This post explains how small-to-medium organizations can automate pre-implementation Security Impact Analysis (SIA) to satisfy NIST SP 800-171 Rev.2 / CMMC 2.0 Level 2 control CM.L2-3.4.4, focusing on practical DevOps pipeline patterns, policy-as-code, and lightweight toolchains that produce audit-ready evidence without slowing delivery.
Why automate pre-implementation Security Impact Analysis for CM.L2-3.4.4
CM.L2-3.4.4 requires analyzing the security impact of changes before they are implemented. Manual reviews are slow, error-prone, and do not scale in modern CI/CD environments. Automating SIA assures consistent detection of high-risk changes (for example, disabling encryption, adding public network access, or loosening IAM policies), provides immediate feedback to developers, and creates machine-readable evidence for auditors and assessors under the Compliance Framework.
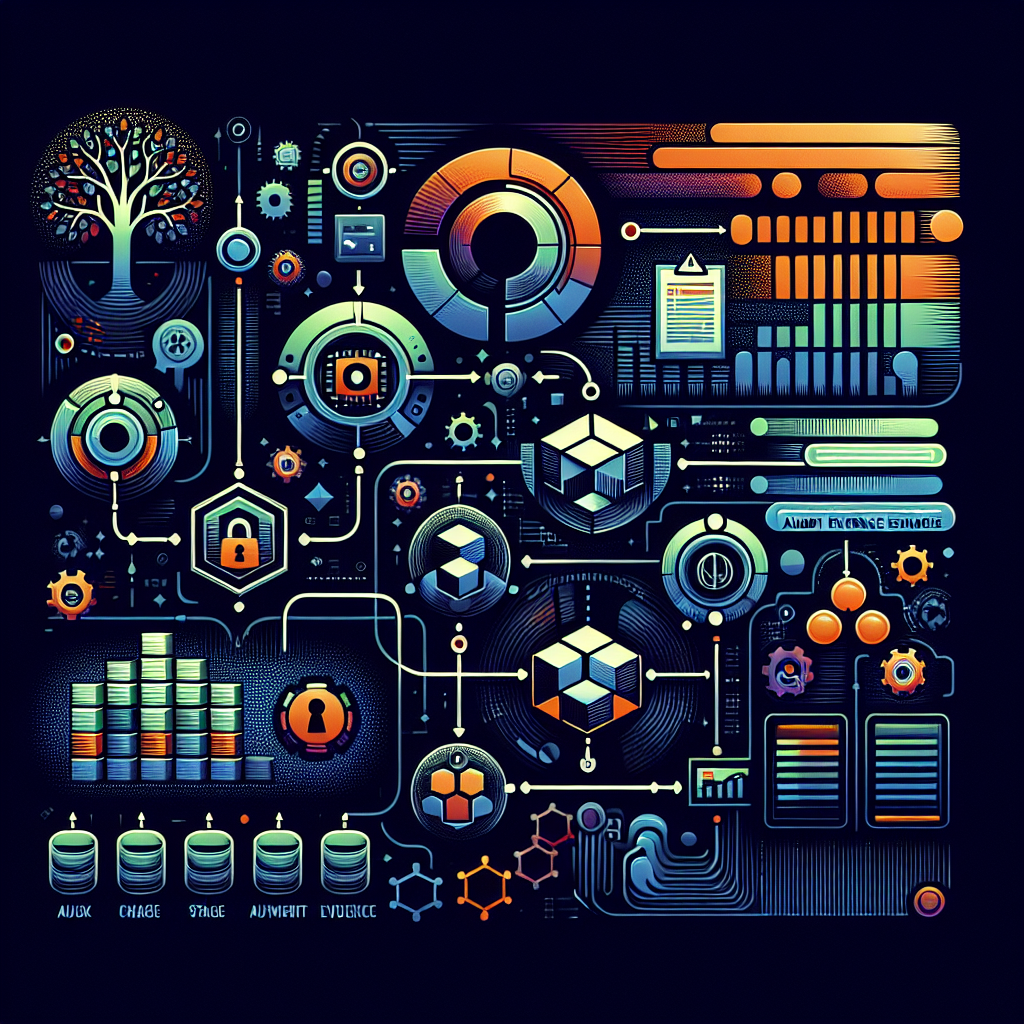
How to automate SIA in DevOps — high-level pattern
Implement SIA as a policy enforcement stage in your Git-centric workflow. Key components: (1) generate a machine-readable "change bundle" (terraform plan JSON, Kubernetes manifest diff, container image diff, or pull request metadata), (2) evaluate the bundle with policy-as-code and scanning tools (OPA/Rego, Checkov, tfsec, Conftest, Semgrep, Trivy), (3) produce a risk-scored SIA report and artifacts, and (4) gate merges with pass/fail thresholds or route to a manual approval queue when required. Ensure all tools emit logs/artifacts stored with the PR or pipeline run for evidence of compliance with CM.L2-3.4.4.
