step-by-step guidance to build an audit-ready vulnerability reporting workflow that...
Read more →
How to create an audit-ready checklist to verify and limit external information system access — FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.III
Step-by-step guidance and an audit-ready checklist to verify and limit...
Read more →
How to Create a Third-Party Agreement Review Checklist for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 4-1-4
Step-by-step guidance and a practical checklist to ensure third-party contracts...
Read more →
How to Create a Step-by-Step Audit Checklist for Periodic Review of Penetration Testing Processes to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-11-4
Practical, step-by-step guidance to build an audit checklist for periodic...
Read more →
How to Create a FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SI.L1-B.1.XIII Checklist: Verifying Protection from Malicious Code Across Your Information Systems
Step-by-step checklist and test procedures to verify FAR 52.204-21 and...
Read more →
How to Create a 90-Day Implementation Plan to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-1-2 Requirements
A practical 90-day roadmap to implement Control 1-1-2 of the...
Read more →
How to Configure Role-Based Access Controls (RBAC) to Enforce Transaction and Function Limits - FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.II
Step-by-step guidance for small businesses to implement RBAC that enforces...
Read more →
How to Configure MFA and SSO to Satisfy Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-2-2: Practical Deployment Steps
Step-by-step guidance for small businesses to implement MFA and SSO...
Read more →
How to Configure Audit Trails for User Traceability — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AU.L2-3.3.2 Implementation Checklist
Practical step-by-step checklist to configure audit trails that satisfy AU.L2-3.3.2...
Read more →
How to Conduct Contractor and Third-Party Screening for CUI Access: NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - PS.L2-3.9.1 Implementation Guide
Practical, actionable guidance for screening contractors and third parties before...
Read more →
How to Conduct a Gap Assessment and Remediation Plan for PE.L1-B.1.IX (FAR 52.204-21 / CMMC 2.0 Level 1 - Control - PE.L1-B.1.IX)
Practical steps to assess gaps and build a remediation plan...
Read more →
How to Choose and Test Antimalware Tools to Demonstrate Compliance: FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SI.L1-B.1.XIII
Practical guidance for selecting, configuring, and testing antimalware tools to...
Read more →
How to Build an Offboarding Checklist to Protect CUI During Terminations and Transfers — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - PS.L2-3.9.2
Step-by-step guidance to build an offboarding checklist that preserves Controlled...
Read more →
How to Build an Incident Response Playbook That Meets NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - IR.L2-3.6.1 (Detection, Analysis, Containment, Recovery)
Step-by-step guidance to create an incident response playbook that satisfies...
Read more →
How to build an HR-IT integrated termination checklist to comply with Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-9-5
Step-by-step guidance for building an HR–IT integrated offboarding checklist that...
Read more →
How to Build an Automated Offboarding Process to Protect CUI — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - PS.L2-3.9.2
Automate offboarding to promptly remove access to CUI and meet...
Read more →
How to Build an Audit-Ready Physical Security Program to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - PE.L2-3.10.1 (Checklist Included)
Step-by-step guidance to design and document an audit-ready physical security...
Read more →
How to Build an Audit-Ready Monitoring Plan for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SC.L1-B.1.X: Templates and Checklists
Step-by-step guidance and ready-to-use templates to build an audit-ready monitoring...
Read more →
How to Build a Practical Incident Response Playbook (Preparation → Recovery) for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - IR.L2-3.6.1
Step-by-step guidance to build an incident response playbook that meets...
Read more →
How to Build a Compliant Penetration Testing Program for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-11-2: Scoping, Execution, and Reporting
Practical guidance for building a penetration testing program that meets...
Read more →
How to Build a Compliance-Ready Authentication Flow for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - IA.L1-B.1.VI: Practical Implementation Guide
Step-by-step, practical guidance to design and implement an authentication flow...
Read more →
How to Build a Compliance Checklist for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.IV to Control Information Processed on Publicly Accessible Systems
Step-by-step guidance and a practical checklist to ensure FAR 52.204-21...
Read more →
How to build a compliance checklist for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-3-3 for information processing facilities
Step-by-step guidance to create a practical, evidence-driven compliance checklist for...
Read more →
How to Build a Business Continuity Plan That Meets Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 3-1-3
Practical, step-by-step guidance to create a Business Continuity Plan that...
Read more →
How Small Businesses Can Deploy Practical Controls to Monitor and Protect Communications: FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SC.L1-B.1.X
Practical, low-cost steps small businesses can take to monitor and...
Read more →
From Design to Deployment: Implementing Segregated Subnetworks in AWS/Azure for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SC.L1-B.1.XI
Practical guide to designing and deploying segregated subnetworks in AWS...
Read more →
Checklist: Configuring Visitor Badges, Escorting, Monitoring and Audit Logs to Achieve FAR 52.204-21 / CMMC 2.0 Level 1 - Control - PE.L1-B.1.IX Compliance
Step-by-step checklist and technical guidance to configure visitor badges, escorting,...
Read more →
Step-by-Step Checklist: Sanitizing or Destroying Reusable Media Before Disposal for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - MP.L1-B.1.VII
Practical, step-by-step guidance for sanitizing or destroying reusable media to...
Read more →
Step-by-Step Checklist for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.III: Verify and Limit External System Connections for Compliance
Practical, step-by-step guidance to verify and limit external system connections...
Read more →
Implement a Media Disposal Policy to Meet FAR 52.204-21 / CMMC 2.0 Level 1 - Control - MP.L1-B.1.VII: Practical Steps and Templates
Learn practical steps, technical methods, and ready-to-use templates to implement...
Read more →
How to Write and Enforce an Inactivity Disablement Policy (Template + Checklist): NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - IA.L2-3.5.6
Practical guidance, a ready-to-use policy template, and an audit-ready checklist...
Read more →
How to Verify and Monitor External System Connections for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.III: Tools, Logs, and Automated Alerts
Step-by-step guidance to verify and continuously monitor external system connections...
Read more →
How to Use NIST SP 800-88 Guidance to Meet FAR 52.204-21 / CMMC 2.0 Level 1 - Control - MP.L1-B.1.VII: Practical Implementation Steps for Sanitizing and Destroying Information System Media
Practical, step-by-step guidance on applying NIST SP 800-88 media sanitization...
Read more →
How to Use Low-Cost Physical Controls to Achieve FAR 52.204-21 / CMMC 2.0 Level 1 - Control - PE.L1-B.1.VIII Compliance: A Small Business Guide
Practical, low-cost physical controls and implementation steps a small business...
Read more →
How to Use Checklists and Templates to Achieve Compliance with Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-9-1: Pre-Employment, During Employment and Post-Separation Requirements
Practical checklist and template-driven guidance to meet ECC – 2...
Read more →
How to Use a Change Management Checklist to Analyze Security Impact Before Implementation — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - CM.L2-3.4.4
Step-by-step guidance and a practical checklist to analyze security impact...
Read more →
How to Train Employees to Spot and Report Insider Threats: A Practical Implementation Checklist for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AT.L2-3.2.3
Practical, step-by-step guidance to train staff to identify and report...
Read more →
How to Schedule and Document Periodic Cybersecurity Requirement Reviews in Projects (Template + Timeline) — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-6-4
Practical, step-by-step guidance to schedule, run, and document periodic cybersecurity...
Read more →
How to sanitize or destroy information system media containing Federal Contract Information before disposal: Step-by-step guide for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - MP.L1-B.1.VII
Step-by-step best practices for securely sanitizing or destroying media containing...
Read more →
How to sanitize and destroy HDDs and SSDs before reuse: practical procedures for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - MP.L1-B.1.VII
Practical, standards-aligned procedures to sanitize or destroy HDDs and SSDs...
Read more →
How to Run Tabletop Exercises to Test Organizational Incident Response Capability: NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - IR.L2-3.6.3 — Template and Checklist
Step-by-step guidance, a reusable exercise template, and an audit-ready checklist...
Read more →
How to Prioritize Vulnerabilities and Develop Remediation Plans Step-by-Step — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - CA.L2-3.12.2
Step-by-step guidance for small businesses to prioritize vulnerabilities and build...
Read more →
How to Prioritize and Remediate Vulnerabilities Using Risk Assessments for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - RA.L2-3.11.3
Practical, step-by-step guidance to use risk assessments to prioritize and...
Read more →
How to Prepare for a CMMC Assessment: Demonstrating Compliance with FAR 52.204-21 / CMMC 2.0 Level 1 - Control - MP.L1-B.1.VII for Media Disposal
Practical step-by-step guidance for small businesses to meet FAR 52.204-21...
Read more →
How to Prepare an SSP for Assessment: Evidence, Artifacts, and Checklists for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - CA.L2-3.12.4
Step-by-step guidance for creating an SSP and assembling evidence, artifacts,...
Read more →
How to Perform a Gap Analysis and Translate Findings into an Executable Roadmap: Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-1-2
Step-by-step guidance for performing a gap analysis against ECC‑2:2024 Control...
Read more →
How to Map Cybersecurity Requirements into Your Project Lifecycle: Practical Templates for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-6-1
Practical guidance and ready-to-use templates to map ECC – 2...
Read more →
How to manage third-party libraries and supply-chain security for external web applications to satisfy Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-15-3
Practical, step-by-step guidance for small businesses to secure third‑party libraries...
Read more →
How to Implement Threat Detection and Triage for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-13-3 Using SIEM and EDR
A practical, step-by-step guide to meeting ECC 2-13-3 by integrating...
Read more →
How to Implement Risk-Based Prioritization for Patching and Remediation — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - RA.L2-3.11.3
Step-by-step guidance to implement risk-based prioritization for patching and remediation...
Read more →
How to implement RBAC step-by-step to limit transactions and functions — FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.II
Step-by-step guide to implement role-based access control (RBAC) to limit...
Read more →
How to Implement NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AU.L2-3.3.9: Limit Audit Logging Management to a Subset of Privileged Users (Step-by-Step)
Step-by-step guidance for small organizations to restrict audit-log management to...
Read more →
How to Implement Multi-Factor Authentication (MFA) for Users, Processes, and Devices: Step-by-Step for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - IA.L2-3.5.2
Step-by-step guide to implementing MFA for users, processes, and devices...
Read more →
How to Implement Layered Malware Defenses (NGAV, EDR, Email Filtering) for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - SI.L2-3.14.2: Practical Configurations
Step-by-step, practical guidance to implement and configure NGAV, EDR, and...
Read more →
How to Implement FAR 52.204-21 / CMMC 2.0 Level 1 - Control - PE.L1-B.1.VIII: A Practical Checklist to Limit Physical Access
Step-by-step checklist and practical guidance to meet FAR 52.204-21 and...
Read more →
How to implement Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-7-3: A practical checklist to meet NCA Data Cybersecurity Controls requirements
Step-by-step checklist to implement ECC – 2 : 2024 Control...
Read more →
How to Implement Application Whitelisting to Control and Monitor User-Installed Software — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - CM.L2-3.4.9
Step-by-step guidance for implementing application whitelisting to control and monitor...
Read more →
How to Implement a Secure Media Disposal Program for Small Contractors: FAR 52.204-21 / CMMC 2.0 Level 1 - Control - MP.L1-B.1.VII Practical Guide
Practical, step-by-step guidance for small contractors to implement a compliant...
Read more →
How to Implement a Compliant Incident Response Policy: Practical Checklist for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-13-1
Step-by-step guidance and a practical checklist to implement a compliant...
Read more →
How to Implement a Compliant Cybersecurity Organizational Structure: Step-by-Step Guide to Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-4-1
Step-by-step practical guidance for implementing a compliant cybersecurity organizational structure...
Read more →
How to Follow a Quick Implementation Checklist for Protecting Information at External and Key Internal Boundaries (FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SC.L1-B.1.X)
Step-by-step checklist to protect information at external and internal boundaries...
Read more →
How to Draft Vendor Security Clauses to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 4-1-3: Practical Contract Language and Examples
Practical, ready-to-use contract language and implementation guidance to ensure vendor...
Read more →
How to deploy and configure antivirus and EDR to meet FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SI.L1-B.1.XIII — practical implementation checklist
Practical step-by-step checklist for small businesses to deploy antivirus and...
Read more →
How to Demonstrate Compliance: Evidence and Testing for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SC.L1-B.1.X
Practical, testable guidance on the evidence and verification steps small...
Read more →
How to Create ECC-Aligned Training Modules to Cover Phishing, Ransomware, and Social Engineering — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-10-3
Step-by-step guidance to design and implement ECC 1-10-3 aligned training...
Read more →
How to Create a Compliance-Ready Audit Log Policy for Physical Access: Checklist and Templates (NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - PE.L2-3.10.4)
Practical step-by-step guidance, checklists, and templates to build a compliance-ready...
Read more →
How to Create a Compliance Checklist for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SI.L1-B.1.XII: Identify, Report, and Fix Information System Flaws
Step-by-step guidance to build a practical compliance checklist for FAR...
Read more →
How to Create a 5-Step Business Continuity Management Plan to Satisfy Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 3-1-2
Step-by-step guidance for small businesses to build a 5-step Business...
Read more →
How to Configure Web Login Pages to Obscure Authentication Feedback (NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - IA.L2-3.5.11) — Practical Implementation Checklist
Step-by-step practical checklist to configure web login pages to obscure...
Read more →
How to Configure VPN, MFA, and Endpoint Controls to Restrict External System Access — FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.III
Practical, step-by-step guidance for configuring VPNs, MFA, and endpoint posture...
Read more →
How to Configure SIP/TLS and SRTP for Compliance with NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - SC.L2-3.13.14
Practical step-by-step guidance for configuring SIP over TLS and SRTP...
Read more →
How to Configure RBAC in Active Directory to Limit System Transactions — FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.II
Practical, step-by-step guidance to implement Role-Based Access Control (RBAC) in...
Read more →
How to Configure Multi-Factor Authentication for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - IA.L1-B.1.VI Compliance: A Technical Checklist
Step-by-step technical checklist to deploy and enforce multi-factor authentication (MFA)...
Read more →
How to Configure Firewalls, VLANs, and ACLs to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-5-2 Requirements
Step-by-step guidance for small businesses to implement firewalls, VLAN segmentation,...
Read more →
How to Conduct Background Checks and Document Results for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - PS.L2-3.9.1 Compliance
Step-by-step guidance on performing and recording background checks to satisfy...
Read more →
How to Conduct a Gap Assessment Against Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-8-1 with Step-by-Step Implementation
Step-by-step guidance to perform a gap assessment for ECC‑2:2024 Control...
Read more →
How to Choose the Right Sanitization Method for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - MP.L1-B.1.VII: Overwriting, Degaussing, and Physical Destruction Guidelines
Practical guidance for small businesses to select and implement overwriting,...
Read more →
How to Choose and Implement Scanning Tools to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - SI.L2-3.14.5: Selection Criteria and Deployment Tips
Practical guidance for selecting and deploying vulnerability and malware scanning...
Read more →
How to Build an Incident Reporting Workflow for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - IR.L2-3.6.2: Templates, Timelines, and Escalation Paths
Practical guide to designing an IR.L2-3.6.2 incident reporting workflow that...
Read more →
How to Build an Audit-Ready Incident Reporting Process for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - IR.L2-3.6.2: Templates, Logs, and Timelines
Practical guidance to create an audit-ready incident reporting process that...
Read more →
How to Build an Audit-Ready Event Logging and Monitoring Management Program for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-12-1
Practical, step-by-step guidance for implementing an audit-ready event logging and...
Read more →
How to Build an Audit-Ready Compliance Program for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-7-2: Practical Implementation Checklist
Step-by-step, audit-ready checklist to implement Control 1-7-2 of the Compliance...
Read more →
How to Build an Audit-Ready Checklist for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SC.L1-B.1.X to Monitor, Control, and Protect Communications
Practical steps and an evidence-driven checklist to meet FAR 52.204-21...
Read more →
How to Build an Audit-Ready Backup and Recovery Review Checklist for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-9-4
Step-by-step guidance to create an audit-ready backup and recovery review...
Read more →
How to Build an Asset Labeling System that Satisfies Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-1-5: Templates and Examples
Practical templates, examples, and step-by-step guidance to implement an asset...
Read more →
How to Build a Termination Playbook to Secure Systems Containing CUI — Implementation Checklist for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - PS.L2-3.9.2
Practical, step-by-step guidance to build a termination playbook that promptly...
Read more →
How to Build a Step-by-Step Whitelisting Strategy to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - CM.L2-3.4.8
Practical step-by-step guidance for implementing application whitelisting to meet NIST...
Read more →
How to Build a Step-by-Step Termination Checklist to Protect CUI - NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - PS.L2-3.9.2
A practical, step-by-step guide to building a termination checklist that...
Read more →
How to Build a Mobile Device Connection Policy for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AC.L2-3.1.18 (With Template)
Practical guide and ready-to-use template for creating a mobile device...
Read more →
How to Build a Media Disposal Policy to Meet FAR 52.204-21 / CMMC 2.0 Level 1 - Control - MP.L1-B.1.VII: Checklist and Templates
Step-by-step guidance, a practical checklist, and ready-to-use templates to build...
Read more →
How to Build a Documented, Approved Physical Security Program for IT Assets with Templates and Checklists — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-14-1
Step-by-step guidance, templates, and checklists to create a documented and...
Read more →
How to Build a Compliant Visitor Escort and Audit Log Program for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - PE.L1-B.1.IX (Checklist & Implementation Steps)
Step-by-step guidance for small businesses to implement a visitor escort...
Read more →
How to Build a BYOD Policy Compliant with Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-6-3: Template and Implementation Checklist
Step-by-step guidance and a ready-to-use template to build a BYOD...
Read more →
How to Automate Periodic Reviews of Your Cybersecurity Awareness Program Using LMS and Reporting Tools — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-10-5
Learn how to automate periodic reviews of your cybersecurity awareness...
Read more →
How to Automate Evidence Collection for Cybersecurity Strategy Reviews under Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-1-3
Automate collection and tamper-evident storage of evidence for ECC –...
Read more →
How to Automate Evidence Collection and Reporting for Periodic Reviews of Physical Protection of Information and Technology Assets — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-14-4
Practical guidance to automate evidence collection and reporting for periodic...
Read more →
How to Automate Compliance Checks for Periodic Network Security Requirement Reviews with Scripts and Tools — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-5-4
Step-by-step guidance to automate periodic network security requirement reviews using...
Read more →
How Small IT Teams Can Implement SC.L1-B.1.X: Stepwise Implementation of FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SC.L1-B.1.X
Practical, step-by-step guidance for small IT teams to implement SC.L1-B.1.X...
Read more →
CUI at Home and Satellite Offices: A 10-Point Checklist to Comply with NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - PE.L2-3.10.6
A practical 10-point checklist to help small businesses protect Controlled...
Read more →
Step-by-Step Template: Define, Document, and Obtain Approval for Your Cybersecurity Strategy to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-1-1
