This post explains how to implement and integrate vulnerability scanning and patch management to meet NIST SP 800-171 Rev.2 / CMMC 2.0 Level 2 control RA.L2-3.11.3 for small-to-midsize contractors, focusing on practical workflows, measurable SLAs, tooling choices, and the concrete evidence auditors expect.
Understanding RA.L2-3.11.3: objectives and risk
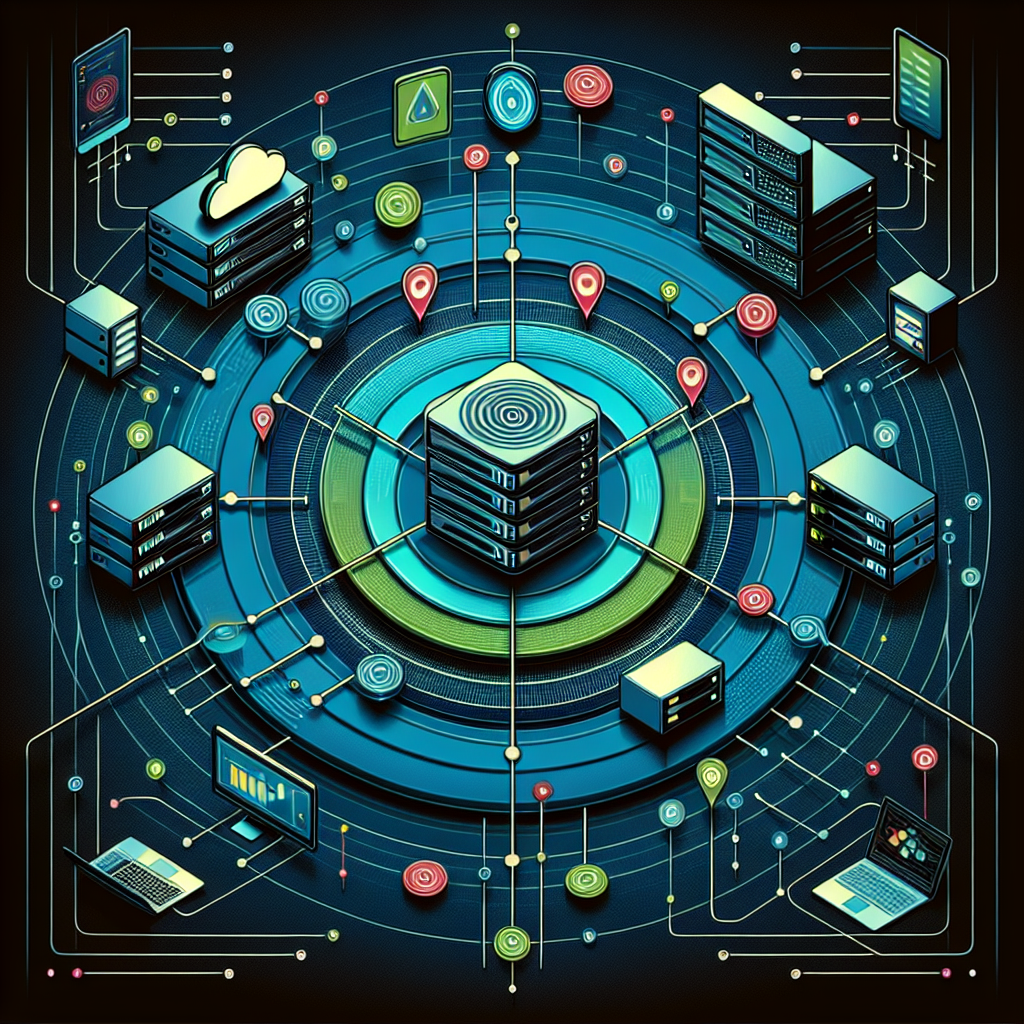
RA.L2-3.11.3 requires organizations to actively scan systems and applications for vulnerabilities and ensure timely remediation or mitigation of identified weaknesses; the key objectives are consistent asset discovery, regular scanning (external and internal), authenticated checks where possible, risk-based prioritization, and documented remediation tracking. Failure to implement these controls risks unauthorized access, data exfiltration of Controlled Unclassified Information (CUI), breach of contract with DoD/prime contractors, and failed assessments that can disqualify your organization from future work.
Practical implementation steps (Compliance Framework-focused)
Start with a verified asset inventory (CMDB or spreadsheet that is reconciled weekly) that tags systems handling CUI, internet-facing services, and high-value servers. For small businesses, use a simple CMDB such as a dedicated sheet or a lightweight tool (NetBox, Snipe-IT) integrated with discovery (Nmap or cloud APIs). Classify assets by owner, environment (prod/stage/test), and patchability (can we apply vendor patches?). This inventory is the foundation for proving coverage to an assessor.
