Network segmentation is one of the most effective technical measures for reducing attack surface and preventing lateral movement; ECC 2-5-3 explicitly requires a maintained segmentation diagram plus supporting policies and controls — this post walks you through practical steps, sample configurations, and real-world small business scenarios to help you meet that requirement under the Compliance Framework.
What ECC 2-5-3 requires (diagram, policies, and controls)
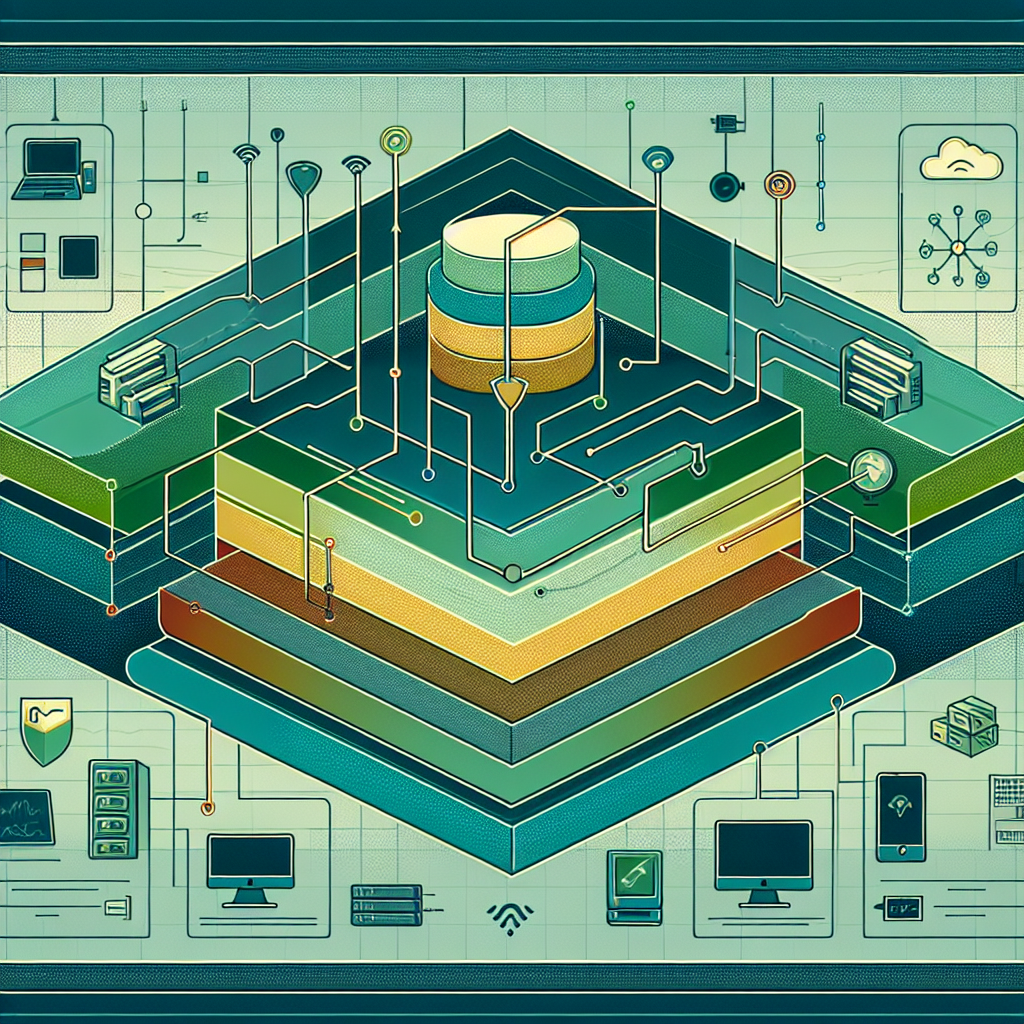
At a minimum, ECC 2-5-3 expects organizations to produce and maintain a current network segmentation diagram, define formal segmentation-related policies (who can access which zones and why), and implement technical controls that enforce those policies. In Compliance Framework terms this means mapping assets to zones, documenting trust levels and permitted flows, recording role-based responsibilities, and operationalizing controls (firewall rules, VLANs, NAC, host-based controls) so the documented policy is actually enforced and auditable.