A practical, step-by-step template to define, document, and obtain formal...
Read more →
Step-by-Step Implementation: Creating an Approved Vulnerability Management Policy for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-10-1
Step-by-step guidance to draft, approve, and operationalize an ECC 2:2024...
Read more →
Step-by-Step: How to Sanitize or Destroy Information System Media to Meet FAR 52.204-21 / CMMC 2.0 Level 1 - Control - MP.L1-B.1.VII
Practical, step-by-step guidance for small businesses to sanitize or destroy...
Read more →
Step-by-Step Guide to Enforce NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AC.L2-3.1.4: Practical Role Separation and Access Controls
Concrete, step-by-step guidance to implement AC.L2-3.1.4 (role separation and access...
Read more →
Implementing Cloud Audit Log Alerts on AWS and Azure to Meet AU.L2-3.3.4 Requirements — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AU.L2-3.3.4
How to design, implement, and tune AWS and Azure audit...
Read more →
How to Use SIEM to Automate Periodic Event Log Reviews and Maintain Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-12-4
Practical guidance on using a SIEM to automate periodic event...
Read more →
How to Use LMS & Automation to Satisfy NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AT.L2-3.2.2: Tools, Templates, and Best Practices
Practical guidance for using an LMS plus automation (SSO, HRIS...
Read more →
How to Use DLP, Containerization, and RBAC to Satisfy NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - SC.L2-3.13.4
Practical, step-by-step guidance for using Data Loss Prevention, containerization, and...
Read more →
How to Use Cloud Security Tools to Schedule and Evidence Periodic Reviews for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 4-2-4
Practical step-by-step guidance for using cloud-native and lightweight tools to...
Read more →
How to Use Cloud and Hybrid Backup Strategies to Fulfill Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-9-3 Requirements
Practical guidance on implementing cloud and hybrid backup strategies to...
Read more →
How to Use a Template & Checklist to Review Cybersecurity Roles under Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-4-2
Step-by-step guidance and a practical checklist to review, validate and...
Read more →
How to Secure Remote and Cloud Communications at Boundaries: VPN, CASB, and Firewall Strategies — FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SC.L1-B.1.X
Practical guidance for small businesses to secure remote and cloud...
Read more →
How to Secure Offsite and Cloud Backups for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-9-3 Compliance
Practical, step-by-step guidance to secure offsite and cloud backups to...
Read more →
How to Run Phishing Simulations and Report Metrics to Demonstrate Compliance — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-10-1
Step-by-step guidance for running phishing simulations, measuring human risk, and...
Read more →
How to Run Cybersecurity Risk Assessments Before Cloud Migrations to Satisfy Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-5-3
Step-by-step guidance for performing cybersecurity risk assessments before cloud migrations...
Read more →
How to Prioritize and Track Vulnerability Remediation Using a PoA&M Template for CMMC 2.0 Level 2 — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - CA.L2-3.12.2
Learn how to use a Plan of Action and Milestones...
Read more →
How to Prepare for a CMMC 2.0 Level 2 Assessment: Demonstrating Compliance with MP.L2-3.8.1 for Media Protection — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - MP.L2-3.8.1
Practical guidance for small businesses to implement, document, and demonstrate...
Read more →
How to Prepare Evidence and Pass an Audit for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - PE.L1-B.1.VIII: Documentation, Metrics, and Common Pitfalls
Practical guidance on assembling documentation, defining metrics, and avoiding pitfalls...
Read more →
How to Integrate Patch Management into Your Maintenance Workflow: Step-by-Step Implementation — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - MA.L2-3.7.1
Practical, step-by-step guidance to integrate patch management into your maintenance...
Read more →
How to Implement VPNs, MFA, and Firewalls to Comply with NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AC.L2-3.1.20
Practical, step-by-step guidance for small businesses to implement VPNs, multi‑factor...
Read more →
How to Implement User and Device Authentication for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - IA.L1-B.1.VI: Step-by-Step MFA and SSO Guide
[Write a compelling 1-sentence SEO description about this compliance requirement]...
Read more →
How to Implement SLA Cybersecurity Requirements for Vendors per Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 4-1-2: Templates and Clauses
Step-by-step guidance and ready-to-use clause examples for embedding ECC 2:2024...
Read more →
How to Implement Multi-Factor Authentication and Strong Password Controls to Fulfill FAR 52.204-21 / CMMC 2.0 Level 1 - Control - IA.L1-B.1.VI
Practical, step-by-step guidance for small businesses to implement multi-factor authentication...
Read more →
How to Implement MFA, Least Privilege, and Device Management for Compliance — FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.I
Practical, step-by-step guidance to implement MFA, least privilege, and device...
Read more →
How to Implement FAR 52.204-21 / CMMC 2.0 Level 1 - Control - PE.L1-B.1.VIII: Step-by-Step Physical Access Control Implementation for Compliance
Step-by-step, practical guidance for small businesses to meet FAR 52.204-21...
Read more →
How to Implement FAR 52.204-21 / CMMC 2.0 Level 1 - Control - PE.L1-B.1.VIII: A Step-by-Step Physical Access Controls Checklist for Compliance
A practical, step-by-step checklist for small businesses to implement FAR...
Read more →
How to Implement Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-7-3 to Meet NCA Data Cybersecurity Controls (Code 490): A Step-by-Step Implementation Plan
Practical, step-by-step guidance to implement ECC – 2 : 2024...
Read more →
How to Implement Data Handling Policies for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-7-2: A Step-by-Step Guide
Step-by-step guidance to implement Data Handling Policies for ECC 2:2024...
Read more →
How to implement cybersecurity risk assessment procedures when migrating to cloud services — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-5-3
Practical, step-by-step guidance to implement risk assessment procedures during cloud...
Read more →
How to Implement Continuous Monitoring to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - CA.L2-3.12.3: A Practical 8-Step Plan
Practical, step-by-step guidance for implementing continuous monitoring to satisfy NIST...
Read more →
How to Implement a Step-by-Step Asset Inventory and Classification Process for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-1-5
Step-by-step guidance to build an auditable asset inventory and classification...
Read more →
How to Harden Windows and Linux Systems to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - CM.L2-3.4.6: A Practical Implementation Checklist
Step-by-step checklist for hardening Windows and Linux systems to meet...
Read more →
How to Draft Vendor SLAs That Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 4-1-2: A Step-by-Step Implementation Checklist
Practical, step-by-step guidance for drafting vendor SLAs that satisfy ECC...
Read more →
How to Document Minimum Security Requirements for External Web Applications: Practical Templates and Examples for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-15-1
Step-by-step guidance and ready-to-use templates to document minimum security requirements...
Read more →
How to Document and Report Strategy Reviews to Satisfy Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-1-3: Templates and Examples
Step-by-step guidance and ready-to-use templates to document and report strategy...
Read more →
How to Destroy Hard Drives, SSDs and Mobile Media to Comply with FAR 52.204-21 / CMMC 2.0 Level 1 - Control - MP.L1-B.1.VII
Practical, actionable guidance for small businesses on sanitizing and destroying...
Read more →
How to Design a Centralized Log Collection and SIEM for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-12-2 Compliance
Step-by-step guidance to design a centralized log collection and SIEM...
Read more →
How to Deploy SIEM and UEBA to Identify Unauthorized Use and Meet SI.L2-3.14.7 — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - SI.L2-3.14.7
Practical, step-by-step guidance for small businesses to deploy SIEM and...
Read more →
How to Create Policies and Procedures to Control Organizational Communications at Boundaries — Template Guide for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SC.L1-B.1.X
Practical template and step-by-step guidance to create policies and procedures...
Read more →
How to Create Evidence-Friendly Logs and Reports to Meet FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SI.L1-B.1.XII
Practical, step-by-step guidance for small businesses to produce tamper-evident logs...
Read more →
How to Create Compliant Audit Reports for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-8-3: Templates and Steps to Capture Scope, Observations, Recommendations, and Remediation
Practical, step-by-step guidance and ready-to-use templates to produce ECC‑2:2024 Control...
Read more →How to Create Audit-Ready Training Evidence for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AT.L2-3.2.2: Templates, Tracking, and Metrics
A practical guide to producing audit-ready training evidence for NIST...
Read more →
How to Create Audit-Ready Change Logs for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - CM.L2-3.4.3: Templates, Fields, and Best Practices
Step-by-step guidance to build audit-ready change logs that meet NIST...
Read more →
How to Create and Maintain Physical Access Audit Logs to Meet FAR 52.204-21 / CMMC 2.0 Level 1 - Control - PE.L1-B.1.IX Requirements
Step-by-step guidance for small businesses to design, implement, and maintain...
Read more →
How to Create an Evidence-Ready Checklist for Demonstrating SC.L1-B.1.X Compliance Under FAR 52.204-21 / CMMC 2.0 Level 1
Step-by-step guide to build an evidence-ready checklist for SC.L1-B.1.X that...
Read more →
How to Create an Audit-Ready Checklist for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.III: Verifying and Controlling Connections to External Systems
Step-by-step guide to build an audit-ready checklist for FAR 52.204-21...
Read more →
How to Create a Risk-Based Implementation Plan for Your Cybersecurity Strategy (Checklist Included) — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-1-2
Step-by-step guidance to build a risk-based implementation plan that meets...
Read more →
How to Create a Practical Implementation Checklist for Monitoring and Controlling Communications for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - SC.L2-3.13.1
Practical step-by-step checklist to monitor, control, and protect organizational communications...
Read more →
How to Create a CUI Risk Assessment Checklist and Template for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - RA.L2-3.11.1
Step-by-step guidance and a practical template to perform and document...
Read more →
How to Correct Information System Flaws Within Required Timeframes — Compliance Checklist for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SI.L1-B.1.XII
Practical, step-by-step guidance for small businesses to discover, prioritize, remediate,...
Read more →
How to configure web apps and APIs to obscure feedback of authentication information for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - IA.L2-3.5.11: practical code and configuration examples
[Write a compelling 1-sentence SEO description about this compliance requirement]...
Read more →
How to Configure Web and API Error Messages to Obscure Feedback of Authentication Information for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - IA.L2-3.5.11
Practical guidance to configure web and API authentication error messages...
Read more →
How to Configure RTO, RPO and Automated Backups for Compliance with Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-9-3
Practical guidance to define RTO/RPO, implement automated backups, and produce...
Read more →
How to Configure Network Controls for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.III: Firewall Rules, Whitelisting, and ACLs You Can Implement Today
Practical, step-by-step guidance on configuring firewall rules, whitelisting, and ACLs...
Read more →
How to Configure MFA to Meet FAR 52.204-21 / CMMC 2.0 Level 1 - Control - IA.L1-B.1.VI for Small Contractors
Step‑by‑step guidance for small contractors to configure multi‑factor authentication (MFA)...
Read more →
How to Configure Endpoint Protection to Automatically Apply New Releases for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SI.L1-B.1.XIV
Step-by-step guidance for small businesses to configure endpoint protection to...
Read more →
How to Configure Endpoint Controls and USB Whitelisting for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - MP.L2-3.8.8 Compliance
Step-by-step guidance to implement endpoint controls and USB device whitelisting...
Read more →
How to Configure Azure AD Conditional Access to Meet FAR 52.204-21 / CMMC 2.0 Level 1 - Control - IA.L1-B.1.VI
Step-by-step guidance to use Azure AD Conditional Access to enforce...
Read more →
How to Build an Audit-Ready Program for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - MA.L2-3.7.2: Policies, Procedures, and Evidence Collection
Step-by-step guidance to create policies, procedures, and an evidence collection...
Read more →
How to Build a Step-by-Step Security Awareness Training Program to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AT.L2-3.2.3
Practical, step-by-step guidance for building a security awareness training program...
Read more →
How to build a penetration testing schedule and review checklist for compliance with Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-11-4
Practical, actionable guidance to design a penetration testing schedule and...
Read more →
How to Build a Patch Management and Vulnerability Reporting Process to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - SI.L2-3.14.1 Compliance
[Write a compelling 1-sentence SEO description about this compliance requirement]...
Read more →
How to Build a Deployable Access Restriction Plan for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.I (Checklist & Templates)
Step-by-step guidance and ready-to-use checklist/templates to implement access restrictions required...
Read more →
How to Build a CUI Remote-Work Security Checklist for Alternate Work Sites — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - PE.L2-3.10.6
Practical step-by-step checklist to secure Controlled Unclassified Information (CUI) at...
Read more →
How to Build a Conflict‑Free Cybersecurity RACI and Role Matrix — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-4-1 (Step‑by‑Step)
Step‑by‑step guidance to design a conflict‑free RACI and role matrix...
Read more →
How to Build a Compliant Cloud DMZ in AWS and Azure with Security Groups and NACLs — FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SC.L1-B.1.XI
Step-by-step guidance to design and implement a compliant cloud DMZ...
Read more →
How to Build a Compliance Checklist to Protect CUI at Remote and Alternate Work Sites — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - PE.L2-3.10.6
Practical steps and a ready checklist to help small businesses...
Read more →
How to Build a Compliance Checklist for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SC.L1-B.1.X: Practical Actions to Secure Key Internal Boundaries
Step-by-step compliance and technical guidance to secure internal network boundaries...
Read more →
How to build a 7-step compliance checklist to identify information system users, processes acting on their behalf, and devices — FAR 52.204-21 / CMMC 2.0 Level 1 - Control - IA.L1-B.1.V
Practical 7-step checklist to identify users, processes acting on their...
Read more →
How to Automate Periodic Reviews of Incident and Threat Management Using SIEM and Workflows — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-13-4
Automate periodic reviews of incident and threat management with SIEM...
Read more →
How to Apply Deny-by-Default Network Controls in AWS/Azure/GCP to Achieve NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - SC.L2-3.13.6 Compliance
Practical, cloud-specific steps to implement deny-by-default network controls in AWS,...
Read more →
Step-by-Step Implementation Checklist to Protect CUI at Rest for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - SC.L2-3.13.16 (Code 191)
Practical, step-by-step checklist to encrypt and protect Controlled Unclassified Information...
Read more →
Step-by-Step Guide to Securely Transporting CUI Media Offsite: NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - MP.L2-3.8.5
Practical, step-by-step guidance for small businesses to securely transport CUI...
Read more →
Step-by-Step Guide to Sanitizing vs Destroying Storage Devices for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - MP.L1-B.1.VII Compliance
Clear, practical steps for small businesses to sanitize or destroy...
Read more →
Step-by-Step Guide: Deploying End-to-End Encryption for Email and File Transfers to Protect CUI — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - SC.L2-3.13.8
Practical, step-by-step guidance to implement end-to-end encryption for email and...
Read more →
Step-by-Step Guide: Configure MFA, Password Policies, and RBAC for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-2-3 Compliance
Practical, step-by-step instructions to implement MFA, strong password policies, and...
Read more →
How to Use Identity and Access Management (IAM) Controls to Enforce AC.L1-B.1.I: Practical Steps for FAR 52.204-21 / CMMC 2.0 Level 1 Compliance
Step-by-step IAM controls and configurations to meet AC.L1-B.1.I, helping small...
Read more →
How to Use IAM Policies to Enforce NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - SC.L2-3.13.3: Practical AWS and Azure Implementation Examples
Practical guidance and copy-paste IAM/Policy examples to enforce encryption-in-transit controls...
Read more →
How to Use ACLs and IAM Policies to Limit System Access per FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.II: Examples for AWS, Azure, and GCP
Practical guidance and cloud-native examples to implement ACLs and IAM...
Read more →
How to Secure External Web Applications to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-15-2 Using Secure Coding and OWASP Best Practices
Practical, step-by-step guidance for applying secure coding and OWASP best...
Read more →
How to Sanitize or Destroy Media Containing Federal Contract Information for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - MP.L1-B.1.VII: A Step-by-Step Implementation Plan
Practical, step-by-step guidance for small businesses to sanitize or destroy...
Read more →
How to Sanitize Hard Drives, SSDs, and USBs Containing FCI for Disposal: FAR 52.204-21 / CMMC 2.0 Level 1 - Control - MP.L1-B.1.VII
Practical, step-by-step guidance for sanitizing HDDs, SSDs, and USBs that...
Read more →
How to Sanitize Hard Drives and SSDs for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - MP.L1-B.1.VII: Tools, Commands, and Verification Steps for FCI
Practical tools, commands, and verification steps to sanitize hard drives...
Read more →
How to Retain and Upskill Full-Time Saudi Cybersecurity Professionals to Sustain Compliance with Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-2-2: Retention Strategies and Career Paths
Practical retention and upskilling strategies for full-time Saudi cybersecurity professionals...
Read more →
How to Protect System Media Containing CUI: Implement NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - MP.L2-3.8.1 with a Step-by-Step Plan for Paper and Digital Records
Practical, step-by-step guidance for small businesses to protect paper and...
Read more →
How to Prioritize and Triage Vulnerabilities for CMMC 2.0 Level 2 Compliance Using Risk Scores — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - RA.L2-3.11.3
Step-by-step guidance to implement risk-scored vulnerability prioritization for CMMC 2.0...
Read more →
How to Prepare for an Audit of FAR 52.204-21 / CMMC 2.0 Level 1 - Control - PE.L1-B.1.VIII: Evidence, Templates, and Implementation Steps to Demonstrate Limited Physical Access
Practical, step-by-step guidance for small businesses to demonstrate limited physical...
Read more →
How to Prepare for an Audit: Evidence, Training Records, and Policies for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AT.L2-3.2.1
Practical, step-by-step guidance for small businesses to create policies, collect...
Read more →
How to Measure Control Effectiveness: Metrics and KPIs for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - CA.L2-3.12.1
Practical guide to measuring control effectiveness for NIST SP 800-171...
Read more →
How to Map and Secure External and Internal Data Flows for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SC.L1-B.1.X: An Implementation Guide
Practical, step-by-step guidance to map and secure internal and external...
Read more →
How to integrate IAM and HR systems to enforce immediate access revocation under Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-9-5
Step-by-step guidance to integrate HRIS and IAM so access is...
Read more →
How to Integrate Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-3-1 into Your ISMS: Practical Implementation Tips
Step-by-step guidance for integrating ECC – 2 : 2024 Control...
Read more →
How to Implement Technical Controls to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-7-2: Configurations and Monitoring for International Commitments
Practical technical guidance to configure systems, enforce geo- and policy-based...
Read more →
How to Implement Network Segmentation and Access Controls for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SC.L1-B.1.X: A Small Business Guide
Step-by-step guide for small businesses to implement practical network segmentation...
Read more →
How to Implement Multi-Factor Authentication to Authenticate Identities for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - IA.L1-B.1.VI: Step-by-Step Deployment Guide
Practical, step-by-step guidance to deploy multi-factor authentication (MFA) that meets...
Read more →
How to Implement MFA, Device Certificates, and Conditional Access for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AC.L2-3.1.18
Step-by-step guidance to implement multi-factor authentication, device certificates, and conditional...
Read more →
How to Implement Low-Cost Physical Security Measures for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - PE.L1-B.1.VIII for Small Contractors
Step-by-step, low-cost physical security measures small contractors can implement to...
Read more →
How to Implement FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.I: Step-by-Step Guide to Limiting Information System Access to Authorized Users, Processes, and Devices
Practical, step-by-step guidance to meet FAR 52.204-21 and CMMC 2.0...
Read more →
How to Implement Continuous Monitoring and Periodic Assessments for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - CA.L2-3.12.1
Practical, step-by-step guidance for implementing continuous monitoring and periodic assessments...
Read more →
How to Implement Background Checks and Screening Policies Before Granting CUI System Access — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - PS.L2-3.9.1
