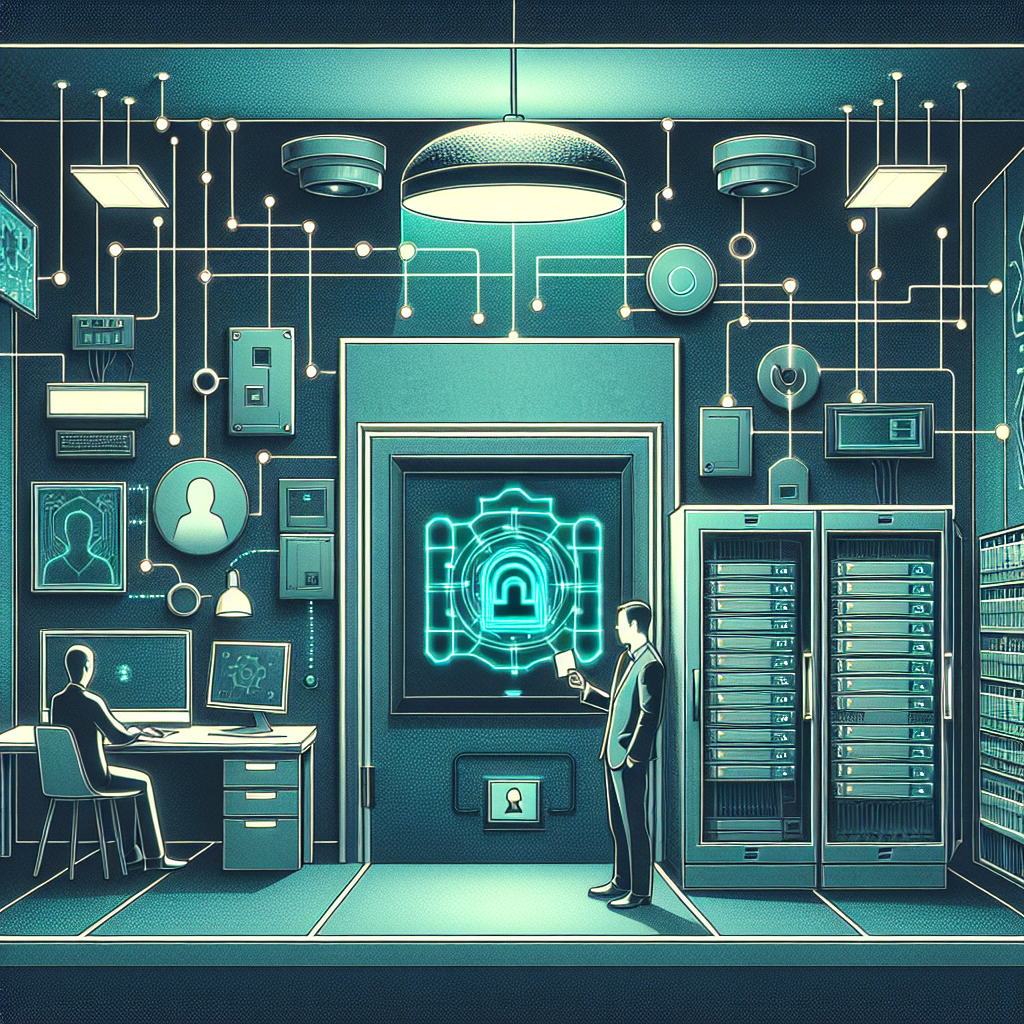
This post explains how to implement the FAR 52.204-21 basic safeguarding requirement and the CMMC 2.0 Level 1 control PE.L1-B.1.VIII (limit physical access to organizational systems, equipment, and the respective operating environments to authorized personnel) in a small-business environment with step-by-step actions, technical details, real-world examples, and evidence collection advice.
Understanding PE.L1-B.1.VIII and FAR 52.204-21 in Practice
At Level 1, CMMC expects foundational physical access controls to protect Federal Contract Information (FCI) and covered systems, and FAR 52.204-21 requires basic safeguarding of contractor information systems. For Compliance Framework practitioners, the objective of PE.L1-B.1.VIII is straightforward: ensure only authorized people can reach systems and media that contain FCI, and create verifiable evidence that access is restricted and monitored. Implementation should be risk-based, scalable for a small office, and documented so auditors can easily confirm controls.
Step-by-step Implementation
1) Scoping and Inventory
Start by scoping: list all areas, systems, and media that store or process FCI (workstations, file servers, network switches, external drives, printed materials). Tag each item with an asset identifier (barcode or QR) and record owner, physical location, and criticality. For a 10-person office example, this might include two desktop workstations used for contract work, one network-attached backup drive, and a locked server cabinet in a shared office suite.
