This post provides a hands-on, vendor-neutral checklist and implementation advice for small contractors who must meet the physical access requirements of FAR 52.204-21 and CMMC 2.0 Level 1 (control PE.L1-B.1.VIII), focusing on pragmatic steps you can take today to protect Federal Contract Information (FCI) with constrained budgets and staff.
Why physical access controls matter under the Compliance Framework
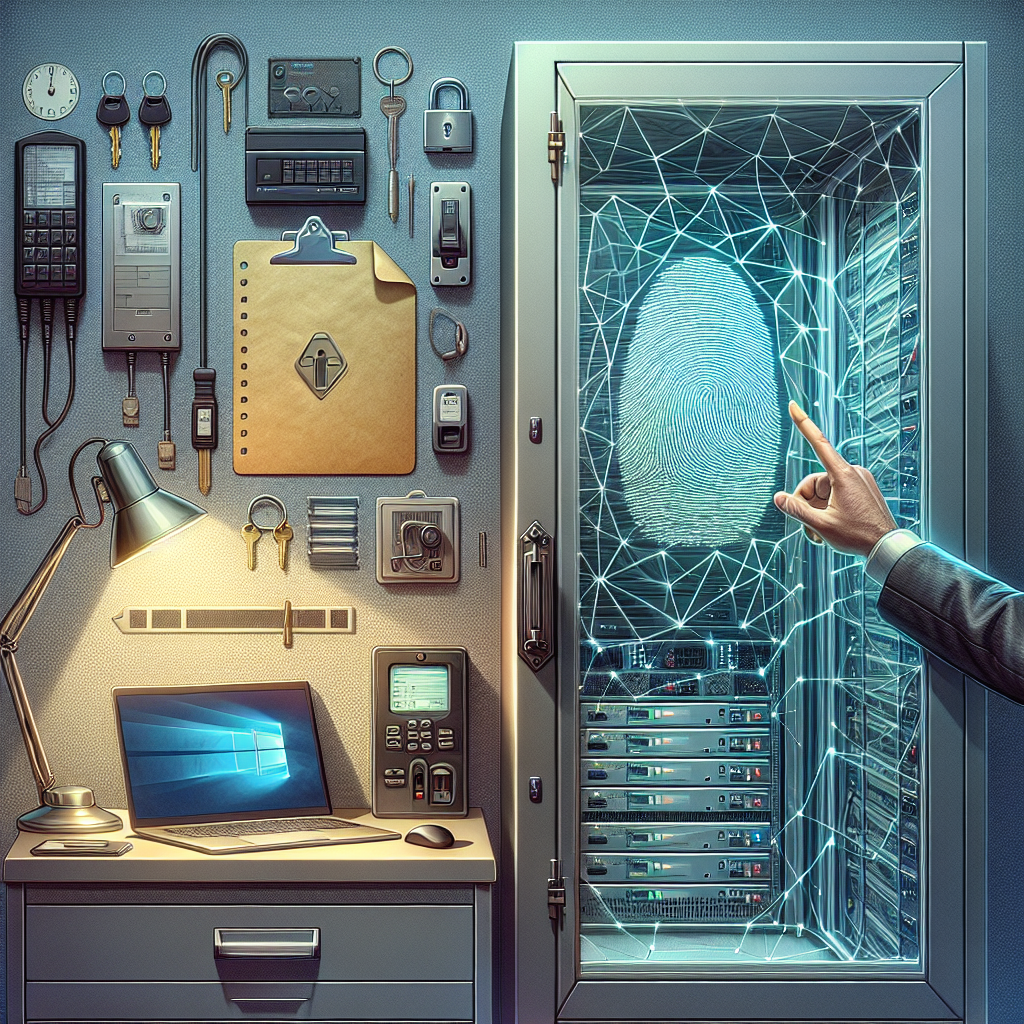
Under the Compliance Framework for FAR 52.204-21 and CMMC Level 1, physical access controls are a foundational safeguard: they limit who can touch systems, media, and equipment that process or store FCI. For small contractors this usually means protecting a single office, a server/telecom closet, laptops and mobile devices, and any printed FCI. The core objective is simple — prevent unauthorized people from viewing, removing, or tampering with covered information and the devices that store it.
Step-by-step implementation checklist for small contractors
Below is a practical checklist organized into discovery, design, implementation, and ongoing operations phases. Each step includes technical detail, a suggested small-business approach, and acceptance criteria so you can test completion.
1) Discovery and scope — Identify what to protect
1. Inventory locations and assets that handle FCI: employee workstations, laptops, printers, file cabinets, routers, switches, and any removable media. Record physical location, owner, and whether the asset stores FCI. Acceptance: a one-page inventory spreadsheet covering all assets and locations.
2) Policy and roles — Define who may access what
2. Create a short Physical Access Policy for Compliance Framework that defines secure areas, visitor procedures, badge and key management, and minimum escorting requirements. Assign a Responsible Person (e.g., office manager / IT lead) who will manage access changes and audits. Acceptance: signed policy and an assigned Responsible Person listed in the inventory.