Step-by-step guidance for small businesses to implement background checks and...
Read more →
How to implement automated updates for malicious code protection mechanisms (AV/EDR/IPS) to satisfy NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - SI.L2-3.14.4
Practical, step-by-step guidance to implement automated updates for antivirus/EDR/IPS that...
Read more →
How to Implement Automated Discovery and Inventory for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - IA.L1-B.1.V: Tools, Configuration, and Compliance Checklist
Step-by-step guidance for implementing automated discovery and inventory to meet...
Read more →
How to Implement a Practical Access Control Checklist for Small Contractors to Meet PE.L1-B.1.VIII Requirements — FAR 52.204-21 / CMMC 2.0 Level 1 - Control - PE.L1-B.1.VIII
A concise, practical guide for small contractors to implement an...
Read more →
How to Implement a Compliance Roadmap for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-1-2: Step-by-Step for Small Businesses
Practical, step-by-step guidance for small businesses to implement ECC –...
Read more →
How to Document and Provide Evidence for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - CM.L2-3.4.4: Templates and Audit-Ready Examples
Step-by-step guidance and ready-to-use templates to document, evidence, and audit...
Read more →
How to Design AWS Subnets and Security Groups to Comply with FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SC.L1-B.1.XI
Practical, step-by-step guidance for designing AWS VPC subnets and security...
Read more →
How to Deploy Secure Session Tokens and OAuth Best Practices to Protect the Authenticity of Communications Sessions (NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - SC.L2-3.13.15)
Practical guidance to deploy secure session tokens and OAuth controls...
Read more →
How to Deploy Multi-Layered Malicious Code Protections (Endpoints, Email, Web) for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SI.L1-B.1.XIII
Practical guide to implementing multi-layered malicious code protections across endpoints,...
Read more →
How to Deploy DLP, MDM, and USB Device Control to Enforce Portable Storage Limits on External Systems — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AC.L2-3.1.21
Step-by-step guidance to meet NIST SP 800-171 / CMMC AC.L2-3.1.21...
Read more →
How to deploy a cost-effective visitor management system for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - PE.L1-B.1.IX: Tools, integrations, and tips
Step-by-step guidance to implement a low-cost visitor management system that...
Read more →
How to Create Incident Report Templates and Evidence Logs for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - IR.L2-3.6.2 Compliance
Practical guidance on building incident report templates and evidence logs...
Read more →
How to create an audit-friendly incident response review checklist — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-13-4
Practical, audit-ready steps to build an incident response review checklist...
Read more →
How to Create a Step-by-Step Network Security Review Checklist to Satisfy Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-5-4
A practical, step-by-step guide to building a network security review...
Read more →
How to Create a Sample Review Schedule and Templates for Cybersecurity Roles to Meet ECC Requirements: Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-4-2
Step-by-step guidance to build a practical role-review schedule and reusable...
Read more →
How to Create a Patch Management Checklist to Update Malicious Code Protection (AV/EDR) — FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SI.L1-B.1.XIV
Step-by-step guidance to build a practical patch-management checklist that ensures...
Read more →
How to Create a Compliance-Ready IAM Review Checklist Aligned to Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-2-4
Step-by-step guidance to build a compliance-ready IAM review checklist that...
Read more →
How to Create a Compliance Checklist for Authenticating Users, Processes, and Devices — FAR 52.204-21 / CMMC 2.0 Level 1 - Control - IA.L1-B.1.VI
Step-by-step guidance to build an auditable checklist that ensures users,...
Read more →
How to Create a Chain-of-Custody Process for CUI Media: Step-by-Step Guide to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - MP.L2-3.8.5
Step-by-step practical guide to design and implement a verifiable chain-of-custody...
Read more →
How to Create a Business Continuity Review Checklist That Meets Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 3-1-4 Requirements
Practical, step-by-step guidance to build a Business Continuity review checklist...
Read more →
How to Configure SIEM, Alerts, and Retention to Satisfy ECC Logging Requirements: Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-12-1
Learn step-by-step how to configure SIEM collection, alerts, and retention...
Read more →
How to Configure Mobile Device Management (MDM) to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AC.L2-3.1.18: Policy-to-Device Implementation
Step‑by‑step guidance for configuring MDM so organizational access and usage...
Read more →
How to Configure Firewalls, VPNs, and DLP to Meet FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SC.L1-B.1.X (Implementation Checklist)
Step-by-step implementation guidance to configure firewalls, VPNs, and DLP so...
Read more →
How to Conduct a Step-by-Step Identity and Access Management Audit for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-2-4
Step-by-step guidance for executing an Identity and Access Management audit...
Read more →
How to Choose and Deploy Endpoint AV/EDR Tools to Achieve FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SI.L1-B.1.XV Compliance
Practical guide to selecting, configuring, and documenting AV/EDR solutions to...
Read more →
How to Build and Implement a Cybersecurity Awareness Program to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-10-2: Step-by-Step Checklist
Step-by-step checklist to build and implement a cybersecurity awareness program...
Read more →
How to Build an Evidence-Based Implementation Plan for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SC.L1-B.1.X (Templates Included)
Step-by-step, evidence-focused guidance and ready-to-use templates to meet FAR 52.204-21...
Read more →
How to Build an Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-6-2 Compliance Checklist for BYOD Enrollment, Encryption, and Access Controls
A practical, actionable checklist to meet Compliance Framework Control 2-6-2...
Read more →
How to Build an Audit-Ready System Security Plan for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - CA.L2-3.12.4: Step-by-Step Template for Defining Boundaries, Environments, and System Connections
Step-by-step, practical template for documenting system boundaries, operational environments, and...
Read more →
How to Build an Audit-Ready Physical Protection Policy Template for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-14-1
Step-by-step guidance to create an audit-ready physical protection policy template...
Read more →
How to build an asset inventory and scanning scope that satisfies NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - RA.L2-3.11.2 for endpoints, network gear, and virtual assets
Step-by-step guidance to create an authoritative asset inventory and scanning...
Read more →
How to Build an Approved Log Management Policy (Step-by-Step) — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-12-1
Step-by-step guidance to create an approved log management policy that...
Read more →
How to Build a Step-by-Step Offboarding Process to Protect CUI During Terminations and Transfers — NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - PS.L2-3.9.2
Practical, step-by-step guidance to build an auditable offboarding process that...
Read more →
How to Build a Step-by-Step Compliance Checklist to Monitor, Control, and Protect Communications — FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SC.L1-B.1.X
A practical, step-by-step checklist for monitoring, controlling, and protecting communications...
Read more →
How to Build a Practical Cloud Compliance Checklist (Legal, Technical, Operational) for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 4-2-3
Step-by-step legal, technical, and operational checklist to implement ECC –...
Read more →
How to Build a Periodic Vulnerability Scanning Program to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - RA.L2-3.11.2 (Scheduling, Scope, and Reporting)
Practical guidance to design and operate a periodic vulnerability scanning...
Read more →
How to Build a Cryptography Review Checklist to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-8-4
A practical, step-by-step guide to building a cryptography review checklist...
Read more →
How to Build a Compliance-Friendly Vulnerability Scanning Schedule for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - RA.L2-3.11.2: Scan Frequency, Triggered Scans, and Reporting
Practical guidance to design a vulnerability-scanning cadence, triggered-scan policies, and...
Read more →
How to automate backup verification and periodic reviews to meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-9-4
Automate backup verification and schedule periodic reviews to satisfy ECC...
Read more →
How to Assign and Support Cybersecurity Roles with Templates and Checklists: Implementation Guide for Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-4-1
Practical, step-by-step guidance to assign and support cybersecurity roles using...
Read more →
30-Day Checklist to Achieve FAR 52.204-21 / CMMC 2.0 Level 1 - Control - IA.L1-B.1.V: Identify Users, Service Accounts, and Devices
A practical 30-day checklist to discover, classify, and control users,...
Read more →
How to Turn Cybersecurity Audit Findings into Actionable Remediation Plans for the Authorizing Official — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-8-3
Practical guidance to convert Compliance Framework audit findings into prioritized,...
Read more →
How to Respond to Ransomware and Advanced Threats Under Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-13-3: Actionable Playbook
Practical, step-by-step playbook to meet ECC 2-13-3 for detecting, containing,...
Read more →
How to Implement User Identity Verification to Meet FAR 52.204-21 / CMMC 2.0 Level 1 - Control - IA.L1-B.1.VI: Step-by-Step Guide
A practical, step-by-step guide for small businesses to implement user...
Read more →
How to Implement Risk Assessment Procedures When Onboarding Third-Party Vendors to Comply with Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-5-3 (Checklist)
Practical, step-by-step guidance and a checklist for implementing vendor risk...
Read more →
How to Implement NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - MP.L2-3.8.2: Step-by-Step to Limit Access to Controlled Unclassified Information (CUI) on System Media
Practical, step-by-step guidance for small businesses to meet MP.L2-3.8.2 (limit...
Read more →
How to Implement Least-Privilege Role-Based Access to Meet FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.II: A Step-by-Step Guide
Practical step-by-step guidance for small businesses to implement least-privilege, role-based...
Read more →
How to Implement Cryptographic Protection for CUI: NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - SC.L2-3.13.8 (Step-by-Step Guide)
Step-by-step implementation guide to satisfy NIST SP 800-171/CMMC 2.0 SC.L2-3.13.8...
Read more →
How to Create an Audit-Ready Checklist for Periodic Review of Hosting and Cloud Computing Services — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 4-2-4
Step-by-step guidance to build an audit-ready periodic review checklist for...
Read more →
How to Create a Physical Access Control Checklist for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - PE.L1-B.1.VIII Compliance
Practical, step-by-step guidance to build a physical access control checklist...
Read more →
How to Create a CUI Risk Assessment Checklist and Evidence Package for Audits | NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - RA.L2-3.11.1
Step-by-step guidance to build a CUI-focused risk assessment checklist and...
Read more →
How to Create a Compliance-Driven Schedule to Review Your Cybersecurity Strategy — Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-1-3 (Template & Timeline)
Step-by-step guide and ready-to-use timeline to meet ECC – 2...
Read more →
How to Create a Compliance Checklist for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AU.L2-3.3.2: Technical Controls, Logging Policies, and Evidence Collection
Step-by-step guidance to implement AU.L2-3.3.2 (audit/logging) for NIST SP 800-171...
Read more →
How to Configure TLS, SPF, DKIM and DMARC to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-4-2 Requirements
Step-by-step guidance to configure TLS, SPF, DKIM and DMARC to...
Read more →
How to Configure TLS and Mutual Authentication for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - SC.L2-3.13.15 Compliance
Step-by-step guidance to configure TLS and mutual (mTLS) authentication to...
Read more →
How to Configure Firewalls, IDS/IPS, and TLS to Protect Organizational Communications: Implementation Checklist for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SC.L1-B.1.X
Practical, step-by-step checklist for configuring firewalls, IDS/IPS, and TLS to...
Read more →
How to Configure Endpoint DLP and USB Whitelisting to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - MP.L2-3.8.7
Step-by-step actionable guidance to implement Endpoint Data Loss Prevention and...
Read more →
How to Build an Operational Incident-Handling Capability for NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - IR.L2-3.6.1: A Step-by-Step Implementation Guide
Step-by-step guidance to implement IR.L2-3.6.1 incident-handling capability to meet NIST...
Read more →
How to Build an AC.L1-B.1.III Compliance Checklist (FAR 52.204-21 / CMMC 2.0 Level 1) for Controlling External System Access
Step-by-step checklist and practical controls to meet AC.L1-B.1.III for controlling...
Read more →
How to Build a Risk-Based Vulnerability Remediation Workflow to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-10-1
Step-by-step guidance to design a risk-based vulnerability remediation workflow that...
Read more →
How to Build a FAR 52.204-21 / CMMC 2.0 Level 1 - Control - MP.L1-B.1.VII Compliance Checklist for Sanitizing or Destroying Media Containing FCI
Practical, step-by-step checklist and implementation guidance to sanitize or destroy...
Read more →
How to build a compliant media destruction policy for FAR 52.204-21 / CMMC 2.0 Level 1 - Control - MP.L1-B.1.VII with templates and procedures
Practical, step-by-step guidance to create a media destruction policy that...
Read more →
AWS VPC Example: Implementing Isolated Subnetworks to Meet FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SC.L1-B.1.XI
Practical guidance and a concrete AWS VPC design for isolating...
Read more →
How to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 4-2-4
Practical guide for SMBs to implement Essential Cybersecurity Controls (ECC...
Read more →
How to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 4-2-3
Practical guide for SMBs to implement Essential Cybersecurity Controls (ECC...
Read more →
How to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 4-2-2
Practical guide for SMBs to implement Essential Cybersecurity Controls (ECC...
Read more →
How to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 4-2-1
Practical guide for SMBs to implement Essential Cybersecurity Controls (ECC...
Read more →
How to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 4-1-4
Practical guide for SMBs to implement Essential Cybersecurity Controls (ECC...
Read more →
How to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 4-1-3
Practical guide for SMBs to implement Essential Cybersecurity Controls (ECC...
Read more →
How to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 4-1-2
Practical guide for SMBs to implement Essential Cybersecurity Controls (ECC...
Read more →
How to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 4-1-1
Practical guide for SMBs to implement Essential Cybersecurity Controls (ECC...
Read more →
How to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 3-1-4
Practical guide for SMBs to implement Essential Cybersecurity Controls (ECC...
Read more →
How to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 3-1-3
Practical guide for SMBs to implement Essential Cybersecurity Controls (ECC...
Read more →
How to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 3-1-2
Practical guide for SMBs to implement Essential Cybersecurity Controls (ECC...
Read more →
How to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 3-1-1
Practical guide for SMBs to implement Essential Cybersecurity Controls (ECC...
Read more →
How to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-9-4
Practical guide for SMBs to implement Essential Cybersecurity Controls (ECC...
Read more →
How to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-9-3
Practical guide for SMBs to implement Essential Cybersecurity Controls (ECC...
Read more →
How to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-9-2
Practical guide for SMBs to implement Essential Cybersecurity Controls (ECC...
Read more →
How to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-9-1
Practical guide for SMBs to implement Essential Cybersecurity Controls (ECC...
Read more →
How to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-8-4
Practical guide for SMBs to implement Essential Cybersecurity Controls (ECC...
Read more →
How to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-8-3
Practical guide for SMBs to implement Essential Cybersecurity Controls (ECC...
Read more →
How to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-8-2
Practical guide for SMBs to implement Essential Cybersecurity Controls (ECC...
Read more →
How to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-8-1
Practical guide for SMBs to implement Essential Cybersecurity Controls (ECC...
Read more →
How to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-7-4
Practical guide for SMBs to implement Essential Cybersecurity Controls (ECC...
Read more →
How to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-7-3
Practical guide for SMBs to implement Essential Cybersecurity Controls (ECC...
Read more →
How to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-7-2
Practical guide for SMBs to implement Essential Cybersecurity Controls (ECC...
Read more →
How to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-7-1
Practical guide for SMBs to implement Essential Cybersecurity Controls (ECC...
Read more →
How to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-6-4
Practical guide for SMBs to implement Essential Cybersecurity Controls (ECC...
Read more →
How to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-6-3
Practical guide for SMBs to implement Essential Cybersecurity Controls (ECC...
Read more →
How to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-6-2
Practical guide for SMBs to implement Essential Cybersecurity Controls (ECC...
Read more →
How to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-6-1
Practical guide for SMBs to implement Essential Cybersecurity Controls (ECC...
Read more →
How to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-5-4
Practical guide for SMBs to implement Essential Cybersecurity Controls (ECC...
Read more →
How to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-5-3
Practical guide for SMBs to implement Essential Cybersecurity Controls (ECC...
Read more →
How to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-5-2
Practical guide for SMBs to implement Essential Cybersecurity Controls (ECC...
Read more →
How to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-5-1
Practical guide for SMBs to implement Essential Cybersecurity Controls (ECC...
Read more →
How to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-4-4
Practical guide for SMBs to implement Essential Cybersecurity Controls (ECC...
Read more →
How to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-4-3
Practical guide for SMBs to implement Essential Cybersecurity Controls (ECC...
Read more →
How to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-4-2
Practical guide for SMBs to implement Essential Cybersecurity Controls (ECC...
Read more →
How to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-4-1
Practical guide for SMBs to implement Essential Cybersecurity Controls (ECC...
Read more →
How to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-3-4
Practical guide for SMBs to implement Essential Cybersecurity Controls (ECC...
Read more →
How to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-3-3
Practical guide for SMBs to implement Essential Cybersecurity Controls (ECC...
Read more →
How to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-3-2
Practical guide for SMBs to implement Essential Cybersecurity Controls (ECC...
Read more →
How to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-3-1
Practical guide for SMBs to implement Essential Cybersecurity Controls (ECC...
Read more →
How to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-2-4
Practical guide for SMBs to implement Essential Cybersecurity Controls (ECC...
Read more →
How to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-2-3
Practical guide for SMBs to implement Essential Cybersecurity Controls (ECC...
Read more →
How to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-2-2
Practical guide for SMBs to implement Essential Cybersecurity Controls (ECC...
Read more →
How to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-2-1
Practical guide for SMBs to implement Essential Cybersecurity Controls (ECC...
Read more →
How to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-15-4
Practical guide for SMBs to implement Essential Cybersecurity Controls (ECC...
Read more →
How to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-15-3
Practical guide for SMBs to implement Essential Cybersecurity Controls (ECC...
Read more →
How to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-15-2
Practical guide for SMBs to implement Essential Cybersecurity Controls (ECC...
Read more →
How to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-15-1
Practical guide for SMBs to implement Essential Cybersecurity Controls (ECC...
Read more →
How to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-14-4
Practical guide for SMBs to implement Essential Cybersecurity Controls (ECC...
Read more →
How to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-14-3
Practical guide for SMBs to implement Essential Cybersecurity Controls (ECC...
Read more →
How to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-14-2
Practical guide for SMBs to implement Essential Cybersecurity Controls (ECC...
Read more →
How to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-14-1
Practical guide for SMBs to implement Essential Cybersecurity Controls (ECC...
Read more →
How to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-13-4
Practical guide for SMBs to implement Essential Cybersecurity Controls (ECC...
Read more →
How to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-13-3
Practical guide for SMBs to implement Essential Cybersecurity Controls (ECC...
Read more →
How to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-13-2
Practical guide for SMBs to implement Essential Cybersecurity Controls (ECC...
Read more →
How to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-13-1
Practical guide for SMBs to implement Essential Cybersecurity Controls (ECC...
Read more →
How to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-12-4
Practical guide for SMBs to implement Essential Cybersecurity Controls (ECC...
