Companies create information technology acceptable use policies to lay out what is an acceptable and unacceptable use of their systems. This protects employers, employees, and clients. So what do you do when an employee violates your security policies or makes a cybersecurity mistake?
Common IT Security Policy Violations
Some of the most common security policy violations I have observed are employees pirating movies, visiting NSFW sites, abusing their admin privileges to instal unauthorized software such as games onto their work computer, using personal cloud services to store corporate files, and connecting unauthorized devices to the network. The policy violations I mentioned are often committed intentionally, the employee knows that they are violating company policy.
Common Security Mistakes Employees Make
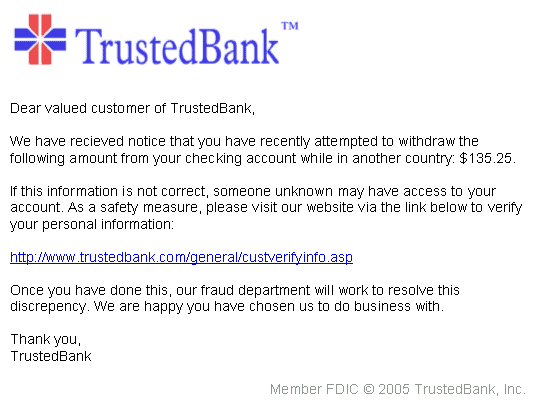
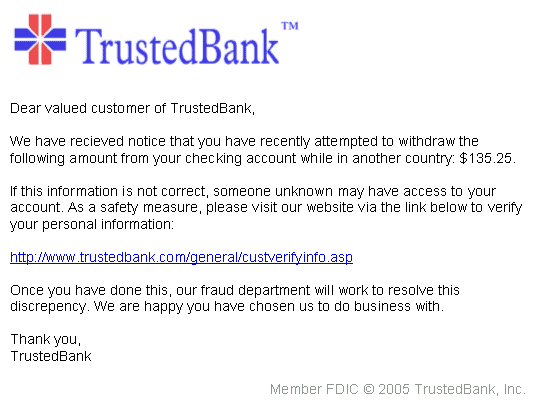
Not all security policy violations are intentional. An employee may let their guard down and let someone into the office who isn’t supposed to be let in. An employee may accidentally access a NSFW site and a manager may not actually be aware that using an unapproved cloud storage service for their new project is a security violation.
Should You Punish Employees?
So what happens when an employee violates a security policy? Some say that punishing an employee could possibly turn them into an insider threat. They may feel resentment for the punishment and may cause more damage.
What if the defendant is a repeat offender? Where do you draw the line? How many times should an employee be allowed to fall for a phishing attack? How many times should an employee be able to get away with using their personal laptop for work? What if the employee downloaded child porn onto their work computer? These are all difficult questions and there isn’t a set answer that covers all scenarios.
Decisions on punishment or sanctions should be left to human resources and upper management. It isn’t security’s place to play judge, jury, and executioner but it is security’s job to document incidents.
What Companies Should be Doing
If an employee falls for a phishing attack or unintentionally commits a security violation then the first action security should take is to provide the user with more training. You don’t need to report anything to their manager just yet as this can embarrass the employee. If they keep making mistakes like writing their password on a sticky note, letting strangers into the office, and violating security policies then you need to report the behavior to human resources as the employee is now a threat to the organization. You can provide suggestions to management such as reducing their access to resources and providing more training.
If an employee keeps committing security violations and is putting the organization at both legal risk and threatening business operations then it's probably best to let the employee go after they have received several warnings.
Be Flexible
The best way to deal with security violations both intentional and unintentional is to be flexible. You want to avoid embarrassing employees and creating a disgruntled employee that becomes an insider threat. You also don’t want employees to think they can get away with everything. Most people are responsible and will take warnings seriously especially if they are given an informative explanation.