3) Zone your space — Public vs. controlled areas
3. Physically separate public-facing zones (reception, waiting) from controlled zones (offices, server closet). Use clear signage and an interior door or card-controlled barrier where staff-only areas begin. For small shops a single keyed door with a keypad or badge reader to the office floor is often sufficient. Acceptance: controlled area has a physical boundary and signage.
4) Implement access methods — locks, badges, and keys
4. Choose access hardware appropriate to risk and budget: high-security keyed deadbolt or commercial-grade electronic keypad (ANSI grade 2 is a good small-business compromise) for entry doors; a keyed lock plus cam-lock cabinet for printed FCI and backup media. If using card readers/badges, pick a cloud-managed access control system that provides exportable audit logs (ID, time, door, result). Technical detail: require encrypted badge tokens (AES), record NTP-synced timestamps, and retain logs at least 90 days. Acceptance: locks installed and tested; one access log export produced.
5) Server/telecom closet hardening
5. Secure server, NAS, and networking equipment in a locked closet or cabinet. Install a door contact sensor (magnetic) to alert on unscheduled openings and an optional tamper- or motion-sensor with local alerting. For small offices, a rack-mount cabinet with a mechanical or electronic lock is low-cost (~$200–$600). Ensure network switches powering cameras or access readers are on a secured PoE switch and isolated onto a management VLAN. Acceptance: closet locked, sensor reporting, and networking gear on a management VLAN.
6) Visitor control and badge lifecycle
6. Implement a visitor log and escort policy: visitors sign in with name, company, host, and time; they must be escorted in controlled areas. De-provision badges and keys within 24 hours of termination or role change; rekey doors if keys are lost or personnel turnover is high. Technical note: if you cannot deploy electronic badges, maintain a manually signed log and take a photo ID copy for higher-risk visits. Acceptance: visitor log in place and examples of deprovisioning records.
7) Surveillance and logging — cameras, retention, and privacy
7. Consider cameras for entrances and server room doors. Minimum recommended specs: 1080p resolution, 10–15 fps, PoE cameras with encrypted storage and user access control. Retain recordings for at least 30–90 days depending on risk and storage capacity; store logs off-device (cloud or separate NAS) and protect them with access controls. Ensure signage indicates video surveillance to meet legal/privacy expectations. Acceptance: cameras recording entrance/closet with verified playback and retention settings.
8) Technical controls for endpoints and media
8. Apply technical protections that complement physical controls: full disk encryption (FDE) for laptops and mobile devices, screen lock after 5 minutes of inactivity, automatic VPN for remote access, and cable locks for workstation laptops left onsite. For removable media, use encrypted USBs and lock them in a cabinet when not in use. Acceptance: FDE enabled on all laptops and documented encryption status per asset inventory.
9) Audit, review, and testing
9. Quarterly walkthroughs and an annual audit are practical for small contractors. Test badge deactivation, visitor log completeness, and perform a simulated unauthorized access attempt (a scheduled penetration test of physical controls). Maintain a findings log with remediation deadlines. Acceptance: completed quarterly checklist and closure of high-priority findings within 30 days.
Real-world scenarios and low-cost examples
Scenario A — 12-person IT consultancy with a single office: install a keypad lock at the main office door ($150–300), a locking cabinet for printed FCI, enable BitLocker/FileVault on all laptops, and use a cloud access control service for the server closet with a single badge reader (~$30/mo). Use a paper visitor log in reception but require visitors to be escorted. Scenario B — Home-based subcontractor with occasional FCI: avoid storing paper FCI; when necessary, keep it in a locked, fire-rated cabinet and use a tablet-based sign-in app for visitors. These low-cost choices meet the principles of the Compliance Framework while staying practical.
Risks of not implementing the control
Failing to implement physical access controls exposes your organization to direct risks: unauthorized disclosure of FCI, hardware theft (laptops, drives), and malicious tampering of network equipment. Noncompliance can lead to contract action, loss of DoD/ federal work, and reputational damage. Operationally, a single compromised laptop with unencrypted FCI can lead to a data breach that costs far more than the modest investments required to implement these controls.
Compliance tips and best practices
Maintain least privilege for physical access — only give keys or badges to people who need them. Automate deprovisioning (disable badge access and VPN within 24 hours of termination). Keep policies short and practical — one page for physical access and a one-page incident response checklist for physical breaches. Log everything you can reasonably capture (access logs, visitor logs, camera footage retention policies) and store logs in a protected, redundant location. Finally, train staff in observing and reporting tailgating and suspicious behavior.
In summary, meeting PE.L1-B.1.VIII under the Compliance Framework is achievable for small contractors through disciplined scoping, inexpensive physical barriers, basic electronic access controls, routine audits, and simple technical complements like full-disk encryption and camera logging; these steps significantly reduce the risk to FCI and help ensure contract compliance without a large enterprise budget.