Read more →
How to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-12-3
Practical guide for SMBs to implement Essential Cybersecurity Controls (ECC...
Read more →
How to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-12-2
Practical guide for SMBs to implement Essential Cybersecurity Controls (ECC...
Read more →
How to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-12-1
Practical guide for SMBs to implement Essential Cybersecurity Controls (ECC...
Read more →
How to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-11-4
Practical guide for SMBs to implement Essential Cybersecurity Controls (ECC...
Read more →
How to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-11-3
Practical guide for SMBs to implement Essential Cybersecurity Controls (ECC...
Read more →
How to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-11-2
Practical guide for SMBs to implement Essential Cybersecurity Controls (ECC...
Read more →
How to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-11-1
Practical guide for SMBs to implement Essential Cybersecurity Controls (ECC...
Read more →
How to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-10-4
Practical guide for SMBs to implement Essential Cybersecurity Controls (ECC...
Read more →
How to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-10-3
Practical guide for SMBs to implement Essential Cybersecurity Controls (ECC...
Read more →
How to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-10-2
Practical guide for SMBs to implement Essential Cybersecurity Controls (ECC...
Read more →
How to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-10-1
Practical guide for SMBs to implement Essential Cybersecurity Controls (ECC...
Read more →
How to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-1-6
Practical guide for SMBs to implement Essential Cybersecurity Controls (ECC...
Read more →
How to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-1-5
Practical guide for SMBs to implement Essential Cybersecurity Controls (ECC...
Read more →
How to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-1-4
Practical guide for SMBs to implement Essential Cybersecurity Controls (ECC...
Read more →
How to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-1-3
Practical guide for SMBs to implement Essential Cybersecurity Controls (ECC...
Read more →
How to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-1-2
Practical guide for SMBs to implement Essential Cybersecurity Controls (ECC...
Read more →
How to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 2-1-1
Practical guide for SMBs to implement Essential Cybersecurity Controls (ECC...
Read more →
How to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-9-6
Practical guide for SMBs to implement Essential Cybersecurity Controls (ECC...
Read more →
How to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-9-5
Practical guide for SMBs to implement Essential Cybersecurity Controls (ECC...
Read more →
How to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-9-4
Practical guide for SMBs to implement Essential Cybersecurity Controls (ECC...
Read more →
How to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-9-3
Practical guide for SMBs to implement Essential Cybersecurity Controls (ECC...
Read more →
How to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-9-2
Practical guide for SMBs to implement Essential Cybersecurity Controls (ECC...
Read more →
How to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-9-1
Practical guide for SMBs to implement Essential Cybersecurity Controls (ECC...
Read more →
How to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-8-3
Practical guide for SMBs to implement Essential Cybersecurity Controls (ECC...
Read more →
How to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-8-2
Practical guide for SMBs to implement Essential Cybersecurity Controls (ECC...
Read more →
How to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-8-1
Practical guide for SMBs to implement Essential Cybersecurity Controls (ECC...
Read more →
How to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-7-2
Practical guide for SMBs to implement Essential Cybersecurity Controls (ECC...
Read more →
How to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-7-1
Practical guide for SMBs to implement Essential Cybersecurity Controls (ECC...
Read more →
How to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-6-4
Practical guide for SMBs to implement Essential Cybersecurity Controls (ECC...
Read more →
How to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-6-3
Practical guide for SMBs to implement Essential Cybersecurity Controls (ECC...
Read more →
How to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-6-2
Practical guide for SMBs to implement Essential Cybersecurity Controls (ECC...
Read more →
How to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-6-1
Practical guide for SMBs to implement Essential Cybersecurity Controls (ECC...
Read more →
How to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-5-4
Practical guide for SMBs to implement Essential Cybersecurity Controls (ECC...
Read more →
How to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-5-3
Practical guide for SMBs to implement Essential Cybersecurity Controls (ECC...
Read more →
How to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-5-2
Practical guide for SMBs to implement Essential Cybersecurity Controls (ECC...
Read more →
How to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-5-1
Practical guide for SMBs to implement Essential Cybersecurity Controls (ECC...
Read more →
How to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-4-2
Practical guide for SMBs to implement Essential Cybersecurity Controls (ECC...
Read more →
How to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-4-1
Practical guide for SMBs to implement Essential Cybersecurity Controls (ECC...
Read more →
How to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-3-4
Practical guide for SMBs to implement Essential Cybersecurity Controls (ECC...
Read more →
How to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-3-3
Practical guide for SMBs to implement Essential Cybersecurity Controls (ECC...
Read more →
How to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-3-2
Practical guide for SMBs to implement Essential Cybersecurity Controls (ECC...
Read more →
How to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-3-1
Practical guide for SMBs to implement Essential Cybersecurity Controls (ECC...
Read more →
How to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-2-3
Practical guide for SMBs to implement Essential Cybersecurity Controls (ECC...
Read more →
How to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-2-2
Practical guide for SMBs to implement Essential Cybersecurity Controls (ECC...
Read more →
How to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-2-1
Practical guide for SMBs to implement Essential Cybersecurity Controls (ECC...
Read more →
How to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-10-5
Practical guide for SMBs to implement Essential Cybersecurity Controls (ECC...
Read more →
How to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-10-4
Practical guide for SMBs to implement Essential Cybersecurity Controls (ECC...
Read more →
How to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-10-3
Practical guide for SMBs to implement Essential Cybersecurity Controls (ECC...
Read more →
How to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-10-2
Practical guide for SMBs to implement Essential Cybersecurity Controls (ECC...
Read more →
How to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-10-1
Practical guide for SMBs to implement Essential Cybersecurity Controls (ECC...
Read more →
How to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-1-3
Practical guide for SMBs to implement Essential Cybersecurity Controls (ECC...
Read more →
How to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-1-2
Practical guide for SMBs to implement Essential Cybersecurity Controls (ECC...
Read more →
How to Meet Essential Cybersecurity Controls (ECC – 2 : 2024) - Control - 1-1-1
Practical guide for SMBs to implement Essential Cybersecurity Controls (ECC...
Read more →
How to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - SI.L2-3.14.7
Practical guide for SMBs to implement NIST SP 800-171 REV.2...
Read more →
How to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - SI.L2-3.14.6
Practical guide for SMBs to implement NIST SP 800-171 REV.2...
Read more →
How to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - SI.L2-3.14.5
Practical guide for SMBs to implement NIST SP 800-171 REV.2...
Read more →
How to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - SI.L2-3.14.4
Practical guide for SMBs to implement NIST SP 800-171 REV.2...
Read more →
How to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - SI.L2-3.14.3
Practical guide for SMBs to implement NIST SP 800-171 REV.2...
Read more →
How to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - SI.L2-3.14.2
Practical guide for SMBs to implement NIST SP 800-171 REV.2...
Read more →
How to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - SI.L2-3.14.1
Practical guide for SMBs to implement NIST SP 800-171 REV.2...
Read more →
How to Meet FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SI.L1-B.1.XIV
Practical guide for SMBs to implement FAR 52.204-21 / CMMC...
Read more →
How to Meet FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SI.L1-B.1.XIII
Practical guide for SMBs to implement FAR 52.204-21 / CMMC...
Read more →
How to Meet FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SI.L1-B.1.XII
Practical guide for SMBs to implement FAR 52.204-21 / CMMC...
Read more →
How to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - SC.L2-3.13.9
Practical guide for SMBs to implement NIST SP 800-171 REV.2...
Read more →
How to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - SC.L2-3.13.8
Practical guide for SMBs to implement NIST SP 800-171 REV.2...
Read more →
How to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - SC.L2-3.13.7
Practical guide for SMBs to implement NIST SP 800-171 REV.2...
Read more →
How to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - SC.L2-3.13.6
Practical guide for SMBs to implement NIST SP 800-171 REV.2...
Read more →
How to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - SC.L2-3.13.5
Practical guide for SMBs to implement NIST SP 800-171 REV.2...
Read more →
How to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - SC.L2-3.13.4
Practical guide for SMBs to implement NIST SP 800-171 REV.2...
Read more →
How to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - SC.L2-3.13.3
Practical guide for SMBs to implement NIST SP 800-171 REV.2...
Read more →
How to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - SC.L2-3.13.2
Practical guide for SMBs to implement NIST SP 800-171 REV.2...
Read more →
How to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - SC.L2-3.13.16
Practical guide for SMBs to implement NIST SP 800-171 REV.2...
Read more →
How to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - SC.L2-3.13.15
Practical guide for SMBs to implement NIST SP 800-171 REV.2...
Read more →
How to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - SC.L2-3.13.14
Practical guide for SMBs to implement NIST SP 800-171 REV.2...
Read more →
How to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - SC.L2-3.13.12
Practical guide for SMBs to implement NIST SP 800-171 REV.2...
Read more →
How to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - SC.L2-3.13.11
Practical guide for SMBs to implement NIST SP 800-171 REV.2...
Read more →
How to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - SC.L2-3.13.10
Practical guide for SMBs to implement NIST SP 800-171 REV.2...
Read more →
How to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - SC.L2-3.13.1
Practical guide for SMBs to implement NIST SP 800-171 REV.2...
Read more →
How to Meet FAR 52.204-21 / CMMC 2.0 Level 1 - Control - SC.L1-B.1.XI
Practical guide for SMBs to implement FAR 52.204-21 / CMMC...
Read more →
How to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - RA.L2-3.11.3
Practical guide for SMBs to implement NIST SP 800-171 REV.2...
Read more →
How to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - RA.L2-3.11.2
Practical guide for SMBs to implement NIST SP 800-171 REV.2...
Read more →
How to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - RA.L2-3.11.1
Practical guide for SMBs to implement NIST SP 800-171 REV.2...
Read more →
How to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - PS.L2-3.9.2
Practical guide for SMBs to implement NIST SP 800-171 REV.2...
Read more →
How to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - PS.L2-3.9.1
Practical guide for SMBs to implement NIST SP 800-171 REV.2...
Read more →
How to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - PE.L2-3.10.6
Practical guide for SMBs to implement NIST SP 800-171 REV.2...
Read more →
How to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - PE.L2-3.10.5
Practical guide for SMBs to implement NIST SP 800-171 REV.2...
Read more →
How to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - PE.L2-3.10.4
Practical guide for SMBs to implement NIST SP 800-171 REV.2...
Read more →
How to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - PE.L2-3.10.2
Practical guide for SMBs to implement NIST SP 800-171 REV.2...
Read more →
How to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - PE.L2-3.10.1
Practical guide for SMBs to implement NIST SP 800-171 REV.2...
Read more →
How to Meet FAR 52.204-21 / CMMC 2.0 Level 1 - Control - PE.L1-B.1.VIII
Practical guide for SMBs to implement FAR 52.204-21 / CMMC...
Read more →
How to Meet FAR 52.204-21 / CMMC 2.0 Level 1 - Control - PE.L1-B.1.IX
Practical guide for SMBs to implement FAR 52.204-21 / CMMC...
Read more →
How to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - MP.L2-3.8.9
Practical guide for SMBs to implement NIST SP 800-171 REV.2...
Read more →
How to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - MP.L2-3.8.8
Practical guide for SMBs to implement NIST SP 800-171 REV.2...
Read more →
How to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - MP.L2-3.8.7
Practical guide for SMBs to implement NIST SP 800-171 REV.2...
Read more →
How to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - MP.L2-3.8.6
Practical guide for SMBs to implement NIST SP 800-171 REV.2...
Read more →
How to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - MP.L2-3.8.5
Practical guide for SMBs to implement NIST SP 800-171 REV.2...
Read more →
How to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - MP.L2-3.8.4
Practical guide for SMBs to implement NIST SP 800-171 REV.2...
Read more →
How to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - MP.L2-3.8.3
Practical guide for SMBs to implement NIST SP 800-171 REV.2...
Read more →
How to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - MP.L2-3.8.2
Practical guide for SMBs to implement NIST SP 800-171 REV.2...
Read more →
How to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - MP.L2-3.8.1
Practical guide for SMBs to implement NIST SP 800-171 REV.2...
Read more →
How to Meet FAR 52.204-21 / CMMC 2.0 Level 1 - Control - MP.L1-B.1.VII
Practical guide for SMBs to implement FAR 52.204-21 / CMMC...
Read more →
How to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - MA.L2-3.7.6
Practical guide for SMBs to implement NIST SP 800-171 REV.2...
Read more →
How to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - MA.L2-3.7.5
Practical guide for SMBs to implement NIST SP 800-171 REV.2...
Read more →
How to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - MA.L2-3.7.4
Practical guide for SMBs to implement NIST SP 800-171 REV.2...
Read more →
How to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - MA.L2-3.7.3
Practical guide for SMBs to implement NIST SP 800-171 REV.2...
Read more →
How to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - MA.L2-3.7.2
Practical guide for SMBs to implement NIST SP 800-171 REV.2...
Read more →
How to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - MA.L2-3.7.1
Practical guide for SMBs to implement NIST SP 800-171 REV.2...
Read more →
How to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - IR.L2-3.6.3
Practical guide for SMBs to implement NIST SP 800-171 REV.2...
Read more →
How to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - IR.L2-3.6.2
Practical guide for SMBs to implement NIST SP 800-171 REV.2...
Read more →
How to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - IR.L2-3.6.1
Practical guide for SMBs to implement NIST SP 800-171 REV.2...
Read more →
How to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - IA.L2-3.5.9
Practical guide for SMBs to implement NIST SP 800-171 REV.2...
Read more →
How to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - IA.L2-3.5.8
Practical guide for SMBs to implement NIST SP 800-171 REV.2...
Read more →
How to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - IA.L2-3.5.7
Practical guide for SMBs to implement NIST SP 800-171 REV.2...
Read more →
How to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - IA.L2-3.5.6
Practical guide for SMBs to implement NIST SP 800-171 REV.2...
Read more →
How to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - IA.L2-3.5.5
Practical guide for SMBs to implement NIST SP 800-171 REV.2...
Read more →
How to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - IA.L2-3.5.4
Practical guide for SMBs to implement NIST SP 800-171 REV.2...
Read more →
How to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - IA.L2-3.5.3
Practical guide for SMBs to implement NIST SP 800-171 REV.2...
Read more →
How to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - IA.L2-3.5.2
Practical guide for SMBs to implement NIST SP 800-171 REV.2...
Read more →
How to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - IA.L2-3.5.11
Practical guide for SMBs to implement NIST SP 800-171 REV.2...
Read more →
How to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - IA.L2-3.5.10
Practical guide for SMBs to implement NIST SP 800-171 REV.2...
Read more →
How to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - IA.L2-3.5.1
Practical guide for SMBs to implement NIST SP 800-171 REV.2...
Read more →
How to Meet FAR 52.204-21 / CMMC 2.0 Level 1 - Control - IA.L1-B.1.VI
Practical guide for SMBs to implement FAR 52.204-21 / CMMC...
Read more →
How to Meet FAR 52.204-21 / CMMC 2.0 Level 1 - Control - IA.L1-B.1.V
Practical guide for SMBs to implement FAR 52.204-21 / CMMC...
Read more →
How to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - CM.L2-3.4.9
Practical guide for SMBs to implement NIST SP 800-171 REV.2...
Read more →
How to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - CM.L2-3.4.8
Practical guide for SMBs to implement NIST SP 800-171 REV.2...
Read more →
How to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - CM.L2-3.4.7
Practical guide for SMBs to implement NIST SP 800-171 REV.2...
Read more →
How to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - CM.L2-3.4.6
Practical guide for SMBs to implement NIST SP 800-171 REV.2...
Read more →
How to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - CM.L2-3.4.5
Practical guide for SMBs to implement NIST SP 800-171 REV.2...
Read more →
How to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - CM.L2-3.4.4
Practical guide for SMBs to implement NIST SP 800-171 REV.2...
Read more →
How to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - CM.L2-3.4.3
Practical guide for SMBs to implement NIST SP 800-171 REV.2...
Read more →
How to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - CM.L2-3.4.2
Practical guide for SMBs to implement NIST SP 800-171 REV.2...
Read more →
How to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - CM.L2-3.4.1
Practical guide for SMBs to implement NIST SP 800-171 REV.2...
Read more →
How to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - CA.L2-3.12.4
Practical guide for SMBs to implement NIST SP 800-171 REV.2...
Read more →
How to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - CA.L2-3.12.3
Practical guide for SMBs to implement NIST SP 800-171 REV.2...
Read more →
How to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - CA.L2-3.12.2
Practical guide for SMBs to implement NIST SP 800-171 REV.2...
Read more →
How to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - CA.L2-3.12.1
Practical guide for SMBs to implement NIST SP 800-171 REV.2...
Read more →
How to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AU.L2-3.3.9
Practical guide for SMBs to implement NIST SP 800-171 REV.2...
Read more →
How to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AU.L2-3.3.8
Practical guide for SMBs to implement NIST SP 800-171 REV.2...
Read more →
How to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AU.L2-3.3.7
Practical guide for SMBs to implement NIST SP 800-171 REV.2...
Read more →
How to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AU.L2-3.3.6
Practical guide for SMBs to implement NIST SP 800-171 REV.2...
Read more →
How to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AU.L2-3.3.5
Practical guide for SMBs to implement NIST SP 800-171 REV.2...
Read more →
How to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AU.L2-3.3.4
Practical guide for SMBs to implement NIST SP 800-171 REV.2...
Read more →
How to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AU.L2-3.3.3
Practical guide for SMBs to implement NIST SP 800-171 REV.2...
Read more →
How to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AU.L2-3.3.2
Practical guide for SMBs to implement NIST SP 800-171 REV.2...
Read more →
How to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AU.L2-3.3.1
Practical guide for SMBs to implement NIST SP 800-171 REV.2...
Read more →
How to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AT.L2-3.2.3
Practical guide for SMBs to implement NIST SP 800-171 REV.2...
Read more →
How to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AT.L2-3.2.2
Practical guide for SMBs to implement NIST SP 800-171 REV.2...
Read more →
How to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AT.L2-3.2.1
Practical guide for SMBs to implement NIST SP 800-171 REV.2...
Read more →
How to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AC.L2-3.1.22
Practical guide for SMBs to implement NIST SP 800-171 REV.2...
Read more →
How to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AC.L2-3.1.21
Practical guide for SMBs to implement NIST SP 800-171 REV.2...
Read more →
How to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AC.L2-3.1.20
Practical guide for SMBs to implement NIST SP 800-171 REV.2...
Read more →
How to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AC.L2-3.1.19
Practical guide for SMBs to implement NIST SP 800-171 REV.2...
Read more →
How to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AC.L2-3.1.13
Practical guide for SMBs to implement NIST SP 800-171 REV.2...
Read more →
How to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 - Control - AC.L2-3.1.12
Practical guide for SMBs to implement NIST SP 800-171 REV.2...
Read more →
How to Meet FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.IV
Practical guide for SMBs to implement FAR 52.204-21 / CMMC...
Read more →
How to Meet FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.III
Practical guide for SMBs to implement FAR 52.204-21 / CMMC...
Read more →
How to Meet FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.II
Practical guide for SMBs to implement FAR 52.204-21 / CMMC...
Read more →
How to Meet FAR 52.204-21 / CMMC 2.0 Level 1 - Control - AC.L1-B.1.I
Practical guide for SMBs to implement FAR 52.204-21 / CMMC...
Read more →