Configure a dual-scan approach: external perimeter scanning from an external scanner and internal authenticated scans from inside the network. For internal systems run authenticated scans against Windows (WinRM/SMB with a least-privilege service account) and Linux (SSH with a sudo-capable account) to get accurate results. Schedule full internal scans weekly and external scans at least weekly; add daily vulnerability checks on internet-facing assets. Tune scans to avoid business disruption (exclude heavy checks during business hours, use credentialed checks to reduce false positives). Map scanner findings to CVE/CVSS, CWE and CPE to support prioritization.
Patch management integration and workflows
Integrate scanning results into your ticketing/change system (Jira, ServiceNow, or even a shared spreadsheet + ticket IDs). Implement a triage table: Critical (CVSS ≥9 or RCE on internet-facing CUI systems) = 7 days, High (CVSS 7–8.9) = 30 days, Medium = 90 days, Low = next maintenance window. For environments with contractual SLAs, adjust timelines to match contract terms. Always create a change record, test patches in a staging environment mirroring production, schedule a maintenance window, and keep rollback plans and snapshots in place. For unpatchable legacy systems, document compensating controls (segmentation, access control lists, host-based firewall rules) and an approved POA&M (Plan of Action & Milestones).
Automation, tools, and technical details
Choose tools that integrate: vulnerability scanners (Tenable Nessus/Nessus Essentials, Qualys, Rapid7, or Greenbone/OpenVAS), patch orchestration (Microsoft WSUS/Intune/Endpoint Manager for Windows, Canonical Landscape for Ubuntu, vendor tools for networking gear), and a ticketing system with APIs to automate ticket creation from scanner APIs. Use scanner credentialing: Windows scans should use domain or local admin-like accounts limited to read-only where possible; avoid storing plaintext credentials—use secrets management (Azure Key Vault, HashiCorp Vault). For cloud, enable AWS Inspector and Azure Security Center vulnerabilities; for containers, add image scanning (Trivy/Clair) into CI/CD. Log patch deployment status: build automated reports with successful installs, pending reboots, and failed patches to provide audit evidence.
Evidence for assessors should include your vulnerability scanning schedule, raw and filtered scan reports (with exporter timestamps), ticket IDs linking to remediation activities, patch deployment logs (SCCM/Intune/WSUS reports), change management approvals, POA&Ms for deferred items, and dashboards showing reduction of open critical findings over time. Keep historic snapshots of reports (monthly) to demonstrate trends and that remediation occurred within SLA windows.
For a small business example: a 50-seat CUI subcontractor uses Microsoft 365 with Intune for endpoint management, WSUS for Windows update control, Nessus Essentials for internal vulnerability scanning (credentialed scans weekly) and a small cloud-based external scan from Qualys Community. Workflow: Nessus triggers a Jira ticket via webhook for Critical/High findings; tickets require owner assignment within 24 hours, remediation plan within 72 hours, and closure post-patch with deployment screenshots and SCCM/Intune logs. For Linux servers in AWS, they use AWS Inspector plus unattended patch baselines for non-production and controlled windows for production with AMI snapshots before baseline updates.
Best practices: enforce asset tagging (CUI vs non-CUI), prioritize internet-facing and CUI-handling assets, maintain a rollback and testing plan, automate as much as possible to reduce human error, and conduct post-patch validation scans. Keep an approved exceptions process documented and limit exceptions’ duration. For network devices and appliances where vendor patches are intermittent, require configuration backups and network segmentation to isolate vulnerable devices until patched.
Not implementing RA.L2-3.11.3 leaves exploitable vulnerabilities in place, increases attack surface, and provides a clear audit failure point. Worst-case scenarios include ransomware locking CUI systems, loss of contracts, regulatory penalties, and reputational damage. Even if immediate compromise doesn’t occur, unaddressed vulnerabilities will almost certainly be discovered during CMMC assessments, leading to findings and remediations that can delay or block contract awards.
In summary, meeting NIST SP 800-171 Rev.2 / CMMC 2.0 Level 2 RA.L2-3.11.3 requires a repeatable, documented program that ties accurate asset inventory and authenticated scanning to a prioritized, auditable patch management workflow with measurable SLAs; small businesses can achieve compliance with a combination of lightweight CMDB practices, credentialed scanning, integration between scanners and ticketing systems, scheduled patch windows and testing, and clear evidence collection (reports, tickets, logs, POA&Ms) for assessors.