Pipeline gating and technical specifics
Concrete steps that work cross-platform: for Terraform changes run "terraform plan -out=plan.tfplan" then "terraform show -json plan.tfplan > plan.json" and feed plan.json to policy engines (Rego, Conftest, or custom Python scripts). For Kubernetes, compute a diff between current manifests and proposed manifests; for container changes, run image vulnerability and configuration scans (Trivy or Clair) during the PR. Example policy checks: detect changes that remove "server_side_encryption" on S3, add "0.0.0.0/0" to security groups, grant "iam:PassRole" to a broad principal, or add an ingress controller rule that exposes CUI endpoints publicly. Automate generation of an SIA report JSON that includes changed resources, failed/passing policies, control mappings (e.g., "NIST 3.4.4 -> CM.L2-3.4.4"), and recommended mitigations.
Toolchain suggestions for small businesses
Small organizations can deploy a minimal but effective stack: GitHub Actions or GitLab CI for pipelines, Checkov/tfsec/Conftest for IaC policy checks, Trivy for container scanning, Semgrep for quick SAST rules, and OPA (Rego) for custom compliance rules that map to NIST/CMMC controls. Use pre-commit hooks locally to catch obvious issues early. For evidence, configure the CI to attach the plan.json, policy evaluation JSON, and an SIA summary to the PR and to an immutable storage (artifact store, S3 with versioning, or your internal compliance repo). This keeps costs low and scales as the team grows.
Step-by-step implementation checklist
Actionable checklist: 1) Inventory change types that require SIA (network, IAM, storage, encryption, services handling CUI). 2) Create policy-as-code rules that assert secure defaults and map to control CM.L2-3.4.4. 3) Add a pipeline stage that generates a change bundle (terraform plan JSON, manifest diff, etc.). 4) Run automated policy evaluations; fail the pipeline for high-severity issues; create advisory comments for medium/low. 5) For blocked changes, auto-create a ticket (JIRA/GitHub Issue) with the SIA report and require an approver with a documented rationale. 6) Log approvals, exceptions, and final artifacts to your evidence store. 7) Periodically review and tune policies to reduce false positives.
Real-world small business scenarios
Scenario A: A small DoD subcontractor uses Terraform on AWS. A developer proposes a change that modifies an S3 bucket to remove server-side encryption. Terraform plan JSON is validated by Checkov and a Rego rule that checks for "server_side_encryption" and fails the PR, automatically adding a comment that links to the NIST/CMMC mapping and a recommended mitigation. Scenario B: A startup runs a Kubernetes cluster and a developer adds a new Service of type LoadBalancer. The pipeline computes the manifest diff, runs a policy that detects creation of external IPs for CUI-labeled namespaces, and moves the change to manual review, logging the SIA artifact in the compliance repo. These automated gates prevent risky changes while keeping the developer informed and auditors supplied with evidence.
Risks of not implementing CM.L2-3.4.4 automation
Failing to analyze security impact pre-implementation increases the likelihood of data exposure, privileged escalation, and non-compliance findings. For example, an unchecked change could make CUI buckets publicly readable, disable encryption, or create overly permissive IAM roles—events that can result in contract loss, fines, or failed audits. Manual processes often miss transient or cross-repository interactions that automated SIA can detect, and lack of evidence trails makes demonstrating compliance to assessors difficult and time-consuming.
Compliance tips and best practices
Best practices: (1) Map each policy check to a specific control ID (NIST 3.4.4 / CM.L2-3.4.4) so evidence clearly demonstrates coverage. (2) Define risk thresholds that trigger manual review vs. automatic block. (3) Maintain an exceptions process with time-boxed, reversible approvals and post-implementation review. (4) Ensure pipeline artifacts are immutable and retained according to your retention policy. (5) Train developers on common SIA failures and provide sample remediation steps in PR comments to speed fixes. (6) Periodically audit your policy repository to align with updates in NIST/CMMC guidance and your threat model.
Summary: Automating pre-implementation Security Impact Analysis for CM.L2-3.4.4 is achievable for small businesses using a small set of pipeline patterns and open-source tools. The goal is consistent, repeatable detection of high-risk changes, inline developer feedback, and audit-ready evidence that maps back to NIST SP 800-171 Rev.2 / CMMC 2.0 Level 2 controls. Start by identifying high-risk change types, codify policies as code, integrate SIA checks into the Git workflow, and capture artifacts for compliance — doing so reduces risk and keeps delivery velocity high while meeting Compliance Framework requirements.