How to Implement HIPAA Facility Access Controls (164.310(a)(1)): A Step-by-Step Compliance Guide
A practical, step-by-step guide to implementing HIPAA Facility Access Controls...
Read more →
How to Draft ISO 27001-Compliant Confidentiality and NDA Templates (Control 6.6 / Code 282)
Step-by-step guidance to create Compliance Framework-aligned confidentiality and NDA templates...
Read more →
How to Create Audit-Ready HIPAA 164.316(a) Policies and Procedures: Templates, Documentation, and Change Control
Step-by-step guidance for building audit-ready HIPAA 164.316(a) policies and procedures...
Read more →
How to Create and Maintain Written HIPAA Policies and Procedures (164.316(b)(1)) — Practical Implementation Checklist
Step-by-step guidance for creating, documenting, and maintaining HIPAA-compliant written policies...
Read more →
How to Create an Audit-Ready Log Review Policy for CMMC - AU.L2-3.3.3 with Templates and Checklists
Step-by-step guidance to build an audit-ready log review policy for...
Read more →
How to Configure Multi‑Factor Authentication and Account Controls to Satisfy FAR 52.204-21
Practical, step‑by‑step guidance for small contractors to configure multi‑factor authentication...
Read more →
How to Build an ISO 27001-Compliant Source Code Access Policy: Templates and Implementation Steps
Step-by-step guidance and ready-to-use templates to build a source code...
Read more →
How to Achieve ISO 27001 Compliance for Policies in 30 Days: Rapid Implementation Checklist and Sample Policy Pack
Practical 30-day plan to build ISO 27001-aligned policies, a sample...
Read more →
CMMC Phased Rollout Begins: What Defense Contractors Need to Know Now
The CMMC phased implementation has officially started. Learn critical dates,...
Read more →

