Media disposal is one of the most commonly overlooked but high-risk areas assessed under FAR 52.204-21 and CMMC 2.0 Level 1 (control MP.L1-B.1.VII): if you cannot show that media containing Federal Contract Information (FCI) or other sensitive data is sanitized or destroyed before reuse or disposal, you fail the assessment — and you expose your organization to data leaks and contract risk.
What MP.L1-B.1.VII requires and the Compliance Framework objective
At Level 1, MP.L1-B.1.VII focuses on ensuring media (electronic and physical) is rendered unreadable or irrecoverable prior to disposal or reuse. The objective in the Compliance Framework context is simple and evidence-driven: demonstrate repeatable procedures, executed controls, and artifacts that prove media containing FCI was appropriately sanitized or destroyed according to accepted standards (e.g., NIST SP 800-88 guidance) or equivalent processes.
Practical implementation steps for small businesses
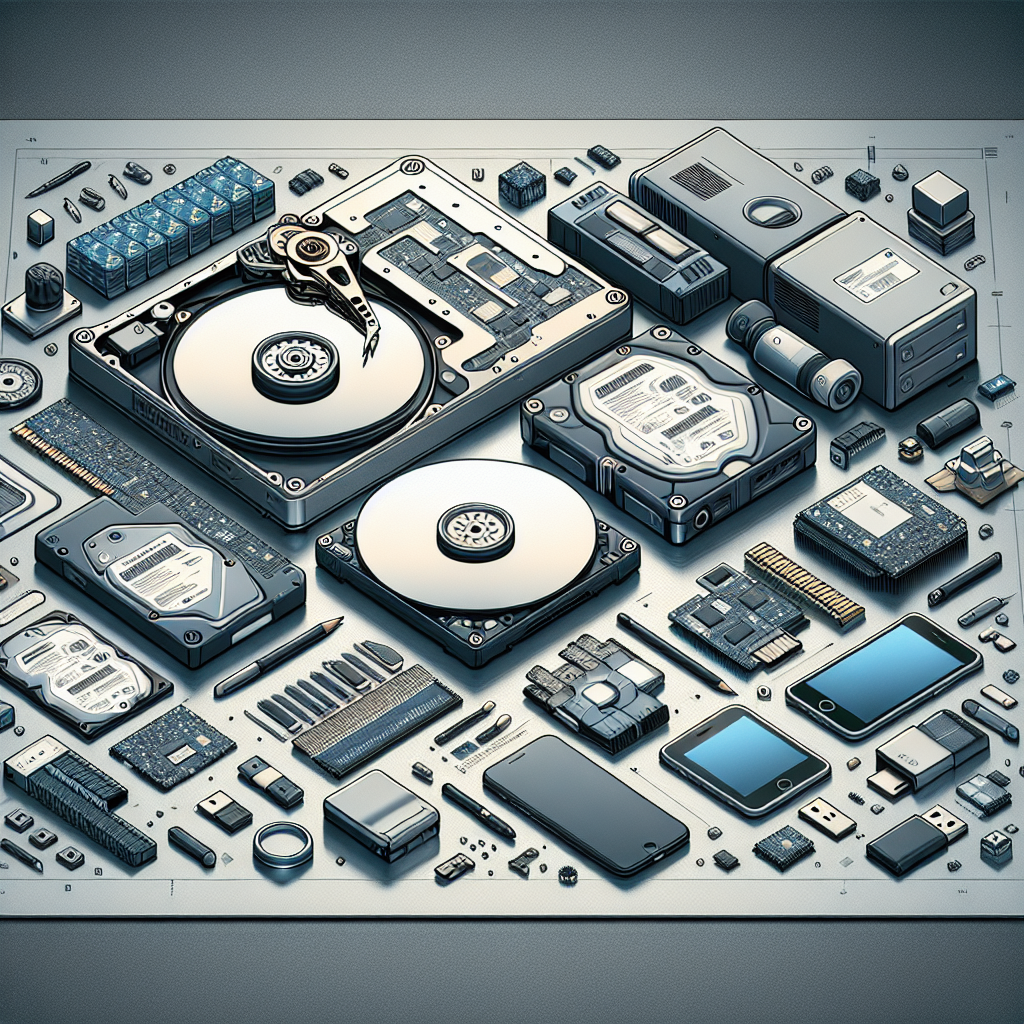
Start with a compact, actionable policy and SOP that defines scope (what counts as media: HDDs, SSDs, USBs, backup tapes, CDs/DVDs, mobile devices, and paper), roles (asset owner, IT, facilities, approved vendor), and a retention-to-disposal workflow. Implement an inventory system (spreadsheet, MDM, or lightweight asset management tool) that tags media with owner, classification (FCI or not), retention end date, and disposal method. For each disposition event, require an approval and a recorded chain-of-custody entry (who handled media, when, why, and verification of sanitization method).