Designing a clear segmentation diagram
Diagram elements and details to include
Your segmentation diagram is the compliance artifact reviewers will open first. Make it actionable: show zones (corporate, accounting, POS, guest, IoT, DMZ, management), subnet ranges (e.g., VLAN10 10.10.10.0/24 - Employees, VLAN20 10.10.20.0/24 - Guest), firewall and router choke points, VPN concentrators, RADIUS/NAC servers, and one-way or restricted flows (e.g., Corporate -> DMZ: TCP 443 to 10.10.50.10). Annotate the diagram with the trust level (high/medium/low), the owner for each zone, the primary enforcement device(s), and references to the rule-set IDs in your firewall or ACL repository to make the diagram a map to live controls rather than a static picture.
Policies you must write and what to include
Create a Segmentation Policy that defines zone definitions, allowed/denied flows, approval processes for exceptions, change control requirements, and review cadence. Include an Access Control Policy that maps roles (HR, Finance, IT, Helpdesk) to zones and permitted protocols. Add an Exceptions/Temporary Access Procedure that mandates justification, time limits, logging, and post-approval review. Finally, tie these policies to incident response and change control — e.g., any segmentation change requires a ticket, risk assessment, and diagram update before being moved to production.
Technical controls and concrete configuration examples
Firewall, VLAN, NAC and host-based rules
Operationalize the policy using layered controls. Examples: - VLANs: configure logical separation on switches (interface vlan 10 ip address 10.10.10.1/24 for Employees). - Firewall rules: implement default deny between zones and explicit allow rules. Example Cisco IOS extended ACL allowing only HTTPS from corporate to DMZ webserver: access-list 101 permit tcp 10.10.10.0 0.0.0.255 host 10.10.50.10 eq 443 apply to outside interface in the right direction. - iptables example for a Linux router enforcing one allow and then deny: iptables -A FORWARD -s 10.10.10.0/24 -d 10.10.50.10 -p tcp --dport 443 -j ACCEPT iptables -A FORWARD -s 10.10.10.0/24 -d 10.10.50.0/24 -j DROP - NAC (802.1X with RADIUS): require device posture before assigning to trusted VLAN; quarantine non-compliant endpoints into a remediation VLAN with internet-only access. - Host-based microsegmentation: use Windows Defender Firewall or host iptables to restrict east-west traffic on critical servers (e.g., accounting server should only accept connections from 10.10.10.0/24 on ports 3389 and 445 from the admin VLAN).
Small-business example: step-by-step implementation
Imagine a 25-person retail business with POS, back-office accounting, guest Wi‑Fi, printers, and 8 IoT cameras. Practical segmentation steps: 1) Inventory assets and assign them to zones (POS -> POS zone, accounting -> Finance zone). 2) Design subnets: POS 10.10.30.0/24, Finance 10.10.40.0/24, Guest 10.10.20.0/24, Cameras 10.10.60.0/24, DMZ 10.10.50.0/24. 3) Configure switch VLANs and tag access ports; enable port security to limit MAC addresses on POS ports. 4) Implement firewall rules: allow only payment gateway traffic from POS to internet and restrict POS -> Finance (default deny). 5) Deploy simple NAC: unauthenticated devices go to Guest or Quarantine VLAN. 6) Update your segmentation diagram and policy, and perform a staged cutover (test POS transactions, verify accounting application connectivity) before enforcing strict rules.
Testing, monitoring, and the risk of not implementing segmentation
Test segmentation with internal scans and validation scripts (nmap from each zone to verify permitted ports) and schedule quarterly penetration tests or tabletop exercises. Monitor with centralized logging (firewall logs, switch logs, NAC events) and alert on anomalous east-west traffic. The risk of not implementing ECC 2-5-3-aligned segmentation is high: an attacker who compromises a single workstation can move laterally to high-value systems (financial records, POS systems), causing data theft, service disruption, regulatory fines, and reputational loss. Additionally, auditors will flag missing diagrams, undocumented exceptions, or unenforced policies — which can lead to failed compliance assessments and contractual penalties.
Summary
To meet ECC 2-5-3 under the Compliance Framework, produce a living segmentation diagram, codify segmentation and access policies, and implement layered technical controls that map directly to that documentation; for small businesses, focus on simple, enforceable VLAN and firewall rules, NAC for posture checking, and host-level hardening — then test, log, and review regularly. Doing this reduces attack surface, makes audits straightforward, and protects your most sensitive assets from lateral threats.