CMMC Level 1: How to Implement Visitor Escort and Monitoring to Meet PE.L1-B.1.IX
Learn exactly how small businesses can implement visitor escort and...
Read more →
Quarterly Access Reviews That Work: Verifying Authorized Users and Devices for AC.L1-B.1.I (CMMC Level 1)
Learn how to run no-nonsense quarterly access reviews to verify...
Read more →
How to Identify Role-Specific Risks and Turn Them into Targeted Modules for NIST 800-171 3.2.1
Learn how to map role-specific risks into targeted training modules...
Read more →










How to Meet AC.L2-3.1.7
Practical guide for SMBs to implement AC.L2-3.1.7 using Microsoft 365...
Read more →
How to Meet AC.L2-3.1.6
Practical guide for SMBs to implement AC.L2-3.1.6 using Microsoft 365...
Read more →
How to Meet AC.L2-3.1.5
Practical guide for SMBs to implement AC.L2-3.1.5 using Microsoft 365...
Read more →
How to Meet AC.L2-3.1.4
Practical guide for SMBs to implement AC.L2-3.1.4 using Microsoft 365...
Read more →
How to Meet AC.L2-3.1.3
Practical guide for SMBs to implement AC.L2-3.1.3 using Microsoft 365...
Read more →
How to Meet AC.L2-3.1.2
Practical guide for SMBs to implement AC.L2-3.1.2 using Microsoft 365...
Read more →
How to Meet AC.L2-3.1.1
Practical guide for SMBs to implement AC.L2-3.1.1 using Microsoft 365...
Read more →
How to Configure SSO and MFA for AC.L2-3.1.1 in Microsoft Entra ID (Azure AD), Okta, and Google Workspace
Learn how to meet AC.L2-3.1.1—limit system access to authorized users,...
Read more →
Configure IAM (SSO, MFA, RBAC) to Limit Access to Authorized Users for AC.L2-3.1.1 Compliance
Learn how to configure SSO, MFA, and RBAC to meet...
Read more →
From Reception to Audit: Real-World Implementation Tips for Escorting Visitors under NIST SP 800-171
Step-by-step, practical guidance for implementing visitor escorting controls to meet...
Read more →
Meeting CMMC Level 1 Requirement | AC.L1-B.1.III – EXTERNAL CONNECTIONS [FCI DATA]
How Small Businesses Can Meet It.
Read more →
Meeting CMMC Level 1 Access Control - AC.L1-B.1.I – Limiting System Access to Authorized Users, Processes, and Devices
Learn how to meet CMMC Level 1 Access Control -...
Read more →
Meeting CMMC AC.L2-3.1.4 - Separation of Duties
Learn how to meet CMMC AC.L2-3.1.4 - Separation of Duties...
Read more →
14+ Security Settings to Boost WhatsApp Privacy
Configure these settings to combat stalkers, spammers, and everyone else...
Read more →
How to Get Your Smartphone Ready for the Next Disaster
If configured correctly, during a disaster a smartphone can be...
Read more →
DeepSeek AI Database Leaked Secret Keys & Over 1 Million Log Lines
DeepSeek AI database security flaw uncovers confidential keys, chat records,...
Read more →
Russian hacker group Star Blizzard launch spear phishing attack via WhatsApp
The Russian hacker group Star Blizzard posed as U.S. government...
Read more →
Biden executive order imposes new cybersecurity standards for companies that do business with the U.S. government
The Biden administration aims to enhance digital security for both...
Read more →
How to Perform a CMMC Level 1 Self-Assessment
Learn how to perform a CMMC Level 1 Self-Assessment
Read more →
Telegram Hands Over Thousands Of Users Data To US Law Enforcement
The arrest of the Telegram founder seems to have caused...
Read more →
Volkswagen data leak exposes location of 800,000 electric car drivers
A Volkswagen subsidiary data breach has exposed the location and...
Read more →
US Army soldier arrested for hacking President Donald Trump’s calls
US Army soldier shared on the Telegram messaging service that...
Read more →
US Treasury documents stolen by Chinese Hackers in Major Incident
Hackers supported by the Chinese government successfully penetrated the Treasury...
Read more →
NIST SP 800-171 Rev 3 or Rev 2? Which is Required in 2024?
What are the new NIST SP 800-171 requiremets? Do they...
Read more →
Ensure that between two and four global admins are designated - Microsoft 365
Designate between two and four global administrators to ensure effective...
Read more →
Establish two emergency access accounts for critical situations, ensuring continuity and security in your system - Microsoft 365
Secure your Microsoft 365 environment by ensuring administrative accounts are...
Read more →
Ensure that administrative accounts are distinct and solely cloud-based - Microsoft 365
Secure your Microsoft 365 environment by ensuring administrative accounts are...
Read more →
4 Business Benefits of Implementing ISO 27001
ISO 27001 is well known in the information security field....
Read more →
How To Conduct An ISO 27001 Risk Assessment
Implementing ISO 27001 involves conducting thorough information security risk assessments,...
Read more →