Technical sanitization methods — specific details
Use NIST SP 800-88 principles: Clear (overwrite), Purge (cryptographic erase, degauss for some magnetic media), Destroy (physically shred or disintegrate). For traditional HDDs, a verified single-pass overwrite with a random pattern is generally acceptable for most small business needs; document the tool (e.g., DBAN, Linux shred with passes specified) and verify completion logs. For SSDs, do not rely on overwriting — prefer full-disk encryption with documented key destruction (crypto-erase) or physical destruction (commercial-grade shredding) because wear-leveling can leave data remnants. Mobile devices and USB drives should use vendor secure-erase tools or physical destruction. For paper records, use cross-cut shredders conforming to P-4 or P-5 quality levels, and require vendor Certificates of Destruction for offsite shredding.
Real-world small business scenarios
Example 1: Laptop end-of-life — a marketing associate’s laptop containing contract emails is decommissioned. Process: 1) IT pulls the asset from the inventory, 2) performs a verified full-disk encryption key escrow check, 3) runs vendor secure-erase (or issues the crypto key destruction process), 4) documents the erase log and obtains manager approval, then records the disposition. Example 2: Old server RAID with mixed SSD/HDD — remove drives, identify media type, use certified destruction vendor for SSDs and overwrite/purge HDDs with logs; retain vendor Certificate of Destruction and photos as assessment evidence. Example 3: Found USB drives — anything unaccounted for containing FCI should be collected, quarantined, and either securely wiped via approved tool or physically destroyed, with chain-of-custody recorded.
Evidence to prepare for the CMMC assessment
Assessors will expect concrete artifacts: the media disposal policy and SOP, a current media inventory, disposal logs showing dates and responsible personnel, tool output or vendor certificates proving sanitization or destruction, contracts and terms for third-party destruction vendors (including COI and certificate-of-destruction clauses), and staff training records. Include sample chain-of-custody forms, photos of destruction when practical, and a small audit report showing periodic checks of the process (e.g., quarterly reconciliation of inventory to disposed items).
Risks of non-implementation and compliance best practices
Failing to implement MP.L1-B.1.VII can lead to data exfiltration, breach notifications, contract termination, loss of future DoD work, and reputational damage. Practical best practices: map each media type to one approved disposal method, enforce full-disk encryption for all laptop and mobile endpoints to make emergency sanitization easier, maintain written agreements with vetted destruction vendors, require dual-approval for media leaving premises, and run periodic tabletop exercises simulating a disposal incident to validate procedures. For small businesses, automate what you can (MDM for inventory and wipe commands, scheduled asset retirement reviews) to reduce manual error.
Summary
To prepare for a CMMC assessment on MP.L1-B.1.VII, create a concise media disposal policy, inventory and tag all media, apply NIST-based sanitization or destruction methods appropriate to media type (with technical verification for SSDs, HDDs, and mobile devices), document chain-of-custody and vendor certificates, and collect these artifacts for assessors. Implementing these steps reduces risk and gives assessors clear, repeatable evidence that your small business meets FAR 52.204-21 / CMMC 2.0 Level 1 media disposal expectations.