2) Define Access Authorization and Policies
Create a written physical access policy that defines who is authorized to access each asset and area, the approval workflow, and how authorization is removed on separation. Use role-based access where possible (e.g., “Engineering team: access to dev room”; “Contract employees: no server room”). Keep a simple change log for permissions. For small businesses, a spreadsheet or lightweight HR ticketing record is sufficient if retained as evidence.
3) Implement Technical Physical Controls
Use layered controls: external doors should have commercial locks or electronic access control (cloud-managed badge reader, mobile credential, or PIN pad). Sensitive areas (server room, file closet) should use higher assurance (electronic door controller with audit logs or a keyed lock with limited-key control). For electronic systems, deploy a PoE door controller with a Wiegand or OSDP reader, ensure controller firmware is updated, and integrate logs into a central archive (CSV export or SIEM) with timestamps synchronized via NTP. If budget is limited, use a keyed lock (ANSI/BHMA grade 1 or 2 recommended for server cabinets) plus a locked cabinet for backup media.
4) Visitor and Contractor Management
Enforce visitor controls: require sign-in, sponsor validation, temporary badges, and escorts when appropriate. Maintain a visitor log (digital or paper) that captures name, company, purpose, arrival/departure times, and sponsor. For remote or co-working sites, require visitors to present ID and register in advance. Store logs as evidence of control and retain them according to contract requirements (commonly 90 days to 1 year depending on policy).
5) Monitoring, Recording, and Evidence Collection
Deploy monitoring where it provides value: a single camera covering the server room door, motion sensors in sensitive rooms, and access controller logs are typical. Ensure video systems use secure credentials, encrypted storage, and time-synced metadata; set retention consistent with business and contract needs (e.g., 30–90 days). Export access-control logs regularly and retain them in read-only format (signed CSV or WORM storage) as evidence. For small businesses, a cloud-managed access system that retains logs and provides exportable audit trails can meet evidence needs with minimal administrative overhead.
6) Training, Onboarding, and Deprovisioning
Train employees and contractors on physical security procedures, tailgating prevention, visitor handling, and device/media handling. Maintain simple training records (attendance lists, dated acknowledgments). Implement an offboarding checklist that includes badge deactivation, key return, and removal from access-control lists; ensure IT and facilities coordinate so access is removed on the employee's last day.
7) Verification, Testing, and Continuous Improvement
Regularly test controls: perform quarterly spot checks (attempted access by authorized and simulated unauthorized people), review logs monthly, and reconcile asset inventory against physical assets semi-annually. Document findings and remediation steps. For example, if building maintenance staff retain keys, update your policy and rekey or replace locks as needed, and capture that change in the risk register.
Real-world Small Business Scenario
Example: A small defense sub-contractor with 12 employees uses a leased office in a multi-tenant building. They install a cloud-managed badge system for the office entrance and a keyed lock on the server cabinet. Laptops are encrypted (BitLocker/FileVault) and kept in employee custody; backup media is stored in the locked cabinet. Visitors must be registered in a tablet-based sign-in app and escorted when accessing any area with FCI. Access logs from the badge system and visitor records are exported monthly and stored in a secure folder with read-only permissions for 1 year to meet contract evidence requirements.
Compliance Tips and Best Practices
Keep evidence simple and structured: an access-control policy document, an asset inventory spreadsheet, exported access logs, visitor logs, training records, and change logs. Use unique IDs for badges and assets to tie records together. Use principle of least privilege for physical areas, rotate keys or disable credentials after a suspected compromise, and enforce secure defaults (disable default passwords on door controllers and cameras). For low-budget environments, favor cloud-managed systems that provide built-in logging and retention to reduce administrative burden.
Risks of Non-Implementation
Failing to implement PE.L1-B.1.VIII controls can lead to unauthorized physical access to systems and FCI, increasing the risk of data theft, inadvertent disclosure, or tampering. Consequences range from contract noncompliance and termination, penalties, and lost future federal opportunities, to reputational damage and remediation costs. For small businesses, a single physical breach can be catastrophic if it involves sensitive contract information.
In summary, meeting FAR 52.204-21 and CMMC 2.0 Level 1 PE.L1-B.1.VIII is achievable for small businesses through scoping, simple but effective physical controls, documented policies, monitored access logging, visitor management, training, and routine verification. Prioritize evidence collection and retention so you can demonstrate compliance during assessments—start with inventory and policy, add layered physical and technical controls, and operationalize regular reviews.