BYOD - Do employees care about data security?
According to a survey conducted by Kaspersky Labs, only 10%...
Read more →
Oakwood Hospital Worker Fired For Facebook Comments in HIPAA Violation
Michigan healthcare provider, Oakwood Healthcare, Inc., has verified that an...
Read more →
HIPAA for Managed Service Providers
Understanding HIPAA is crucial for Managed Service Providers offering services...
Read more →
4 Stages of Containing a Data Breach
Data breaches have become increasingly common, leading many organizations to...
Read more →
ISO 27001 Asset Based Risk Assessment
For those who are new to information security risk assessments,...
Read more →

5 Reasons Why Your Business Needs a Pen Test
Penetration testing is a highly effective method for evaluating your...
Read more →
ISO 27001 Internal Audit
Accelerating the ISO 27001 audit process can be facilitated by...
Read more →
ISO 27001 and Third Party Vendors
Organizations pursuing ISO 27001 certification but rely on third-party vendors...
Read more →

HIPAA Password Sharing
Password sharing in healthcare may contribute to productivity in certain...
Read more →
Evidence Remotley Wiped From Police Station
Placing phones in a microwave prevents hacking?
Read more →
How ISO 27001 Can Protect Homeland Security
ISO 27001 can address the US Department of Homeland Security’s...
Read more →


Why ISO 27001 Information Classification Is Important
The classification of information plays a crucial role in every...
Read more →
ISO 27001 Benefits for Small Organizations
Many small organizations believe that implementing ISO 27001 is either...
Read more →

HIPAA Compliance for Medical Centers
Medical centers must comply with the Administrative Simplification standards of...
Read more →
HIPAA Compliance In Urgent Care
The correlation between HIPAA compliance in urgent care is not...
Read more →
HIPAA Compliance Officer
To become HIPAA compliant, a Covered Entity or Business Associate...
Read more →
HIPAA Email Compliance
Covered entities and business associates are obligated to implement various...
Read more →
HIPAA Compliant Hosting
In order to safeguard sensitive patient information stored in the...
Read more →
HIPAA Text message (SMS) Regulations
Text message (SMS) regulations under HIPAA outline the specific circumstances...
Read more →

HIPAA Training Requirements
The HIPAA training requirements lean more towards offering guidance rather...
Read more →

HIPAA and HITECH
Covered Entities and Business Associates must familiarize themselves with the...
Read more →
HIPAA Password Sharing Policy
A Password Sharing Policy that is compliant with HIPAA should...
Read more →
HIPAA Compliance for Medical Records
Safeguarding the security of medical records are required to meet...
Read more →
HIPAA Risk Assessment
Performing a HIPAA risk assessment is crucial for ensuring compliance...
Read more →
HIPAA Guide for Dentists
The master guide for HIPAA compliance for all dentists, regardless...
Read more →
HIPAA Encryption Requirements
Everything you need to know about HIPAA encryption requirements
Read more →

HIPAA Telemedicine
The comprehensive HIPAA guide for telemedicine and the proper methods...
Read more →
HIPAA Social Media Policy
Healthcare organizations must prioritize HIPAA compliance when it comes to...
Read more →
Healthcare Cybersecurity
An In-depth Look at Cybersecurity in the US Healthcare Industry...
Read more →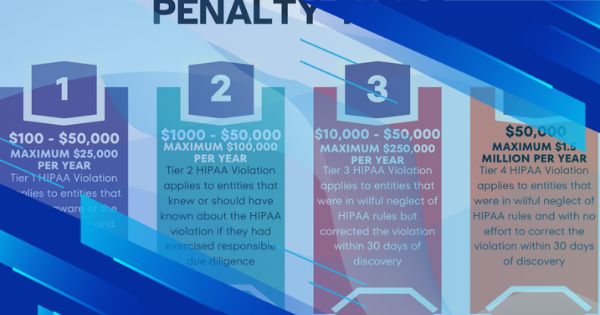
UnitedHealthcare Pays Settlement for HIPAA violation over Patient Medical Records Request
UnitedHealthcare Settles for $80,000
Read more →
Incident Response Testing for NIST SP 800-171 & CMMC 2.0
Use our incident response tests to meet requirement 3.6.3.
Read more →
Control and Manage Physical Access Devices – NIST SP 800-171 & CMMC 2.0
How do you meet the security requirement 3.10.5 “Control and...
Read more →
Is Your Microsoft 365 Tenant Configured for NIST SP 800-171 & CMMC Compliance?
More than likely, you haven’t configured your Microsoft 365 tenant...
Read more →
Flying to the Cloud – IT & Security Transformation
Learn how we configured a client's Microsoft 365 environment to...
Read more →
Maintaining Systems and Compliance
Learn how our Azure AD services can streamline and secure...
Read more →
Data Mining and Extracting Historical Data
How we helped a regional logistics company access historical data...
Read more →
Email marketing automation platform = six figure increase in sales
How we helped a small business increase their sales by...
Read more →
Certification after Certification
Learn how our policies and procedures service enabled a customer...
Read more →
Small Business, Big Compliance - NIST SP 800-171
Learn how we helped a DoD contractor meet DFARS NIST...
Read more →
The Physics Behind Microsoft 365 Security
Learn how we helped a DoD contractor meet compliance requirements...
Read more →
Security Configuration Settings for NIST SP 800-171 & CMMC Compliance
Learn how to meet your configuration management requirements for NIST...
Read more →
How to Meet NIST SP 800-171 & CMMC Mobile Code Requirements
Learn how to meet your mobile code protection requirements for...
Read more →
Looking for an Information Security Framework? Use this.
Using a security frame helps an organization establish and meet...
Read more →
Guide to NIST SP 800-171 & CMMC 2.0 Security Control Domains
Learn the objectives of each security control family.
Read more →
Using BitLocker Encryption for NIST SP 800-171 & CMMC 2.0 Compliance
Learn how to use BitLocker encryption to meet NIST SP...
Read more →
Guide to Insider Threat Awareness Training for NIST SP 800-171 & CMMC
Learn how to meet insider threat training requirements for NIST...
Read more →
Guide to Split Tunneling (3.13.7) for NIST SP 800-171 and CMMC
What is split tunneling and how does it relate to...
Read more →
The Ultimate Guide to Privacy and Security Notices for NIST 800-171 and CMMC
What is a privacy and security notice? Where does it...
Read more →
The Ultimate Guide to Incident Response for NIST 800-171 and CMMC 2.0
How do you meet NIST 800-171 and CMMC 2.0 incident...
Read more →
The Ultimate Guide to USB Compliance for CMMC and NIST 800-171
Can I still use USB storage if we implement NIST...
Read more →
Cyberwarfare vs Cyber Espionage, What is the Difference?
Cyber buzzwords always get thrown around causing confusion for readers....
Read more →
Top 5 In Demand Cybersecurity Certifications
Which of these top 5 cybersecurity certifications do you have?...
Read more →
Data Classification Labels for Your Small Business
Having trouble with data classification in your small business? Here...
Read more →
10 Ways to Improve Your Small Business's Cybersecurity
Perform these tasks to greatly improve cybersecurity at a small...
Read more →
NIST SP 800-171 Personnel Security Requirements
Learn everything you need to know about your Personnel Security...
Read more →
What is a System Security Officer, System Owner, and Information Owner?
Learn what these essential roles are for your system security...
Read more →
NIST SP 800-171 Physical Security Requirements Explained
Learn how to meet your NIST SP 800-171 and CMMC...
Read more →
Vulnerability Scanning Requirements for NIST SP 800-171
Learn how to meet your NIST SP 800-171 and CMMC...
Read more →
How I Passed the CISSP Exam on My First Try
Follow my tips on how to pass the CISSP exam....
Read more →
NIST SP 800-171 Least Privilege Requirements
What does “Least Privilege” mean and what are the associated...
Read more →
NIST SP 800-171 Separation of Duties Requirements
What does “Separation of Duties” mean and what are the...
Read more →
How the Time on your Computer Affects NIST SP 800-171 Compliance
There are many intricate requirements related to NIST SP 800-171...
Read more →
System Security Plans Explained
To meet NIST SP 800-171 requirements you must create and...
Read more →
NIST SP 800-171 CUI Sanitization and Destruction Methods
Learn how to meet your NIST SP 800-171 media sanitization...
Read more →
What Documentation Should You Have for NIST SP 800-171?
A cybersecurity program isn’t really a formal program until it...
Read more →
What are the NIST SP 800-171 Password Requirements?
The password requirements for NIST SP 800-171 are not very...
Read more →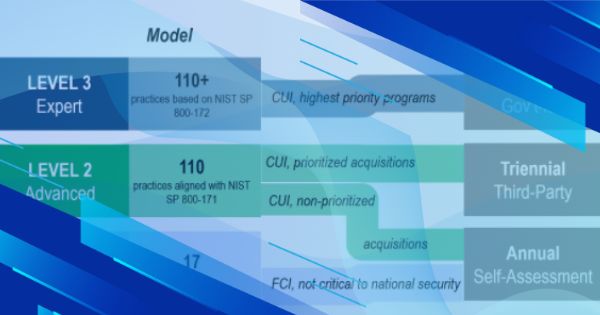
What CMMC 2.0 Means for your Business
CMMC 2.0 has streamlined CMMC and brought it in line...
Read more →
Easy to Use Incident Response Checklist
Organizations should have standardized procedures for responding to incidents, use...
Read more →
How to Protect the Confidentiality of CUI
Learn how to protect the confidentiality of CUI using physical...
Read more →
Using DISA STIGs to Meet NIST SP 800-171 and CMMC Requirements
Learn how using DISA STIGs can help you meet your...
Read more →
How to Create a Hardware and Software Inventory for your System Security Plan
Every system security plan should include or reference a hardware...
Read more →
How to Meet Requirements 3.6.3 and IR.3.099: Test the organizational incident response capability.
Learn how to “Test the organizational incident response capability” to...
Read more →
What are NIST SP 800-171 and CMMC Malicious Code Protection Requirements?
In this post, we will discuss how to meet your...
Read more →
How to Create a Plan of Action & Milestones for NIST SP 800-171
A plan of action and milestones document is critical to...
Read more →
What is a Collaborative Computing Device?
Learn what a collaborative computing device is and how to...
Read more →
What is a Basic (Contractor Self-Assessment) NIST SP 800-171 DoD Assessment?
Learn what a basic NIST SP 800-171 DoD assessment is...
Read more →
How to Meet NIST SP 800-171 & CMMC Personnel Security Requirements
To meet CMMC and NIST SP 800-171 requirements, organizations must...
Read more →
How to Meet NIST SP 800-171 & CMMC Physical Protection Requirements
To meet CMMC and NIST SP 800-171 requirements, organizations must...
Read more →
Meeting Personnel Training Requirements for NIST SP 800-171 & CMMC Using Free Resources
The NIST 800-171 and CMMC security frameworks both have an...
Read more →
What is a Summary Level Score (SPRS)? + How to Calculate it
Read more →
Meeting AC.1.001 and 3.1.1 Security Control Requirements for CMMC & NIST SP 800-171
Read more →
How to Control and Monitor Mobile Code for NIST SP 800-171 & CMMC
Read more →
NIST SP 800-171: How to Perform a Self-Assessment
Read more →
Digital Bug Out Bag Essentials
Are you preparing for a natural disaster, civil unrest, nuclear...
Read more →
Cybersecurity Border Crossing and Travel Tips
When traveling or crossing through border controls there are a...
Read more →
Easy to Follow Online Privacy Guide
Learn how to clean up your online presence and stay...
Read more →
Data Classification 101 Guide
Classifying and labeling data is a critical part of any...
Read more →
Is it Cybersecurity or Cyber Security? How do you spell it?
Is cybersecurity spelled as one word or two? The answer...
Read more →
The Principle of Least Functionality, Simplicity is the Ultimate Sophistication
Employing the principle of least functionality is critical for organizations...
Read more →.png)
Information Security or Cyber Security? Which term should we use?
The term cyber security is often heard in the media,...
Read more →
The History of Hacking: 1903 the world's first Hack
In 1903 the world’s first hacking incident occurred, marking the...
Read more →
CMMC: Policies and Procedures Contractors Should Have
Companies with cybersecurity maturity model certification (CMMC) level two or...
Read more →
5 Open-source Cybersecurity Tools Every Company Needs
Using free and open-source software (FOSS) to meet your cybersecurity...
Read more →
6 Cybersecurity Risks Associated with Working From Home
Although an operational necessity, allowing employees to work from home...
Read more →
CMMC Portable/Removable Storage Security Requirements
What are the cybersecurity maturity model certification (CMMC) requirements for...
Read more →
Laptops given to British school kids came preloaded with malware
Laptops supplied to British schools by the Department for Education...
Read more →
12 Things You Need to Know About the Signal Messenger App
The Signal Messenger App is rising in popularity. Here are...
Read more →
5 Simple Ways to Improve Your Organization’s Cybersecurity
Tackling cybersecurity challenges is no walk in the park. However,...
Read more →
CMMC FAQ
Cybersecurity Maturity Model Certification (CMMC) frequently asked questions (FAQ)
Read more →
Signs an Employee Might Be an Insider Threat
More than 34% of businesses around the globe are affected...
Read more →
Why Ad Blockers Should Be Part of Your Endpoint Security Strategy
Malvertising is a serious threat that can often be overlooked....
Read more →
How to Protect Printers From Cyber Threats
We are used to locking down workstations and servers however...
Read more →
How Going Paperless Improves Cybersecurity
Want to help save the environment and improve your information...
Read more →
4 Reasons Small Business Doesn't Invest in Cybersecurity
Small businesses are often the target of cyber attacks. Why...
Read more →
3 Free Ways to Boost Cybersecurity Awareness
Training employees on cybersecurity practices and reminding them of security...
Read more →
Should You Punish Employees for Cybersecurity Violations?
Everyone can agree that breaking the rules should have its...
Read more →
Physical Security Measures are an Important Part of Cybersecurity
Our data may be stored digitally but fundamentally it is...
Read more →
What is Split Tunneling? Should You Allow It?
What is split tunneling as it relates to virtual private...
Read more →

CMMC Privacy & Security Notice Requirements
Learn which companies need to deploy system use notifications, what...
Read more →
What You Need to Know About the Cybersecurity Maturity Model Certification (CMMC)
There are important new updates to the DoD Cybersecurity Maturity...
Read more →
What are Your CMMC Antivirus Requirements?
Companies with CMMC requirements will need to deploy antivirus software...
Read more →
5 Free Apps & Services To Protect Your Privacy
Tired of Silicon Valley and the Government tracking your every...
Read more →
Practical Home Cybersecurity Tips
Use these tips to protect your home from cyber threats....
Read more →
How Often Should Users Be Required to Reset Their Password?
Does requiring users to reset their passwords every few months...
Read more →
What is the difference between "Separation of Duties" and "Least Privilege"
Separating the duties of employees and implementing the principle of...
Read more →
What is the Difference Between Data Privacy and Security?
Privacy and security are related but what is the difference?...
Read more →
FALSE: Hiding your WiFi SSID is more secure than not, and here's why:
Does hiding your SSID improve security?
Read more →

How to Create A Business Impact Analysis (BIA)
We discuss business impact analysis definition, steps, and provide templates...
Read more →
How to Choose an Enterprise Grade Multi-factor Authentication (MFA) Solution
Knowing how to choose the right multi-factor authentication (MFA) solution...
Read more →
Cheat Sheets Every Cybersecurity Pro Needs
Check out these useful cheat sheets for cybersecurity tools like...
Read more →
What are keyloggers and what guidance does the CMMC provide
A keylogger is a device or application that is used...
Read more →
What is an Incident Response Plan? What Should it Contain?
The occurrence of a cybersecurity incident isn’t a matter of...
Read more →
What information should you collect when a cybersecurity incident occurs? What are your CMMC Incident Response Requirements?
It is important for organization’s to collect information on cybersecurity...
Read more →
What is the NIST Privacy Framework?
The NIST Privacy Framework provides organizations with a tool to...
Read more →
Use This Simple Trick to Prevent 94% of Windows Vulnerabilities
By revoking administrator rights from a Windows system you can...
Read more →
How a Gap Analysis Can Help Your Company Prepare for CMMC
By conducting a third party CMMC gap analysis your company...
Read more →
14 year old boy takes down Amazon, CNN, Yahoo!, and eBay. Also CMMC and DDoS Attacks...
A 14 year old boy took down Amazon, CNN, Yahoo!,...
Read more →
What is Dumpster Diving and how does it relate to the cybersecurity maturity model certification (CMMC)?
In the world of cybersecurity, dumpster diving is a technique...
Read more →
CMMC - What is CUI, CDI, CTI, and FCI
What is CUI, CDI, CTI, and FCI? CMMC (Cybersecurity Maturity...
Read more →
What is Encryption and how is Encryption used in the CMMC (Cybersecurity Maturity Model Certification)?
Encryption is the process of encoding information so that it...
Read more →
What is a Firewall? How do they relate to the Cybersecurity Maturity Model Certification (CMMC)?
A firewall is a network security system that monitors and...
Read more →

What's the Difference Between SSL and TLS?
In short, SSL is the now deprecated predecessor of TLS....
Read more →

Practicing Good OpSec on Social Media
Social media can help you connect with friends and family,...
Read more →
Building a Patch and Vulnerability Management Program
A patch and vulnerability management program is one of the...
Read more →
Common CMMC Misconceptions
Many defense contractors are confused about CMMC. Here are two...
Read more →
Why Your Company Needs to Block Browser Extensions
Browser extensions can increase productivity, however, left unmanaged they can...
Read more →

How to Provide Free Cybersecurity Training to Your Employees
Your employees can receive some of the same training as...
Read more →
How to Protect Your Smartphone from Hackers
Continue reading to find out how to prevent hackers from...
Read more →
How to Protect Your Twitter Account From Hackers
Learn to how to secure your twitter account to avoid...
Read more →
7 Small Business Cybersecurity Statistics You Need to Know
Here are the top small business cybersecurity statistics you need...
Read more →
Successful Cybersecurity Programs Focus on the Basics
Companies often overlook the basic elements of cybersecurity, leaving them...
Read more →
Top 10 Useful Cybersecurity Statistics for 2020
Here are the top 10 recent cybersecurity statistics you need...
Read more →
How to Control Portable Storage Devices
77 percent of corporate end-users surveyed have used personal flash...
Read more →
How to Create a System Security Plan (SSP)
A system security plan (SSP) lists an organization’s cybersecurity requirements...
Read more →
Use DISA STIGs to Secure Your IT Systems
The Defense Information Systems Agency (DISA) has a wide range...
Read more →
New CMMC Timeline - What Your Company Needs to Do Now
The cybersecurity maturity model certification accreditation board (CMMC-AB) released a...
Read more →
How to Sanitize or Destroy Digital & Non-Digital Media
Did you know that 42% of used drives sold on...
Read more →
You Company’s Culture Must Adapt to CMMC
A company culture fostering discipline will be a great asset...
Read more →
How to Create an IT Acceptable Use Policy + Templates
Creating an acceptable use policy for your information system is...
Read more →
Change Control - Important Considerations Before Making Changes to your IT Systems
Change control procedures are the backbone of any mature cybersecurity...
Read more →
CMMC - What is meant by Mobile Code?
When reading the term “Mobile code” many folks are left...
Read more →
What is an information system?
Understanding what an information system is and its components is...
Read more →
America Needs the Cybersecurity Maturity Model Certification (CMMC) Program
“From U.S. businesses to the federal government, to state and...
Read more →
What are your CMMC password requirements?
We explain your cybersecurity maturity model certification (CMMC) password requirements....
Read more →
CMMC Audit & Accountability Domain Explained
In this post we explain the CMMC audit & accountability...
Read more →
CMMC Access Control Domain Explained
In this post we explain the CMMC access control domain...
Read more →

Does your company need a CMMC?
Around 300,000 companies will need to earn a cybersecurity maturity...
Read more →
America's Plan to Protect its Defense Industry from Cyber Threats
America will protect its defense industrial base from cyber attacks...
Read more →



What is the Cybersecurity Maturity Model Certification (CMMC)?
The cybersecurity maturity model certification is a new DoD cybersecurity...
Read more →

Do CMMC requirements apply to non-DoD contracts?
As of June 2020, CMMC requirements will only apply to...
Read more →

Who Needs a CMMC Certification?
Learn which companies need to earn a CMMC certification to...
Read more →
CMMC - What is Federal Contract Information (FCI)?
Learn what Federal Contract Information (FCI) is and how it...
Read more →
CMMC - What is controlled unclassified information (CUI)?
Learn what CUI is and how it relates to CMMC....
Read more →

CMMC - What Companies Struggle with the Most
Here are the top cybersecurity compliance requirements DoD contractors struggle...
Read more →